Microsoft’s April 27 expansion of Azure Local is one of its most consequential moves yet in the contested market for sovereign cloud infrastructure, but it is also one of the easiest to misunderstand. The company is not simply launching a European-style restricted public cloud, nor is it turning every Azure service into an on-premises appliance. Instead, Microsoft is stretching Azure Local from a relatively constrained hybrid platform into a much larger Sovereign Private Cloud foundation that can span edge sites, regulated datacenters, and potentially thousands of servers inside a customer-controlled boundary.
Microsoft has spent years trying to define the right answer to digital sovereignty. Its first instinct, like that of other hyperscalers, was to add guardrails to the public cloud: data residency, customer-managed keys, access logging, policy templates, and regional commitments. That approach works for many enterprises, but it does not satisfy organizations that need operational independence from the public cloud itself.
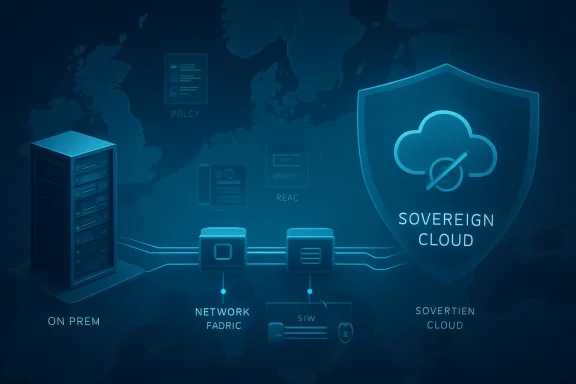
The new Azure Local push lands in a different category. It is best understood as a customer-operated Azure-like environment, built on validated hardware and managed with familiar Azure tooling, but physically deployed in an organization’s own facilities or trusted partner datacenters. That distinction matters because sovereignty is not just about where data sits; it is also about who controls the hardware, who can administer the platform, and what happens when connectivity to the public cloud disappears.
Historically, Azure Local came from the lineage of Azure Stack HCI, Microsoft’s attempt to modernize on-premises virtualization with Azure Arc, Hyper-V, software-defined infrastructure, and cloud-based management. The platform was attractive for branch offices, edge deployments, and hybrid modernization projects, but it did not look like a full-scale sovereign cloud replacement. The prior 16-node cluster ceiling reinforced that perception.
Now Microsoft is positioning Azure Local as a foundation for much larger sovereign environments. The company says deployments can grow from hundreds to thousands of servers within a single sovereign boundary, while the newest disaggregated architecture allows compute and storage to scale separately. That is a meaningful technical shift, but it does not remove every trade-off that comes with operating cloud-style infrastructure on hardware an organization must still buy, validate, secure, and maintain.
That framing gives governments and regulated sectors a more concrete answer to a long-standing problem. Public cloud can be fast, elastic, and innovation-rich, but agencies handling classified, law-enforcement, land registry, telecom, healthcare, or financial infrastructure often need more control than a normal region can offer. Azure Local’s appeal is that it brings some Azure operating models closer to those environments without asking them to surrender physical control.
Still, the phrase sovereign cloud can blur important boundaries. A sovereign public cloud region, a national partner cloud, and an on-premises sovereign private cloud are not interchangeable. Azure Local’s new role is closer to a private cloud appliance ecosystem than a hyperscale public cloud region with sovereign policy controls.
Microsoft documentation for disaggregated Azure Local deployments still describes individual instances in more bounded terms, including deployments from one machine up to dozens of machines when using SAN storage. The broader “thousands” message appears to refer to a sovereign environment composed of multiple Azure Local deployments, infrastructure pools, or managed footprints rather than a single monolithic cluster. That is not necessarily a weakness, but it is architecturally important.
For large enterprises, this model may actually be preferable. A telecom operator, national registry, or defense organization usually does not want one enormous fault domain. It wants separated pools across sites, racks, regions, or operational units, all governed under a consistent framework.
