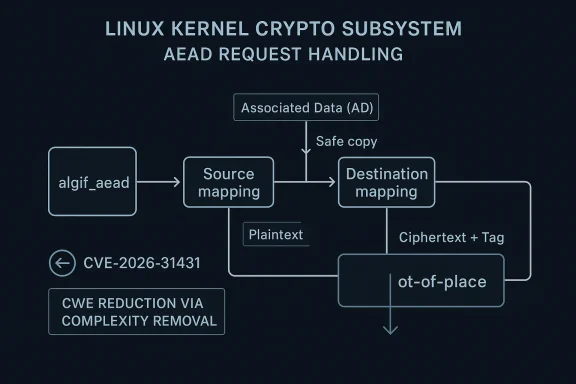
The Linux kernel’s algif_aead code has received a narrowly scoped but security-relevant fix in CVE-2026-31431, and the public record makes the intent unusually clear: the subsystem is being pushed back to out-of-place operation, while preserving only the copying of associated data. The advisory says the in-place complexity added by commit 72548b093ee3 brought no real benefit because the source and destination come from different mappings, so the kernel maintainers chose to simplify the path and remove unnecessary logic. That kind of correction is often easy to underestimate, but in kernel crypto code, simplification is frequently the real hardening step. Linux kernel crypto API is built around a simple but unforgiving promise: callers must describe their data layout correctly, and the kernel will process encryption or decryption through carefully defined request structures. For AEAD modes, the contract includes both the plaintext or ciphertext and the associated data, with the associated data passed separately through
That separation matters because AEAD is not ordinary block-cipher plumbing. The algorithm authenticates both the encrypted payload and the associated data, and the data layout determines whether the kernel can safely and efficiently process a request. The docs also note that encryption and decryption have different memory structures, with associated data on the front and the authentication tag appended where appropriate. In other words, the kernel crypto layer is full of edge conditions that look mundane in code but are critical in practice.
The algif_aead interface sits in the user-space-facing part of that machinery. It translates user requests into crypto API operations, and that translation layer is where assumptions about mappings, buffer ownership, and in-place versus out-of-place handling can become brittle. The CVE description indicates that the kernel’s previous attempt to support in-place operation was not paying for its complexity in any meaningful way. When the source and destination are not really the same mapping, support for inturn into bookkeeping for a case that does not truly exist.
That is why this CVE is interesting even without a dramatic exploitation narrative. The fix is not described as a classic memory-corruption patch or a privilege-escalation primitive. Instead, it reads like a design correction: remove unnecessary branching, copy the associated data directly, and go back to the simpler model the subsystem already fit best. I less clever is often more secure.
The public record also shows that Microsoft’s Security Update Guide is tracking the issue, which is increasingly normal for Linux kernel CVEs that matter to mixed-platform enterprises. Microsoft’s advisory ecosystem routinely includes industry-published vulnerabilities and uses the same publication flow for transparency and downstream visibility. That does not make Microsoft the source of the bug, but it does make the disclosure much more visible to organizations that monitor security through Microsoft tooling.
The core of the change is deceptively small. According to the CVE text, the fix “mostly reverts” commit 72548b093ee3, except for the part that copies the associated data. In practice, that means the ke added complexity needed to pretend the request can be meaningfully handled in-place and returning to a cleaner out-of-place model.
The Linux AEAD documentation reinforces this point indirectly. It explains that the caller manages the data layout, the kernel uses the request structure to interpret that layout, and associated data has its own handling rules. That is a strong hint that changing the model of the buffer arrangement can ripple through correctness, not just performance.
That distinction is critical. Associated data is not payload, but it is not optional decoration either. In AEAD, the integrity of the metadata is part of the security boundary, which means any handling change has to be conservative. The simpler the movement of that data, the easier it is to reason about correctness.
A practical way to read this is that the patch reduces the number of special cases the kernel must juggle. Fewer branches mean feweliasing mistakes, edge-case regressions, or accidental divergence between encryption and decryption behavior. That is exactly the sort of fix kernel maintainers tend to prefer for stable backports.
The broader AEAD documentation shows why that matters. The API already has separate expectations for associated data, plaintext, ciphertext, and tags, and it allows aliasing only in carefully defined circumstances. That means the interface is tolerant of some overlap, but it is not a license for arbitrary buffer reuse.
From a security perspective, this is the kind of code that can become hard to audit because it appears to be more flexible than it actually needs to be. Flexi a commit message, but in a kernel subsystem that handles cryptographic requests, flexibility often translates into more state combinations to test. More combinations usually mean more corner cases.
