Quest’s product update at Microsoft Ignite 2025 marks a clear push to put generative AI into the middle of identity security for hybrid Microsoft estates — adding AI-written risk summaries, a Security Guardian Agent for Microsoft Security Copilot, workload‑identity coverage for Entra ID, and a bundled Identity Modernization Suites strategy that ties migration, security, audit, backup, and recovery into a single vendor story.
Background
Enterprises running Microsoft-based identities face a growing list of pressures: sprawling hybrid Active Directory deployments, accelerating cloud-native workload identities in Microsoft Entra, exploding alert volumes, and the arrival of agentic AI and automated workflows that multiply non-human identities. Vendors and platform providers are responding with tools that pair automation, context-aware analytics, and orchestration to shorten the gap from detection to containment. Quest positions its latest release as one of those answers, combining new AI-driven summaries and Copilot-agent integrations with migration and data management enhancements intended to create an “AI-ready” identity foundation.What Quest announced — the headlines
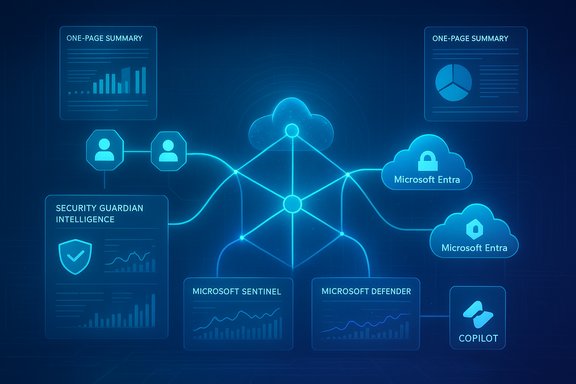
- AI‑generated security assessment summaries inside Security Guardian Intelligence, including one‑page executive reports that highlight critical identity gaps and prioritized remediation steps.
- A Security Guardian Agent published to the Microsoft Security Store that integrates identity context into Microsoft Security Copilot, and tighter integration with Microsoft Sentinel and Microsoft Defender for Identity.
- Expanded identity coverage with Security Guardian Audit (a cloud‑native audit and compliance offering) and discovery/protection for non‑human / workload identities in Microsoft Entra ID.
- New Identity Modernization Suites — three tiers of a combined migration, security, audit, backup and recovery platform designed to reduce risk during cloud migrations.
- Enhancements to On Demand Migration for the Microsoft Power Platform, including Power Apps discovery and a Power Automate discovery preview.
- Progress on the erwin Data Management Platform, with additional GenAI capabilities to accelerate delivery of governed, trusted data products.
Why this matters: the identity problem at Microsoft scale
Modern Microsoft identity environments often contain a mix of on‑premises Active Directory (AD), synchronized Azure AD/Entra tenants, service principals, managed identities, and numerous automation credentials. Microsoft’s own guidance frames these machine or workload identities (service principals, applications, managed identities) as distinct from human users and highlights the unique risks they introduce — credential sprawl, unattended access, and high‑impact privileges that are often unmanaged by conventional IAM approaches. Addressing those gaps requires tooling that can both discover and reason about identity relationships across hybrid estates. Microsoft has also been building an ecosystem around Security Copilot and a dedicated Microsoft Security Store for partner agents and integrations — a distribution and orchestration layer for AI agents that can enrich alerts, prioritize incidents, and automate routine remediation tasks. Vendors that integrate into that ecosystem can present their specialized contextual engines — in this case, identity context — directly to security analysts working inside Microsoft’s security workflows. That is the architectural premise behind Quest’s Copilot agent announcement.Deep dive: Security Guardian gets GenAI summaries and Copilot integration
What the AI summaries do
- Generate an AI‑written, one‑page executive summary that surfaces the most critical identity misconfigurations, exposures, and prioritized remediation steps. The feature is pitched to reduce the barrier for teams that may lack deep AD expertise and to speed stakeholder communications and remediation approvals.
- Provide prioritized remediation guidance that maps findings to action items, intended to cut investigation and response time compared with manual triage. This is presented as part of Security Guardian Intelligence, Quest’s GenAI‑enabled layer for identity insight.
The Copilot agent and Microsoft integration
- The Security Guardian Agent is available through the Microsoft Security Store and is built to work with Microsoft Security Copilot, feeding identity context, findings, and remediation actions directly into Copilot workflows. This integrates Quest’s detections with Microsoft Sentinel’s hunting graphs and with Defender for Identity telemetry.
- Microsoft’s approach to embedding partner agents in Copilot and Sentinel focuses on agentic workflows that automate routine analysis, enrich alerts with contextual relationships, and orchestrate response playbooks at machine speed — a capability Quest is leveraging for identity risk prevention and containment.
Identity lifecycle coverage: audit, workload identities, and recovery
Cloud-native auditing and compliance
Quest has introduced Security Guardian Audit, a cloud‑native auditing solution designed to replace legacy on‑premise auditing stacks with scalable retention, reporting, and compliance-focused controls. The rationale: modern regulatory needs and e‑discovery requirements increasingly demand longer retention and centralized cloud auditing. Quest frames this as bringing the strengths of its previous Change Auditor tooling into a cloud‑native architecture.Workload identity coverage for Entra ID
The update explicitly calls out enhanced visibility for Entra workload identities — service principals, managed identities, and application objects — to detect over‑privileged or exposed non‑human identities and to provide remediation guidance. Microsoft’s Entra Workload Identity model recognizes the unique risk posture of machine identities, and the industry is moving to treat those identities as first‑class security citizens. Quest’s work here is directly aimed at that gap.Faster recovery: vendor claims to verify cautiously
Quest asserts that, when paired with Quest Disaster Recovery for Identity, its suite can accelerate identity recovery from incidents “up to 90 percent faster,” and that stopping exposure and recovery faster can save organizations millions in downtime costs. These figures are presented in vendor materials and are plausible for certain recovery workflows, but should be treated as vendor performance claims until validated in independent customer case studies or third‑party benchmarks. Independent verification of precise percentages and dollar savings is not available in public independent reporting at the time of writing.Migration and modernization: Identity Modernization Suites and On Demand Migration
Identity Modernization Suites — an integrated approach
Quest’s new Identity Modernization Suites package migration capabilities, security, audit, backup, and recovery into a tiered offering meant to reduce migration risk when moving from legacy on‑premises AD to cloud‑native Entra ID configurations. The suites include pre‑migration risk assessments and secure backup and recovery to support large transformations. Quest positions this as an attempt to reduce tool sprawl and give a single vendor pathway for identity modernization at scale.Power Platform coverage: discovery for low-code assets
Quest is expanding On Demand Migration to include discovery for Microsoft Power Platform assets — Power Apps and Power Automate — acknowledging that low‑code/no‑code assets are a growing source of identity, data, and integration complexity. This is a pragmatic addition: Power Platform artifacts frequently contain embedded connections and service accounts that must be inventoried during tenant consolidations, divestitures, or mergers.Data management: erwin and GenAI
Quest’s erwin Data Management Platform was re‑positioned earlier in the year as a unified data management layer for AI, and today’s updates extend GenAI capabilities to accelerate the creation and distribution of trusted data products. The linkage here is strategic: secure, modern identities are a precondition for trusted data mobility and governance, and Quest is packaging identity, migration, and data governance into a single narrative about AI readiness.Strengths: where this offering can help teams today
- Contextual identity insights at scale. By combining Active Directory and Entra context with AI‑driven summaries, Security Guardian can reduce the cognitive load on understaffed SOCs and provide a clear remediation path for high‑impact identity exposures.
- Faster operational response through Copilot agents. Integration with Microsoft Security Copilot and Sentinel means identity signals can be enriched and acted on inside the analyst workflow, shortening mean time to detection and containment when playbooks are correctly configured. Microsoft’s Security Copilot and Security Store are explicitly designed to enable partner agents to operate in these workflows.
- Broad lifecycle coverage. Between audit, prevention, workload identity discovery, migration tooling, and disaster recovery, Quest’s messaging focuses on covering the full identity lifecycle — detection, containment, remediation, migration, and recovery. That breadth can be operationally valuable during large Microsoft 365/Entra transformations.
- Reduced tool fragmentation for Microsoft customers. Packaging migration, identity security, and data governance reduces the need for multiple point tools, which can simplify procurement and operational overhead for large enterprises.
Risks and caveats — what security teams should watch for
- Vendor claims versus independent proof. Key numbers in the announcement — such as “moving more than 200 petabytes” or “up to 90 percent faster recovery” and “more than three billion chat messages” migrated — are presented as vendor claims. These are notable but should be validated through customer references or third‑party audits before being used in procurement decisions. Treat these figures as marketing claims until independently verified.
- AI summarization risks: hallucination and correctness. Generative AI can accelerate analysis, but it can also produce inaccurate or overconfident wording if the underlying evidence is weak or misinterpreted. Executive summaries and remediation guidance generated by AI should be treated as advisory outputs that require human validation, at least until the organization has confidence in the model’s precision and traceability. Implement guardrails that log evidence, link findings to raw telemetry, and retain human sign‑off for high‑impact changes.
- Automation and blast radius. Copilot agents that execute remediations or orchestration steps reduce time to response — but they also increase the blast radius for misapplied automations. Access controls, change review gates, and test environments are essential to prevent automated fixes from inadvertently breaking production authentication flows or rolling back legitimate configurations. Microsoft’s agent model presumes analyst‑in‑the‑loop patterns; organizations must adopt strict role separation and least‑privilege for agent execution.
- Identity sprawl and non‑human identity explosion. The scale of machine identities is growing rapidly. Microsoft’s guidance highlights the difficulty of managing non‑human identities; vendor tooling can help discover and prioritize them, but organizations must commit to lifecycle policies — short‑lived credentials, managed identities, rotation, and regular attestation — to prevent recurring risk. Detection alone is not governance.
