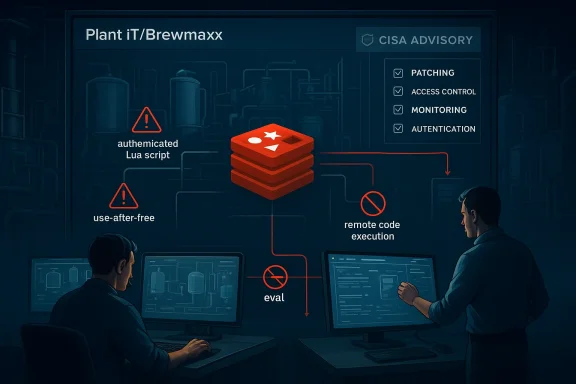
Schneider Electric’s Plant iT/Brewmaxx advisory is a reminder that modern industrial software risk rarely comes from a single proprietary bug. In this case, the problem sits at the intersection of an embedded third-party component, a high-value automation platform, and a set of operational assumptions that often leave production environments more exposed than administrators realize. The affected versions, 8.2.1 and earlier, reportedly ship with Redis in a way that permits an authenticated attacker to abuse specially crafted Lua scripts, manipulate the garbage collector, trigger a use-after-free, and potentially reach remote code execution if the right conditions are met. The mitigations are straightforward in concept but disruptive in practice: patch, harden Redis, disable risky commands, and restart systems across the plant stack. Schneider Electric’s own security notice and the matching CISA advisory both stress that this is not a theoretical housekeeping item; it is a concrete industrial cybersecurity problem with real operational consequences.
The latest Schneider Electric notice lands in a familiar place for industrial operators: an application that was designed to make plant control and process automation easier now inherits the security posture of the components underneath it. Plant iT and Brewmaxx are long-running automation platforms used in industrial environments where uptime, deterministic behavior, and predictable maintenance windows matter more than convenience. Their appeal is obvious, especially in beverage and process industries where recipes, batch logic, and operator workflows need to remain consistent across shifts and sites. That same longevity, however, means older architectural decisions can persist long after the original threat model has changed.
Redis is at the center of this particular issue. Redis is an open-source, in-memory database widely used for speed and simplicity, but in industrial deployments it often sits inside a much larger system that was not designed to absorb experimental or exploit-prone behavior. The advisory language matters here: an authenticated user can use a specially crafted Lua script to interfere with the garbage collector and trigger a use-after-free condition. In plain English, that means the platform’s scripting layer can be pushed into unsafe memory handling, and once memory corruption enters the picture, the boundary between a crash and code execution becomes worryingly thin.
The remediation guidance is unusually direct. Schneider Electric recommends applying ProLeiT-2025-001, then disabling eval commands in Redis on the application server, VisuHub, engineering workstations, and workstations that support emergency mode functionality. The vendor also instructs operators to force the use of secure Redis configuration templates and restart all patched servers and workstations. Those steps are not cosmetic. They reflect the reality that a patch alone is only part of the answer when the vulnerable feature set is still available to authenticated users and when multiple operator-facing endpoints may share the same underlying trust model.
The Redis issue also reflects a broader trend in industrial software security: vendors increasingly depend on mainstream open-source components, but those components arrive with their own release cadence, memory-safety assumptions, and configuration footguns. Redis is fast and mature, but Lua scripting has long been one of the more delicate features in its ecosystem. When a platform exposes script evaluation to users or service accounts that were never meant to think like exploit developers, it creates a path from normal administration to low-level memory manipulation. That is exactly the kind of bridge attackers like to find in OT products.
Schneider Electric has published similar cyber guidance across its automation portfolio, and the pattern is consistent: patch first, then reduce exposure, segment networks, and constrain remote access. That is not just vendor boilerplate. CISA’s ecosystem of industrial advisories routinely shows that PLCs, SCADA tools, and industrial monitoring applications become significantly more dangerous when reachable from broader enterprise networks or when built-in services remain turned on longer than necessary. In other words, an advisory about Redis in Plant iT/Brewmaxx is also a reminder that configuration and architecture are part of the vulnerability surface.