The fix therefore does something that good kernel maintenance often does: it removes a feature that looked useful but was not actua That kind of deletion is sometimes more valuable than a new safeguard because it shrinks the surface area that future bugs can exploit. Less code really can mean less risk.
That matters for enterprise deployments too. A tiny savings in copying is rarely worth a harder-to-review implementation in a security-sensitive subsystem. Administrators do not patch kernels oretical elegance; they patch them because they need predictable behavior under load. Predictability is what this fix seems to restore.
That design choice is especially important because associated data can be subtle. It is not part of the encrypted payload, but it is authenticated as part of the same operation, which means a mistake can create a false sense of integrity. A path that seems “just metadata” can still become the place where a request is accepted or rejected.
The fix’s emphasis on copherefore not a retreat from security goals. It is a way of making the implementation match the actual semantics of the API. When code paths align with the specification, there is less room for accidental reinterpretation.
Thathen the source and destination are already coming from different mappings. In that environment, trying to simulate in-place behavior can be more confusing than useful. A direct copy avoids having to preserve a model that the actual mappings do not support cleanly.
A related operational point is that fewer aliasing assumptionting easier. Testers can validate request behavior against a simpler expectation, and distributions can backport the change with less fear of subtle semantic drift. That is exactly the kind of stable-tree friendliness kernel maintainers value.
The kernel crypto documentation suggests why even non-exploit bugs matter here. AEAD request handling is tightly specified, and mismanaging the data model can affect both integrity and reliability. In a subsystem this sensitive, a bug does not need to be spectacular to deserve attention.
The fact that the CVE is tied to multiple stable references ntainers considered it suitable for production branches, not merely a cleanup for the next development cycle. Stable-worthy fixes tend to be narrow, understandable, and low-regression. Those are all encouraging signs for operators.
For enterprise environments, especially those using kernel crypto in storage, networking, or platfotical question is not only whether there is a known exploit. It is whether the current implementation is the simplest safe one. In this case, the answer appears to be yes: simpler is safer.
Because Microsoft tracks Linux CVEs in the Security Update Guide, mixed Windows/Linux shops will also see the issue through familiar enterprise tooling. That is useful: it means the vulnerability can appear in the same patch management dashboards as Windows and Azure issues, even though the underlying code lives in the Linux kernel.
In practice, that visibility helps teams make patch decisions faster. The downside is that a “Linux kernel CVE” in a Microsoft-facing dashboard can be easy to dismiss as someone else’s problem. It is not. If the affected Linux systems are part of an enterprise platform stack, the patch belongs in the normal maintenance cycle. re
For consumers, the risk is likely much lower, simply because most consumer systems do not directly exercise kernel crypto interfaces in a way that exposes this specific wrapper logic. But low exposure is not no exposure, and kernel updates should still be taken seriously. Consumer systems benefit ication and hardening as servers.
A good rule of thumb is that even when the direct user impact seems limited, kernel fixes can still eliminate future attack paths or prevent subtle regressions in shared code. Consumers do not need to understand the patch details to benefit from them. They just need vendor updates applied promptly.
This is a pattern seen repeatedly in kernel maintenance. The kernel docs define the contract carefully, and upstream fixes often move code back toward the contract rather than trying to extend the contract with special cases. That approach tends to age better because it is easier to review, easier to backport, and easier to test.
The same logic applies here. If the source and destination are already coming from different mappings, the kernel does not gain much from trying to support an in-place fiction. It gains more by preserving a clear, direct out-of-place flow and copying the associated data explicitly.
That also matters for vendor ecosystems. Distribution kernels and OEM images often lag upstream by design, so the real question is whether the fix was easy to carry forward. The more self-contained the patch, the more likely it is to land quickly and stay intact across versions.
The second thing to watch is vendor backport velocity. For most organizations, the upstream commit matters less than the kernel pping in their fleet. If distributions move quickly, exposure will be brief; if they do not, the old behavior can linger in long-term support trees longer than teams expect. That is why backport tracking matters so much in kernel security.
Finally, it is worth watching whether this fix prompts any broader review of adjacent kernel crypto wrappers. When maintainers remove unnecessary ath, they often uncover similar assumptions elsewhere. That is usually a healthy sign. It means the codebase is being pushed toward the simplest safe model rather than allowed to accumulate cleverness for its own sake.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
aead_request_set_ad. The upstream documentation is explicit that the caller must reserve space correctly even in the out-of-place case, and that associated data can be treated differently from the payload itself.That separation matters because AEAD is not ordinary block-cipher plumbing. The algorithm authenticates both the encrypted payload and the associated data, and the data layout determines whether the kernel can safely and efficiently process a request. The docs also note that encryption and decryption have different memory structures, with associated data on the front and the authentication tag appended where appropriate. In other words, the kernel crypto layer is full of edge conditions that look mundane in code but are critical in practice.
