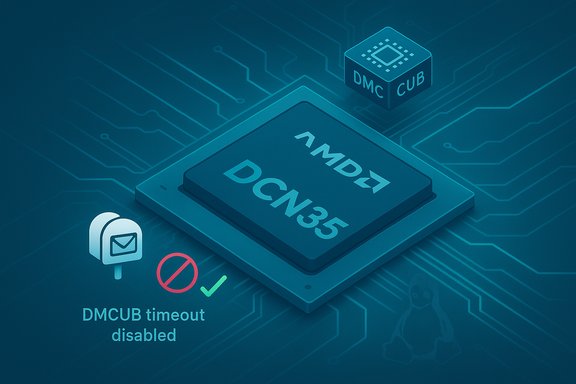
The Linux kernel’s drm/amd/display tree was patched to address CVE-2024-46870 by disabling the DMCUB timeout on DCN35 hardware—a targeted change intended to prevent a deterministic kernel hang that can occur when the display microcontroller takes longer than expected to process commands, potentially leaving the display subsystem in an undefined state and resulting in a local denial-of-service.
Modern AMD GPUs include tiny on-chip microcontrollers (the DMCU family) that offload low-level display sequencing and power-management tasks. These microcontrollers save power by entering idle or low-power states when unused; host drivers communicate with them via mailbox-like interfaces. On DCN35 (Display Core Next 3.5) silicon, maintainers observed that the microcontroller (DMCUB) can sometimes take longer than expected to process certain mailbox commands, which created a hazardous timing window in the driver. That timing window matters because driver code historically used a timeout policy: if a DMCUB command timed out, the driver would log a diagnostic error and attempt to continue. On ASICs without the IPS/advanced power sequencing, that policy is generally safe; on DCN35 with IPS, however, the timeout behavior could produce a race in which the driver attempts to access DCN state while the NIU port or other register domains remained inaccessible. The result could be timeouts, register access failures, or a kernel hang requiring a reboot to recover—an availability impact operators must treat seriously. Multiple distribution and vulnerability trackers classified the issue as medium severity with an availability-first impact, and vendors pushed fixes or backports into their kernel packages after the upstream remedy landed. The community’s interim decision was simple and pragmatic: disable the DMCUB timeout on DCN35 to avoid the hazardous race while maintainers investigate the underlying cause of the longer-than-expected microcontroller latency.
The upstream change is small and low-risk, but the deeper latency cause remains under investigation—so maintain vigilance: confirm vendor package mappings, preserve kernel logs when anomalies occur, and treat shared GPU-exposed infrastructure as the highest-priority remediation vector until all systems are validated as patched.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background
Background
Modern AMD GPUs include tiny on-chip microcontrollers (the DMCU family) that offload low-level display sequencing and power-management tasks. These microcontrollers save power by entering idle or low-power states when unused; host drivers communicate with them via mailbox-like interfaces. On DCN35 (Display Core Next 3.5) silicon, maintainers observed that the microcontroller (DMCUB) can sometimes take longer than expected to process certain mailbox commands, which created a hazardous timing window in the driver. That timing window matters because driver code historically used a timeout policy: if a DMCUB command timed out, the driver would log a diagnostic error and attempt to continue. On ASICs without the IPS/advanced power sequencing, that policy is generally safe; on DCN35 with IPS, however, the timeout behavior could produce a race in which the driver attempts to access DCN state while the NIU port or other register domains remained inaccessible. The result could be timeouts, register access failures, or a kernel hang requiring a reboot to recover—an availability impact operators must treat seriously. Multiple distribution and vulnerability trackers classified the issue as medium severity with an availability-first impact, and vendors pushed fixes or backports into their kernel packages after the upstream remedy landed. The community’s interim decision was simple and pragmatic: disable the DMCUB timeout on DCN35 to avoid the hazardous race while maintainers investigate the underlying cause of the longer-than-expected microcontroller latency. What exactly was fixed
At the technical level, the remediation is surgical: the kernel change disables the DMCUB command timeout path for DCN35 hardware so the driver will not abort a mailbox request (and then proceed under unsafe assumptions) when DMCUB responses are delayed. The upstream rationale is pragmatic—eliminate the fragile “fail-and-continue” branch that can leave clock or register domains in an inconsistent state, and avoid invoking code that expects the DCN to be reachable while it may not be. Disabling the timeout avoids that race and restores robust progressability of display sequencing on affected hardware. Upstream commit references and stable-tree backports were recorded in vulnerability databases and kernel trees; vendors tracked and mapped those commits into distribution kernel packages and advisories. Where available, distribution security notices list which kernel package versions include the remediation. Operators should rely on vendor changelogs and package metadata to confirm whether a given kernel build contains the upstream commit(s).Why this is primarily an availability issue
This is not a memory-corruption, privilege-escalation, or code-execution bug. The observable fault is a deterministic hang or driver deadlock that affects availability: the kernel display driver may block while waiting for a microcontroller response that does not arrive in time, or subsequent register accesses may timeout because the hardware’s NIU port or clock domain is disabled. Those states often manifest as pageflip timeouts, compositor crashes, or even host reboots in worst-case sequences. The technical root cause is a power-state / timing race—one of the more insidious classes of faults in display and embedded controller interactions. Practically, the attack vector is local: a user or process able to interact with DRM device nodes (/dev/dri/*) or otherwise exercise display configuration operations (hot-plug, modesetting, MST hub activity) can trigger the problematic path. That makes the issue particularly relevant for multi-user systems, CI runners, VDI environments, or cloud/virtual hosts that expose GPU devices to untrusted tenants. For single-user desktops with well-behaved hardware, the probability of accidentally hitting the corner case is lower, though not zero.Technical analysis: how the race arises and why disabling the timeout helps
The hardware/software contract
DMCUB executes display-level microcode on the GPU and sometimes sleeps to save power. The host driver issues commands using mailbox interfaces and expects timely responses. If the microcontroller is asleep or takes longer than expected, the driver must either wait safely (with correct wake sequence semantics) or avoid assuming the hardware is fully accessible. On DCN35, a mismatch between the driver’s timeout policy and the microcontroller’s behavior created a window where the driver might believe the DCN was usable while it was not.The dangerous path
When the driver logs and continues on a mailbox timeout, subsequent code may attempt register writes or read operations on DCN blocks (clock selection, NIU port accesses). If the underlying hardware domain is inaccessible or transitioning power states, those accesses can timeout or hang; because these operations often run under kernel locks or privileged contexts, the effect cascades into kernel stalls or watchdog-triggered reboots. The disabling-of-timeout approach prevents the driver from taking the “continue with a logged error” branch that set up this cascade.Why this change is low-risk and pragmatic
Disabling a timeout is conservative: it trades a strict enforcement behavior (abort when response is slow) for a policy that avoids continuing into unsafe code paths. Upstream maintainers flagged this as an immediate mitigation to remove the hang while they investigate the deeper cause of the DMCUB latency. Because the change affects only DCN35 timeout behavior and is localized, it is straightforward to backport into stable kernel branches and vendor kernels with minimal regression surface—exactly the type of surgical fix kernel maintainers prefer for hardware sequencing issues.Practical impact: who should prioritize patching
- Single-user desktops and laptops: moderate priority. If you run a single-user desktop and you don’t expose /dev/dri to unprivileged users or containers, the practical risk is lower. However, users with docking stations, MST hubs, or frequent hot-plug events should update sooner rather than later because link training or sink behavior can increase the chance of hitting a timing edge.
- Multi-user workstations, VDI hosts, CI runners, and cloud images: high priority. Any environment that exposes GPU devices to multiple tenants or untrusted jobs should treat this as a meaningful denial-of-service primitive until patched. The deterministic nature of the hang makes it attractive for targeted disruption.
- Embedded devices and OEM kernels: critical attention required. Vendor-supplied kernels and long-tail embedded images often lag upstream; these devices may not receive the backport promptly and can remain exposed for months. Track vendor advisories for embedded platforms and schedule vendor-supplied updates or rebuild images with the upstream commit cherry-picked where appropriate.
Detection and forensic indicators
When hunting for hits or verifying post-incident state, look for these artifacts in system logs and monitoring channels:- Kernel log lines referencing DMUB, DMCUB, mailbox timeouts, or explicit DCN/NIU register access timeouts.
- Repeated “Pageflip timed out” messages from the DRM subsystem or compositor crashes (Wayland/Xwayland) correlated with hot-plug or mode-change events.
- Driver resets and amdgpu watchdog traces showing the driver blocked in DC sequencing code. Preserve dmesg and serial console logs for triage.
- Check kernel version: uname -r.
- Confirm amdgpu is loaded: lsmod | grep amdgpu.
- Inspect DRM device nodes’ permissions: ls -l /dev/dri/*.
- Scan journalctl -k and dmesg for amdgpu/DMUB/DMCUB timeouts or pageflip messages.
Remediation and mitigation guidance
Primary remediation
Install the vendor/distribution kernel update that contains the upstream commit disabling the DMCUB timeout for DCN35, then reboot into the patched kernel. Kernel-level code changes require a reboot to take effect, and package changelogs should be inspected to ensure the correct stable commit is present in the kernel package you install. Use your distribution security tracker or vendor advisory to map CVE-2024-46870 to package versions.If you cannot patch immediately — compensating controls
- Restrict access to DRM device nodes: implement udev rules that limit /dev/dri/* to trusted groups and remove passthrough to untrusted containers. This reduces the local attack surface.
- Avoid exposing GPU devices via passthrough (--device=/dev/dri) to untrusted workloads or guests until patched.
- Harden container runtimes: drop unnecessary capabilities and do not allow module loading for non-admin accounts.
- Increase monitoring and alerting for amdgpu-related kernel oops, pageflip timeouts, and repeated resets to detect attempted exploitation early.
Verification after patching
- Reboot into the patched kernel and rerun representative display sequences: hot-plug, docking, MST hub usage, and compositor stress tests.
- Monitor kernel logs for the absence of DMCUB/DMUB mailbox timeouts and amdgpu watchdog entries over a representative window (24–72 hours recommended for intermittent issues).
- Confirm the kernel package changelog or vendor advisory lists CVE-2024-46870 or the upstream commit IDs.
Patch availability and vendor mapping
Multiple distributions and trackers recorded CVE-2024-46870 and mapped the upstream commit into their kernel packages. Upstream stable-tree commits are referenced in OSV/NVD entries, and vendors such as Ubuntu, SUSE, Debian, and cloud providers reflected the remediation in security notices or package updates. However, package names and fixed versions differ by distribution and kernel series; vendors may backport the change into different stable branches depending on their release policy. Always consult the distro or vendor security tracker and the kernel package changelog to confirm the presence of the fix before declaring systems remediated.Risk assessment: strengths and residual concerns
Strengths of the upstream response
- The fix is deliberately narrow and low-risk: disabling a timeout for a specific hardware generation is conservative and easy to backport, minimizing regression probability. This helped vendors ship updates quickly.
- The Linux kernel community and distribution maintainers coordinated mapping and advisories so administrators can identify affected packages and plan rollouts efficiently.
Residual risks and caveats
- Vendor lag in the long tail: embedded images, OEM kernels, and vendor-supplied appliances may not receive backports promptly; those devices can remain vulnerable for extended periods. Treat the long tail as the dominant exposure risk.
- Exposure by configuration: environments that deliberately mount /dev/dri into untrusted containers, or provide GPU passthrough to many tenants, remain high-risk until all hosts are patched. The deterministic hang primitive is attractive for disruption in such settings.
- Detection blind spots: If hosts do not preserve kernel logs, serial console captures, or crash dumps, repeated exploitation attempts may go unnoticed. Preserve logs whenever you see related symptoms.
Incident response checklist (concise and actionable)
- Inventory: enumerate hosts with amdgpu loaded and /dev/dri accessible (uname -r; lsmod | grep amdgpu; ls -l /dev/dri/*).
- Prioritize: schedule immediate patches for multi-tenant hosts, VDI, CI runners, and shared workstations.
- Patch: apply vendor kernel updates that include the upstream commit mapped to CVE-2024-46870; reboot hosts.
- Compensate if needed: restrict /dev/dri access, remove GPU passthrough for untrusted guests, and harden container capabilities.
- Verify: reproduce representative display activity post-patch and watch logs for 24–72 hours to confirm absence of DMCUB/DMUB timeouts.
Caveats and unverifiable aspects
The upstream mitigation intentionally avoids addressing the root cause—why DMCUB sometimes takes longer than expected on DCN35—opting instead to disable the timeout to prevent immediate hangs. That means the underlying latency behavior remains under investigation; the long-term fix may require deeper firmware or hardware policy changes. Administrators should treat the timeout disable as a robust short-to-medium-term mitigation but monitor vendor channels for additional follow-ups that may alter behavior or require firmware updates. This root-cause work was not fully disclosed in public advisories and remains an investigatory item for hardware/firmware teams. Additionally, the precise commit IDs and the mapping into every vendor kernel package vary; while upstream and multiple vendors listed fixes and backports, verification requires checking the package changelog for each distribution or contacting vendor support if package metadata is inconclusive. Do not assume a kernel upgrade is sufficient without confirming the presence of the specific remediation commit for CVE-2024-46870.Conclusion
CVE-2024-46870 is a pragmatic, availability-centric fix addressing a race between the Linux kernel driver and the DMCUB microcontroller on DCN35 hardware. The upstream remedy—disabling the DMCUB timeout on DCN35—reduces the chance of a deterministic kernel hang by removing a fragile “log-and-continue” path that could leave DCN domains inaccessible. Operators should prioritize patching hosts that expose AMD GPUs to untrusted users or tenants, use compensating controls where immediate patching is impractical, and verify post-patch behavior using kernel logs and representative display workloads.The upstream change is small and low-risk, but the deeper latency cause remains under investigation—so maintain vigilance: confirm vendor package mappings, preserve kernel logs when anomalies occur, and treat shared GPU-exposed infrastructure as the highest-priority remediation vector until all systems are validated as patched.
Source: MSRC Security Update Guide - Microsoft Security Response Center