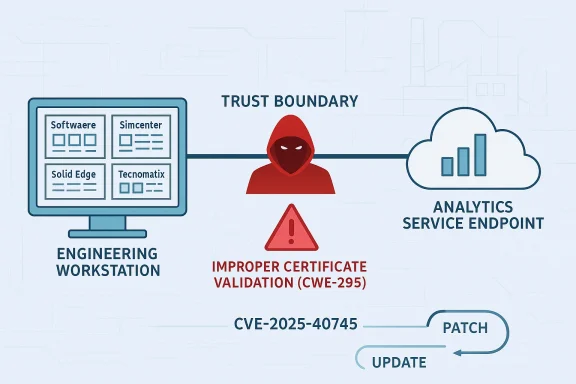
Multiple Siemens engineering and manufacturing applications are now exposed to a certificate-validation flaw in Siemens Analytics Toolkit, and the practical risk is more serious than the modest CVSS 3.7 score might suggest. Siemens says an unauthenticated remote attacker could use the weakness to perform man-in-the-middle attacks, which means the issue can undermine trust in software update and analytics connections rather than merely causing a nuisance crash. The advisory covers a wide spread of products, from Siemens Software Center to Simcenter, Solid Edge, and Tecnomatix Plant Simulation, underscoring how a shared component can create a broad but uneven attack surface. s.com](SSA-981622))
Certificate validation failures remain a classic example of a bug that looks narrow on paper but can have outsized security consequences in the field. When software accepts the wrong certificate, or fails to validate a client certificate correctly, it can create a false sense of trust between systems that are supposed to be verifying one another. In industrial and engineering environments, that trust is often the backbone of update distribution, telemetry, licensing, and connected services.
Siemens’ advisory shows that this is not a theoretical concern. The company states that affected applications “do not properly validate client certificates to connect to Analytics Service endpoint,” which opens the door to man-in-the-middle interception by a remote attacker without authentication. That wording matters because it frames the weakness as a control-plane issue, not just a data-plane nuisance.
The affected-product list also reveals the real-world shape of Siemens software. Siemens Software Center, Simcenter 3D, Simcenter Femap, Simcenter STAR-CCM+, Solid Edge SE2025, Solid Edge SE2026, and Tecnomatix Plant Simulation are all named as impacted products. These are not consumer utilities in the ordinary sense; they are tools that participate in engineering workflows, software distribution, simulation, and manufacturing planning.
That breadth gives the issue a supply-chain flavor. A common toolkit used across multiple applications means one validation bug can ripple through many product lines, which is exactly why industrial advisories often matter even when the direct CVSS score is low. The danger is not just that an attacker can intercept traffic; it is that the attacker may be able to do so inside workflows that organizations implicitly treat as trusted.
Siemens also pairs the advisory with a familiar industrial-security message: protect network access, segment critical systems, and follow operational guidance. In other words, the company is signaling that patching is the primary fix, but that network hardening remains an important second layer. That combination is typical of industrial advisories, where software remediation and environmental controls have to work together.
What stands out is the difference between the older CVSS 3.1 score and the newer CVSS v4.0 score. Siemens lists 3.7 under CVSS v3.1, but 6.3 under CVSS v4.0. That gap is a reminder that scoring systems evolve, and newer models may better reflect operational concern even when the fundamental bug class is well understood. A low-to-moderate score does not automatically mean low real-world urgency.
The advisory also identifies the reporter: Konrad Porzezynski is credited in the acknowledgments. That matters less for the technical fix than for the disclosure path, but it reinforces that this is a discovered and reported defect, not a speculative interpretation. Disclosure provenance is useful when defenders are trying to judge whether they are dealing with a vendor-confirmed issue or a secondary claim.
In this case, the advisory’s language suggests a pathway to interception rather than direct code execution. That distinction matters. Integrity and confidentiality are the main casualties here, not availability, which means defenders should think about stolen data, poisoned updates, and manipulated responses. A sophisticated attacker can do a great deal with those capabilities even without dropping malware in the classic sense.
That version mapping is important because industrial software often ships in staggered release trains. Administrators cannot assume a single patch level covers all branches, especially when products are maintained across annualized or update-based versioning schemes. The result is a patching environment where the same vulnerability may need different remediation instructions for different installed products.