The algif_aead interface sits in the user-space-facing part of that machinery. It translates user requests into crypto API operations, and that translation layer is where assumptions about mappings, buffer ownership, and in-place versus out-of-place handling can become brittle. The CVE description indicates that the kernel’s previous attempt to support in-place operation was not paying for its complexity in any meaningful way. When the source and destination are not really the same mapping, support for inturn into bookkeeping for a case that does not truly exist.
That is why this CVE is interesting even without a dramatic exploitation narrative. The fix is not described as a classic memory-corruption patch or a privilege-escalation primitive. Instead, it reads like a design correction: remove unnecessary branching, copy the associated data directly, and go back to the simpler model the subsystem already fit best. I less clever is often more secure.
The public record also shows that Microsoft’s Security Update Guide is tracking the issue, which is increasingly normal for Linux kernel CVEs that matter to mixed-platform enterprises. Microsoft’s advisory ecosystem routinely includes industry-published vulnerabilities and uses the same publication flow for transparency and downstream visibility. That does not make Microsoft the source of the bug, but it does make the disclosure much more visible to organizations that monitor security through Microsoft tooling.
 What the Fix Actually Changes
What the Fix Actually Changes
The core of the change is deceptively small. According to the CVE text, the fix “mostly reverts” commit 72548b093ee3, except for the part that copies the associated data. In practice, that means the ke added complexity needed to pretend the request can be meaningfully handled in-place and returning to a cleaner out-of-place model.Why out-of-place is simpler here
Out-of-place operation means the source and destination live separately, which aligns well with the fact that the data originates from different mappings. If those mappings are already distinct, then in-place handling offers little to no advantage and can create a false sense of efficiency. ends to optimize something that is not actually shared often ends up increasing risk rather than reducing cost.The Linux AEAD documentation reinforces this point indirectly. It explains that the caller manages the data layout, the kernel uses the request structure to interpret that layout, and associated data has its own handling rules. That is a strong hint that changing the model of the buffer arrangement can ripple through correctness, not just performance.
Associated data stays special
One important detail is that the fix does not abandon associated data handling. It explicitly preserves copying of the AD, which is sensible because AEAD security depends on the associated d the authenticated computation. The bug fix is not “stop touching metadata”; it is “stop overcomplicating the request path and just copy the AD directly.”That distinction is critical. Associated data is not payload, but it is not optional decoration either. In AEAD, the integrity of the metadata is part of the security boundary, which means any handling change has to be conservative. The simpler the movement of that data, the easier it is to reason about correctness.
A practical way to read this is that the patch reduces the number of special cases the kernel must juggle. Fewer branches mean feweliasing mistakes, edge-case regressions, or accidental divergence between encryption and decryption behavior. That is exactly the sort of fix kernel maintainers tend to prefer for stable backports.
Why In-Place Support Was a Problem
In-place support is attractive in theory because it can reduce copying. But theory and kernel reality are not always aligned, especially when the source and destinang from distinct mappings. The CVE text says directly that there is “no benefit” in operating in-place here, which is a very strong way of saying the optimization was illusory.The hidden cost of “helpful” complexity
Complexity in crypto code is rarely free. Every extra condition added to make a code path more generic creates another place where the data model can become ambiguous, especially when the kernel user mappings and internal buffers. If the semantics are already out-of-place in practice, then in-place support may simply introduce control-flow clutter.The broader AEAD documentation shows why that matters. The API already has separate expectations for associated data, plaintext, ciphertext, and tags, and it allows aliasing only in carefully defined circumstances. That means the interface is tolerant of some overlap, but it is not a license for arbitrary buffer reuse.
From a security perspective, this is the kind of code that can become hard to audit because it appears to be more flexible than it actually needs to be. Flexi a commit message, but in a kernel subsystem that handles cryptographic requests, flexibility often translates into more state combinations to test. More combinations usually mean more corner cases.
The fix therefore does something that good kernel maintenance often does: it removes a feature that looked useful but was not actua That kind of deletion is sometimes more valuable than a new safeguard because it shrinks the surface area that future bugs can exploit. Less code really can mean less risk.
Performance versus correctness
There is also a useful lesson here about the balance between optimization and correctness. A micro-optimization that does not materially improve throughput but does increase the mental model burden is usuallyernel crypto code is performance-sensitive, but not every potential shortcut is actually a shortcut once the bookkeeping and edge-case handling are counted.That matters for enterprise deployments too. A tiny savings in copying is rarely worth a harder-to-review implementation in a security-sensitive subsystem. Administrators do not patch kernels oretical elegance; they patch them because they need predictable behavior under load. Predictability is what this fix seems to restore.
