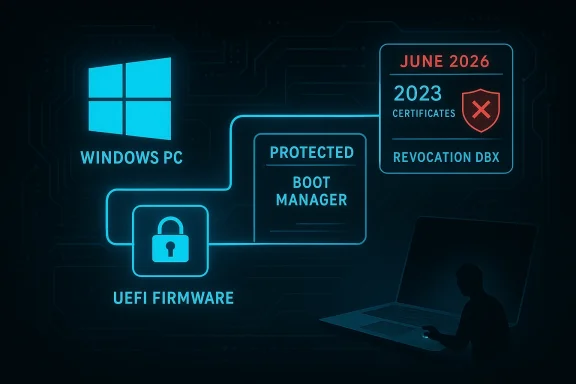
Secure Boot looks simple from the outside: if the boot chain is trusted, the PC starts clean; if it is not, the machine should refuse to boot risky code. But the reality is messier. The system does not fail because attackers are “breaking” Secure Boot in some dramatic cryptographic sense; it fails because old, still-signed boot components can be abused as trusted launch pads, and Microsoft has had to balance revocation against the risk of breaking real machines. Microsoft’s own guidance now says Secure Boot certificates issued in 2011 begin expiring in June 2026, and that devices must move to the newer 2023 certificate set to keep receiving boot-chain protections com]
Secure Boot is one of Windows’ most important pre-OS defenses, but it is not a magic shield. It depends on firmware trust stores, signed boot managers, and a revocation model that has to account for legacy hardware, third-party operating systems, and recovery media. That is why Microsoft now warns that some systems mamware updates, and why the company says most devices will be updated automatically while some will not
The MakeUseOf framing is directionally right on the most important point: the bypass problem is less about “cracking” Secure Boot than about abusing trust that remains valid too long. Microsoft’s BlackLotus response, for example, centered on CVE-2022-21894 and later guidance around CVE-2023-24932, which describes how vulnerable Windows boot managers can still be used as a foothold if revocations are not applied
What the casual-reader version often underplays is operational scale. Microsoft’s support docs now explicitly say that if devices miss the certificate migration, they may lose the ability to receive future boot-stage security fixes, including Windows Boot Manager updates and Secure Boot revocation list changes. In other words, the risk is not just an immediate exploit; it is a long-term security stagnation problem
There is also a subtle but crucial distinction between “secure boot is bypassable” and “most users are currently at imminent risk.” Microsoft and the NSA both describe bootkits as especially dangerous because they operate before the OS and can interfere with BitLocker, HVCI, and Defender. But exploitation still typically requires physical access or administrative control, so the practical exposure depends heavily on the threat model and device stewardship
That is why public Secure Boot bypasses have historically been so alarming. BootHole, BlackLotus, and related issues did not “defeat” the cryptography; they exploited signed but vulnerable software that still sat inside the trust envelope. Microsoft’s BlackLotus guidance describes UEFI bootkits as dangerous precisely because they run before the OS and can disable or weaken layered protections that users assume are always present
The current certificate-rotation story is the long tail of that same design. Microsoft says the current Secure Boot certificates are the original 2011 set, and they begin expiring in June 2026. The company is rolling out new 2023 certificates to maintain continuity, but it also warns that some systems may need firmware updates or other manual intervention to complete the transition
That tension explains the pacing of Microsoft’s recent updates. The vendor has been adding not just boot-chain changes, but also status visibility and rollout controls, including Windows Security app indicators that tell users whether their device is fully updated, partially updated, or unable to receive automated Secure Boot certificate updates due to firmware limitations
The result is a downgrade-style attack. If an attacker can force a machine to load an older boot manager version, they can potentially activate a flaw Microsoft has already fixed in newer releases but has not yet fully revoked at the firmware trust layer. That is why the Secure Boot DBX matters so much: it is the list that tells firmware which formerly trusted items are now forbidden
A practical summary:
The important nuance is that BlackLotus did not prove Secure Boot was meaningless. It proved that revocation lag is exploitable. When the revocation list has not caught up with known vulnerable boot components, Secure Boot still trusts them, and an attacker can use that trust against the machine
This is why bypasses are often about time, not genius. Attackers look for the longest-lived signed artifact that still opens the door. Defenders then have to revoke it without causing collateral damage. That lag is the gap where Secure Boot bypasses live
