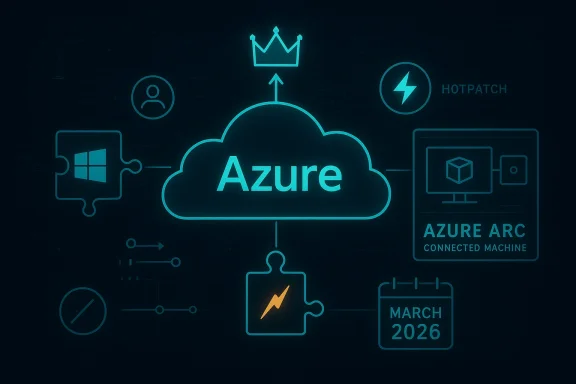
Microsoft’s March 13, 2026 Azure update landed in a year when cloud operators are already under pressure to balance velocity, resilience, and security, and the latest servicing wave shows why that balance keeps getting harder. The update set is not just about a single product: it sits inside a broader Microsoft March patch cycle that included multiple high-impact Windows and Azure fixes, from hotpatchable RRAS vulnerabilities to new cloud and hybrid-workload issues. For enterprises, the significance is less about any one bulletin and more about the emerging pattern: Azure and Windows are increasingly being serviced as one operational surface, with identity, networking, containers, and automation all tied together in ways that raise both the stakes and the complexity of patch management. rate cycle arrived against a backdrop of intensified cloud-security scrutiny, especially around identity-adjacent services, hybrid management extensions, and the control planes that glue Azure workloads to Windows infrastructure. The March Patch Tuesday wave included issues across Windows, .NET, Office, Azure services, and newer AI-adjacent components, signaling that Microsoft’s attack surface is no longer neatly divided between “cloud” and “endpoint.” That matters because defenders do not patch those domains separately in real life; they triage them as a shared risk budget.
The Azure-related disclosures in the Marathey reflect a familiar but increasingly urgent trend: cloud platform features are being targeted not only for remote compromise, but also for privilege escalation after initial access. That includes Azure Compute Gallery, Azure IoT Explorer, Azure Arc hybrid components, and experimental or early-stage tooling like Azure MCP Server Tools. In other words, the risk profile is not merely “internet-facing service got hacked”; it is often “an authenticated foothold became a route to deeper control.”
At the same time, Microsoft’s update strategy is becoming more differentiated. Some dle others arrive as out-of-band hotpatches designed to reduce downtime for enterprise estates that can least afford restarts. That is a significant change in how Microsoft is asking organizations to think about security operations: not just “apply the patch,” but “apply the right patch path for this workload, this ring, and this uptime constraint.”
The Fathom issue context also matters because the publication’s recent coverage has repeatedly highlighted the strain on instip technical, and organizational stability under pressure. The broader arc is clear even when the specific article cannot be fully extracted here: cloud updates are no longer narrow product notes; they are political economy stories about dependence, trust, and infrastructure risk. That lens is especially relevant to Azure, whose services increasingly underpin both enterprise productivity and critical digital services.
Azure has become the layer where many organizations discover that their “cloud” is really a federation of identities, Aoweakness in one component can cascade across governance, deployment, and data access, especially when the affected service sits close to automation or hybrid administration. The March 2026 cycle reinforces that reality.
Azure Compute Gallery’s permissive-regex flaw is a classic example of how input validation mistakes can become escalation vectors. Azure Arc’s hybrid worker extension, meanwhile, underscores how on-host agents and extensions have become strategic choke points in cloud administration. Both cases imeter; it is a moving set of privileged software components embedded in customer estates.
This kind of flaw is especially dangerous in a service that manages images and deployment workflows because those workflows often sit close to automation accounts. If the exploiauthenticated user a higher privilege state, the result can be lateral movement into more sensitive Azure resources. That makes remediation urgent even when the bug appears local or niche.
IoT tooling tends to collect, render, or transport device metadata, credentials, and telemetry. That makes any cleartext exposure or authentication weakness especially troubling because the tool may be used in staging, production-adjacent, or partner-managed environments. A flaw in the interface can therefore become a flaw in the operational supply chain.