Organizations considering the platform should evaluate scale in layers:
That is particularly relevant for sovereign environments. Government archives, land records, surveillance analytics, telecom data, and industrial systems often have massive storage needs that do not map neatly to proportional compute growth. A disaggregated architecture lets organizations preserve enterprise SAN investments instead of replacing them wholesale with hyperconverged nodes.
Microsoft’s partner ecosystem is central here. Dell Technologies, HPE, Lenovo, NetApp, Hitachi Vantara, DataON, and others are part of the validated hardware story. That gives customers more choice, but it also reinforces that Azure Local is not a generic bring-any-server platform.
Active Directory remains deeply embedded in enterprise infrastructure, but it can also become a deployment constraint. Domain controllers require planning, redundancy, network paths, firewall rules, and operational ownership. Removing that dependency for specific Azure Local deployment paths can reduce friction at edge sites, industrial facilities, and sensitive environments where every additional service increases the attack surface.
Local Identity with Key Vault is not a universal cure for identity complexity. It still requires careful secret management, DNS planning, access control, and operational discipline. But it points in the right direction: sovereign infrastructure must be manageable even when normal enterprise dependencies are unavailable or intentionally excluded.
This capability addresses a recurring criticism of hybrid cloud platforms. If the cloud management plane is required for critical operations, the local deployment is not truly autonomous. Microsoft is trying to answer that concern with a local-first control plane for disconnected scenarios.
Key disconnected requirements include:
For many workloads, CPU-based acceleration may be enough. Document processing, retrieval-augmented generation pipelines, lightweight inferencing, anomaly detection, and local analytics can benefit from proximity to data and lower operational complexity. The cost and supply constraints around GPUs make this pitch even more attractive.
However, Microsoft is also clear that high-performance GPU infrastructure remains supported for more demanding scenarios. Foundry Local is meant to bring larger models into controlled environments for qualified customers, while Azure Local can host Kubernetes-based AI workloads. The result is a layered AI story rather than a single product.
The distinction matters because AI systems are rarely just model runtimes. They require vector stores, data pipelines, governance tools, monitoring, identity integration, content safety, model lifecycle controls, and developer workflows. If those components are fragmented between local and cloud environments, architecture becomes more complicated.
Practical AI opportunities include:
AT&T represents a different but equally important category: mission-critical telecom infrastructure. Telecom operators care about latency, resilience, lifecycle management, and control over hardware footprints. Azure Local gives Microsoft a way to participate in telco modernization without forcing every workload into a conventional Azure region.
FiberCop adds the edge infrastructure dimension. Distributed network operators need platforms that can live close to where services are delivered. A single edge node, a rack-scale deployment, and a larger datacenter footprint can all be part of the same architectural family.
That is not a flaw if the customer truly needs control. For defense, public safety, telecom, and critical national services, owning the operational boundary may be non-negotiable. But for mainstream enterprises, the economics can be more complex than the marketing suggests.
Azure Local is priced and managed through Azure mechanisms, but the physical estate remains local. That creates a hybrid cost model: capital expense for hardware, operational expense for support and staffing, subscription or core-based charges for software, and consumption charges for selected cloud services. The resulting business case must be tested against both public cloud and traditional private cloud alternatives.
For WindowsForum readers familiar with home labs, Hyper-V clusters, and Windows Server infrastructure, this is an important distinction. Azure Local is not simply “install Azure on any rack server.” It is a curated ecosystem with supported configurations.
Common operational implications include:
Microsoft’s Azure Local strategy is distinct because it leans heavily into customer-operated infrastructure. Rather than saying, “Trust our sovereign region,” Microsoft can say, “Run the environment inside your own boundary.” That is powerful for customers skeptical of public cloud jurisdictional exposure.
The downside is service depth. Public sovereign regions can offer a broader catalog of managed services because they remain hyperscale clouds. Azure Local provides stronger physical and operational control, but with a narrower set of local services.
The competitive comparison looks like this:
Consumers will not buy Azure Local, and most will never knowingly interact with it. The impact is indirect: more resilient telecom services, safer government data handling, better local processing for public services, and potentially stronger continuity during outages or crises. In that sense, sovereign infrastructure is a public-interest technology even when it is invisible.
The Windows ecosystem angle is also significant. Azure Local is built on familiar Microsoft infrastructure foundations, including Hyper-V and Windows Server-adjacent operational patterns. For organizations with deep Microsoft skills, it may be easier to adopt than a completely new private cloud stack.
That forces architecture teams to classify workloads carefully. Some applications are good candidates for Azure Local because they run well on VMs, Kubernetes, SQL Server, or edge AI components. Others are poor candidates because they depend heavily on hyperscale managed services.
A practical workload sorting model might be:
Microsoft also needs to clarify the relationship between Azure Local, Foundry Local, Microsoft 365 Local, and the broader Sovereign Cloud portfolio. The pieces are useful, but the naming can feel like a maze. Buyers need plain-language architecture maps that explain what runs locally, what depends on Azure, what works disconnected, and what remains unavailable.
Watch these developments closely:
Microsoft’s Azure Local expansion is therefore both a genuine step forward and a carefully bounded one. It gives organizations a more scalable way to run Azure-consistent infrastructure inside their own sovereign boundary, with better storage flexibility, improved identity options, and a clearer disconnected operations story. But it is not yet a full local Azure, and its success will depend on whether customers value control enough to accept the cost and complexity that control brings.
Source: Techzine Global Microsoft scales up Azure Local to a sovereign cloud, or does it?
 Overview
Overview
Microsoft has spent years trying to define the right answer to digital sovereignty. Its first instinct, like that of other hyperscalers, was to add guardrails to the public cloud: data residency, customer-managed keys, access logging, policy templates, and regional commitments. That approach works for many enterprises, but it does not satisfy organizations that need operational independence from the public cloud itself.The new Azure Local push lands in a different category. It is best understood as a customer-operated Azure-like environment, built on validated hardware and managed with familiar Azure tooling, but physically deployed in an organization’s own facilities or trusted partner datacenters. That distinction matters because sovereignty is not just about where data sits; it is also about who controls the hardware, who can administer the platform, and what happens when connectivity to the public cloud disappears.
Historically, Azure Local came from the lineage of Azure Stack HCI, Microsoft’s attempt to modernize on-premises virtualization with Azure Arc, Hyper-V, software-defined infrastructure, and cloud-based management. The platform was attractive for branch offices, edge deployments, and hybrid modernization projects, but it did not look like a full-scale sovereign cloud replacement. The prior 16-node cluster ceiling reinforced that perception.
Now Microsoft is positioning Azure Local as a foundation for much larger sovereign environments. The company says deployments can grow from hundreds to thousands of servers within a single sovereign boundary, while the newest disaggregated architecture allows compute and storage to scale separately. That is a meaningful technical shift, but it does not remove every trade-off that comes with operating cloud-style infrastructure on hardware an organization must still buy, validate, secure, and maintain.
Azure Local Becomes a Sovereign Private Cloud Building Block
From hybrid convenience to sovereignty strategy
The most important change is not merely scale; it is positioning. Azure Local is no longer being treated only as a hybrid infrastructure option for remote offices or modernization projects. Microsoft is framing it as the infrastructure layer of Sovereign Private Cloud, alongside Microsoft 365 Local and Foundry Local for productivity and AI workloads.That framing gives governments and regulated sectors a more concrete answer to a long-standing problem. Public cloud can be fast, elastic, and innovation-rich, but agencies handling classified, law-enforcement, land registry, telecom, healthcare, or financial infrastructure often need more control than a normal region can offer. Azure Local’s appeal is that it brings some Azure operating models closer to those environments without asking them to surrender physical control.
Still, the phrase sovereign cloud can blur important boundaries. A sovereign public cloud region, a national partner cloud, and an on-premises sovereign private cloud are not interchangeable. Azure Local’s new role is closer to a private cloud appliance ecosystem than a hyperscale public cloud region with sovereign policy controls.
- Azure Local runs on customer-controlled or partner-controlled infrastructure.
- Sovereign Public Cloud keeps workloads in Microsoft-operated regions with enhanced controls.
- National Partner Clouds rely on domestic or regional operators with localized governance.
- Sovereign Private Cloud emphasizes disconnected or customer-operated control.
- Azure Arc provides a bridge for policy, management, and selected services.
The Scale Question: Thousands of Servers, but Not One Giant Cluster
Why the wording matters
Microsoft’s headline claim is that Azure Local can now support deployments of up to thousands of servers within a single sovereign environment. That sounds dramatic because Azure Local was previously associated with much smaller cluster limits. But in practical terms, buyers need to distinguish between a sovereign environment, an Azure Local instance, and a cluster architecture.Microsoft documentation for disaggregated Azure Local deployments still describes individual instances in more bounded terms, including deployments from one machine up to dozens of machines when using SAN storage. The broader “thousands” message appears to refer to a sovereign environment composed of multiple Azure Local deployments, infrastructure pools, or managed footprints rather than a single monolithic cluster. That is not necessarily a weakness, but it is architecturally important.
For large enterprises, this model may actually be preferable. A telecom operator, national registry, or defense organization usually does not want one enormous fault domain. It wants separated pools across sites, racks, regions, or operational units, all governed under a consistent framework.
What scale changes operationally
Scaling Azure Local changes the conversation from “Can this run a few edge workloads?” to “Can this become a strategic private cloud platform?” That unlocks new patterns for regulated sectors, especially where data gravity and latency make public cloud less attractive. The challenge is that private cloud scale demands public cloud discipline.Organizations considering the platform should evaluate scale in layers:
- Physical infrastructure design across racks, sites, power, cooling, and networking.
- Cluster and instance boundaries that define resilience and operational blast radius.
- Governance and identity architecture for consistent policy across environments.
- Lifecycle management for firmware, drivers, operating system updates, and Azure Local releases.
- Workload placement rules for latency-sensitive, classified, or disconnected applications.
Disaggregated Architecture Is the Real Technical Breakthrough
Compute and storage finally separate
The standout technical change is disaggregated deployment. Traditional hyperconverged infrastructure tightly couples compute and storage, which is elegant at small and medium scale but can become expensive or awkward when workloads demand one resource faster than the other. Azure Local’s new SAN-based model allows compute and storage to scale independently.That is particularly relevant for sovereign environments. Government archives, land records, surveillance analytics, telecom data, and industrial systems often have massive storage needs that do not map neatly to proportional compute growth. A disaggregated architecture lets organizations preserve enterprise SAN investments instead of replacing them wholesale with hyperconverged nodes.
Microsoft’s partner ecosystem is central here. Dell Technologies, HPE, Lenovo, NetApp, Hitachi Vantara, DataON, and others are part of the validated hardware story. That gives customers more choice, but it also reinforces that Azure Local is not a generic bring-any-server platform.
- SAN storage support is now generally available for Azure Local.
- Fibre Channel connectivity is part of the current release path.
- iSCSI support is expected to follow rather than being the first-class starting point.
- Storage Spaces Direct and SAN volumes can coexist in supported scenarios.
- Validated hardware remains a core requirement, not a suggestion.
Identity and Disconnected Operations Move Closer to Reality
Reducing dependency on Active Directory
Another major update is Local Identity with Azure Key Vault, now generally available. This allows Azure Local deployments to be provisioned without requiring Microsoft Active Directory as a hard dependency in certain isolated environments. For air-gapped, disconnected, or tightly firewalled scenarios, that matters more than it may sound.Active Directory remains deeply embedded in enterprise infrastructure, but it can also become a deployment constraint. Domain controllers require planning, redundancy, network paths, firewall rules, and operational ownership. Removing that dependency for specific Azure Local deployment paths can reduce friction at edge sites, industrial facilities, and sensitive environments where every additional service increases the attack surface.
Local Identity with Key Vault is not a universal cure for identity complexity. It still requires careful secret management, DNS planning, access control, and operational discipline. But it points in the right direction: sovereign infrastructure must be manageable even when normal enterprise dependencies are unavailable or intentionally excluded.
The importance of offline governance
Microsoft’s February general availability of disconnected Azure Local operations set the stage for this announcement. The basic premise is that policy enforcement, role-based access control, auditing, and compliance configuration can continue locally when public cloud connectivity is absent. That is essential for environments where disconnection is not an outage but a requirement.This capability addresses a recurring criticism of hybrid cloud platforms. If the cloud management plane is required for critical operations, the local deployment is not truly autonomous. Microsoft is trying to answer that concern with a local-first control plane for disconnected scenarios.
Key disconnected requirements include:
- Local policy enforcement when Azure connectivity is unavailable.
- Local auditing and compliance controls inside the sovereign boundary.
- Reduced external dependencies for identity and deployment.
- Operational continuity during emergencies, isolation, or classified missions.
- Consistent management models across connected and disconnected estates.
AI at the Edge: Useful, but Not the Full Azure AI Stack
Inference without always needing GPUs
Microsoft is also pitching the expanded Azure Local as an AI infrastructure platform. Intel Xeon 6 processors, with built-in AI acceleration through Intel AMX, provide one foundation for inference and analytics workloads that do not necessarily require expensive GPU clusters. That is a sensible message for enterprises trying to run AI near sensitive data without exporting it to a public region.For many workloads, CPU-based acceleration may be enough. Document processing, retrieval-augmented generation pipelines, lightweight inferencing, anomaly detection, and local analytics can benefit from proximity to data and lower operational complexity. The cost and supply constraints around GPUs make this pitch even more attractive.
However, Microsoft is also clear that high-performance GPU infrastructure remains supported for more demanding scenarios. Foundry Local is meant to bring larger models into controlled environments for qualified customers, while Azure Local can host Kubernetes-based AI workloads. The result is a layered AI story rather than a single product.
What is still missing
The biggest limitation is that Azure Local does not equal the full Azure AI portfolio. Services such as Azure OpenAI Service, Microsoft Fabric, and Cosmos DB are not simply available as local equivalents in this sovereign environment. That creates a major gap for organizations hoping to reproduce cloud-native AI and data architectures on premises.The distinction matters because AI systems are rarely just model runtimes. They require vector stores, data pipelines, governance tools, monitoring, identity integration, content safety, model lifecycle controls, and developer workflows. If those components are fragmented between local and cloud environments, architecture becomes more complicated.
Practical AI opportunities include:
- Local inferencing for sensitive data that cannot leave a facility.
- Edge RAG for document and knowledge retrieval in controlled environments.
- Video and audio analytics in industrial, defense, and public safety contexts.
- Kubernetes-hosted AI services managed through Arc-enabled patterns.
- Hybrid AI pipelines where training, tuning, or orchestration may still use public cloud.
Customer Signals: Kadaster, AT&T, and FiberCop Show the Target Market
Sovereignty as operational control
Microsoft’s named customers illustrate the intended audience. The Dutch Land Registry, Kadaster, is exactly the kind of public agency for which data location, governance, and operational control are not abstract concerns. Land records are foundational civic infrastructure, and their integrity has national significance.AT&T represents a different but equally important category: mission-critical telecom infrastructure. Telecom operators care about latency, resilience, lifecycle management, and control over hardware footprints. Azure Local gives Microsoft a way to participate in telco modernization without forcing every workload into a conventional Azure region.
FiberCop adds the edge infrastructure dimension. Distributed network operators need platforms that can live close to where services are delivered. A single edge node, a rack-scale deployment, and a larger datacenter footprint can all be part of the same architectural family.
- Government agencies need jurisdictional control and auditability.
- Telecom providers need resilient infrastructure at operational scale.
- Critical infrastructure operators need continuity under degraded connectivity.
- Healthcare and finance need compliance without sacrificing modernization.
- Industrial organizations need local processing near equipment and data sources.
The Hardware Reality: Sovereignty Reintroduces Datacenter Ownership
The cloud trade-off reverses
The uncomfortable truth is that Azure Local brings back responsibilities many organizations moved to the cloud to escape. Customers need validated servers, supported storage, network design, firmware management, physical security, spare capacity, and lifecycle planning. Sovereignty does not eliminate infrastructure work; it relocates it.That is not a flaw if the customer truly needs control. For defense, public safety, telecom, and critical national services, owning the operational boundary may be non-negotiable. But for mainstream enterprises, the economics can be more complex than the marketing suggests.
Azure Local is priced and managed through Azure mechanisms, but the physical estate remains local. That creates a hybrid cost model: capital expense for hardware, operational expense for support and staffing, subscription or core-based charges for software, and consumption charges for selected cloud services. The resulting business case must be tested against both public cloud and traditional private cloud alternatives.
Validated hardware narrows flexibility
Microsoft requires validated hardware for good reason. A platform that combines virtualization, clustering, storage, security baselines, and cloud management cannot be reliable across arbitrary server combinations. But validation also limits procurement freedom.For WindowsForum readers familiar with home labs, Hyper-V clusters, and Windows Server infrastructure, this is an important distinction. Azure Local is not simply “install Azure on any rack server.” It is a curated ecosystem with supported configurations.
Common operational implications include:
- Procurement lead times for validated hardware and storage.
- Vendor coordination across Microsoft and hardware partners.
- Network constraints that may be difficult to change after deployment.
- Firmware and driver discipline as part of platform health.
- Capacity planning that must account for local redundancy and growth.
Competitive Pressure: Microsoft’s Different Answer to AWS, Google, and Oracle
Public sovereign cloud versus private sovereign cloud
Microsoft’s rivals are pursuing sovereignty from different angles. AWS has pushed the European Sovereign Cloud as a physically and logically separate cloud operated in Europe with dedicated governance promises. Oracle offers EU Sovereign Cloud regions and dedicated cloud options. Google Cloud works through partnerships such as T-Systems and S3NS, emphasizing local operational controls and external key management.Microsoft’s Azure Local strategy is distinct because it leans heavily into customer-operated infrastructure. Rather than saying, “Trust our sovereign region,” Microsoft can say, “Run the environment inside your own boundary.” That is powerful for customers skeptical of public cloud jurisdictional exposure.
The downside is service depth. Public sovereign regions can offer a broader catalog of managed services because they remain hyperscale clouds. Azure Local provides stronger physical and operational control, but with a narrower set of local services.
The market is fragmenting
The sovereign cloud market is not converging on one model. It is fragmenting into tiers of control, each with its own compromises. That fragmentation may benefit Microsoft because Azure already spans public cloud, Arc-enabled hybrid management, private cloud infrastructure, and productivity workloads.The competitive comparison looks like this:
- AWS emphasizes an independently operated European sovereign public cloud model.
- Oracle emphasizes sovereign regions, dedicated cloud, and enterprise database proximity.
- Google emphasizes partner-led sovereign controls and regional operating models.
- European providers emphasize local ownership, legal alignment, and political legitimacy.
- Microsoft emphasizes a spectrum from public sovereign controls to Azure Local private deployments.
Enterprise and Consumer Impact Are Very Different
Enterprises get choices; consumers get indirect benefits
For enterprise IT, this announcement expands the menu of serious options. A bank, hospital network, telecom operator, or government agency can now consider Azure Local for larger regulated workloads that previously exceeded the platform’s perceived scale. That does not mean every workload should move there, but the architectural ceiling is higher.Consumers will not buy Azure Local, and most will never knowingly interact with it. The impact is indirect: more resilient telecom services, safer government data handling, better local processing for public services, and potentially stronger continuity during outages or crises. In that sense, sovereign infrastructure is a public-interest technology even when it is invisible.
The Windows ecosystem angle is also significant. Azure Local is built on familiar Microsoft infrastructure foundations, including Hyper-V and Windows Server-adjacent operational patterns. For organizations with deep Microsoft skills, it may be easier to adopt than a completely new private cloud stack.
Developers face a mixed experience
For developers, the story is more complicated. Azure-consistent management helps, but local service availability is not equivalent to public Azure. Applications designed around Cosmos DB, Fabric, Azure OpenAI Service, or other managed services may require redesign, substitution, or hybrid routing.That forces architecture teams to classify workloads carefully. Some applications are good candidates for Azure Local because they run well on VMs, Kubernetes, SQL Server, or edge AI components. Others are poor candidates because they depend heavily on hyperscale managed services.
A practical workload sorting model might be:
- Keep in public Azure when elasticity and managed service depth matter most.
- Move to sovereign public cloud when regional control and policy guardrails are sufficient.
- Use Azure Local when data, latency, disconnection, or operational control dominate.
- Use national partner clouds when domestic operational governance is a formal requirement.
- Avoid forced migration when application dependencies make local operation brittle.
Strengths and Opportunities
Microsoft’s expanded Azure Local strategy is strongest where sovereignty, resilience, and hybrid consistency overlap. It gives regulated organizations a credible way to modernize local infrastructure while retaining more control than a conventional public cloud deployment can provide.- Stronger operational control for governments, defense, telecom, and critical infrastructure.
- Better scale narrative for Azure Local beyond small clusters and edge-only deployments.
- Disaggregated architecture that allows compute and storage to grow independently.
- SAN reuse that protects existing enterprise storage investments.
- Disconnected operations for environments where cloud connectivity is unavailable or prohibited.
- Azure-consistent management for teams already invested in Azure Arc and Microsoft tooling.
- Local AI inference for sensitive workloads that should remain inside a controlled boundary.
Risks and Concerns
The risks are equally real because Azure Local asks customers to operate sophisticated infrastructure while still accepting Microsoft’s ecosystem constraints. The platform may reduce sovereignty concerns, but it does not erase complexity, cost, or service gaps.- Limited local service catalog compared with full public Azure.
- No simple replacement for cloud-native services such as Fabric, Cosmos DB, or Azure OpenAI Service.
- Validated hardware requirements that reduce procurement flexibility.
- Operational burden for patching, capacity planning, lifecycle management, and physical resilience.
- Potential messaging confusion between sovereign public cloud, private cloud, and national partner cloud.
- Network design constraints that may be difficult to revise after deployment.
- Cost uncertainty for large multi-rack or sovereign-scale deployments as pricing models evolve.
Looking Ahead
The next test is service depth
The next phase will determine whether Azure Local becomes a niche sovereign platform or a broader private cloud standard for regulated industries. Scale and storage flexibility solve important infrastructure problems, but customers will judge the platform by the workloads it can actually run. If Microsoft expands the local service catalog without compromising autonomy, Azure Local becomes much more compelling.Microsoft also needs to clarify the relationship between Azure Local, Foundry Local, Microsoft 365 Local, and the broader Sovereign Cloud portfolio. The pieces are useful, but the naming can feel like a maze. Buyers need plain-language architecture maps that explain what runs locally, what depends on Azure, what works disconnected, and what remains unavailable.
Watch these developments closely:
- Whether Microsoft adds more Azure data and AI services to local or disconnected environments.
- How pricing evolves for multi-rack and sovereign-scale deployments.
- Whether iSCSI support broadens storage design flexibility beyond Fibre Channel-first scenarios.
- How national governments classify Azure Local under procurement and sovereignty frameworks.
- Whether reference customers expand beyond early adopters into mainstream regulated enterprises.
Microsoft’s Azure Local expansion is therefore both a genuine step forward and a carefully bounded one. It gives organizations a more scalable way to run Azure-consistent infrastructure inside their own sovereign boundary, with better storage flexibility, improved identity options, and a clearer disconnected operations story. But it is not yet a full local Azure, and its success will depend on whether customers value control enough to accept the cost and complexity that control brings.
Source: Techzine Global Microsoft scales up Azure Local to a sovereign cloud, or does it?