That helps explain the vendor’s caution. Automatic revocation can break bootable media, interfere with older firmware, and strand systems that depend on recovery workflows built around old signatures. Microsoft’s guidance explicitly notes that the transition affects boot components and revocation lists, not just one neat patch in Windows Update
That is also why the rollout is staged. Microsoft has been pushing certificate updates through Windows servicing channels, adding status visibility, and using targeted updates to prepare the boot environment. The company is trying to avoid a world where one revocation event creates a fleet of expensive recovery jobs
The result is frustrating but rational: Microsoft is prioritizing continuity, which inevitably slows universal enforcement. In security terms, that is less satisfying than a hard revocation, but in fleet-management terms it is often the only viable path
That distinction matters because it creates a silent-risk category. The machine appears fine, the user sees no obvious failure, and yet the platform gradually becomes easier to attack at the earliest stage of startup. That is exactly the sort of security decay that is hard to detect until after damage has already occurred
That is a helpful move because it turns an abstract certificate lifecycle issue into something visible to users and administrators. But visibility is not the same as remediation. Users still have to act, and for many home systems, they probably will not know what the warning means until the day it matters
The biggest enterprise risk is partial deployment. If some endpoints receive the 2023 certificates and some do not, support teams can end up with a split fleet where the same security baseline means different things on different devices. That creates a long-term compliance problem, not just a patching problem
And unlike in enterprise, the consumer is less likely to recognize the warning signs. A machine that still boots normally feels healthy, even if it is slowly losing early-boot resilience. That is why Microsoft’s status messaging matters, even if it will reach only a fraction of users in time
That is why this is not just a security update. It is an ecosystem migration. And like all ecosystem migrations, the hard part is not the theory; it is getting every dependency to move together
That is also why Microsoft and security agencies emphasize endpoint hardening at the device level. If the attacker can touch the machine, the boot chain becomes the first line of defense, not the last. Losing that line can defeat OS-level controls before they even begin
This is also why the problem feels recurring. The patch fixes one version, but the old signed version remains legally acceptable to Secure Boot until the revocation list says otherwise. That lag is the exploit surface
The approach also fits Microsoft’s broader stance on boot-chain resiliency: use the servicing stack, use the Windows Security app, and use targeted updates to prepare the environment ahead of the 2026 expiration window. It is boring operationally, but that is often the right kind of boring for firmware trust infrastructure
It also explains why Microsoft has not simply flipped a universal switch. The company is trying to protect the boot chain without causing catastrophic breakage for devices that depend on older firmware behavior or recovery paths. That is an ugly but necessary compromise
That strategy is a sign of maturity, not weakness. The platform is too diverse for one-size-fits-all firmware trust migration, and Microsoft is finally treating it that way
The deeper question is whether Secure Boot can evolve without losing the compatibility that made Windows successful in the first place. That tension will not disappear, because the operating system has to support a vast hardware estate and a broad range of recovery and boot scenarios. But the certificate refresh shows Microsoft is now treating boot trust as a living system, not a static feature
What to watch next:
Source: MakeUseOf Why Windows Secure Boot can be bypassed so easily (and what Microsoft isn't telling you)
 Overview
Overview
Secure Boot is one of Windows’ most important pre-OS defenses, but it is not a magic shield. It depends on firmware trust stores, signed boot managers, and a revocation model that has to account for legacy hardware, third-party operating systems, and recovery media. That is why Microsoft now warns that some systems mamware updates, and why the company says most devices will be updated automatically while some will notThe MakeUseOf framing is directionally right on the most important point: the bypass problem is less about “cracking” Secure Boot than about abusing trust that remains valid too long. Microsoft’s BlackLotus response, for example, centered on CVE-2022-21894 and later guidance around CVE-2023-24932, which describes how vulnerable Windows boot managers can still be used as a foothold if revocations are not applied
What the casual-reader version often underplays is operational scale. Microsoft’s support docs now explicitly say that if devices miss the certificate migration, they may lose the ability to receive future boot-stage security fixes, including Windows Boot Manager updates and Secure Boot revocation list changes. In other words, the risk is not just an immediate exploit; it is a long-term security stagnation problem
There is also a subtle but crucial distinction between “secure boot is bypassable” and “most users are currently at imminent risk.” Microsoft and the NSA both describe bootkits as especially dangerous because they operate before the OS and can interfere with BitLocker, HVCI, and Defender. But exploitation still typically requires physical access or administrative control, so the practical exposure depends heavily on the threat model and device stewardship
Background
Secure Boot was designed as a trust gate for the earliest stage of the Windows startup sequence. Firmware checks signatures before handing off to the boot manager, and only signed, trusted components are supposed to load. That design works well until one of the trusted components itself contains a flaw, at which point the whole chain inherits the weaknessThat is why public Secure Boot bypasses have historically been so alarming. BootHole, BlackLotus, and related issues did not “defeat” the cryptography; they exploited signed but vulnerable software that still sat inside the trust envelope. Microsoft’s BlackLotus guidance describes UEFI bootkits as dangerous precisely because they run before the OS and can disable or weaken layered protections that users assume are always present
The current certificate-rotation story is the long tail of that same design. Microsoft says the current Secure Boot certificates are the original 2011 set, and they begin expiring in June 2026. The company is rolling out new 2023 certificates to maintain continuity, but it also warns that some systems may need firmware updates or other manual intervention to complete the transition
That tension explains the pacing of Microsoft’s recent updates. The vendor has been adding not just boot-chain changes, but also status visibility and rollout controls, including Windows Security app indicators that tell users whether their device is fully updated, partially updated, or unable to receive automated Secure Boot certificate updates due to firmware limitations
Why Secure Boot Bypasses Work
The core reason Secure Boot can be bypassed is that trust is inherited. If a bootloader is Microsoft-signed, Secure Boot allows it to run. If that signed bootloader is vulnerable, an attacker may be able to use it as a legitimate trampoline into unsigned or malicious code without ever defeating the signature system itselfTrusted code can still be dangerous
This is the uncomfortable truth behind many firmware and boot-chain bugs: signed does not mean safe forever. Microsoft’s own boot-manager revocation guidance for CVE-2023-24932 exists because the BlackLotus campaign leveraged a vulnerable but trusted component rather than inventing a new cryptographic bypassThe result is a downgrade-style attack. If an attacker can force a machine to load an older boot manager version, they can potentially activate a flaw Microsoft has already fixed in newer releases but has not yet fully revoked at the firmware trust layer. That is why the Secure Boot DBX matters so much: it is the list that tells firmware which formerly trusted items are now forbidden
A practical summary:
- The attacker does not need to forge Microsoft’s signature.
- The attacker may only need to find an older signed binary that remains trusted.
- Once loaded, that binary can undermine the boot chain.
- The defense is revocation, but revocation is operationally risky.