- Operational complexity and vendor lock‑in. Consolidating migration, security, audit, backup, and recovery into a single vendor suite simplifies procurement but can increase lock‑in risk. Organizations should evaluate exportability of audit logs, interoperability with other security tools, and the ability to retain forensic data independently from the vendor. Ask hard questions about data portability, API access, and cross‑tool validations.
- Regulatory and privacy implications. Automated identity discovery and long‑term audit retention interact with privacy laws, data residency, and cross‑border compliance. Ensure that the auditing and AI features meet regulatory obligations for access control, data minimization, and retention. Cloud‑native audit solutions must include controls for legal holds and selective export for eDiscovery.
Practical guidance: how to evaluate and pilot these tools
- Define measurable objectives. Start pilots with clear goals — e.g., reduce AD privileged escalation windows by X days, reduce mean time to remediation for identity alerts by Y percent — and instrument baseline metrics.
- Validate AI outputs against evidence. Require that every AI‑generated summary includes links to the raw findings and a confidence indicator; verify a statistically significant sample of recommendations before allowing automated remediation.
- Stage automation permissions. Begin with read‑only Copilot agent actions that propose playbook steps, then progress to orchestrated changes after a controlled approval policy is in place.
- Inventory and attestation programs. Combine discovery outputs from the vendor with internal CMDB/asset inventories and mandate periodic attestation for all privileged service principals and managed identities.
- Verify recovery SLAs in testing. Conduct tabletop and live recovery drills that exercise Quest’s recovery tooling (or any vendor recovery capability) and measure the claimed reductions in recovery time in your environment. Treat vendor performance claims as hypotheses to be proven in your tests.
Recommended procurement questions
- What evidence‑backed case studies can the vendor provide showing real recovery‑time reductions and documented business impact?
- How are AI outputs generated, what data is used, and can customers audit the model inputs and outputs for compliance?
- What controls exist to prevent automated playbooks from executing destructive changes? Is there full RBAC for agent operations?
- How does the vendor integrate with third‑party SIEMs or ticketing systems outside the Microsoft stack? Will audit logs remain accessible if the vendor is offboarded?
- For Identity Modernization Suites: how are backups encrypted, where are they stored, and what is the recovery RTO/RPO in third‑party testing?
The wider market context: Microsoft’s agent ecosystem and identity priorities
Microsoft has been actively enabling partner agents and a marketplace for security integrations. The Microsoft Security Store and Security Copilot agents are intended to create an ecosystem where specialized partner engines (for identity, network, or data security) provide domain expertise directly inside Microsoft workflows. That architectural evolution amplifies the reach of vendors like Quest but also changes the security operations model: teams must now manage a catalog of agents, their permissions, and their operational boundaries. At the same time, Microsoft’s Entra Workload Identity guidance makes it clear that machine identities require different governance than humans. Any vendor claiming to secure that category must show robust discovery, attestation, and remediation capabilities — plus operational playbooks for long‑term lifecycle management. Quest’s announcements aim at that gap, but adoption success depends on organizational discipline and cross‑team coordination.Final assessment
Quest’s announcements represent a logical step: adding generative AI summaries, Copilot agent integration, and broader lifecycle controls responds to real pain points in hybrid Microsoft identity management. The product story is coherent — identity detection, AI‑driven prioritization, automated action through Copilot, migration tooling, and governed data foundation through erwin. For Microsoft‑centric organizations seeking tighter identity control during large cloud migrations, the integrated vendor approach offers a compelling operational simplification. However, the initiative is not a silver bullet. Customers should treat vendor performance metrics as hypotheses to be validated, maintain human oversight of AI outputs, and institute strict controls for any automation that performs remediations. Non‑human identity proliferation and automation complexities introduce new governance responsibilities that tooling alone cannot eliminate. The real benefit will accrue to teams that pair these new controls with hardened lifecycle policies: short‑lived credentials, automated rotation, attestation cadence, and conservative automation permissions.Practical next steps for Windows and Microsoft identity teams
- Pilot Security Guardian Intelligence in a segmented environment and compare AI summaries to manual assessments for accuracy and actionability.
- Map all discovered workload identities to owners and attach an attestation cadence as part of migration plans.
- Integrate Copilot agent playbooks with ticketing and change‑control systems so proposed remediations create auditable workflows.
- Test disaster recovery playbooks and measure actual RTO/RPO improvements during controlled failover exercises.
- Review data portability and retention terms for cloud audits and backups before committing to long‑term retention strategies.
The melding of AI summarization, Copilot agents, and lifecycle tooling makes Quest’s Security Guardian updates a noteworthy entry in the Microsoft identity security ecosystem. For teams grappling with hybrid AD, Entra workload identities, and migration complexity, the suite offers practical capabilities — but success will hinge on careful validation of vendor claims, disciplined governance of AI and automation, and rigorous testing of recovery and remediation playbooks. In short: promising technology, but organizational craftsmanship will determine the security outcomes.
Source: SecurityBrief Asia Quest unveils AI-driven tools for Microsoft identity security
