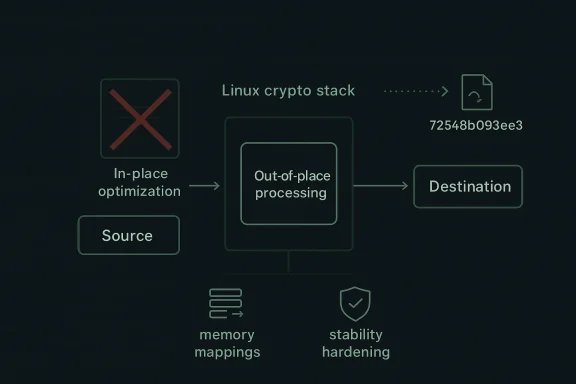
In the Linux kernel, CVE-2026-31431 marks a small but telling correction in the algif_aead crypto interface: the code is being pushed back toward out-of-place operation after a prior attempt to optimize for in-place handling proved unnecessary. The published description says the fix mostly reverts commit 72548b093ee3, except for copying associated data directly, because the source and destination already come from different mappings and there is no practical benefit to the added complexity. That makes this a classic kernel-maintenance vulnerability: not a dramatic exploit headline, but a reminder that subtle design choices in low-level code can create real security and stability risk when they overcomplicate a path that did not need to be clever in the first place. The record was newly published from kernel.org and surfaced in Microsoft’s vulnerability guide on April 22, 2026, with NVD still awaiting a final CVSS assessment at publication time. rst thing to understand about algif_aead is that it sits in a layer of the Linux crypto stack that is easy to overlook until something goes wrong. It is not a flashy application-level API; it is part of the kernel’s interface for authenticated encryption, where correctness depends on the careful choreography of buffers, mappings, and metadata. The recent CVE record indicates that maintainers decided the attempted in-place path was not worth the added complexity, because the source and destination do not naturally share the same mapping context.
That matters becauslives at a junction where performance tuning can collide with memory-safety discipline. A path that looks elegant on paper can become fragile if it tries to reuse buffers in ways the surrounding subsystem does not actually support. In this case, the engineering judgment appears to have shifted back to a simpler and more defensible model: operate out-of-place, and only preserve the direct copying of associated data.
The record’s wording is also revealing. a classic exploit primitive such as an overrun, use-after-free, or privilege escalation. Instead, it reads like a correctness-driven security fix that removes unnecessary branching and state handling from a sensitive kernel path. That kind of change often lands in the CVE system because the Linux kernel treats reliability and security as intertwined, especially where a bug can turn into memory corruption, undefined behavior, or hard-to-debug cryptographic failures under certain call patterns.
For operators, the important question is not whether this is t makes headlines. It is whether the affected kernel build is in use and whether the vendor backport has landed. With Linux CVEs, especially ones sourced from kernel.org stable commits, the practical exposure window is often defined less by the upstream fix and more by how quickly downstream distributions, appliances, and vendor kernels absorb it. That is why this entry deserves attention even before NVD has assigned a formal severity score.
At a technical level, the fix is described as ommit 72548b093ee3. The kernel maintainers evidently concluded that the in-place optimization created complexity without buying meaningful benefit in this path. The source and destination buffers already originate from different mappings, which means the optimization was at best awkward and at worst a maintenance hazard.
That is an important design correction because crypto code is one of those areas where the easiest-look the worst lifetime cost. If a subsystem’s input and output are already segregated by memory mappings, forcing them into an in-place model can introduce extra branches, extra state transitions, and more opportunities for mistakes. The published description suggests maintainers decided that direct copying of associated data was the only part worth keeping from the earlier change.
The broader lesson is that less clever code is often safer code in the kernel. When a feature is built on an assumption that does not hold in tmodel, it may still compile, but it will accumulate awkward edge cases that become maintenance debt. CVE-2026-31431 looks like a cleanup of exactly that sort of debt.
That is not unusual in Linux kernel land. A bug does not need to be a textbook remote-code-execution case to justify a CVE. If it changes how memory is handled, complicates the integrity of a kernel subsystemlexity to create future exploitability concerns, maintainers and CVE recorders will often treat it as a security issue rather than a mere bug fix. Here, the adjustment appears to be about eliminating a risky design direction before it calcified into a larger problem.
This is also the kind of CVE that can look deceptively small to outside observers. Small does not mean irrelevant in kernel engineering. It often means the maintainers caught the issue while the patch could still be narrow, localized, and low-risle branches. That is a good sign, not a reason to ignore it.