There is also a broader lesson here about shared component exposure. When Siemens says “multiple Siemens applications are affected,” it is not merely restating a product list. It is revealing that one underlying toolkit flaw can affect a portfolio of products that otherwise appear unrelated to end users. That is a textbook example of why component inventory matters as much as application inventory.
The score may also understate the value of the target. Engineering applications are often connected to licensing, update, analytics, or cloud-assisted services that are not directly visible in a standard asset inventory. If an attacker can sit between the client and the service, the attacker may be able to downgrade trust, observe traffic patterns, or insert malicious responses. That is not just a privacy problem; it can become an operational integrity problem.
In industrial settings, a man-in-the-middle attack can be a stepping stone rather than the final act. Intercepted analytics traffic might reveal architecture details, license behavior, or update flows that help an attacker plan a second-stage move. Even when no direct exploit chain is documented, the ability to impersonate a trusted endpoint is itself a valuable primitive. That is the part defenders should not minimize.
For consumers or individual engineers, the risk is narrower but still real. The most likely harm is a compromised session, a manipulated response, or a trust failure during software communication. In day-to-day terms, that could mean bad updates, misleading status, or data leakage from tools that are expected to be secure by design. The problem is not loud failure; it is quiet deception.
Siemens’ own guidance reinforces that point. The advisory tells customers to protect network access with appropriate mechanisms and to configure systems according to the company’s industrial-security operational guidelines. That is not boilerplate for its own sake. It reflects the reality that industrial software can be sensitive not only to software bugs but to where and how it is deployed.
The broader market implication is that industrial software vendors are being judged not just on features, but on trust architecture. Customers increasingly expect certificate pinning, proper validation chains, secure update behavior, and well-documented patching guidance. A flaw like CVE-2025-40745 chips away at confidence in the surrounding ecosystem, even if the specific remediation is straightforward.
It also means that the visible product list may not tell the whole story. Some applications may expose the Analytics Toolkit more obviously, while others may use it in background service paths that defenders do not routinely test. This is the kind of vulnerability where dependency awareness is more important than brand awareness.
That does not mean the newer score is “more true” in some absolute sense, but it does suggest that the newer model better captures the operational relevance of the attack path. The issue is not that an attacker can necessarily crash systems or execute code; it is that a network attacker can get in the middle of a trust-sensitive conversation. Modern security teams should read that as a signal to prioritize the issue by exposure, not by the headline number alone.
There is a useful lesson here for patch triage. If a vulnerability weakens authentication or trust establishment, then the apparent severity can lag behind the business significance. Trust-control failures are notoriously underweighted by people who think in terms of RCE and ransomware first. Yet in enterprise environments, silent interception can be the precursor to much larger trouble.
The safest interpretation is simple: if you run one of the affected builds, treat it as a priority update. The attack may be subtle, but subtle attacks are often the ones that succeed longest because they do not announce themselves with obvious outages. That is precisely why they deserve prompt attention.
The advisory also includes a familiar industrial-security reminder to limit network exposure and to place control-system networks behind firewalls and segmentation boundaries. Even though this issue concerns analytics and software tooling rather than a PLC or controller, the same architectural logic applies. The more tightly you bound trust paths, the harder it is for a network attacker to exploit a validation failure.
That said, patching alone may not be enough in real environments. Engineering organizations often have change-control constraints, validation cycles, and compatibility concerns that slow rollout. When that happens, compensating controls like segmentation, restricted routing, and tighter service access become more important, not less. In other words, remediation is both a software task and an environment task.
Organizations should also verify whether the products are used in offline environments, managed update paths, or production engineering stations. Those use cases are not equally risky. A workstation that never touches untrusted networks is a different problem from a shared service brokered across a corporate WAN.
For rivals, the immediate opportunity is not to advertise perfection, which no one can credibly do, but to emphasize secure-by-design practices more aggressively. That means stronger certificate handling, clearer update integrity checks, and more transparent release notes about fixed dependency lines. In a market where customers increasingly audit software supply chains, security engineering becomes part of product differentiation.
For Siemens, the upside is that the remediation path is relatively clean. The company has specific fixed versions and a straightforward update recommendation. That matters because fast, unambiguous guidance tends to preserve more trust than vague language ever could. Still, the longer-term reputational question will hinge on whether customers see this as an isolated validation bug or as another sign that shared tooling needs deeper hardening.
What customers may remember less favorably is the idea that a validation mistake in one toolkit can cross product lines so broadly. That is the kind of lesson that nudges buyers toward more careful dependency reviews, especially in mixed engineering estates.
It will also be worth watching whether Siemens expands its guidance or whether downstream customers identify additional products that rely on the same toolkit behavior. Shared-component advisories often begin with a finite list and then broaden as asset owners map their own estates more carefully. That is one reason these disclosures deserve more attention than their scores imply.
What defenders should watch next:
Source: CISA Siemens Analytics Toolkit | CISA
 Background
Background
Certificate validation failures remain a classic example of a bug that looks narrow on paper but can have outsized security consequences in the field. When software accepts the wrong certificate, or fails to validate a client certificate correctly, it can create a false sense of trust between systems that are supposed to be verifying one another. In industrial and engineering environments, that trust is often the backbone of update distribution, telemetry, licensing, and connected services.Siemens’ advisory shows that this is not a theoretical concern. The company states that affected applications “do not properly validate client certificates to connect to Analytics Service endpoint,” which opens the door to man-in-the-middle interception by a remote attacker without authentication. That wording matters because it frames the weakness as a control-plane issue, not just a data-plane nuisance.
The affected-product list also reveals the real-world shape of Siemens software. Siemens Software Center, Simcenter 3D, Simcenter Femap, Simcenter STAR-CCM+, Solid Edge SE2025, Solid Edge SE2026, and Tecnomatix Plant Simulation are all named as impacted products. These are not consumer utilities in the ordinary sense; they are tools that participate in engineering workflows, software distribution, simulation, and manufacturing planning.
That breadth gives the issue a supply-chain flavor. A common toolkit used across multiple applications means one validation bug can ripple through many product lines, which is exactly why industrial advisories often matter even when the direct CVSS score is low. The danger is not just that an attacker can intercept traffic; it is that the attacker may be able to do so inside workflows that organizations implicitly treat as trusted.
Siemens also pairs the advisory with a familiar industrial-security message: protect network access, segment critical systems, and follow operational guidance. In other words, the company is signaling that patching is the primary fix, but that network hardening remains an important second layer. That combination is typical of industrial advisories, where software remediation and environmental controls have to work together.
What Siemens Actually Disclosed
The core disclosure is concise: multiple Siemens applications are affected by improper certificate validation in Siemens Analytics Toolkit. Siemens says the flaw could permit a remote, unauthenticated attacker to conduct man-in-the-middle attacks against the Analytics Service endpoint. The vulnerability is tracked as CVE-2025-40745 and mapped to CWE-295: Improper Certificate Validation.What stands out is the difference between the older CVSS 3.1 score and the newer CVSS v4.0 score. Siemens lists 3.7 under CVSS v3.1, but 6.3 under CVSS v4.0. That gap is a reminder that scoring systems evolve, and newer models may better reflect operational concern even when the fundamental bug class is well understood. A low-to-moderate score does not automatically mean low real-world urgency.
The advisory also identifies the reporter: Konrad Porzezynski is credited in the acknowledgments. That matters less for the technical fix than for the disclosure path, but it reinforces that this is a discovered and reported defect, not a speculative interpretation. Disclosure provenance is useful when defenders are trying to judge whether they are dealing with a vendor-confirmed issue or a secondary claim.
Why certificate validation bugs are dangerous
Certificate validation problems often seem abstract until they are mapped onto an actual deployment. If a client accepts a spoofed or improperly validated certificate, it may connect to a malicious endpoint while believing it is talking to the legitimate service. That can expose credentials, configuration data, software packages, and session traffic, depending on how the application uses the TLS channel.In this case, the advisory’s language suggests a pathway to interception rather than direct code execution. That distinction matters. Integrity and confidentiality are the main casualties here, not availability, which means defenders should think about stolen data, poisoned updates, and manipulated responses. A sophisticated attacker can do a great deal with those capabilities even without dropping malware in the classic sense.
- The flaw is remote and unauthenticated.
- The likely abuse case is interception and impersonation.
- The issue centers on an Analytics Service endpoint.
- The vulnerable behavior affects multiple Siemens applications.
- The weakness is categorized as CWE-295.
Affected Products and Patch Targets
Siemens has been unusually specific about the affected builds, and that specificity is one of the advisory’s biggest strengths. Siemens Software Center is affected up to versions below V3.5.8.2, Simcenter 3D up to below V2506.6000, Simcenter Femap up to below V2506.0002, Simcenter STAR-CCM+ up to below V2602, Solid Edge SE2025 up to below V225.0 Update 13, Solid Edge SE2026 up to below V226.0 Update 04, and Tecnomatix Plant Simulation up to below V2504.0008.That version mapping is important because industrial software often ships in staggered release trains. Administrators cannot assume a single patch level covers all branches, especially when products are maintained across annualized or update-based versioning schemes. The result is a patching environment where the same vulnerability may need different remediation instructions for different installed products.
There is also a broader lesson here about shared component exposure. When Siemens says “multiple Siemens applications are affected,” it is not merely restating a product list. It is revealing that one underlying toolkit flaw can affect a portfolio of products that otherwise appear unrelated to end users. That is a textbook example of why component inventory matters as much as application inventory.
Patch versions at a glance
The advisory’s remediation table is the operational payload most readers will want to see. For defenders, the message is straightforward: update to the first fixed release or later.- Siemens Software Center — update to V3.5.8.2 or later.
- Simcenter 3D — update to V2506.6000 or later.
- Simcenter Femap — update to V2506.0002 or later.
- Simcenter STAR-CCM+ — update to V2602 or later.
- Solid Edge SE2025 — update to V225.0 Update 13 or later.
- Solid Edge SE2026 — update to V226.0 Update 04 or later.
- Tecnomatix Plant Simulation — update to V2504.0008 or later.
Why the Risk Is Bigger Than the Score
A 3.7 CVSS v3.1 score looks modest, but this is one of those cases where severity and operational impact can drift apart. The flaw does not need privileges, user interaction, or an existing foothold. It is exposed over the network, and Siemens explicitly says the attacker can be unauthenticated. That combination can still matter a great deal in environments where trust is assumed rather than continuously verified.The score may also understate the value of the target. Engineering applications are often connected to licensing, update, analytics, or cloud-assisted services that are not directly visible in a standard asset inventory. If an attacker can sit between the client and the service, the attacker may be able to downgrade trust, observe traffic patterns, or insert malicious responses. That is not just a privacy problem; it can become an operational integrity problem.
In industrial settings, a man-in-the-middle attack can be a stepping stone rather than the final act. Intercepted analytics traffic might reveal architecture details, license behavior, or update flows that help an attacker plan a second-stage move. Even when no direct exploit chain is documented, the ability to impersonate a trusted endpoint is itself a valuable primitive. That is the part defenders should not minimize.
Enterprise impact vs. consumer impact
For enterprises, the issue is most serious where Siemens software is tied to managed deployments, shared services, or centralized engineering workflows. An attacker who can impersonate a service endpoint may be able to interfere with software delivery, harvest data, or manipulate application behavior across many users. That can create broad exposure even if the initial vulnerability is “just” certificate validation.For consumers or individual engineers, the risk is narrower but still real. The most likely harm is a compromised session, a manipulated response, or a trust failure during software communication. In day-to-day terms, that could mean bad updates, misleading status, or data leakage from tools that are expected to be secure by design. The problem is not loud failure; it is quiet deception.
- Enterprise environments face shared-service blast radius.
- Individual users face session integrity and confidentiality risks.
- The attack does not require prior authentication.
- The bug can enable endpoint impersonation.
- Security teams should treat the issue as a trust boundary failure.
The Industrial Software Angle
This advisory is especially notable because it lands in the industrial and manufacturing software ecosystem, where security failures often carry outsize consequences. Siemens markets many of these products as engineering, simulation, or lifecycle tools, but those tools increasingly sit near the operational edge of industrial IT. That makes their trust relationships more important than they might appear from a desktop icon alone.Siemens’ own guidance reinforces that point. The advisory tells customers to protect network access with appropriate mechanisms and to configure systems according to the company’s industrial-security operational guidelines. That is not boilerplate for its own sake. It reflects the reality that industrial software can be sensitive not only to software bugs but to where and how it is deployed.
The broader market implication is that industrial software vendors are being judged not just on features, but on trust architecture. Customers increasingly expect certificate pinning, proper validation chains, secure update behavior, and well-documented patching guidance. A flaw like CVE-2025-40745 chips away at confidence in the surrounding ecosystem, even if the specific remediation is straightforward.
Shared toolkits, shared exposure
A shared toolkit can be a force multiplier for product design, but it also creates a synchronized risk profile. Once a validation defect exists in a common component, every product that inherits it becomes part of the same incident class. That means patch management teams need to think horizontally across the portfolio, not vertically by product silo.It also means that the visible product list may not tell the whole story. Some applications may expose the Analytics Toolkit more obviously, while others may use it in background service paths that defenders do not routinely test. This is the kind of vulnerability where dependency awareness is more important than brand awareness.
- Shared components can create portfolio-wide exposure.
- Trust failures may hide in background service paths.
- The same toolkit bug can affect very different products.
- Product teams and platform teams need shared remediation tracking.
- SBOM-style visibility would help reduce blind spots.
What the CVSS Scores Really Say
The advisory’s dual scoring is worth a closer look. Under CVSS v3.1, Siemens lists AV:N/AC:H/PR:N/UI:N/S:U/C:L/I:N/A:N, which captures a network-reachable flaw with low confidentiality impact and no direct integrity or availability impact. Under CVSS v4.0, however, the score rises to 6.3, with the vector reflecting network attack conditions and a clearer recognition of the exploitation pathway.That does not mean the newer score is “more true” in some absolute sense, but it does suggest that the newer model better captures the operational relevance of the attack path. The issue is not that an attacker can necessarily crash systems or execute code; it is that a network attacker can get in the middle of a trust-sensitive conversation. Modern security teams should read that as a signal to prioritize the issue by exposure, not by the headline number alone.
There is a useful lesson here for patch triage. If a vulnerability weakens authentication or trust establishment, then the apparent severity can lag behind the business significance. Trust-control failures are notoriously underweighted by people who think in terms of RCE and ransomware first. Yet in enterprise environments, silent interception can be the precursor to much larger trouble.
Why this matters for defenders
Security teams should not rely on the CVSS score alone when evaluating this advisory. They should ask whether any affected Siemens products are used to reach external services, whether they operate across untrusted networks, and whether their certificate chain validation is part of an update or analytics workflow. That contextual check is what turns a generic advisory into a real risk decision.The safest interpretation is simple: if you run one of the affected builds, treat it as a priority update. The attack may be subtle, but subtle attacks are often the ones that succeed longest because they do not announce themselves with obvious outages. That is precisely why they deserve prompt attention.
- Do not let a low CVSS v3 score lull you into inaction.
- Prioritize systems with network exposure.
- Review whether the component touches update or analytics flows.
- Validate that fixed versions are actually deployed.
- Assume trust-boundary bugs can precede bigger compromises.
Siemens’ Remediation and Guidance
The vendor response is clear: update to the latest fixed versions. Siemens says it has released new versions for the affected products and recommends updating accordingly. In security terms, that is the strongest and most direct mitigation available, and it is the one defenders should prefer whenever possible.The advisory also includes a familiar industrial-security reminder to limit network exposure and to place control-system networks behind firewalls and segmentation boundaries. Even though this issue concerns analytics and software tooling rather than a PLC or controller, the same architectural logic applies. The more tightly you bound trust paths, the harder it is for a network attacker to exploit a validation failure.
That said, patching alone may not be enough in real environments. Engineering organizations often have change-control constraints, validation cycles, and compatibility concerns that slow rollout. When that happens, compensating controls like segmentation, restricted routing, and tighter service access become more important, not less. In other words, remediation is both a software task and an environment task.
What a practical response plan looks like
A sensible defensive sequence would start with inventory, then move to exposure, then to patching. First identify which Siemens applications are installed. Then confirm whether they fall below the fixed versions listed in the advisory. Finally, prioritize internet-exposed or cross-trust deployments before rolling out broader updates. That order reduces the chance of wasting time on low-value targets while vulnerable systems remain open.Organizations should also verify whether the products are used in offline environments, managed update paths, or production engineering stations. Those use cases are not equally risky. A workstation that never touches untrusted networks is a different problem from a shared service brokered across a corporate WAN.
- Build an inventory of Siemens applications.
- Check exact version numbers against the fixed builds.
- Prioritize systems with network exposure.
- Apply network segmentation and access controls.
- Validate that the patch does not disrupt engineering workflows.
Competitive and Ecosystem Implications
This advisory also matters because Siemens competes in software ecosystems where trust is a selling point. Engineering and manufacturing customers do not buy simulation and lifecycle tools purely on features; they also buy them on confidence that they can be deployed safely in complex environments. A trust flaw therefore affects not just the vulnerable builds, but the perceived maturity of the surrounding platform.For rivals, the immediate opportunity is not to advertise perfection, which no one can credibly do, but to emphasize secure-by-design practices more aggressively. That means stronger certificate handling, clearer update integrity checks, and more transparent release notes about fixed dependency lines. In a market where customers increasingly audit software supply chains, security engineering becomes part of product differentiation.
For Siemens, the upside is that the remediation path is relatively clean. The company has specific fixed versions and a straightforward update recommendation. That matters because fast, unambiguous guidance tends to preserve more trust than vague language ever could. Still, the longer-term reputational question will hinge on whether customers see this as an isolated validation bug or as another sign that shared tooling needs deeper hardening.
What customers will remember
Customers tend to remember three things in advisories like this. They remember whether the vendor named the affected products clearly, whether remediation was actionable, and whether the security message was practical rather than evasive. Siemens does reasonably well on all three counts here. The advisory is specific, the update paths are spelled out, and the general guidance aligns with industrial-security best practice.What customers may remember less favorably is the idea that a validation mistake in one toolkit can cross product lines so broadly. That is the kind of lesson that nudges buyers toward more careful dependency reviews, especially in mixed engineering estates.
- Security clarity can become a competitive feature.
- Clear fixed-version guidance reduces customer friction.
- Shared toolkit flaws invite portfolio scrutiny.
- Vendors with stronger certificate handling can differentiate.
- Buyers may ask for more supply-chain transparency going forward.
Strengths and Opportunities
The positive side of this advisory is that Siemens has done many of the right things quickly and clearly. The company identified the issue, named the affected products, published specific fixed versions, and tied the bug to a familiar CWE category. That makes life easier for security teams that need to move from uncertainty to action. The guidance is also consistent with broader industrial-security best practices, which gives defenders a coherent remediation story rather than a guess.- Clear affected-product mapping.
- Specific fixed versions for each product line.
- A direct statement of the attack path.
- A vendor-confirmed remediation plan.
- Alignment with industrial-security guidance.
- Acknowledgment of the reporter.
- A relatively limited exploit primitive compared with many industrial CVEs.
Risks and Concerns
The main concern is that the weakness affects trust, and trust failures are often harder to detect than crashes. A man-in-the-middle attack can be silent, intermittent, and difficult to prove after the fact, which makes incident response harder than with a more obvious exploit. There is also the practical problem of mixed-version estates, where one product is patched and another is still exposed. That sort of partial remediation can leave organizations with a false sense of security.- Silent interception can evade detection.
- Mixed-version deployments may remain partially exposed.
- Older CVSS scores may understate business impact.
- Patch timing can vary across engineering teams.
- Background service paths may be overlooked.
- Segmentation gaps can widen exposure.
- A shared toolkit flaw can affect more products than the first list suggests.
Looking Ahead
The next thing to watch is remediation uptake across Siemens customers. If organizations move quickly to the fixed versions, the practical exposure window should shrink fast. If patching is delayed by validation cycles or compatibility concerns, the issue could linger much longer in engineering environments that are slow to change by design.It will also be worth watching whether Siemens expands its guidance or whether downstream customers identify additional products that rely on the same toolkit behavior. Shared-component advisories often begin with a finite list and then broaden as asset owners map their own estates more carefully. That is one reason these disclosures deserve more attention than their scores imply.
What defenders should watch next:
- Confirmation that all affected products reach the fixed builds.
- Any follow-on Siemens guidance for hardening service access.
- Evidence of certificate-validation issues in adjacent product lines.
- Reports from engineering teams about rollout friction or compatibility issues.
- Signs that third-party integrators are bundling the vulnerable versions into larger solutions.
Source: CISA Siemens Analytics Toolkit | CISA