The timing of this disclosure also matters. CISA has continued to publish Schneider Electric advisories across 2025 and into 2026, including notices affecting EcoStruxure and Modicon product lines. That broader cadence suggests that industrial security teams should not treat this incident as an isolated software defect. Instead, it fits a recurring pattern in which a vendor’s product family can be exposed through different layers at different times: application logic, control logic, web interfaces, or embedded third-party libraries. The lesson is persistent: the stack is the attack surface.
In practice, use-after-free bugs are dangerous because they allow a program to continue using memory after it has been returned to the allocator. If an attacker can shape allocation patterns, timing, or object lifetimes, the freed memory may be reused in a way that hands the attacker control over pointers or execution flow. In an industrial application, that kind of bug can have consequences beyond application instability. It can become the foothold for changing configuration, undermining process oversight, or pivoting deeper into a constrained OT network.
Schneider Electric’s mitigation language strongly suggests that the vulnerable behavior is tied not just to versioning but also to Redis command exposure. The instruction to disable eval commands across the application server, VisuHub, engineering workstations, and emergency-mode workstations is revealing. It indicates that the safest posture is not merely to fix the library, but to remove the attack primitive from operational use wherever possible. That is a classic defense-in-depth answer to a scripting-layer memory bug.
The restart requirement is especially important because industrial systems frequently survive for long periods with stale services, lingering processes, or partial configuration changes. If a patched binary is installed but an old service instance is still in memory, the system may remain vulnerable until it is fully cycled. Schneider Electric’s guidance acknowledges that reality. In OT, installation is not the same as remediation.
There is also an architectural lesson in the Redis hardening instructions. Disabling eval commands reduces the risk that future script-based abuse can be replayed, even if some exposed component still has residual weaknesses. For administrators, that is a valuable pattern: rather than relying on one patch to solve every future class of abuse, cut off the most dangerous capability where the business process allows it. That is particularly wise for shared or multi-purpose operator stations.
For consumer readers, the product names may not be familiar, but the stakes should be. These are industrial platforms used in environments where physical output depends on software behaving correctly. That includes food and beverage production, process plants, and other sectors where downtime is expensive and unsafe conditions can arise quickly. Even if the flaw is “just” in software, the downstream effect can be a manufacturing halt or worse.
The more interesting impact is systemic. Industrial operators increasingly want the same convenience that IT teams have enjoyed for years: centralized management, remote access, reusable templates, and software-defined workflows. The problem is that every convenience layer can become another target. When vendor guidance starts telling users to disable commands, restart systems, and isolate networks, it reveals the cost of convenience in a high-availability plant.
For rivals, the message is just as clear. Industrial automation platforms are now judged not only on function and reliability but on how transparently they handle third-party dependency risk. If a competitor ships similar Redis-backed services, it will be asked uncomfortable questions about script exposure, sandboxing, and whether default configurations are safe enough for real plants. In that sense, one advisory becomes a market benchmark.
The episode also reinforces a larger truth about OT security branding. Vendors love to say they support defense in depth, least privilege, and hardened defaults, but customers increasingly want proof in the form of concrete mitigations and upgrade paths. Schneider’s response here is fairly strong because it pairs a fix with a set of operationally specific hardening steps. That pragmatic packaging is what customers now expect.
The advice to isolate control and safety networks behind firewalls and keep them away from the business network is not a generic best practice buried for legal reasons. It directly addresses the way industrial compromise often unfolds: the initial foothold is in the enterprise zone, and the later movement is toward engineering or supervisory systems. In a world where a Redis scripting flaw can be accessed by an authenticated user, segmentation remains one of the few controls that meaningfully slows lateral movement.
Physical security also matters more than many outside the OT world realize. Schneider Electric explicitly reiterates that controllers should be placed in locked cabinets and never left in Program mode. That may sound old-fashioned, but it reflects a hard lesson: cyber incidents in plants frequently combine digital flaws with physical or procedural weakness. The best patch in the world cannot help if unauthorized personnel can tamper with the environment.
A second thing to watch is whether additional guidance follows for specific deployment variants, especially sites that rely heavily on emergency-mode workstations or heavily customized configurations. Industrial vendors often publish follow-up notes when initial mitigations meet real-world friction. If that happens here, it will likely be because plant teams need help reconciling security hardening with uptime constraints.
Finally, this advisory could encourage more customers to audit their use of Redis, Lua scripting, and privileged automation services across the rest of the plant estate. That would be a healthy side effect. A vulnerability like this should not just trigger a single fix; it should prompt a broader review of which services really need scripting enabled at all.
Source: CISA Schneider Electric Plant iT/Brewmaxx | CISA
 Overview
Overview
The latest Schneider Electric notice lands in a familiar place for industrial operators: an application that was designed to make plant control and process automation easier now inherits the security posture of the components underneath it. Plant iT and Brewmaxx are long-running automation platforms used in industrial environments where uptime, deterministic behavior, and predictable maintenance windows matter more than convenience. Their appeal is obvious, especially in beverage and process industries where recipes, batch logic, and operator workflows need to remain consistent across shifts and sites. That same longevity, however, means older architectural decisions can persist long after the original threat model has changed.Redis is at the center of this particular issue. Redis is an open-source, in-memory database widely used for speed and simplicity, but in industrial deployments it often sits inside a much larger system that was not designed to absorb experimental or exploit-prone behavior. The advisory language matters here: an authenticated user can use a specially crafted Lua script to interfere with the garbage collector and trigger a use-after-free condition. In plain English, that means the platform’s scripting layer can be pushed into unsafe memory handling, and once memory corruption enters the picture, the boundary between a crash and code execution becomes worryingly thin.
The remediation guidance is unusually direct. Schneider Electric recommends applying ProLeiT-2025-001, then disabling eval commands in Redis on the application server, VisuHub, engineering workstations, and workstations that support emergency mode functionality. The vendor also instructs operators to force the use of secure Redis configuration templates and restart all patched servers and workstations. Those steps are not cosmetic. They reflect the reality that a patch alone is only part of the answer when the vulnerable feature set is still available to authenticated users and when multiple operator-facing endpoints may share the same underlying trust model.
Background
Industrial vendors have spent years learning that the word “authentication” does not equal “safety.” In an enterprise or consumer app, requiring login credentials can reduce risk substantially. In an OT environment, however, authenticated misuse can still be catastrophic if the authenticated account belongs to an engineer, integrator, or technician with broad privileges. Plant iT and Brewmaxx sit squarely in that category because they are built to support plant operations, engineering changes, visualization, and supervisory control. That makes any authenticated scripting path especially sensitive, because the person behind the keyboard may already have enough reach to affect production logic.The Redis issue also reflects a broader trend in industrial software security: vendors increasingly depend on mainstream open-source components, but those components arrive with their own release cadence, memory-safety assumptions, and configuration footguns. Redis is fast and mature, but Lua scripting has long been one of the more delicate features in its ecosystem. When a platform exposes script evaluation to users or service accounts that were never meant to think like exploit developers, it creates a path from normal administration to low-level memory manipulation. That is exactly the kind of bridge attackers like to find in OT products.
Schneider Electric has published similar cyber guidance across its automation portfolio, and the pattern is consistent: patch first, then reduce exposure, segment networks, and constrain remote access. That is not just vendor boilerplate. CISA’s ecosystem of industrial advisories routinely shows that PLCs, SCADA tools, and industrial monitoring applications become significantly more dangerous when reachable from broader enterprise networks or when built-in services remain turned on longer than necessary. In other words, an advisory about Redis in Plant iT/Brewmaxx is also a reminder that configuration and architecture are part of the vulnerability surface.
The timing of this disclosure also matters. CISA has continued to publish Schneider Electric advisories across 2025 and into 2026, including notices affecting EcoStruxure and Modicon product lines. That broader cadence suggests that industrial security teams should not treat this incident as an isolated software defect. Instead, it fits a recurring pattern in which a vendor’s product family can be exposed through different layers at different times: application logic, control logic, web interfaces, or embedded third-party libraries. The lesson is persistent: the stack is the attack surface.
Why Redis is such a sensitive dependency
Redis often earns trust because it is familiar, documented, and operationally lightweight. In many environments that makes it attractive for caching, queueing, and state management, especially where low latency is critical. But in an industrial setting, the same speed and flexibility can become a liability if scripting features are exposed beyond a tightly controlled admin boundary. A Lua script that can influence garbage collection is not just “a script”; it is a potential memory-corruption primitive.Why industrial users feel this differently than IT admins
For an IT administrator, a vulnerable application service may be one incident in a long queue of patching tasks. For a plant operator, the same flaw can affect batch production, operator visibility, and emergency workflows. That means patch windows are harder to schedule, validation is more complex, and restart requirements can be operationally expensive. The vendor’s instruction to restart all patched servers and workstations is therefore not a trivial footnote; it is part of the actual fix path.The Vulnerability Mechanics
The core issue is a memory-safety flaw reachable through authenticated Lua script execution in Redis as deployed with Plant iT/Brewmaxx versions 8.2.1 and earlier. According to the advisory text, the crafted script can manipulate garbage collector behavior, create a use-after-free condition, and potentially allow remote code execution. That sequence is important because it maps an attacker’s leverage from a high-level scripting interface to a low-level memory corruption outcome, which is exactly how serious exploit chains are born.In practice, use-after-free bugs are dangerous because they allow a program to continue using memory after it has been returned to the allocator. If an attacker can shape allocation patterns, timing, or object lifetimes, the freed memory may be reused in a way that hands the attacker control over pointers or execution flow. In an industrial application, that kind of bug can have consequences beyond application instability. It can become the foothold for changing configuration, undermining process oversight, or pivoting deeper into a constrained OT network.
Schneider Electric’s mitigation language strongly suggests that the vulnerable behavior is tied not just to versioning but also to Redis command exposure. The instruction to disable eval commands across the application server, VisuHub, engineering workstations, and emergency-mode workstations is revealing. It indicates that the safest posture is not merely to fix the library, but to remove the attack primitive from operational use wherever possible. That is a classic defense-in-depth answer to a scripting-layer memory bug.
What makes this different from a typical app bug
This is not a bug in a report viewer or a dashboard widget. It is a flaw in the underlying data and scripting layer that can be reached by someone who already has credentials. That raises the stakes because authenticated abuse often blends into normal operator activity and can be harder to spot than a noisy remote probe. It also means that stolen credentials, weak role separation, or shared admin accounts become more dangerous than they already were.Why exploitability matters in OT
Industrial environments rarely rely on a single security boundary. They rely on layered trust: controllers, engineering stations, HMI nodes, historians, and service accounts each have a role. If one authenticated user can drive a memory-corruption path, the attacker may not need to breach the firewall at all. They only need a foothold with sufficient permissions inside the plant trust zone. That is why CISA advisories so often emphasize segmentation and access minimization alongside vendor patches.Patch and Mitigation Strategy
The primary fix is ProLeiT-2025-001, distributed through ProLeiT Support, and Schneider Electric says it should be installed immediately. But the vendor does not stop there. After patching, administrators are told to disable Redis eval commands, enforce secure Redis configuration templates, and restart all affected servers and workstations. That sequence is deliberate: patch the software, eliminate the exploitable function, standardize the configuration, and then reboot to ensure the runtime state actually changes.The restart requirement is especially important because industrial systems frequently survive for long periods with stale services, lingering processes, or partial configuration changes. If a patched binary is installed but an old service instance is still in memory, the system may remain vulnerable until it is fully cycled. Schneider Electric’s guidance acknowledges that reality. In OT, installation is not the same as remediation.
There is also an architectural lesson in the Redis hardening instructions. Disabling eval commands reduces the risk that future script-based abuse can be replayed, even if some exposed component still has residual weaknesses. For administrators, that is a valuable pattern: rather than relying on one patch to solve every future class of abuse, cut off the most dangerous capability where the business process allows it. That is particularly wise for shared or multi-purpose operator stations.
Practical operator response sequence
- Inventory affected Plant iT/Brewmaxx nodes and verify whether any are at version 8.2.1 or below.
- Apply ProLeiT-2025-001 through the vendor support channel.
- Disable Redis eval wherever the advisory says it is present.
- Force secure Redis configuration templates from the patch manual.
- Restart all patched servers and workstations to ensure the fix is active.
- Validate operator workflows after restart, especially VisuHub and emergency-mode stations.
Why configuration templates matter
Templates are more than convenience tools. In large automation estates, they are how administrators preserve consistent security settings across many machines. If a secure Redis template can be forced into system settings, it reduces the odds that a one-off engineer, contractor, or local admin leaves a node in an unsafe state. That is a subtle but powerful control in environments where configuration drift is one of the most common hidden risks.Enterprise and Plant Impact
For enterprises running Plant iT/Brewmaxx, the immediate impact is likely to be felt in engineering and operations coordination. Engineering workstations often have the broadest permissions and the most direct access to system-level functionality, so a flaw involving authenticated scripting and memory corruption is especially concerning there. A compromise of those endpoints could alter recipes, logic, or operator visibility, depending on deployment architecture and access boundaries.For consumer readers, the product names may not be familiar, but the stakes should be. These are industrial platforms used in environments where physical output depends on software behaving correctly. That includes food and beverage production, process plants, and other sectors where downtime is expensive and unsafe conditions can arise quickly. Even if the flaw is “just” in software, the downstream effect can be a manufacturing halt or worse.
The more interesting impact is systemic. Industrial operators increasingly want the same convenience that IT teams have enjoyed for years: centralized management, remote access, reusable templates, and software-defined workflows. The problem is that every convenience layer can become another target. When vendor guidance starts telling users to disable commands, restart systems, and isolate networks, it reveals the cost of convenience in a high-availability plant.
OT versus IT priorities
IT teams often optimize for patch velocity and endpoint standardization. OT teams optimize for continuity, safety, and validated behavior. Those priorities can clash when a security fix requires restarts or changes to operational tooling. That tension is why industrial advisories often emphasize compensating controls and segmented architecture: vendors know that not every site can patch in minutes, but every site can usually tighten exposure.Why authenticated abuse still deserves urgent attention
Security teams sometimes downgrade authenticated flaws because they assume “if you have the credentials, you already have access.” That assumption is too optimistic in industrial networks. Credentials may be shared, stolen, or reused across stations, and an authenticated foothold can become the fastest route to broad impact. The difference between a harmless login and a memory-corruption exploit is the difference between routine admin work and a possible RCE path.Competitive and Market Implications
This disclosure also highlights the competitive pressure industrial vendors face as they integrate more open-source infrastructure. Customers want modern capability, cloud-aware management, and reuse of proven components, but they are increasingly unwilling to accept security debt as the price of progress. A vendor like Schneider Electric has to keep showing that it can ship patches quickly, document mitigations clearly, and help customers reduce exposure without forcing a complete platform overhaul.For rivals, the message is just as clear. Industrial automation platforms are now judged not only on function and reliability but on how transparently they handle third-party dependency risk. If a competitor ships similar Redis-backed services, it will be asked uncomfortable questions about script exposure, sandboxing, and whether default configurations are safe enough for real plants. In that sense, one advisory becomes a market benchmark.
The episode also reinforces a larger truth about OT security branding. Vendors love to say they support defense in depth, least privilege, and hardened defaults, but customers increasingly want proof in the form of concrete mitigations and upgrade paths. Schneider’s response here is fairly strong because it pairs a fix with a set of operationally specific hardening steps. That pragmatic packaging is what customers now expect.
What this means for vendors
Security disclosures have become part of the sales conversation. Buyers now look at patch cadence, support channels, and how quickly a vendor can turn a vulnerability into actionable guidance. When advisories cite specific products, versions, affected stations, and follow-up steps, they reduce uncertainty for customers and improve trust, even when the underlying news is bad. That is the right long-term play in a market where trust is expensive.What this means for customers
Customers should expect more dependency-driven advisories, not fewer. Industrial stacks are converging with mainstream software practices, which means open-source memory bugs, scripting issues, and configuration weaknesses will keep appearing in vendor notices. The organizations that win will be the ones that treat software composition as an operational discipline, not an afterthought.Why the Mitigation Advice Looks Familiar
Schneider Electric’s broader cybersecurity guidance is consistent across its product lines: segment networks, control physical access, minimize exposure, and use secure remote access methods such as VPNs when needed. The company’s CISA-backed advisories repeatedly push the same themes because those controls are still the most effective way to reduce blast radius in industrial environments. That consistency is useful; it gives administrators a familiar playbook rather than a one-off patch note with no follow-through.The advice to isolate control and safety networks behind firewalls and keep them away from the business network is not a generic best practice buried for legal reasons. It directly addresses the way industrial compromise often unfolds: the initial foothold is in the enterprise zone, and the later movement is toward engineering or supervisory systems. In a world where a Redis scripting flaw can be accessed by an authenticated user, segmentation remains one of the few controls that meaningfully slows lateral movement.
Physical security also matters more than many outside the OT world realize. Schneider Electric explicitly reiterates that controllers should be placed in locked cabinets and never left in Program mode. That may sound old-fashioned, but it reflects a hard lesson: cyber incidents in plants frequently combine digital flaws with physical or procedural weakness. The best patch in the world cannot help if unauthorized personnel can tamper with the environment.
The role of remote access
Remote access is now indispensable for many industrial operators, especially after years of expanding service demands and geographically distributed plants. But the same feature that lets an engineer troubleshoot quickly can also widen the attack surface if credentials, VPNs, or remote desktop tools are poorly managed. Schneider’s guidance is explicit that VPNs should be current, trusted, and paired with secure device hygiene. That is basic hygiene, but in OT, basic hygiene saves plants.Why mobile media remains on the checklist
The advisory’s reminder to scan CDs, USB drives, and other mobile data exchange methods may seem dated, but industrial environments still rely on removable media more often than office networks do. Air-gapped or semi-isolated systems routinely exchange files through controlled removable devices, which makes malware screening a necessary defensive step. The persistence of this guidance tells you a lot about how OT actually works in the field.Strengths and Opportunities
The encouraging part of this advisory is that Schneider Electric has given operators something concrete to do. The patch, the configuration change, and the restart requirement are all operationally understandable, and the vendor has tied them to specific system roles rather than issuing a vague warning. That clarity reduces ambiguity at a time when OT teams do not have the luxury of trial and error.- Clear vendor fix path through ProLeiT-2025-001.
- Specific hardening steps for Redis rather than generic advice.
- Configuration templates reduce drift across many workstations.
- Restart guidance helps ensure the runtime fix actually takes effect.
- Scope is defined by version and deployment role, which helps prioritization.
- Security posture improves if eval is disabled permanently.
- Opportunity to audit broader OT access and account privilege design.
Risks and Concerns
The main concern is that the flaw sits behind authentication but still exposes a path to memory corruption. That combination is especially dangerous because it can be dismissed too easily by teams that assume login requirements make a bug low-risk. In OT environments, authenticated misuse can be every bit as damaging as anonymous remote exploitation, especially when privileged operator or engineering accounts are involved.- Authenticated access does not equal safe access in OT.
- Use-after-free bugs can become reliable RCE if exploitation matures.
- Shared or over-privileged accounts expand the blast radius.
- Restart requirements may slow deployment in 24/7 facilities.
- Configuration drift can leave some nodes unprotected.
- Emergency-mode stations may be overlooked during patching.
- Incomplete segmentation can turn a local issue into a network-wide problem.
The human-factor risk
Industrial incidents often exploit process gaps more than pure software defects. If one plant applies the patch while another waits for a maintenance shutdown, the organization now has a split security posture. That variation creates a soft target for attackers who know that operational delays are common. In practice, the weakest site often defines the real risk for the whole enterprise.The supply-chain lesson
Third-party dependency risk is now unavoidable in industrial automation. The question is no longer whether a vendor uses open-source components, but whether the vendor can identify, isolate, and fix the failure mode quickly enough. Customers should expect more of these advisories and should budget not only for patches, but for testing, restart windows, and rollback planning.What to Watch Next
The next few weeks will tell us whether this advisory becomes a quiet patch cycle or a more disruptive operational event. The most important signal is how quickly affected organizations can deploy ProLeiT-2025-001 and whether the recommended Redis hardening steps are adopted broadly or left half-finished in the field. If operators treat the patch as enough on its own, they may leave dangerous command paths enabled longer than intended.A second thing to watch is whether additional guidance follows for specific deployment variants, especially sites that rely heavily on emergency-mode workstations or heavily customized configurations. Industrial vendors often publish follow-up notes when initial mitigations meet real-world friction. If that happens here, it will likely be because plant teams need help reconciling security hardening with uptime constraints.
Finally, this advisory could encourage more customers to audit their use of Redis, Lua scripting, and privileged automation services across the rest of the plant estate. That would be a healthy side effect. A vulnerability like this should not just trigger a single fix; it should prompt a broader review of which services really need scripting enabled at all.
- Verify whether any Plant iT/Brewmaxx deployments remain on version 8.2.1 or earlier.
- Confirm that ProLeiT-2025-001 is installed everywhere it should be.
- Check that eval is disabled on all affected Redis instances.
- Reboot patched servers and workstations and validate services afterward.
- Review account privilege, segmentation, and remote-access controls site-wide.
Source: CISA Schneider Electric Plant iT/Brewmaxx | CISA