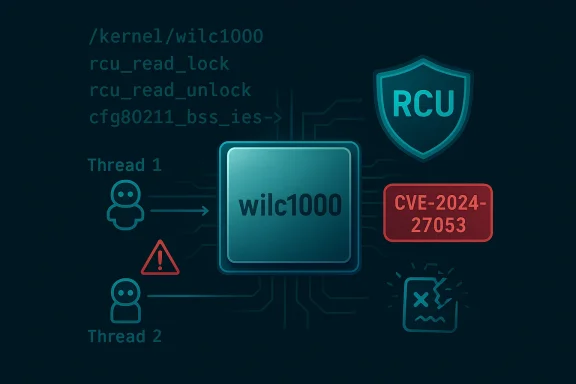
A subtle misuse of the Linux kernel’s Read-Copy-Update (RCU) primitives in the WILC1000 Wi‑Fi driver has surfaced as CVE-2024-27053, a high‑severity flaw that can lead to sustained or persistent denial‑of‑service for affected systems and — under specific race conditions — risks more serious memory-corruption outcomes. The bug stems from dereferencing an RCU-protected pointer in the Wi‑Fi connection path outside an RCU read critical section; upstream patches address the issue by constraining the RCU-protected window to only the minimal work required to safely copy IEs (information elements) instead of wrapping the entire parsing routine. Systems shipping the vulnerable wilc1000 driver should be considered at elevated risk until patched; the practical mitigation is a kernel update or device vendor firmware update that contains the fix.
The WILC1000 (wilc1000) driver supports certain Microchip/Atmel Wi‑Fi chips used in embedded Linux devices and some small form-factor systems. The affected code sits in drivers/net/wireless/microchip/wilc1000, specifically in the hif.c unit where join/connect path processing takes place. During connection setup, the kernel parses the target BSS’s IEs — a variable-length blob of data describing capabilities, security parameters, and more — using helper functions that access a cfg80211_bss structure linked via an RCU pointer.
RCU (Read-Copy-Update) is a synchronization mechanism widely used in the Linux kernel to allow readers to traverse shared data structures without taking heavy locks, while writers perform updates with minimal contention. Proper RCU usage requires that any dereference of an RCU-protected pointer takes place while the caller is in an RCU read-side critical section (for example, bracketed by rcu_read_lock() / rcu_read_unlock()), or that the code uses the specialized rcu*dereference** helpers when the call context guarantees safe use. When RCU usage rules are violated, the kernel’s lock validator (lockdep) and runtime checks may trigger warnings; worse, races can produce use-after-free, out-of-bounds access, or crashes.
The change that triggered the issue came during a refactor of the wilc1000 driver’s list-management approach: at one point SRCU (Sleepable RCU) handling was converted to ordinary RCU, which simplified some paths but introduced subtle contexts where RCU readers could end up calling blocking operations or otherwise violate RCU semantics. The specific CVE arises not from the conversion itself but from a dereference performed while not in an RCU critical section, observed in the join/connect parsing routine.
If a vendor has not published an update for a device that uses the WILC1000 chip, operators must assume the device remains vulnerable until an update is provided or an acceptable mitigation is put in place.
The wilc1000 RCU bug is a textbook example of how a small concurrency mistake in a device driver can translate directly into high-severity operational risk. The fix is small and well-scoped, but the operational challenge is getting that fix into every kernel image and firmware image that powers real-world devices. Prompt patching and sensible mitigations will remove the immediate danger; in the longer term, this CVE should encourage driver maintainers and integrators to bake stronger concurrency verification into their development and release pipelines so similar mistakes are caught long before code reaches production.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background
Background
The WILC1000 (wilc1000) driver supports certain Microchip/Atmel Wi‑Fi chips used in embedded Linux devices and some small form-factor systems. The affected code sits in drivers/net/wireless/microchip/wilc1000, specifically in the hif.c unit where join/connect path processing takes place. During connection setup, the kernel parses the target BSS’s IEs — a variable-length blob of data describing capabilities, security parameters, and more — using helper functions that access a cfg80211_bss structure linked via an RCU pointer.RCU (Read-Copy-Update) is a synchronization mechanism widely used in the Linux kernel to allow readers to traverse shared data structures without taking heavy locks, while writers perform updates with minimal contention. Proper RCU usage requires that any dereference of an RCU-protected pointer takes place while the caller is in an RCU read-side critical section (for example, bracketed by rcu_read_lock() / rcu_read_unlock()), or that the code uses the specialized rcu*dereference** helpers when the call context guarantees safe use. When RCU usage rules are violated, the kernel’s lock validator (lockdep) and runtime checks may trigger warnings; worse, races can produce use-after-free, out-of-bounds access, or crashes.
The change that triggered the issue came during a refactor of the wilc1000 driver’s list-management approach: at one point SRCU (Sleepable RCU) handling was converted to ordinary RCU, which simplified some paths but introduced subtle contexts where RCU readers could end up calling blocking operations or otherwise violate RCU semantics. The specific CVE arises not from the conversion itself but from a dereference performed while not in an RCU critical section, observed in the join/connect parsing routine.
What exactly is wrong: a concise technical summary
- The affected function is the join/connection parser that inspects cfg80211_bss IEs: the code reads a pointer to struct cfg80211_bss_ies via an RCU dereference.
- That pointer dereference happens outside an RCU read-side critical section, which is semantically incorrect and provokes lockdep “suspicious RCU usage” warnings when runtime RCU checking is enabled.
- The practical risk from that incorrect dereference is a race: while the code assumes the IEs pointer remains valid, another thread or CPU could free or update that memory, producing memory corruption, out-of-bounds reads, or kernel oops/crashes — all of which map to denial of service for the affected system.
- Upstream fixes do not blanket the entire parsing function with an RCU critical section; instead, they narrow the protected region to the minimal area needed to copy out the IEs into a local buffer. This minimizes the time spent in RCU read critical section and reduces the risk of introducing other locking or blocking problems.
Why this matters: impact and severity
CVE-2024-27053 is classified with a high severity rating (CVSS around 9.1 in published advisories). That score reflects a combination of factors:- Attack vector: The issue sits in the Wi‑Fi connect path and can be triggered when the kernel parses connection target parameters; vendors and advisories assessed the attack vector as network‑accessible in the sense that it involves wireless connection operations.
- Attack complexity: The flaw is a straightforward RCU misusage. Triggering it reliably in a wild environment may require timing conditions, but fuzzing tools and runtime checkers (lockdep, syzbot) can and did find the unstable code path.
- Privileges required: Published vectors treat the condition as exploitable without elevated privileges in certain contexts; however, exploitation scenarios vary depending on the environment (embedded devices vs. full distributions) and the userspace component that invokes cfg80211 connect operations.
- Consequence: The primary consequence is denial of availability — a kernel crash or persistent instability that prevents normal network connectivity or requires a reboot to recover. In extreme races, memory corruption could open the door to more severe escalations. Repeated exploitation could cause sustained unavailability for network services or devices relying on the Wi‑Fi interface.
- Embedded gateways, routers, or IoT devices using WILC1000 hardware may be taken offline by crafted network inputs or by malformed connection attempts.
- Laptops or SBCs (single-board computers) that include the wilc1000 driver in their kernel may see local or remote attempts to disturb connection setup and thereby deny new connections.
- Systems performing automated connection management via wpa_supplicant or other userspace daemons can reach the problematic kernel path repeatedly, increasing the chances of triggering the race.
Exploitability and realistic attack scenarios
It helps to separate theoretical reachability from practical attack paths:- In many Linux deployments, the connect path is exercised by userspace processes with sufficient privileges (for example, network managers or background daemons). An attacker who can coerce such a userspace component to issue connect requests can push the kernel down the vulnerable path. Whether that can be done remotely depends on local configuration and whether the device exposes services that allow remote trigger of connect operations.
- Some advisory assessments and distribution CVEs list the vector as network-based, reflecting the fact that the problem occurs while parsing IEs that originate from a BSS description — which in turn comes from wireless management frames or netlink messages. In practice, a remote attacker on the same wireless medium may be able to craft frames or manipulate association parameters to influence the parsing routine.
- Automated fuzzing (e.g., syzbot) and static/dynamic analysis flagged this code path already; those tools show that exploitation is plausible even if a polished public proof-of-concept was not widely published at the time of vendor advisories.
The upstream fix: what changed in the code
Upstream maintainers addressed the issue with a small, surgical change:- Instead of dereferencing the RCU pointer and then parsing IEs while outside of an RCU read critical section, the patched code enters an RCU read-side critical section only long enough to safely copy the IE data into a local buffer.
- Parsing and any more complex processing then happen on the local copy, outside the RCU read-side critical section. This reduces the window of RCU protection to the necessary minimum and avoids holding RCU read locks during potentially blocking or long operations.
- A parallel theme in the driver’s broader history: there have been attempts to convert some list management from SRCU to RCU; parts of that conversion were later reverted for correctness, because SRCU’s different semantics are sometimes necessary when readers might sleep or when code must perform blocking operations while referencing list elements.
Vendor and distribution response
Major Linux distributions and downstream vendors moved quickly to incorporate the upstream patch into stable kernel trees and to release security updates for affected kernel branches. Patch notifications and distribution advisories were published, and the typical guidance is:- Update the kernel package to a release that contains the wilc1000 RCU fix for your distribution and kernel branch.
- Reboot the device after the kernel update to ensure the new kernel is running and the driver is reloaded with the fix.
If a vendor has not published an update for a device that uses the WILC1000 chip, operators must assume the device remains vulnerable until an update is provided or an acceptable mitigation is put in place.
Practical mitigation and remediation steps (for administrators)
- Prioritize updates
- Identify systems that include the wilc1000 driver (check kernel config/modules or dmesg output for wilc1000 references).
- Treat systems with the driver as high-priority for kernel updates or vendor firmware updates.
- Apply vendor/distribution patches immediately
- Install the updated kernel package that includes the fix for CVE‑2024‑27053.
- Reboot the machine after installing the kernel update so the new kernel and driver are active.
- If patching is not possible immediately, consider temporary mitigations
- For devices where kernel updates are not available, consider disabling the wireless interface or blacklisting the wilc1000 driver module to prevent the vulnerable code from being used. Be aware that blacklisting will remove wireless capability entirely for that hardware.
- If the device uses network management services that automatically attempt connections (for example, a rogue user or misconfigured service), restrict or stop those services temporarily.
- Place vulnerable devices behind network controls that limit wireless exposure: use radio-frequency (RF) controls, isolate the device’s wireless from sensitive networks, or require explicit administrative approval for connections.
- Audit logs and monitor for unusual crashes or reboots
- The vulnerability can lead to kernel oopses and unpredictable reboots. Monitor system logs for signs of crashes, warnings from lockdep, and repeated wireless connection failures.
- If you observe repeated crashes consistent with the described call chain (connect → cfg80211_connect → wilc_parse_join_bss_param), treat that as evidence of attempted exploitation or accidental triggering.
- Coordinate with vendors for embedded devices
- For embedded devices or appliances, reach out to the device vendor for firmware updates or formal guidance. Many vendors will release device-specific kernel packages or firmware images that include the upstream fix.
Developer guidance: avoiding RCU mistakes in drivers
This vulnerability is a clear example of how subtle concurrency primitives can cause high-impact bugs in kernel drivers. Key takeaways for driver authors and maintainers:- Understand the semantics of RCU vs SRCU: RCU readers must not call blocking operations or perform actions that could sleep. If the read-side might sleep, SRCU or other mechanisms are the correct choice.
- Minimize RCU critical sections: do the smallest possible amount of work while in rcu_read_lock(); copy or snapshot the data needed and then operate on the copy.
- Use the appropriate rcu*dereference** helpers matching the lock context (for example, rcu_dereference_rtnl() when under rtnl lock).
- Run lockdep and static/runtime race detectors (and fuzzers like syzbot) in CI or during driver validation; these tools frequently catch suspicious RCU usage that’s easy to miss in review.
- When performing refactors (for instance, changing from SRCU to RCU), re-evaluate all call paths for sleep, blocking, or potential nested operations that invalidate simpler RCU semantics. A conversion that simplifies code may nonetheless introduce unsafe assumptions.
Risk assessment and long‑term implications
- Short term: the risk is concrete and actionable. A kernel crash or persistent denial of service for devices with the WILC1000 hardware is a plausible, practical outcome of the bug. The immediate remediation — kernel or firmware update — is straightforward for systems that can be patched.
- Medium term: the incident underscores the fragility of concurrency in complex kernel code and the need for cautious refactors. RCU complexity will remain a recurring source of subtle bugs, particularly in drivers that must balance performance (low locking overhead) against correctness.
- Attack surface: because the flaw occurs in networking code, an attacker with sufficient proximity or ability to dispatch crafted frames, netlink messages, or induce connect attempts could leverage it. Organizations with embedded fleets or exposed wireless infrastructure should prioritize inventorying affected devices.
- Mitigation difficulty: where devices cannot be updated (end-of-life appliances, deeply embedded systems), operators face difficult choices: remove wireless capability, isolate devices, or accept residual risk. That disparity amplifies the operational impact beyond the kernel patch itself.
How to verify you’re no longer vulnerable
- Check kernel changelogs: look for kernel fixes that mention “wilc1000” and “RCU” or reference the join/connect parsing fix. Distribution security advisories will list CVE‑2024‑27053 if they shipped an affected kernel.
- Inspect your running kernel: confirm the kernel version or revision includes the patch. On systems that cannot easily be patched, consider temporarily blacklisting the module and observing whether the problem disappears.
- Watch for lockdep warnings: if lockdep is enabled on a test system, the earlier problematic code emitted “suspicious RCU usage” messages referencing wilc_parse_join_bss_param; absence of those messages after patching is a positive sign.
- Test on a non‑production sandbox: reproduce connect attempts and watch dmesg for the relevant call chain. Do not attempt intrusive testing on production infrastructure without prior authorization.
Final recommendations
- Immediately apply kernel updates provided by your Linux distribution or device vendor that explicitly mention the WILC1000 fix for RCU usage. Reboot to ensure the patched kernel is active.
- For embedded fleets, contact hardware vendors for firmware or kernel updates; escalate within vendor support channels if a fix is not available.
- Where updates are delayed or impossible, enforce mitigations such as driver blacklisting or network isolation to reduce exposure.
- Use this incident to strengthen pre-release validation: enable lockdep and RCU runtime checks in development kernels, and incorporate fuzzing and CI checks for concurrency-sensitive components.
- Maintain an accurate hardware inventory so that future driver vulnerabilities can be triaged and remediated quickly across all affected assets.
The wilc1000 RCU bug is a textbook example of how a small concurrency mistake in a device driver can translate directly into high-severity operational risk. The fix is small and well-scoped, but the operational challenge is getting that fix into every kernel image and firmware image that powers real-world devices. Prompt patching and sensible mitigations will remove the immediate danger; in the longer term, this CVE should encourage driver maintainers and integrators to bake stronger concurrency verification into their development and release pipelines so similar mistakes are caught long before code reaches production.
Source: MSRC Security Update Guide - Microsoft Security Response Center