A lot of kernel vulnerabilities begin with the same pattern: a maintainer tries to tighten a path, reduce copies, or reuse memory more aggressively, and then discovers that the abstraction boundary underneath is less forgiving than expected. In crypto code, that can quickly become a question of whether the data andable and auditable. Once that clarity is lost, even a small misstep can have consequences well beyond the original optimization.
The patch’s decision to preserve direct copying of associated data while abandoning the rest of the in-place path suggests the maintainers identified a clean dividing line between useful and unnecessary complexity. That is a strong sign the fix is aimed at correctness first and performance second. That order is often the right order in low-level crypt- Crypto paths are highly sensitive to buffer semantics.
The business impact is likely to be modest in comparison to a remote exploit or privilege escalation, but “modest” is not the same as “ignorable.” Kernel crypto bugs can create subtle instability, complicate incident response, and force unexpected patch cycles in environments that rely on hardened kernel builds. If the affected path is present in a distro kernel, enterprise administrators should expect vendor backpream source changes to be the real remediation vehicle.
The practical reality is that consumer impact will be mediated by wor device vendor ships the kernel. A laptop running a mainstream desktop distro may receive the patch quickly, while an embedded Linux appliance or niche device could remain on an older vendor kernel for much longer. That is why the consumer side of Linux security is often less about immediate exploit drama and more about patch cadence.
It is also worth noting that cryptographic plumbing bugs can matter indirectly even if users never interact with the affected interface consciously. Security code tends and layered into other subsystems. A defect that looks niche today can become tomorrow’s support headache if it intersects with another kernel path.
The wording here is especially telling because it says the fix “mostly reverts” the earlier commit rather than replacing it wholesale. That suggests the maintainers found one pge worth keeping — the copying of associated data — while deciding the in-place logic was not defensible. That kind of selective reversal is often a sign of thoughtful review rather than panic.
It also reinforces a larger security truth: complexity is itself an attack surface. Even if no one can yet point to a public exploit, code that performs unnecessary contortions around memory handling is exactly they teams prefer to simplify early.
This timing matters because many organizations still lean on scores as a triage shortcut. When a score is absent, defenders have to lean more heavily on technical context, subsystem criticality, and the patch lineage. In kernel cases like this, that isach anyway, because exposure depends heavily on deployment specifics rather than on a one-size-fits-all rating.
The record also helps prevent the common mistake of waiting for a polished severity label before taking a look. That delay is often where patch debt starts. For a kernel issue, early awareness is usually more valuable than a tidy score badge.
Another opportunity is educational: this CVE can serve as a reminder that data layout decisions are security decisions. If source and destination mappings are different, the safest representation is usually the one that respects that fact rather than trying to paper over it.
A second concern is vendor patch lag. Upstream availability does not guarantee immediate exposure reduction in the real world, especially on long-term-, appliance kernels, or embedded devices. The most persistent risk in kernel CVEs is often the time between upstream fix and downstream deployment.
Another subtle risk is that a small revert may be misread as a trivial code-style decision rather than a security hardening move. It is not trivial if the earlier direction was introducing avoidabletographic plumbing. That kind of misunderstanding can slow remediation and muddy operational priorities.
A second thing to watch is whether maintainers use this moment to review adjacent crypto-helper code for similar in-place assumptions. Kernel work has a way of revealing nearby design de corrected, and the crypto layer is especially sensitive to hidden buffer-model mismatches. If this CVE prompts a wider audit, the benefit will likely exceed the footprint of the original fix.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
That matters becauslives at a junction where performance tuning can collide with memory-safety discipline. A path that looks elegant on paper can become fragile if it tries to reuse buffers in ways the surrounding subsystem does not actually support. In this case, the engineering judgment appears to have shifted back to a simpler and more defensible model: operate out-of-place, and only preserve the direct copying of associated data.
The record’s wording is also revealing. a classic exploit primitive such as an overrun, use-after-free, or privilege escalation. Instead, it reads like a correctness-driven security fix that removes unnecessary branching and state handling from a sensitive kernel path. That kind of change often lands in the CVE system because the Linux kernel treats reliability and security as intertwined, especially where a bug can turn into memory corruption, undefined behavior, or hard-to-debug cryptographic failures under certain call patterns.
For operators, the important question is not whether this is t makes headlines. It is whether the affected kernel build is in use and whether the vendor backport has landed. With Linux CVEs, especially ones sourced from kernel.org stable commits, the practical exposure window is often defined less by the upstream fix and more by how quickly downstream distributions, appliances, and vendor kernels absorb it. That is why this entry deserves attention even before NVD has assigned a formal severity score.
 What Changed in algif_aead
What Changed in algif_aead
At a technical level, the fix is described as ommit 72548b093ee3. The kernel maintainers evidently concluded that the in-place optimization created complexity without buying meaningful benefit in this path. The source and destination buffers already originate from different mappings, which means the optimization was at best awkward and at worst a maintenance hazard.That is an important design correction because crypto code is one of those areas where the easiest-look the worst lifetime cost. If a subsystem’s input and output are already segregated by memory mappings, forcing them into an in-place model can introduce extra branches, extra state transitions, and more opportunities for mistakes. The published description suggests maintainers decided that direct copying of associated data was the only part worth keeping from the earlier change.
Why out-of-place is simpler
Out-of-place processing is not automatically slower in a meaningful way when the system’s rt support true in-place reuse anyway. In this case, the source and destination do not share the same mapping context, so the “optimization” was more conceptual than practical. Removing it reduces the code path’s cognitive load, which is often a security improvement in itself because simpler kernel logic is easier to reason about, test, and backport.The broader lesson is that less clever code is often safer code in the kernel. When a feature is built on an assumption that does not hold in tmodel, it may still compile, but it will accumulate awkward edge cases that become maintenance debt. CVE-2026-31431 looks like a cleanup of exactly that sort of debt.
- The patch mostly reverts an earlier in-place optimization.
- Associated data copying remains intact.
- The source and destination use different mappings.
- The new plexity in a sensitive kernel path.
Why This Became a CVE
One of the most interesting parts of this record is that it shows how the kernel security process treats correctness issues as security-relevant when they asensitive subsystem. The description does not yet carry a final NVD score, but the vulnerability was still published to the CVE List and added to the NVD dataset, which means it crossed the threshold for public tracking.That is not unusual in Linux kernel land. A bug does not need to be a textbook remote-code-execution case to justify a CVE. If it changes how memory is handled, complicates the integrity of a kernel subsystemlexity to create future exploitability concerns, maintainers and CVE recorders will often treat it as a security issue rather than a mere bug fix. Here, the adjustment appears to be about eliminating a risky design direction before it calcified into a larger problem.
Security relevance without a dramatic exploit
The wording suggests a defensive rollback rather than a hard vulnerability with a neatly described attack chain. That does not make it unimportant. Kernel crypto interfaces are ttrusted plumbing is exactly where maintainers want the least possible ambiguity. A design that invites confusion between in-place and out-of-place handling can become a maintenance trap even if no attacker has yet demonstrated a reliable exploit.This is also the kind of CVE that can look deceptively small to outside observers. Small does not mean irrelevant in kernel engineering. It often means the maintainers caught the issue while the patch could still be narrow, localized, and low-risle branches. That is a good sign, not a reason to ignore it.
- CVEs can cover correctness fixes, not just overt exploits.
- Kernel crypto code is considered security-sensitive by default.
- Narrow patches are often the best outcome in this class of bug.
- A small code simplification can reduce future attack surface.
The
The Linux crypto API is one of the kernel’s deepest plumbing layers, and that makes its bugs especially important even when they do not immediately look like security theater. Authenticated encryption sits at the core of how the kernel handles integrity and ntees, so any issue that disturbs its buffer handling deserves careful treatment. The record for CVE-2026-31431 strongly implies that the earlier in-place model was not actually aligned with the architecture of the path it was trying to optimize.A lot of kernel vulnerabilities begin with the same pattern: a maintainer tries to tighten a path, reduce copies, or reuse memory more aggressively, and then discovers that the abstraction boundary underneath is less forgiving than expected. In crypto code, that can quickly become a question of whether the data andable and auditable. Once that clarity is lost, even a small misstep can have consequences well beyond the original optimization.
Why buffer placement matters
When source and destination come from different mappings, the semantics of “in-place” become murky. What sounds like a local optimization may actually force the kernel to emulate a behavior the hardware or memory model does not naturally provide. The result is extra complexity without a real end-usetly the kind of tradeoff security engineers like to unwind.The patch’s decision to preserve direct copying of associated data while abandoning the rest of the in-place path suggests the maintainers identified a clean dividing line between useful and unnecessary complexity. That is a strong sign the fix is aimed at correctness first and performance second. That order is often the right order in low-level crypt- Crypto paths are highly sensitive to buffer semantics.
- Optimization that fights the memory model is usually a bad bargain.
- Associated data handling was preserved, not discarded.
- Simpler data flow tends to be more auditable.
Enterprise Impact
For enterprise defenders, the question is less about the abstract CVE and more about whether their kernel supply chcted code path. Because this is a Linux kernel issue sourced from kernel.org and already visible in Microsoft’s update guide, it is the kind of record that can surface in mixed-platform vulnerability operations even if the systems thews-based. That visibility matters in organizations that track Linux, Windows, and cloud infrastructure in a single workflow.The business impact is likely to be modest in comparison to a remote exploit or privilege escalation, but “modest” is not the same as “ignorable.” Kernel crypto bugs can create subtle instability, complicate incident response, and force unexpected patch cycles in environments that rely on hardened kernel builds. If the affected path is present in a distro kernel, enterprise administrators should expect vendor backpream source changes to be the real remediation vehicle.
What admins should focus on
The key operational task is validation, not speculation. Teams should confirm whether their supported kernel versions include the fix, and they should verify vendor advisories rather than assuming that a mainline commit means they are covered. In practice, that means checking distro changelogs, appliance bulletins, and any backported security notices tied to the stable references associated with the CVEy important in enterprises that standardize on long-lived kernel streams. Those environments often prioritize compatibility and uptime, which can stretch the time between upstream publication and real-world exposure reduction. That lag is where most operational risk lives.- Confirm whether your vendor kernel includes the backport.
- Check appliance firmware and embedded Linux images, not just servers.
- Treat stable-tree references asl.
- Do not rely solely on CVE text when the severity score is still pending.
Consumer Impact
For most consumer Linux users, CVE-2026-31431 is unlikely to translate into an obvious day-to-day problem. The affected code lives deep inside the kernel crypto stack, not in a visible desktfacing application. That said, consumers should not assume “deep kernel issue” means “no action required,” because ordinary package update flows often carry these fixes silently in the background.The practical reality is that consumer impact will be mediated by wor device vendor ships the kernel. A laptop running a mainstream desktop distro may receive the patch quickly, while an embedded Linux appliance or niche device could remain on an older vendor kernel for much longer. That is why the consumer side of Linux security is often less about immediate exploit drama and more about patch cadence.
Where the risk is highest
The highest consumer risk is usually not on a typical desktop wIt is on devices with slow firmware refresh cycles, limited visibility into kernel provenance, or custom vendor images where the user cannot easily confirm what has been backported. In those cases, the CVE matters because the path to verification is opaque.It is also worth noting that cryptographic plumbing bugs can matter indirectly even if users never interact with the affected interface consciously. Security code tends and layered into other subsystems. A defect that looks niche today can become tomorrow’s support headache if it intersects with another kernel path.
- Desktop users will usually see this only through normal updates.
- Embedded and appliance users may wait longer for backports.
- The biggest concern is visibility into what the vendor actually shipped.
- Crypto-path fixesirectly to broader system reliability.
Historical Pattern: Kernel Reverts as Hardening
This CVE fits a long-running kernel pattern: a change introduces complexity, real-world use shows the complexity is not buying enough value, and the subsystem is simplified again. That cycle is not failure; it is how mature kernel engineering cny cases, the safest patch is a partial rollback that preserves only the useful part of the original idea.The wording here is especially telling because it says the fix “mostly reverts” the earlier commit rather than replacing it wholesale. That suggests the maintainers found one pge worth keeping — the copying of associated data — while deciding the in-place logic was not defensible. That kind of selective reversal is often a sign of thoughtful review rather than panic.
Why reverts are sometimes the right security move
In kernel maintenance, a revert can be stronger than a patch-on-patch approach when the original assumption turns out to be flawed. Instead of layering more conditionals onto britt remove the part that created the brittleness. That reduces maintenance cost, lowers regression risk, and helps future reviewers understand the subsystem’s intended behavior.It also reinforces a larger security truth: complexity is itself an attack surface. Even if no one can yet point to a public exploit, code that performs unnecessary contortions around memory handling is exactly they teams prefer to simplify early.
- Partial reverts are a common kernel hardening tactic.
- Keeping the useful part of a change can preserve performance or correctness.
- Removing unnecessary logic usually improves reviewability.
- Simpler crypto code is easier to trust and easier to support.
NVD Status and Disclosure Timing
At publication time, the NVD entry for CVE-2026-31431 was present but had not yet been fuVSS score. That is not unusual for fresh Linux kernel CVEs, especially when the record is still being built from upstream kernel.org material and stable references. The lack of a score does not mean the issue is unimportant; it means the formal rating process is still catclosure.This timing matters because many organizations still lean on scores as a triage shortcut. When a score is absent, defenders have to lean more heavily on technical context, subsystem criticality, and the patch lineage. In kernel cases like this, that isach anyway, because exposure depends heavily on deployment specifics rather than on a one-size-fits-all rating.
Why publication still matters before scoring
The public CVE record gives administrators and vendors a stable identifier to track through advisories, patch notes, and vulnerability management tools. That identifier is often what makes coordination possible across the Linux ecosystem, especially when the actual fix is already available in upIn other words, the CVE is the coordination layer, even before the score arrives.The record also helps prevent the common mistake of waiting for a polished severity label before taking a look. That delay is often where patch debt starts. For a kernel issue, early awareness is usually more valuable than a tidy score badge.
- NVD enrichment often follows the kernel.org disclosureVSS score does not mean a missing issue.
- CVE IDs are useful for cross-vendor coordination.
- Early awareness is more useful than waiting for a score in many kernel cases.
Strengths and Opportunities
The good news is that this appears to be a narrow, well-contained fix with a clear rationale. That gives Linux maintainers and downstream vendors a relatively easy path to backporting, and it gives operators a straightforward verification strates a healthy willingness to back away from complexity when the architecture does not justify it.- The patch is surgical, not sprawling.
- The fix is easy to explain to administrators.
- Downstream backports should be relatively low ride path is narrow and specific.
- The change reduces cognitive overhead for future maintainers.
- Simpler crypto handling often improves auditability.
- The record reinforces the value of conservative kernel design.
Opportunity for maintainers
Ttunity here for broader review of adjacentalgif_aead logic. Whenever a kernel subsystem decides that one optimization was not worth the complexity, it is a good time to ask whether nearby code makes the same assumption in a slightly different form. That kind of follow-up review often pays dividends in future stability.Another opportunity is educational: this CVE can serve as a reminder that data layout decisions are security decisions. If source and destination mappings are different, the safest representation is usually the one that respects that fact rather than trying to paper over it.
Risks and Concerns
The main concern is that the issue may be underestimated because it does not arrive with an obvious exploit narrative. Kernel fixes that look like clstructural fragility, and security teams sometimes push those into lower-priority buckets too quickly. That would be a mistake here, because the whole point of the revert is to remove complexity that did not belong in the path.A second concern is vendor patch lag. Upstream availability does not guarantee immediate exposure reduction in the real world, especially on long-term-, appliance kernels, or embedded devices. The most persistent risk in kernel CVEs is often the time between upstream fix and downstream deployment.
Practical pitfalls for defenders
Organizations can also trip over the absence of a final CVSS score and assume the item is steality, kernel issues often require a more nuanced triage than a single number can provide. If a system uses the affected kernel branch, the right question is whether the fix is present — not whether the score has arrived yet.Another subtle risk is that a small revert may be misread as a trivial code-style decision rather than a security hardening move. It is not trivial if the earlier direction was introducing avoidabletographic plumbing. That kind of misunderstanding can slow remediation and muddy operational priorities.
- Patch lag is the biggest practical exposure window.
- Missing CVSS data can create false confidence.
- Small reverts can hide important hardening work.
- Embedded and vendor-managed kernels are the hardest to vercrypto plumbing should always be treated cautiously.
- Security teams should validate presence of the fix, not just the CVE label.
Looking Ahead
The next thing to watch is how quickly downstream vendors fold the fix into supported kernel streams. Because the issue is tied to a stable kernel commit trail, it should be relatively straightforward for distributors to ideckport and issue their own advisory language around it. That will matter more than the upstream publication date for most real deployments.A second thing to watch is whether maintainers use this moment to review adjacent crypto-helper code for similar in-place assumptions. Kernel work has a way of revealing nearby design de corrected, and the crypto layer is especially sensitive to hidden buffer-model mismatches. If this CVE prompts a wider audit, the benefit will likely exceed the footprint of the original fix.
What administrators should monitor
- Vendor advisories that mention the backported fix.
- Distro kernel package changelogs.
- Embedded firmware updates that refresh kerlow-on cleanup in related
algif_*crypto paths. - The eventual NVD severity assignment.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center