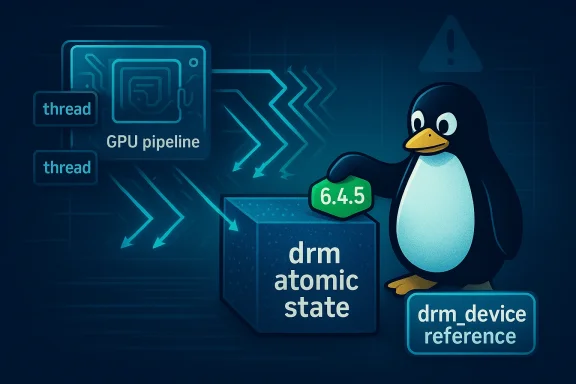
A race in the Linux kernel’s Direct Rendering Manager (DRM) stack — tracked as CVE‑2023‑51043 — can let a nonblocking atomic modeset commit touch freed kernel memory when it races with a driver unload, producing a use‑after‑free that can crash or destabilize systems and has been fixed upstream in the 6.4.5 stable release. (cdn.kernel.org)
Graphics drivers are among the most complex device drivers in the Linux kernel because they must coordinate user requests, long-running operations (page flips, vblank waits), and hardware teardown during hotplug or module removal. The DRM atomic modesetting interface is the modern API drivers use to apply sets of display changes as single, consistent transitions; these operations can be performed synchronously or nonblocking (asynchronous) to avoid stalling user processes. That flexibility, however, increases the kernel’s concurrency surface and creates timing windows that require careful reference‑counting and synchronization. (cdn.kernel.org)
CVE‑2023‑51043 is a textbook example: a nonblocking atomic commit can be queued or run in a context that does not carry a guaranteed reference to the underlying drm_device, and if a driver unload proceeds concurrently, the kernel can free the drm_atomic_state object while the commit work is still in flight. The upstream fix unconditionally grabs a drm_device reference for drm_atomic_state structures to close that window. (cdn.kernel.org)
Why this matters: use‑after‑free faults in kernel drivers are dangerous because they can trigger immediate kernel oops/panic (denial‑of‑service) and, in some contexts, can be leveraged for more severe memory‑corruption outcomes. For CVE‑2023‑51043 the immediate impact is availability loss and potential kernel instability; the practical exploitability depends on the attacker’s ability to orchestrate the specific race and the environment’s exposure surface (local access to the DRM device nodes, untrusted code executing on the host, containerized GPU workloads, etc.).
Why this is a robust fix: reference counting is the canonical kernel technique for managing shared lifetimes across asynchronous contexts. The fix trades a tiny bit of extra reference bookkeeping for strong safety guarantees across the async commit path; it avoids complex locking that could reintroduce deadlock risk during hotunplug sequences. (cdn.kernel.org)
Common vendor responses include:
Security practitioners should therefore prioritize remediation based on exposure: production servers and cloud hosts where GPU devices are accessible to untrusted users deserve immediate patching; single‑user desktops with controlled access remain at lower risk but should still be updated as part of regular maintenance.
This particular defect is fixed upstream and has been folded into distribution updates; operators should treat vendor advisories as the authoritative source of fixed package versions and act according to their operational risk profile and exposure model. (cdn.kernel.org)
Conclusion: the kernel’s DRM atomic race CVE‑2023‑51043 is a high‑impact but patchable flaw. Apply the upstream or vendor fixes, harden GPU device exposure, and continue to monitor for additional DRM concurrency issues as part of routine kernel maintenance and security hygiene. (cdn.kernel.org)
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background
Background
Graphics drivers are among the most complex device drivers in the Linux kernel because they must coordinate user requests, long-running operations (page flips, vblank waits), and hardware teardown during hotplug or module removal. The DRM atomic modesetting interface is the modern API drivers use to apply sets of display changes as single, consistent transitions; these operations can be performed synchronously or nonblocking (asynchronous) to avoid stalling user processes. That flexibility, however, increases the kernel’s concurrency surface and creates timing windows that require careful reference‑counting and synchronization. (cdn.kernel.org)CVE‑2023‑51043 is a textbook example: a nonblocking atomic commit can be queued or run in a context that does not carry a guaranteed reference to the underlying drm_device, and if a driver unload proceeds concurrently, the kernel can free the drm_atomic_state object while the commit work is still in flight. The upstream fix unconditionally grabs a drm_device reference for drm_atomic_state structures to close that window. (cdn.kernel.org)
What exactly was the bug?
At a technical level, the bug lives in drivers/gpu/drm/drm_atomic.c and concerns the lifecycle of a struct drm_atomic_state (the in‑kernel representation of a pending modeset change). Under normal blocking ioctl semantics the calling context implicitly holds a drm_device reference (through the ioctl path), but nonblocking commits were allowed to proceed without explicitly taking and holding that reference. If a hotunplug or driver unload sequence raced with a nonblocking commit, the drm_device and associated state could be freed while the commit’s helper workqueue or later code paths still referenced the now‑freed memory — a classic use‑after‑free (UAF). The patch adds an unconditional drm_device reference to drm_atomic_state to ensure the state remains valid for the commit path. (cdn.kernel.org)Why this matters: use‑after‑free faults in kernel drivers are dangerous because they can trigger immediate kernel oops/panic (denial‑of‑service) and, in some contexts, can be leveraged for more severe memory‑corruption outcomes. For CVE‑2023‑51043 the immediate impact is availability loss and potential kernel instability; the practical exploitability depends on the attacker’s ability to orchestrate the specific race and the environment’s exposure surface (local access to the DRM device nodes, untrusted code executing on the host, containerized GPU workloads, etc.).
Scope and severity
- Affected code: drivers/gpu/drm/drm_atomic.c in Linux kernel releases before 6.4.5.
- Upstream fix: included in the Linux 6.4.5 stable release (the changelog documents Daniel Vetter’s commit that unconditionally references drm_device for drm_atomic_state). (cdn.kernel.org)
- CVSS and risk: NVD records assign a High severity rating (CVSS v3.1 base score 7.0), reflecting high confidentiality, integrity and availability impacts in the assessment used there; the practical attack vector is local and has high complexity because a timed race is required.
How an attacker could (theoretically) abuse it
This vulnerability is not a remote, unauthenticated service‑facing bug — exploitation requires local access to GPU device interfaces and the ability to trigger atomic modeset ioctls, which in many systems means access to /dev/dri/* or to a GPU‑accelerated process. Attack scenarios include:- A local unprivileged user exploiting a setuid or containerized process that has access to DRM device nodes to trigger an asynchronous commit while a privileged driver unload/hotunplug event is triggered (for example via module removal or device unplug sequences). (cdn.kernel.org)
- Malicious or buggy userland components (e.g., containerized GPU workloads, GPU‑accelerated web renderers, or desktop compositors) that deliberately schedule nonblocking commits in tight loops while inducing driver teardown.
- Automated fuzzing (Syzkaller) style sequences that generate the precise interleaving to reproduce a UAF; several DRM UAFs in recent years have been discovered this way and reported to upstream.
The upstream fix (what changed in the code)
The upstream remedy, authored by Daniel Vetter and merged into the 6.4.5 stable release, is straightforward and conservative: ensure every drm_atomic_state grabs and holds a reference to the drm_device for the duration of its lifetime, regardless of whether the commit is blocking or nonblocking. That extra reference prevents the drm_device (and the state that points at it) from being freed while async commit work is in flight. The changelog entry documents both the problem rationale — the drm_dev_unplugged() checks are intentionally racy to avoid deadlocks — and the fix rationale — explicit reference counting to avoid UAF. (cdn.kernel.org)Why this is a robust fix: reference counting is the canonical kernel technique for managing shared lifetimes across asynchronous contexts. The fix trades a tiny bit of extra reference bookkeeping for strong safety guarantees across the async commit path; it avoids complex locking that could reintroduce deadlock risk during hotunplug sequences. (cdn.kernel.org)
Which systems are affected and how vendors reacted
Upstream: kernels prior to 6.4.5. The precise set of affected kernel package versions in a given OS depends on whether maintainers backported the fix into their stable kernel branch or shipped a newer kernel release. Vendor advisories and distribution trackers list the specific fixed package versions for Debian, SUSE, Amazon Linux and other distributions. For example, SUSE enumerated CVE‑2023‑51043 in its kernel support update list and Debian’s security tracker shows the fix applied to multiple release trees. Administrators should consult their distribution’s security advisories and changelogs to identify fixed package numbers.Common vendor responses include:
- Shipping a kernel update that contains the upstream 4e076c7 commit or an equivalent stable backport. (cdn.kernel.org)
- Listing the CVE in standard security advisories with fixed package versions and upgrade instructions.
Practical mitigation and remediation steps
Short term (immediate):- Patch: Install vendor kernel updates that include the fix. For upstream consumers, upgrade to Linux kernel 6.4.5 or later. This is the single most reliable remediation. (cdn.kernel.org)
- If you cannot update immediately, reduce exposure by restricting access to DRM device nodes: remove world‑writable or group access to /dev/dri/* and ensure only trusted users and services can open GPU device nodes. This will limit who can trigger the ioctl paths used by the vulnerability.
- For shared or multi‑tenant hosts (cloud or workstation classrooms), consider revoking GPU access from untrusted containers and processes until you can patch. Use cgroup device whitelists or container runtime options to prevent device node binding.
- Monitor logs: watch for kernel oops messages referencing drm_atomic, drm_atomic_helper_wait_for_vblanks, or similar DRM helper functions; such traces can indicate attempted reproductions or crashes.
- Apply least privilege: ensure display and GPU device access is only granted when necessary and consider runtime policies (SELinux, AppArmor) to further restrict which binaries can make DRM ioctls.
- Use vendor backports: if a vendor provides a backported patch for your kernel branch (common for enterprise distributions), prefer the vendor‑tested package rather than manual upstream merges. Distribution trackers and advisories list those package versions.
- For environments that expose untrusted GPU workloads (e.g., GPU‑accelerated containers, browser GPU acceleration in multiuser setups), evaluate architectural changes to isolate GPU access into dedicated trusted helper processes that can be sandboxed and restarted if compromised.
- Encourage upstream and driver maintainers to keep async commit lifetimes annotated and to run fuzzing/tooling (Syzkaller, KUnit) against DRM paths — many recent DRM UAFs have been found by such tooling.
Why this class of bug keeps appearing in DRM
The DRM subsystem must balance two hard constraints:- Avoid deadlocks and maintain responsiveness during hotunplug/remove sequences (which argues against taking long‑held global locks during ioctl handling).
- Maintain robust lifetime guarantees for objects that cross synchronous and asynchronous execution contexts (which argues for explicit reference counting).
Assessing exploitability: realistic or theoretical?
From the public documentation and upstream patch notes the bug is exploitable only from local code that can invoke nonblocking DRM atomic commits and has some way to trigger or influence a driver unload/hotunplug concurrently. That makes large‑scale remote exploitation unlikely unless an adversary already has local foothold or has control of processes that can access DRM device nodes (for example, in poorly isolated GPU cloud setups or multiuser workstations). NVD and many trackers classify the impact as high but note the attack complexity is high and privileges required are low‑to‑limited — i.e., a local actor with limited privileges can attempt the race but must be able to reach and manipulate the device paths.Security practitioners should therefore prioritize remediation based on exposure: production servers and cloud hosts where GPU devices are accessible to untrusted users deserve immediate patching; single‑user desktops with controlled access remain at lower risk but should still be updated as part of regular maintenance.
What to watch for in kernel/syslog after patching
After you install the kernel update, verify:- The kernel package version matches a fixed release or includes the 4e076c7/6.4.5 change.
- No new kernel oops messages referencing drm_atomic, drm_atomic_helper_wait_for_vblanks, or drm_atomic_state appear.
- On systems where you applied a vendor backport, check vendor advisories and changelog metadata for the CVE entry to confirm the fix was included. Distribution trackers list fixed versions per release tree.
Critical analysis: strengths of the fix, remaining risks
Strengths- The upstream fix is simple, surgical, and low risk: adding explicit reference counting is a well‑understood kernel pattern that avoids complex locking and does not change DRM’s external API or commit semantics. The change has already been merged into the stable kernel and backported by distributors. (cdn.kernel.org)
- The patch addresses the root cause (missing lifetime guarantee) instead of attempting brittle timing mitigations; this reduces the chance of reintroducing the bug under different concurrency scenarios. (cdn.kernel.org)
- The DRM stack is large and historically has seen multiple, distinct UAF and TOCTOU problems. Fixing one lifetime mismatch does not guarantee there are no other racing paths; maintainers must continue to audit and fuzz asynchronous flows. Public KASAN and syzbot reports show other atomic helper UAFs can surface as new kernel versions evolve.
- Systems that cannot be patched quickly (embedded devices, appliances, custom kernels) remain vulnerable until maintainers provide a tested backport or an upgrade path is adopted. Administrators must weigh operational constraints against the availability risk posed by plastic UAFs.
- While the immediate impact is Denial‑of‑Service, the theoretical possibility of escalation to code execution means high‑security environments should be more conservative and expedite updates and device access hardening. Public advisories do not prove code execution is trivial or available in the wild for this particular CVE; that outcome depends on memory layout, mitigations (KASLR, SMEP/SMAP), and the attacker’s local foothold. Treat that escalation potential as a cautionary risk rather than an established exploitation pattern.
Recommended checklist for sysadmins and security teams
- Inventory: identify hosts and kernels where GPU DRM drivers are present and where /dev/dri/* devices are exposed to untrusted users.
- Patch: apply vendor kernel updates that include the 6.4.5 upstream fix or equivalent backports. Prioritize multi‑tenant and server environments. (cdn.kernel.org)
- Harden: restrict device node access, use cgroup device controls, and remove GPU device binding from untrusted containers/processes.
- Monitor: add kernel oops and DRM helper function patterns to your incident monitoring rules. Collect and retain crash logs for post‑patch verification.
- Validate: confirm that your kernel changelog or package metadata shows the upstream commit or vendor advisory entry for CVE‑2023‑51043. Distribution trackers and vendor advisories provide exact package names and versions.
Final thoughts
CVE‑2023‑51043 is a strong reminder that asynchronous device‑driver paths — the parts that improve responsiveness and avoid deadlocks — are also a source of subtle lifetime bugs. The fix is deliberate and follows kernel best practice: when a user‑visible object crosses into asynchronous execution, it must carry its own lifetime guarantee. For defenders, the practical takeaway is straightforward: patch quickly where GPU devices are exposed to untrusted actors, restrict access to device nodes, and treat DRM regressions discovered by fuzzing tools as high‑priority stability and security items.This particular defect is fixed upstream and has been folded into distribution updates; operators should treat vendor advisories as the authoritative source of fixed package versions and act according to their operational risk profile and exposure model. (cdn.kernel.org)
Conclusion: the kernel’s DRM atomic race CVE‑2023‑51043 is a high‑impact but patchable flaw. Apply the upstream or vendor fixes, harden GPU device exposure, and continue to monitor for additional DRM concurrency issues as part of routine kernel maintenance and security hygiene. (cdn.kernel.org)
Source: MSRC Security Update Guide - Microsoft Security Response Center