Associated Data and Security Semantics
Associated data is one of the least glamorous parts of AEAD, but it is also one of the most important. It is the metadata that must be authenticated even when it is not encrypted, and getting that wrong undermines the point of AEAD altogether. The Linux docs explicitly call foraead_request_set_ad to describe the associated data memory location before encryption or decryption happens.Why the AD path should be boring
In secure systems, the best metadata path is usually the boring one. If the kernel can copy associated data directly and keep the rest of ightforward, then the implementation becomes easier to reason about and less likely to drift. The CVE description suggests that is exactly the conclusion the maintainers reached.That design choice is especially important because associated data can be subtle. It is not part of the encrypted payload, but it is authenticated as part of the same operation, which means a mistake can create a false sense of integrity. A path that seems “just metadata” can still become the place where a request is accepted or rejected.
The fix’s emphasis on copherefore not a retreat from security goals. It is a way of making the implementation match the actual semantics of the API. When code paths align with the specification, there is less room for accidental reinterpretation.
Subsection: Why aliasing matters
The kernel docs say associated data can alias source data in certain cases, but that is a permission, not a requirement. Allowing aliasing does not mean every caller or every wrapper layer should optimize around it. In a wrapper like algif_aead, the safest behavior may be the most literal one: copy what should be copied, and leave the request model unambiguous.Thathen the source and destination are already coming from different mappings. In that environment, trying to simulate in-place behavior can be more confusing than useful. A direct copy avoids having to preserve a model that the actual mappings do not support cleanly.
A related operational point is that fewer aliasing assumptionting easier. Testers can validate request behavior against a simpler expectation, and distributions can backport the change with less fear of subtle semantic drift. That is exactly the kind of stable-tree friendliness kernel maintainers value.
How Serious Is CVE-2026-31431?
At the moment, the public record shows **no NVD CVSis not unusual for a newly published CVE. That means defenders should avoid overreading the scoring silence as evidence of triviality. It simply means the enrichment process has not yet produced a final numeric assessment.What we can infer, cautiously
Based on the description alone, this does not read like a headline-making remote code execution bug. It looks morand complexity issue in a crypto interface, which could lead to unexpected behavior or security degradation if the request path is mishandled. That is a careful inference, not a confirmed exploit path.The kernel crypto documentation suggests why even non-exploit bugs matter here. AEAD request handling is tightly specified, and mismanaging the data model can affect both integrity and reliability. In a subsystem this sensitive, a bug does not need to be spectacular to deserve attention.
The fact that the CVE is tied to multiple stable references ntainers considered it suitable for production branches, not merely a cleanup for the next development cycle. Stable-worthy fixes tend to be narrow, understandable, and low-regression. Those are all encouraging signs for operators.
What kind of impact is most plausible?
The most plausible impact is operational and correctness-driven rather than catastrophic. If a kernel request layer is unnecessarily computcomes are misbehavior, inconsistent handling, or avoidable bugs in future changes rather than immediate compromise. That makes the patch important even if the severity number eventually lands low or moderate.For enterprise environments, especially those using kernel crypto in storage, networking, or platfotical question is not only whether there is a known exploit. It is whether the current implementation is the simplest safe one. In this case, the answer appears to be yes: simpler is safer.
Enterprise and Consumer Impact
The impact of a crypto-interface CVE varies a lot depending on where the kernel is deployed. On a typical desktop or laptop, the affected path d in a way that users notice. On servers, appliances, and cloud infrastructure, kernel crypto paths are much more likely to sit on the critical path for real workloads.Enterprise exposure
Enterprises should care most about this if they run workloads that rely on kernel crypto wrappers or if they consume vendor kernels with backported crypto changes. The danger in enterprise ebout visible failure and more about silent mismatch between intended semantics and actual behavior. Those gaps are hard to diagnose after the fact.Because Microsoft tracks Linux CVEs in the Security Update Guide, mixed Windows/Linux shops will also see the issue through familiar enterprise tooling. That is useful: it means the vulnerability can appear in the same patch management dashboards as Windows and Azure issues, even though the underlying code lives in the Linux kernel.
In practice, that visibility helps teams make patch decisions faster. The downside is that a “Linux kernel CVE” in a Microsoft-facing dashboard can be easy to dismiss as someone else’s problem. It is not. If the affected Linux systems are part of an enterprise platform stack, the patch belongs in the normal maintenance cycle. re
For consumers, the risk is likely much lower, simply because most consumer systems do not directly exercise kernel crypto interfaces in a way that exposes this specific wrapper logic. But low exposure is not no exposure, and kernel updates should still be taken seriously. Consumer systems benefit ication and hardening as servers.
A good rule of thumb is that even when the direct user impact seems limited, kernel fixes can still eliminate future attack paths or prevent subtle regressions in shared code. Consumers do not need to understand the patch details to benefit from them. They just need vendor updates applied promptly.
Broader Kernel SecVE is a good reminder that kernel security work is often about subtracting complexity, not merely adding checks. The cleanest fix is not always a lock, a guard, or an extra branch. Sometimes the right answer is to stop pretending a harder model is useful and return to the one the architecture actually supports.
Simplicity as a security control
When a codeve data, simplicity is not just aesthetic. It reduces the number of possible execution states, which reduces the number of places where assumptions can break. In a crypto wrapper like algif_aead, that reduction is meaningful because the data flow is already structured and heavily constrained.This is a pattern seen repeatedly in kernel maintenance. The kernel docs define the contract carefully, and upstream fixes often move code back toward the contract rather than trying to extend the contract with special cases. That approach tends to age better because it is easier to review, easier to backport, and easier to test.
The same logic applies here. If the source and destination are already coming from different mappings, the kernel does not gain much from trying to support an in-place fiction. It gains more by preserving a clear, direct out-of-place flow and copying the associated data explicitly.
Stable maintenance matters
Theeferences in the CVE record suggests maintainers wanted this fix available to downstream distributions without waiting for a major kernel train. That is a sign of maturity in the Linux security process: narrow fixes are routed quickly when they improve correctness without destabiliThat also matters for vendor ecosystems. Distribution kernels and OEM images often lag upstream by design, so the real question is whether the fix was easy to carry forward. The more self-contained the patch, the more likely it is to land quickly and stay intact across versions.
Strengths and Opportunities
The good news is that this looks like a patch with very favorable properties: it is narrowly scoped, easy to reason about, and aligned with the existing AEAD API model. That makes it a strong candidate for stable backporting and a low-drama update for most vendors. It also reduces future maintenance burden by removing a needless special case.- Simplifies the code path by removing in-place complexity that did not provide real benefit.
- Preserves associated data handling, which protects the semantics AEAD depends on.
- Improves auditability by making request flow more direct and predictable.
- Helps stable backports because the fix is narrow and conceptually clean.
- Reduces regression risk by aligning implementation with the documented API model.
- Strengthens long-term maintainability by eliminating an unnecessary branch of behavior.
- Makes testing easier because the expected behavior is more straightforward to validate.
Risks and Concerns
The main concern is not that this looks like an immediate exploit, but that complexity in crypto wrappers tends to hide bugs until later. A path that “works” but is more complicated than necessary can become a liability in future refactors, especially when multiple mappings and request semantics meet in one place.- Hidden semantic drift could reappear if future changes reintroduce in-place assumptions.
- Downstream patch lag may leave vendor kernels carrying the older logic for some time.
- Misplaced confidence is possible if teams assume “no CVSS yet” means “not important.”
- Regression risk exists whenever a code path is simplified in a performance-sensitive subsystem.
- Enterprise visibility gaps may occur if Linux kernel CVEs are buried inside broader dashboards.
- Testing shortcuts could miss edge cases if teams validate only common request patterns.
- Complex wrapper code is inherently harder to review than the direct out-of-place model.
Looking Ahead
The most important thing to watch next is the finalization of enrichment around this CVE, especially whether NVD asther downstream advisories provide more detail about scope. Until then, the safest interpretation is the one the upstream description already gives: the fix is a design simplification that should be treated as a real maintenance update, not a cosmetic cleanup.The second thing to watch is vendor backport velocity. For most organizations, the upstream commit matters less than the kernel pping in their fleet. If distributions move quickly, exposure will be brief; if they do not, the old behavior can linger in long-term support trees longer than teams expect. That is why backport tracking matters so much in kernel security.
Finally, it is worth watching whether this fix prompts any broader review of adjacent kernel crypto wrappers. When maintainers remove unnecessary ath, they often uncover similar assumptions elsewhere. That is usually a healthy sign. It means the codebase is being pushed toward the simplest safe model rather than allowed to accumulate cleverness for its own sake.
- Check whether your vendor kernel includes the backport.
- Verify any system using kernel AEAD interfaces for related changes.
- Prioritize appliances and server images over isolated desktops.
- Watch for follow-up stable commits in adjacent crypto code.
- Treat simplification patches as security work, not just cleanup.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center