The security challenge is that such tools are often treated as benign because they are not the primary production service. That mindset is risky. When a diagnostic utility can leak data or mishandle authentication, it becomes part of the threat surface juckend it queries. In cloud operations, the helper app can be the weak link.*
The risk is amplified by the fact that MCP-style tooling is meant to bridge natural-language or agent actions to real systems. Those bridges are powerful, but they also compress several layers of intent, authorization, and network trust into a very small number of calls. That compression is efficient — and dangerous.
For Azure-adjacent teams, the lesson is simple: if Microsoft can move quickly on a high-risk networking issue, it may do the same elsewhere when the exploitation potential is serious enough. Organizations therefore need deployment processes that can absorb sudden, out-of-band changes without chaos. Speed becomes a requirement, not a luxury.
This means patch prioritization cannot be based only on severity scores. It has to reflect role in the environment, exposure to privileged automation, and the likelihood that a flaw can be chained with other weaknesses. The March cycle is a reminder that context beats classification.
That creates an opening for competitors to emphasize lower-complexity architectures, fewer moving parts, or stronger defaults. Yet the market reality is that enterprises often need Microsoft’s breadth, so the question becomes not whether to avoid complexity entirely, but whether Microsoft can keep reducing the risk premium attached to using it. That remains an open contest.
The other thing to watch is whether Microsoft keeps extending hotpatch-style remediation to more of its security surface. If it does, enterprise operators may gain the ability to close serious gaps without disruptive restarts. But that only works if customers can identify eligible systems quickly and trust their deployment pipelines enough to use thehaonal discipline around it.*
Source: Fathom Journal Fathom - For a deeper understanding of Israel, the region, and global antisemitism
The Azure-related disclosures in the Marathey reflect a familiar but increasingly urgent trend: cloud platform features are being targeted not only for remote compromise, but also for privilege escalation after initial access. That includes Azure Compute Gallery, Azure IoT Explorer, Azure Arc hybrid components, and experimental or early-stage tooling like Azure MCP Server Tools. In other words, the risk profile is not merely “internet-facing service got hacked”; it is often “an authenticated foothold became a route to deeper control.”
At the same time, Microsoft’s update strategy is becoming more differentiated. Some dle others arrive as out-of-band hotpatches designed to reduce downtime for enterprise estates that can least afford restarts. That is a significant change in how Microsoft is asking organizations to think about security operations: not just “apply the patch,” but “apply the right patch path for this workload, this ring, and this uptime constraint.”
The Fathom issue context also matters because the publication’s recent coverage has repeatedly highlighted the strain on instip technical, and organizational stability under pressure. The broader arc is clear even when the specific article cannot be fully extracted here: cloud updates are no longer narrow product notes; they are political economy stories about dependence, trust, and infrastructure risk. That lens is especially relevant to Azure, whose services increasingly underpin both enterprise productivity and critical digital services.
 Why Azure updates now matter more than ever
Why Azure updates now matter more than ever
Azure has become the layer where many organizations discover that their “cloud” is really a federation of identities, Aoweakness in one component can cascade across governance, deployment, and data access, especially when the affected service sits close to automation or hybrid administration. The March 2026 cycle reinforces that reality.- Identity and privilege are still the core prizes.
- Hybrid management tools are now frequent attack paths.
- Operational friction is part of the security calculation.
- Hotpatching is becoming ie services** are no longer isolated from Windows patching rhythms.
The March 2026 Azure Security Pattern
The most revealing aspect of the March 2026 Azure-related disclosures is not any one headline but the pattern they form. Microsoft’s cloud and hybrid ecosystem is showing repeated weakness in places where trusted administrative pathways meet complex validation logic. That is a dangerous combination because attackers do not need to defeat the whole platform; they only need to exploit the trust boundary that was assumed to be safe.Privilege escalation remains the dominant theme
Several March entries point to elevation-of-privilege flaws, including Azure Compute Gallery and Azure Arc hybrid worker extension issues. This is important because privilege escalation is often the so domain-wide incident or a cloud-wide compromise. It is the part of the intrusion chain where the attacker stops being a guest and starts acting like an administrator.Azure Compute Gallery’s permissive-regex flaw is a classic example of how input validation mistakes can become escalation vectors. Azure Arc’s hybrid worker extension, meanwhile, underscores how on-host agents and extensions have become strategic choke points in cloud administration. Both cases imeter; it is a moving set of privileged software components embedded in customer estates.