- The risk window can persist for years if organizations do not apply the fix
BlackLotus made the issue real
BlackLotus changed the conversation because it was not theoretical. Microsoft’s security blog says the campaign targeted CVE-2022-21894, and that UEFI bootkits can interfere with BitLocker, HVCI, and Defender before Windows protections fully load. That means a pre-OS compromise can neutralize other defenses users think they can rely on laterThe important nuance is that BlackLotus did not prove Secure Boot was meaningless. It proved that revocation lag is exploitable. When the revocation list has not caught up with known vulnerable boot components, Secure Boot still trusts them, and an attacker can use that trust against the machine
The Windows trust chain is only as strong as its oldest signed links
That is the fundamental weak point in any large compatibility ecosystem. Windows must support older hardware, older recovery tools, and cross-boot environments; as a result, it cannot instantly revoke every legacy component the moment a flaw is found. Microsoft’s Secure Boot documents make clear that the 2011 certificate family has to be replaced carefully because the same trust infrastructure is used across OEM firmware and even third-party operating systemsThis is why bypasses are often about time, not genius. Attackers look for the longest-lived signed artifact that still opens the door. Defenders then have to revoke it without causing collateral damage. That lag is the gap where Secure Boot bypasses live
Why Microsoft Has Been Slow to Push Automatic Revocation
Microsoft’s public guidance strongly suggests that the company is not ignoring the problem; it is managing a dangerous tradeoff. Revoking the wrong thing, or revoking it too aggressively, can leave a machine unable to boot securely—or in the worst case, unable to boot at all until recovery steps are takenCompatibility is not a side issue
The MakeUseOf article correctly points out the operational burden of manual remediation. Microsoft’s own support documentation says the new 2023 certificates are being rolled out now, but also that some systems may require additional firmware updates. The support page for IT professionals goes further, explaining that devices need to be updated before the 2011 certificates expire or they risk losing future security protections for the boot chainThat helps explain the vendor’s caution. Automatic revocation can break bootable media, interfere with older firmware, and strand systems that depend on recovery workflows built around old signatures. Microsoft’s guidance explicitly notes that the transition affects boot components and revocation lists, not just one neat patch in Windows Update
Why the fix is more than a checkbox
A lot of security problems are solved with a single patched binary. Secure Boot certificate updates are different because they touch platform trust, not just an application. Microsoft’s guidance makes the consequences plain: if devices are not updated, they will stop receiving future boot security updates and may fall out of complianceThat is also why the rollout is staged. Microsoft has been pushing certificate updates through Windows servicing channels, adding status visibility, and using targeted updates to prepare the boot environment. The company is trying to avoid a world where one revocation event creates a fleet of expensive recovery jobs
The enterprise dilemma
For enterprises, the math is even harder. An update that protects one boot-chain flaw but triggers downtime on a slice of endpoints is not “just a patch.” It becomes an asset-inventory problem, a firmware-validation problem, and a support-capacity problem all at once. That is one reason Microsoft’s enterprise guidance emphasizes self-managed mitigation paths instead of forcing the change universally at the same momentThe result is frustrating but rational: Microsoft is prioritizing continuity, which inevitably slows universal enforcement. In security terms, that is less satisfying than a hard revocation, but in fleet-management terms it is often the only viable path
What the 2026 Certificate Expiration Means
The June 2026 expiration window is the biggest near-term reason Secure Boot is back in the spotlight. Microsoft says the 2011 certificates begin expiring in June 2026 and may expire by October 2026, which means machines that miss the transition will progressively lose the ability to accept future boot-chain protectionsWhy the expiry matters even if the PC still boots
A common misunderstanding is that an expired Secure Boot certificate means a machine immediately stops working. Microsoft says that is not the case: the device will still start and standard Windows updates will still install. What changes is the system’s ability to receive future boot security fixes and maintain a fully protected early-boot postureThat distinction matters because it creates a silent-risk category. The machine appears fine, the user sees no obvious failure, and yet the platform gradually becomes easier to attack at the earliest stage of startup. That is exactly the sort of security decay that is hard to detect until after damage has already occurred
Microsoft is trying to surface the problem earlier
The Windows Security app now includes Secure Boot status indicators tied to the certificate update state. Microsoft says some devices may show a “Requires action” status if they cannot receive the automated update due to firmware or hardware limitations, and that the badge can change to a red stop icon as early as June 2026 in some casesThat is a helpful move because it turns an abstract certificate lifecycle issue into something visible to users and administrators. But visibility is not the same as remediation. Users still have to act, and for many home systems, they probably will not know what the warning means until the day it matters
A simple timeline
- Microsoft-issued Secure Boot certificates from 2011 begin expiring in June 2026.
- Devices that have received the new 2023 certificates remain protected.
- Devices that miss the update can still boot, but lose future boot-chain servicing.
- Older vulnerable boot components remain more useful to attackers if revocation is incomplete.
- Microsoft and OEMs continue to push updates, but not every device can be updated automatically
Enterprise Impact vs Consumer Impact
The same Secure Boot flaw has very different consequences depending on whether the device is managed or unmanaged. For enterprises, the issue is mostly about governance, inventory, and deployment discipline. For consumers, it is more about awareness, firmware support, and the odds that the machine simply never gets the right updateEnterprises have tools, but also more failure points
Large organizations can inventory hardware, push firmware updates, and use policy to validate boot state. That is an advantage. But they also have a wider mix of models, lifecycle states, and recovery media, which means certificate rotation can expose hidden dependencies that a consumer laptop would never encounterThe biggest enterprise risk is partial deployment. If some endpoints receive the 2023 certificates and some do not, support teams can end up with a split fleet where the same security baseline means different things on different devices. That creates a long-term compliance problem, not just a patching problem
Consumers mostly need automatic updates and good hardware support
For home users, Microsoft says the new certificates will be delivered through regular Windows Update channels for most supported systems, and most people do not need to do anything. That is the good news. The bad news is that older systems, firmware-stale systems, and devices with unusual boot configurations may not fit the automatic pathAnd unlike in enterprise, the consumer is less likely to recognize the warning signs. A machine that still boots normally feels healthy, even if it is slowly losing early-boot resilience. That is why Microsoft’s status messaging matters, even if it will reach only a fraction of users in time
The recovery-media problem is easy to miss
One of the most practical complications is boot media. Microsoft’s guidance and related rollout notes make clear that changes to the boot trust chain can affect recovery media, system images, and other tools that rely on older signing assumptions. That can create a nasty surprise when a system needs emergency recovery and the rescue media no longer behaves the way administrators expectThat is why this is not just a security update. It is an ecosystem migration. And like all ecosystem migrations, the hard part is not the theory; it is getting every dependency to move together
How Attackers Actually Exploit the Weakness
Attackers are not usually trying to attack the cryptographic root directly. They are trying to reach a signed component that can be exploited in a downgraded or legacy state, then use that foothold to disable or evade protections deeper in the boot chain. That is why the threat model is so persistent even after Microsoft patches the individual bugPhysical access changes everything
Many Secure Boot bypass paths require either physical access or some form of administrative control. That narrows the risk compared with a network worm, but it does not make the issue trivial. A stolen laptop, a malicious insider, or a service technician with the wrong tools can all create a realistic exploitation pathThat is also why Microsoft and security agencies emphasize endpoint hardening at the device level. If the attacker can touch the machine, the boot chain becomes the first line of defense, not the last. Losing that line can defeat OS-level controls before they even begin
Downgrade attacks are the real pattern
Downgrade attacks are attractive because they reuse trust. If the firmware still trusts a vulnerable boot manager, the attacker does not need a new exploit chain; they only need to place the older component back in the path. That is precisely the sort of issue Microsoft’s revocation guidance is meant to stop, and it is why DBX updates are so importantThis is also why the problem feels recurring. The patch fixes one version, but the old signed version remains legally acceptable to Secure Boot until the revocation list says otherwise. That lag is the exploit surface
Why bootkits are so nasty
Bootkits are high-value malware because they operate early and persistently. Microsoft says they can interfere with Defender, BitLocker, and HVCI, which means they can weaken not just one security control but the whole stack built on top of the boot process. That makes them disproportionately dangerous relative to the number of machines they actually infectWhat Microsoft Is Doing Now
Microsoft is not standing still. The company has published guidance for IT professionals, consumer-facing guidance on certificate expiration, and newer status reporting inside Windows Security. Those steps suggest a coordinated platform effort rather than a one-off patch cycleCertificate rollout is now part of normal servicing
Microsoft says the new 2023 certificates are being rolled out through Windows Update and related servicing channels for most supported devices. That is the least disruptive path, because it blends platform trust changes into ordinary maintenance instead of forcing a separate security migration event on every user at onceThe approach also fits Microsoft’s broader stance on boot-chain resiliency: use the servicing stack, use the Windows Security app, and use targeted updates to prepare the environment ahead of the 2026 expiration window. It is boring operationally, but that is often the right kind of boring for firmware trust infrastructure
Revocation guidance remains the hard edge
For the BlackLotus-era issue, Microsoft’s support pages still point administrators to explicit revocation and boot-manager mitigation steps. That tells us the company sees this as a platform-hardening campaign, not just a malware cleanup exerciseIt also explains why Microsoft has not simply flipped a universal switch. The company is trying to protect the boot chain without causing catastrophic breakage for devices that depend on older firmware behavior or recovery paths. That is an ugly but necessary compromise
The High Confidence Database matters
Microsoft has also been using a High Confidence Database approach to identify which systems can safely receive automated certificate updates. That sounds obscure, but it is actually a very practical tool: it lets Microsoft target update behavior based on device class and capability rather than pretending every Windows machine can absorb the same boot-level change in the same wayThat strategy is a sign of maturity, not weakness. The platform is too diverse for one-size-fits-all firmware trust migration, and Microsoft is finally treating it that way
Strengths and Opportunities
Microsoft’s current approach has real strengths, especially if the company can keep the rollout smooth and make the status messaging understandable to ordinary users. The biggest opportunity is to turn a painful security lifecycle event into a permanent improvement in how Windows manages boot trust. Done right, this could reduce the blast radius of future bootkit campaigns and make Secure Boot more resilient over the next decade.- Automatic delivery of the 2023 certificates to most supported devices reduces friction.
- Windows Security status indicators make boot trust more visible to users.
- Staged rollout lowers the chance of mass breakage.
- DBX revocation gives Microsoft a way to invalidate known-bad boot components.
- Enterprise guidance gives admins a roadmap rather than forcing guesswork.
- Bootkit awareness is now much higher because of BlackLotus.
- Future platform discipline may prevent another long-lived revocation backlog
Risks and Concerns
The risks are substantial because the problem sits at the intersection of security, compatibility, and recovery. Any mistake can leave users in a worse place than before, and any delay leaves a trust gap open longer than it should be. The worst outcome is not necessarily a dramatic boot failure; it is a quiet, widespread security downgrade that nobody notices until attackers exploit it.- Manual steps mean many users and even some admins will simply not complete the fix.
- Firmware fragmentation makes automated deployment uneven.
- Recovery media breakage can create support nightmares.
- Legacy hardware may never fully support the new certificate chain.
- Misconfigured revocation could strand devices or cause boot failures.
- Security complacency may persist because devices still appear to boot normally.
- Physical-access attacks remain realistic for laptops, kiosks, and shared systems
Looking Ahead
The next major checkpoint is the June 2026 expiration window, and it will be a revealing test of how well Microsoft’s staged rollout has actually worked. If the automatic update path reaches most supported systems, the ecosystem will absorb the transition with manageable disruption. If not, the industry will discover just how many Windows devices were quietly relying on legacy trust anchors all alongThe deeper question is whether Secure Boot can evolve without losing the compatibility that made Windows successful in the first place. That tension will not disappear, because the operating system has to support a vast hardware estate and a broad range of recovery and boot scenarios. But the certificate refresh shows Microsoft is now treating boot trust as a living system, not a static feature
What to watch next:
- Whether Windows Security shows clear, understandable certificate status on more devices.
- How many systems require manual firmware intervention instead of automatic updates.
- Whether Microsoft expands DBX revocations further for known vulnerable boot managers.
- How OEM firmware teams handle older models nearing the expiration deadline.
- Whether enterprises build Secure Boot certificate checks into routine compliance scans.
- Whether recovery-media incompatibilities surface during real-world support cases.
- Whether future bootkits continue to exploit revocation lag rather than cryptography itself
Source: MakeUseOf Why Windows Secure Boot can be bypassed so easily (and what Microsoft isn't telling you)
Last edited: