Fast Startup is designed to shave seconds off cold boots by saving a partial OS state to disk, but because it deliberately preserves kernel and driver state between shutdowns it can also hide faults, block other operating systems from safely accessing Windows volumes, and interfere with certain update, encryption and firmware workflows—so the convenience of a slightly faster boot comes with trade-offs that every Windows user should understand. ])
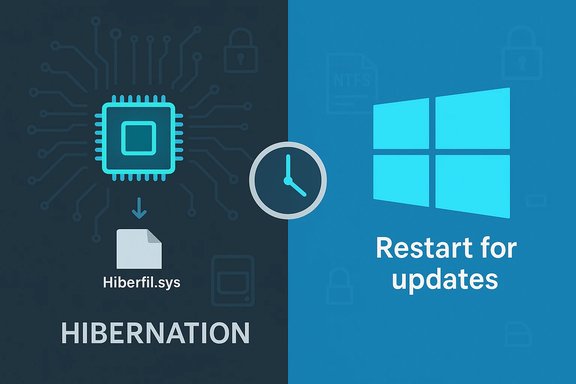
Fast Startup (sometimes called “hybrid shutdown” or “hybrid boot”) is a Windows feature introduced in Windows 8 and retained in Windows 10 and Windows 11. Instead of performing a full kernel teardown on shutdown, Windows logs off user sessions but hibernates the kernel session, writing a kernel image and loaded drivers to Hiberfil.sys and restoring that image on the next power-on. That approach cuts the time needed for kernel and driver in reduces the time-to-desktop by a measurable amount on older machines and hard-disk-based systems. This is not the same as full Hibernate. In full Hibernate the entire user session (open apps, windows, and user state) is saved and restored. Fast Startup saves only the kernel session and drivers, giving the feel of a fresh start with less work for the firmware and OS startup code. Importantly, Fast Startup is applied on shutdown → power on, but not on Restart; Restart always triggers a full cold boot. That distinction explains many of the headaches users see when updates or drivers appear not to have applied after a shutdown.
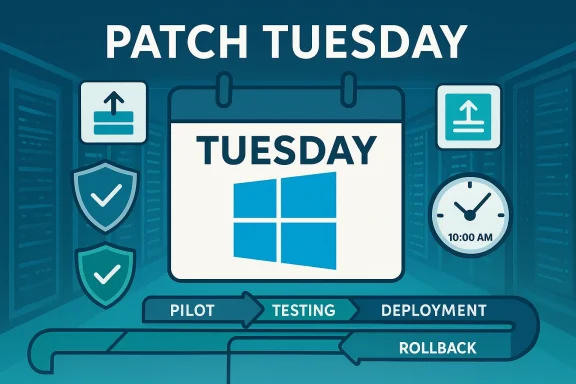
Some updates and driver installs require a full kernel restart to complete. Because Shutdown with Fast Startup preserves kernel state, simply shutting down and powering on may leave updates unapplied. Restart is the reliable operation that triggers a full initialization and forces updates and driver replacements to finish. This behavior explains why installers explicitly ask you to Restart, not just Shut down and power on later.
Source: Guiding Tech Common Fast Startup Issues and When (and How) to Disable It
 Background / Overview
Background / Overview
Fast Startup (sometimes called “hybrid shutdown” or “hybrid boot”) is a Windows feature introduced in Windows 8 and retained in Windows 10 and Windows 11. Instead of performing a full kernel teardown on shutdown, Windows logs off user sessions but hibernates the kernel session, writing a kernel image and loaded drivers to Hiberfil.sys and restoring that image on the next power-on. That approach cuts the time needed for kernel and driver in reduces the time-to-desktop by a measurable amount on older machines and hard-disk-based systems. This is not the same as full Hibernate. In full Hibernate the entire user session (open apps, windows, and user state) is saved and restored. Fast Startup saves only the kernel session and drivers, giving the feel of a fresh start with less work for the firmware and OS startup code. Importantly, Fast Startup is applied on shutdown → power on, but not on Restart; Restart always triggers a full cold boot. That distinction explains many of the headaches users see when updates or drivers appear not to have applied after a shutdown. How Fast Startup works (technical summary)
The mechanics in plain lwith Fast Startup enabled, Windows closes user sessions but serializes the kernel session and kernel-mode drivers to the hibernation file (Hiberfil.sys).
- On Power On, Windows loads the serialized kernel image from Hiberfil.sys instead of reinitializing every kernel component and driver. That bypass short-circuits portions of the full boot.
- On Restart, Fast Startup is intentionally bypassed so the system performs a full cold boot; installers and update processes typically require Restart to guarantee a clean kernel state.
Key technical points verified against vendor documentation
- Fast Startup depends on Windows’ hibernation infrastructure; disabling hibernation disables Fast Startup. The administrative command to toggle hibernation is powercfg /hibernate on|off (or powercfg -h on|off). Disabling hibernation removes Hiberfil.sys.
- Fast Startup is enabled by default on many Windows installations, but it is not universal; hardware and firmware (ACPI S-states) determine availability.
Common Fast Startup issues — what goes wrong and why
Fast Startup’s model—preserving a portion of system state—introduces a set of predictable failure modes. These are repeatable and widely reported by vendors and community troubleshooting guidnstallers appear incompleteSome updates and driver installs require a full kernel restart to complete. Because Shutdown with Fast Startup preserves kernel state, simply shutting down and powering on may leave updates unapplied. Restart is the reliable operation that triggers a full initialization and forces updates and driver replacements to finish. This behavior explains why installers explicitly ask you to Restart, not just Shut down and power on later.
Dual-boot and cross-OS filesystem access
When Windows uses Fast Startup, the NTFS volume may be left in a state similar to hibernation. Other operating systems—most notably Linux—refuse to mount NTFS partitions that appear hibernatedAs a result, dual-boot users often see missing or locked Windows partitions unless Fast Startup is disabled. This is one of the clearest, most concrete reasons to turn Fast Startup off on multi-OS machines.Encryption and third‑party disk tools
Full-disk or container encryption tools such as VeraCrypt have documented warnings about Fast Startup. Preserved kernel or driver state can leave cached key material or mounted volumes fter a Fast Startup shutdown, producing inconsistent behavior and potential security surprises. Users performing disk operations, imaging, or offline antivirus scans should disable Fast Startup while troubleshooting or working on volumes.Device and peripheral initialization failures
Because Fast Startup restores a previously initialized kernel and driver set, some hardware—particularly older or buggy drivers—may fail to reinitialize correctly at the next boot. Symptoms include missing USB devices, network adapters that don’t wake, or devices that appear in Device Manager only after a full Restart.Firmware and BIOS access difficulties
Because Fast Startup reduces the time between power on and OS handover, the window to trigger firmware hotkeys (F2, DEL, Esc, etc. can be very short or appear inconsistent. e, adjusting UEFI settings, or deliberately booting to alternate media may find Fast Startup interfering with their workflow. Temensures a predictable firmware entry window.Edge behaviors: phantom wakes and battery drain (anecdotal)
There are anecdotal reports ofigher-than-expected battery draw on some laptop models when Fast Startup is enabled. These claims appear hardware-dependent and are not universal; treat them as empirical observations to be tested on the specific device rather than as a universal property of Fast Startup. If you observe such symptoms, disabling Fast Startup is a lo step.When you should disable Fast Startup (decision tree)
Fast Startup is safe and convenient for many single‑OS, consumer-grade systems with modern drivers and SSD storage. But in the following situations you should disable it immediately:- Dual‑booting Windows with Linux or another OS (to avoid NTFS hibernation states).
- Using third‑party encryption (VeraCrypt, certain BitLocker scenarios) or preparing disks for offline operations or imaging.
- Frequently entering BIOS/UEFI, flashing firmware, or changing boot media—these workflows demand deterministic access to firmware menus.
- Experiencing updates or driver installs that appear not to apply after shutdown, or devices that consistently fail to initialize unless you Restart.
- Running server or enterprise imaging workflows where a deterministic, repeatable cold boot is required (test via Group Policy/MDM before mass deployment).
- Single‑OS consumer laptops/desktops with modern NVMe or SATA SSDs and up‑to‑date drivers, where the typical cold-boot win is a few seconds and you value the convenience. Even here, adopt the habit of performing a weekly Restart after updates.
How to check whether Fast Startup is enabled and how to disable it
There are several ways to view and change the setting—GUI, command line, Group Policy, or Registry. Use the method that best fits your comfort level; the GUI is reversible and preserves hibernation, while the command-line option that disables hibernation removes Hiberfil.sys altogether.Option A — Control Panel (recommended if you want to preserve hibernate)
- Open Control Panel → Power Options.
- Click Choose what the power buttons do.
- Click Change settings that are currently unavailable.
- Under Shutdown settings, uncheck Turn on fast startup (recommended).
- Click Save changes and perform a full shutdown to verify behavior.
This approach disables Fast Startup while keeping hibernation available.
Option B — Command line (disables hibernation, removes Hiberfil.sys)
- Open Command Prompt or PowerShell as Administrator.
- Run: powercfg /hibernate off (or powercfg -h off).
- To re-enabl on.
Note: Disabling hibernation also disables Fast Startup and deletes Hiberfil.sys. Use this only if you do not use hibernate.
Option C — Group Policy (for Pro/Edu/Enterprise / enterprise rollouts)
- Computer Configuration → Administrat → Shutdown → Require use of fast startup. Use Group Policy or MDM to enforce settings across fleets after broad pilot testing.
Option D — Registry (if the GUI option is missing)
- If the Fast Startup option is missing in Power Options it often means hibernation is disabled or hardware does not support it. The registry key HiberbootEnabled at HKLM\SYSTEM\CurrentControlSet\Control\Session Manager\Power controls the behavior; however, editing the Registry requires care and is best done only when recommended by support or after a backup.
Practical step-by-step: safe troubleshooting workflow
- Identify the problem type (dual‑boot mount error, updates not applied, device initialization failure).
- For dual‑boot or disk operations, disable Fast Startup via Control Panel and reboot using Restart to ensure a clean kernel.
- If you need to remove hibernation entirely (for disk space or other reasons), use powercfg /hibernate off but be aware this deletes Hiberfil.sys and removes hibernate from power options.
- After disabling Fast Startup, reproduce the problem; if it’s resolved, keep Fast Startup off for that workflow. If not resoltinue troubleshooting drivers, update logs, and firmware.
Measuring boot time and validating the impact
Subjective impressions are misleading. Use objective metrics before and after any change:- Event Viewer → Applicat → Microsoft → Windows → Diagnostics‑Performance → Operational. Look for Event ID 100 (BootDuration) to compare cold boot times. This avoids stopwatch variability and gives reproducible numbers.
- For quick checks, measure time from power-on to desktop across multiple runs and average the result. If you rely on Fast Startup and care about deterministic freshness (e.g., after updates), schedule weekly Restarts.
Critical analysis — strengths, limitations, and risks
rtup produces materially faster cold boots especially on mechanical drives where kernel and driver initialization is more expensive. It’s a low-friction optimization that benefits many non‑technical users.
- It’s reversible and configurable; administrators can push policies or individual users can toggle it as needed.
Limitations
- The absolute gains on modern NVMe SSD systems are often measured in seconds; for many SSD-based machines the convenience gain is marginal. Systems with modern controllers and optimized firmware already boot quickly, so Fast Startup’s benefit is smaller.
- Fast Startup creates problems: updates that require full kernel reinitialization, cross‑OS mounting problems, and encryption edge cases. Those are not transient bugs but a consequence of the design trade-off.
Roncerns
- In enterprise imaging or firmware rollout scenarios, Fast Startup can produce inconsistent results. Managed environments should pilot changes and use Group Policy/MDM to standardize behavior.
- Disabling hibernation via powercfg /hibernate off will permanently remove Hiberfil.sys until re-enabled and can remove the user-visible Hibernate power option—take care if you rely on hibernate forflows.
- Some claims in community forums (battery drain, phantom wakes) are anecdotal and hardware dependent; they should be tested on the specific device rather than assumed. Flag these as empirical observations, not guaranteed effects.
Recommendations — what to do, when, and how long to test
- Dual‑boot or encryption users: disable Fast Startup permanently. The risk of data corruption or inconsistent encryption behavior outweighs a modest boot time gain. Test the configuration immediately by mounting partitions in the secondary OS or running the encryption workflow you need.
- Single‑OS consumer with SSD: leave Fast Startup enabled if you value the small convenience and you don’t perform firmware operations frequently. However, adopt the habit of doing a full Restart after any system update, driver update, or firmware change.
- IT admins and fleets: pilot changes across representative hardware. Use Group Policy/MDM to push settings and document procedures to suspend BitLocker and disable Fast Startup during firmware or imaging operations.
- If you see odd peripheral behavior, missler messages that insist on a Restart, disable Fast Startup as an early troubleshooting step before deep driver-level debugging.
Troubleshooting checklist (quick reference)
- If Fast Startup option is missing: ensure hibernation is enabled (powercfg /hibernate on), or check the HiberbootEnabled registry key.
- Need a guaranteed clean boot for updates/drivers? Use Restart explicitly.
- Dual‑boot mount errors? Disable Fast Startup, then verify from the other OS.
- Disk or encryption operations failing? Disable Fast Startup and repeat the operation with a cold boot.
- Want to reclaim Hiberfil.sys? Run powercfg /hibernate off (but remember this removes Hibernate permanently until re-enabled).
Conclusion
Fast Startup is an elegant, low-risk performance trade-off that makes everyday boots a touch snappier by preserving kernel state between shutdowns. For most single‑OS consumers with modern hardware it is a convenience; for power users, dual‑booters, encryption workflows, firmware updaters, and managed fleets it is a variable that introduces real operational risk. The practical approach is simple: measure first, apply Restart for reliability, and disable Fast Startup when you need determinism or cross‑OS access. When in doubt, disable it temporarily for troubleshooting—toggling Fast Startup via Control Panel is reversible and preserves hibernation, while powercfg /hibernate off is a more permanent removal of the hibernation file and should be used deliberately. This balance—small convenience versus deterministic, predictable behavior—summarizes the design trade‑offs built into Fast Startup. For anyone managing systems, the safe path is to document your decision, pilot any fleet-level changes, and verify outcomes with objective boot metrics and hands-on tests across representative hardware.Source: Guiding Tech Common Fast Startup Issues and When (and How) to Disable It