Why this is a defender’s headache
These bugs are hard because they often live in software that administrators trust implicitly. They also tend to be discovered late, after an attacker has already established some degree of access. That makes the remediation story more complicated than a simple “close the port” instruction. *Operateof blast radius, not just CVSS scores.- Attackers gain value by chaining flaws.
- Admin tooling is especially sensitive.
- Hybrid agents are high-trust software.
- Validation bugs are easy to underestimate.
- The post-exploitation phase is where damage multiplies.
Azure Arc and the Hybrid Control Plane
Azure Arc continues to represent one of Microsoft’s most ambitious ideas: extend Azure management to seds outside the core cloud. That ambition brings convenience, but it also enlarges the security surface in exactly the places where enterprises are most fragmented. The March 2026 Arc-related disclosures suggest that the hybrid control plane is now a prime target.The Connected Machine agent as a trust anchor
Azure Arc’s Connected Machine agent, commonly packaged as azcmagent, is the host-side component that links machines back to Azure management. That makes it a trust anchor, but also a high-value target because compromise there can expose both local and cloud resources. A flaw in that layer is not merely a host bug; it is a potential bridge into centralized managemeneecome a pivot point. If an attacker can manipulate the agent’s behavior, they may gain opportunities to affect permissions, deploy rogue actions, or interfere with policy enforcement. This is why hybrid managers should be treated as production-critical software, not as optional add-ons. That distinction is often missed until after the incident.Enterprise implications
For enterprises, the Arc story is really an invdo not know which machines are Arc-enabled, which extensions are installed, and which workloads rely on those extensions, then you cannot assess exposure quickly enough. The March disclosures make clear that defenders need service-level visibility, not just OS-level visibility.- Identify all Arc-connected assets.
- Map installed extensions and agent versions.
- Segment administrativ.
- Watch for anomalous control-plane actions.
- Treat hybrid agents as crown-jewel software.
Azure Compute Gallery and Input Validation Failures
Azure Compute Gallery sits at the heart of image distribution and lifecycle management for many cloud teams. It is the kind of platform service that looks mundane until a flaw in its validation logic turns into a local prie to a permissive regular expression is a reminder that security bugs are often born from convenience engineering.Why regex bugs are not trivial
A permissive regex is one of those defects that sounds minor until you unpack the consequences. Validation logic is supposed to keep malformed or malicious input out of privileged operations. When the check is too loose, the boundary collapses, and the attacker may be able to submit input that the developer never intended to permit.This kind of flaw is especially dangerous in a service that manages images and deployment workflows because those workflows often sit close to automation accounts. If the exploiauthenticated user a higher privilege state, the result can be lateral movement into more sensitive Azure resources. That makes remediation urgent even when the bug appears local or niche.
Broader cloud lessons
The Compute Gallery case shows how cloud customers inherit not only Microsoft’s service quality but also Microsoft’s internal assumptions about parsing, auct naming. When those assumptions fail, the customer’s own governance model may not catch the problem in time. In practical terms, this is another argument for layered controls, not blind trust in platform defaults.- Validate service inventory continuously.
- Review automation identities and roles.
- Log privileged image-management actions.
- Isolate administrative pipelines.
- Testafter updates.
Azure IoT Explorer and the Old Problem of New Interfaces
Azure IoT Explorer is a developer and operator tool, but it lives in a space where lightweight utilities often become privileged gateways into broader environments. March 2026 disclosures around information disclosure in Azure IoT Explorer highlight a familiar risk: *tools that help humans inspect devices can inadvertently expose sensit.in operational toolsIoT tooling tends to collect, render, or transport device metadata, credentials, and telemetry. That makes any cleartext exposure or authentication weakness especially troubling because the tool may be used in staging, production-adjacent, or partner-managed environments. A flaw in the interface can therefore become a flaw in the operational supply chain.
The security challenge is that such tools are often treated as benign because they are not the primary production service. That mindset is risky. When a diagnostic utility can leak data or mishandle authentication, it becomes part of the threat surface juckend it queries. In cloud operations, the helper app can be the weak link.*
What makes this category hard to secure
IoT management tools are designed for flexibility, which often means broad protocol support, a rich UI, and many edge cases. All of that increases the chances of a bug in transport handling, session management, or local storage. The March 2026 entries suggest that Microsoft i how to secure convenience-heavy tooling without making it unusable.- Treat diagnostic tools as sensitive assets.
- Restrict access to operator workstations.
- Encrypt traffic and stored secrets.
- Rotate credentials exposed to IoT tooling.
- Monitor for unexpected data disclosure.
Azure MCP Server Tools and the AI Security Frontier
One of th items in the March 2026 wave is the disclosure involving Azure MCP Server Tools. Even from the limited detail surfaced in the forum material, the lesson is clear: as Microsoft integrates Model Context Protocol-style tooling into cloud operations, it is importing an entire new class of security assumptions.Why SSRF matters here
A server-side request forgery flaw in an MCP toolchain is not just anothriven or agentic environment, SSRF can be a route to token theft, internal service probing, or abuse of privileged connectors. That makes the impact potentially far larger than the immediate component name suggests.The risk is amplified by the fact that MCP-style tooling is meant to bridge natural-language or agent actions to real systems. Those bridges are powerful, but they also compress several layers of intent, authorization, and network trust into a very small number of calls. That compression is efficient — and dangerous.
A new attack surface for administrators
Enterprises experimenting with agentitreat AI tooling as privileged middleware, not as a productivity toy. A flaw in the server-side request path may allow an attacker to use the system’s own reach against it. That changes the way admins should think about segmentation, logging, and secret handling inside AI-integrated control planes.- Inventory every MCP-facing endpointng from core secrets.
- Restrict outbound request destinations.
- Audit token scopes aggressively.
- Assume internal pivoting is a primary risk.
RRAS Hotpatching and Why It Matters to Azure-Adjacent Operations
Although RRAS is a Windows feature rather than an Azure service, the March 2026 hotpatch story matters cause it illustrates Microsoft’s evolving approach to high-severity remediation. The restartless hotpatch model is becoming more important in estates where uptime is sacred and network services cannot be interrupted casually.The logic of out-of-band response
Microsoft’s March 13 hotpatch for RRAS vulnerabilities demonstrates a willingness to break the monthly rhythm when risk is acute. Thause it tells enterprise customers that Microsoft sees some issues as too urgent to wait for the standard cycle. In practical terms, this improves response time, but it also raises expectations for rapid operational readiness.For Azure-adjacent teams, the lesson is simple: if Microsoft can move quickly on a high-risk networking issue, it may do the same elsewhere when the exploitation potential is serious enough. Organizations therefore need deployment processes that can absorb sudden, out-of-band changes without chaos. Speed becomes a requirement, not a luxury.
Managing no-restart updates
Hotpatching is not magic. gn, validation, and rollback planning. That makes it a great model for environments that have invested in modern servicing, but a frustration for those still operating with brittle legacy patch pipelines.- Validate hotpatch eligibility in advance.
- Keep maintenance rings well-defined.
- Test behavior after non-restart remediation.
- Track out-of-band advisories separately.
- Align patch policy with uptime requiremeerprise vs Consumer Divide
Enterprise exposure is broader and deeper
Enterprises face the hardest problem because they must account for scale, heterogeneity, and uptime all at once. Azure Arc, Compute Gallery, IoT tooling, and AI-integrated services can all be present in different parts of , often managed by different teams with different levels of visibility. That fragmentation is exactly what attackers exploit.This means patch prioritization cannot be based only on severity scores. It has to reflect role in the environment, exposure to privileged automation, and the likelihood that a flaw can be chained with other weaknesses. The March cycle is a reminder that context beats classification.
Consumer impact is mostly indirect
Consumers are less likely to be directly affected by Azure service flaws unless they are using Microsoft’s cloud tools in development, device management, or identity workflows. Stfice outages, degraded trust in Microsoft platforms, and delayed updates in products that share code or servicing logic with the cloud stack. That indirect impact is often underappreciated.- Enterprises need control-plane visibility.
- Consumers mainly feel service quality spillover.
- Developers may inherit cloud-tool exposure.
- IT admins face the heaviest patch burden.
- Managed-service providers sit in the middlvions
Cloud vendors are competing on operational confidence
The real competition is no longer just features or price. It is whether a vendor can deliver complex platform services without exposing customers to frequent emergency remediation. Microsoft’s hotpatching and rapid response models help on that front, but each high-profile Azure vulnerability still reminds customers that modernization increases dtThat creates an opening for competitors to emphasize lower-complexity architectures, fewer moving parts, or stronger defaults. Yet the market reality is that enterprises often need Microsoft’s breadth, so the question becomes not whether to avoid complexity entirely, but whether Microsoft can keep reducing the risk premium attached to using it. That remains an open contest.
The AI angle raises the stakes further
The Azure MCP Server Tools disclosure suggests that Microsoft’s next major competitive battleground may be how safely it brings AI into operational control planes. Whoever can make agentic systems more trustworthy will have ah customers slow-roll adoption or lock advanced capabilities behind tighter guardrails.- Security maturity is now a market differentiator.
- Operational simplicity has renewed appeal.
- AI tooling adds a new layer of scrutiny.
- Hybrid management can amplify vendor lock-in.
- Rapid patching can also signal platform confidence.
Strengths and Opportunities
The March 2026 Azure update cycle is unsettling, but it also shows that Microsoft haaes to use them well. The ability to ship out-of-band hotpatches, the depth of its telemetry, and the reach of its cloud administration ecosystem give it a chance to improve security at scale faster than smaller vendors can. The opportunity now is to turn that scale into predictable resilience rather than periodic emergency response.- Hotpatching reduces downtime for cr Microsoft’s broad platform reach enables faster coordinated response.
- Azure’s service telemetry can support better detection.
- Hybrid tooling allows centralized policy enforcement.
- Security fixes across cloud and endpoint can be aligned.
- Better inventory tools can reduce blind spots.
- AI-integrated operations could improve triage if secured properly.
Risks and Concerns
The same scale lragility. Every additional extension, service bridge, and agent increases the chance that a small flaw becomes an enterprise incident. The March 2026 update cycle highlights several recurring concerns: privilege escalation, validation mistakes, opaque confidence metadata, and the possibility that AI-era tools will introduce new trust dependencies faster than they can be secured.- Hybrid agents can become high-value compromise points.
- Privilege escalation remains the fastest path to impact.
- Validation errors in cloud services are hard to spot early.
- Out-of-band updates can strain patch governance.
- AI-connected tooling may enlarge the blast radius of mistakes.
- Operational complexity can outpace docum.s** in advisories are helpful but not sufficient on their own.
Looking Ahead
The next few servicing cycles will reveal whether March 2026 was an isolated burst of Azure-adjacent disclosures or the start of a more persistent pattern. What matters most is whether Microsoft and its customers treat these events as part of a systemic hardening process rather than as discrete fire drills. That means better asset inventory, tighter privilege boundaries, and stronger segmentation around management planes and diagnostic tooling.The other thing to watch is whether Microsoft keeps extending hotpatch-style remediation to more of its security surface. If it does, enterprise operators may gain the ability to close serious gaps without disruptive restarts. But that only works if customers can identify eligible systems quickly and trust their deployment pipelines enough to use thehaonal discipline around it.*
- Track additional Azure hybrid-service advisories.
- Monitor whether AI-related management tools draw more scrutiny.
- Watch for more restartless or out-of-band fixes.
- Reassess patch prioritization based on privilege pathways.
- Expand inventory of agents, extensions, and connectors.
Source: Fathom Journal Fathom - For a deeper understanding of Israel, the region, and global antisemitism
Last edited: