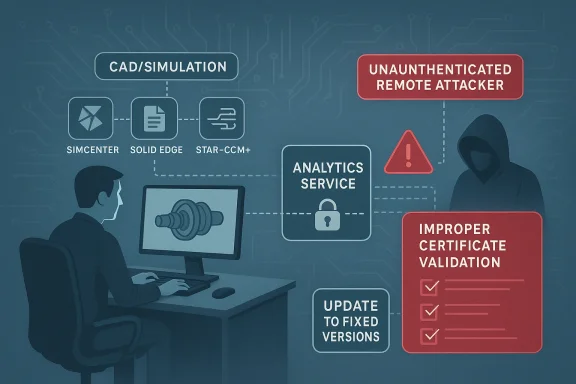
Multiple Siemens engineering and manufacturing applications are affected by an improper certificate validation flaw in Siemens Analytics Toolkit, and the result is more serious than the CVSS number alone might suggest. According to Siemens ProductCERT, the issue can let an unauthenticated remote attacker stage man-in-the-middle attacks against the Analytics Service endpoint, which is why Siemens has issued fixed versions and is urging customers to update immediately. The advisory ties the weakness to CVE-2025-40745 and lists a broad set of affected products across the Siemens software stack, including Siemens Software Center, Simcenter 3D, Simcenter Femap, Simcenter STAR-CCM+, Solid Edge, and Tecnomatix Plant Simulation.
This is a classic example of a vulnerability that looks narrow on paper but can become strategically important in practice. Improper certificate validation is not the kind of flaw that usually produces immediate code execution or a flashy exploit chain, but it undermines trust at the transport layer, and trust is exactly what engineering software depends on when it exchanges data, updates, and service calls. When a product suite is used by design teams, simulation teams, and manufacturing planners, a compromise of the connection path can ripple through configuration data, project integrity, and update confidence.
Siemens’ own wording matters here. The company says affected applications do not properly validate client certificates to connect to the Analytics Service endpoint. That means the vulnerable software may accept a malicious or forged certificate in a context where it should have rejected it, opening the door to interception or impersonation. In a remote attack scenario, that can allow the attacker to sit in the middle of what should be a trusted session and observe, tamper with, or redirect traffic.
The advisory also reflects a broader pattern in industrial and engineering security: the most important problems are often not dramatic memory corruption bugs, but trust failures in components that sit quietly inside large ecosystems. Siemens tools are widely used in environments where design data, simulation workflows, and production planning are tightly linked. If an attacker can tamper with the path between a client and an internal service, the impact can extend beyond confidentiality and into operational reliability, especially when teams rely on signed updates, secure endpoints, and consistent configuration data.
This disclosure also arrives in a market where Siemens products routinely span both enterprise IT and industrial OT-adjacent workflows. That overlap makes patching more complicated than it would be for a consumer app. Teams need to coordinate with engineering users, validation groups, and sometimes production stakeholders before they roll out updates, which is exactly why vendor fixes and clear remediation guidance are so important. Siemens has already published new versions and is directing customers to the latest builds for every affected product family.
The affected product list is broad. Siemens says the issue applies to Siemens Software Center versions below V3.5.8.2, Simcenter 3D below V2506.6000, Simcenter Femap below V2506.0002, Simcenter STAR-CCM+ below V2602, Solid Edge SE2025, Solid Edge SE2026, and Tecnomatix Plant Simulation below V2504.0008. Those fixed versions matter because this is not a single isolated app defect; it is a platform-level trust problem with reach across several product lines.
The advisory’s remediation guidance is equally straightforward: update to the latest version available for each product line. Siemens points customers to product-specific fixed releases rather than offering a universal workaround, which is often a sign that the vulnerable component is integrated deeply enough that version-specific servicing is the cleanest path forward. For defenders, that means inventory accuracy matters just as much as patch availability.
That matters a great deal in industrial software ecosystems, where trust relationships are foundational. Engineering tools often talk to update services, analytics endpoints, and backend systems that feed workflows, synchronization, or telemetry. If the software cannot reliably verify the peer certificate, secure communication becomes conditional rather than guaranteed, and conditional trust is exactly what adversaries try to exploit.
The advisory’s CVSS v3.1 vector also helps explain the risk profile: AV:N/AC:H/PR:N/UI:N/S:U/C:L/I:N/A:N. That indicates a network-reachable issue with low confidentiality impact and no integrity or availability impact scored in the base vector, but the attack complexity is high. Even so, the presence of a network vector and no privilege requirement means the bug is reachable in the broad sense, which is enough to justify attention in exposed or poorly segmented environments.
A second reason this class of flaw deserves attention is that it often sits beneath other defensive assumptions. Organizations may believe they have protected an analytics or update channel with TLS, VPNs, or internal network segmentation. But if the client-side validation is weak, the attacker does not need to defeat the network perimeter; they only need to exploit the trust decision inside the software. That is a much smaller hill to climb.
For enterprise IT, the biggest risk is not just whether a workstation is vulnerable, but whether the vulnerable endpoint sits on a network path that attackers can realistically influence. For engineering teams, the concern is whether simulation and design data can be trusted if update or service traffic is intercepted. For manufacturers, the stakes can rise further if compromised trust in a toolchain delays approvals, corrupts project state, or undermines the chain of custody on design artifacts.
That distinction matters because some organizations still treat engineering software as if it were insulated from standard vulnerability management. It is not. The tools in this advisory are deeply embedded in modern product development, and attackers love software that sits near valuable intellectual property or high-trust update channels. A low-score bug in the wrong place can still be the front door to a much more serious incident.
What makes the issue noteworthy is that it does not require authentication. Siemens explicitly says an unauthenticated remote attacker could abuse the weakness. That combination is always worth attention, particularly when the vulnerable component is part of a service endpoint that may already be assumed to be trustworthy by internal systems.
This is also why the attack complexity is important. High complexity usually reduces the chance of mass exploitation, but it does not erase exposure. It often means defenders have a somewhat longer window to patch, yet that window should not become a reason to delay. High-complexity remote bugs in widely deployed software still get abused when the target set is valuable enough. Industrial and engineering software often is.
A nuanced reading of the advisory suggests the main immediate risk is not broad worm-like propagation but targeted abuse against organizations that expose or bridge analytics services across trust zones. That makes the issue particularly relevant for larger engineering enterprises, system integrators, and manufacturers with distributed environments. The more places the toolkit is reachable from, the more interesting it becomes to an attacker.
But the operational reality is more complicated. Many Siemens customers operate long-lived engineering environments where version changes require compatibility testing, document validation, and sometimes coordination with outside contractors. That means patch timing may lag even when the security guidance is clear. The challenge for defenders is to balance speed with the need to preserve engineering continuity.
A sensible response sequence looks like this:
Organizations should also remember that patching is not only about installation. It is about verifying that the old version is actually gone, that the new version is active, and that any bundled or embedded copy of the affected toolkit has been replaced. In complex engineering environments, version drift is a common source of false confidence. Visible compliance is not the same as actual remediation.
It also highlights the growing importance of shared component governance. A weakness in a toolkit can affect multiple products at once, which is efficient from a development perspective but dangerous from a security perspective. Vendors gain consistency by reusing components; defenders inherit a larger blast radius when that component has a flaw. That tradeoff is central to modern software risk.
For competitors, incidents like this are both a warning and an opportunity. They are a warning because customers increasingly expect secure-by-default trust handling, transparent advisory language, and predictable patch paths. They are an opportunity because vendors that can prove stronger isolation, clearer component inventories, or better update orchestration may use that posture as a differentiator. In the industrial software market, security maturity is product strategy.
There is also a supply-chain lesson here. Once software portfolios become interdependent enough, a flaw in one shared library or toolkit can resonate across design, simulation, and planning products. That pushes buyers toward better software bills of materials, stronger change management, and clearer vendor accountability. The market is steadily rewarding vendors that can show not only what they ship, but what they embed.
The most important practical step is exposure reduction. If a vulnerable system does not need broad network access, it should not have it. If a system can be segmented away from untrusted networks or managed through tighter trust boundaries, that reduces the usefulness of the flaw even before the patch lands. As always in industrial and engineering environments, defense in depth buys time.
It will also be worth watching whether security teams use this advisory as a catalyst to review certificate handling across their broader Siemens estate. Many organizations assume TLS is “solved” once a connection is encrypted, but this bug is a reminder that validation logic is the real gatekeeper. A secure channel is only secure if both ends actually check what they are talking to.
Source: CISA Siemens Analytics Toolkit | CISA
 Overview
Overview
This is a classic example of a vulnerability that looks narrow on paper but can become strategically important in practice. Improper certificate validation is not the kind of flaw that usually produces immediate code execution or a flashy exploit chain, but it undermines trust at the transport layer, and trust is exactly what engineering software depends on when it exchanges data, updates, and service calls. When a product suite is used by design teams, simulation teams, and manufacturing planners, a compromise of the connection path can ripple through configuration data, project integrity, and update confidence.Siemens’ own wording matters here. The company says affected applications do not properly validate client certificates to connect to the Analytics Service endpoint. That means the vulnerable software may accept a malicious or forged certificate in a context where it should have rejected it, opening the door to interception or impersonation. In a remote attack scenario, that can allow the attacker to sit in the middle of what should be a trusted session and observe, tamper with, or redirect traffic.
The advisory also reflects a broader pattern in industrial and engineering security: the most important problems are often not dramatic memory corruption bugs, but trust failures in components that sit quietly inside large ecosystems. Siemens tools are widely used in environments where design data, simulation workflows, and production planning are tightly linked. If an attacker can tamper with the path between a client and an internal service, the impact can extend beyond confidentiality and into operational reliability, especially when teams rely on signed updates, secure endpoints, and consistent configuration data.
This disclosure also arrives in a market where Siemens products routinely span both enterprise IT and industrial OT-adjacent workflows. That overlap makes patching more complicated than it would be for a consumer app. Teams need to coordinate with engineering users, validation groups, and sometimes production stakeholders before they roll out updates, which is exactly why vendor fixes and clear remediation guidance are so important. Siemens has already published new versions and is directing customers to the latest builds for every affected product family.
What Siemens disclosed
Siemens ProductCERT published SSA-981622 on 2026-04-14, and the advisory is direct: multiple Siemens applications are affected by CVE-2025-40745, a certificate validation issue in Siemens Analytics Toolkit. Siemens assigns a CVSS v3.1 base score of 3.7 and a CVSS v4.0 base score of 6.3, which is a reminder that the newer model can paint a more nuanced picture of practical risk even when the older score looks low.The affected product list is broad. Siemens says the issue applies to Siemens Software Center versions below V3.5.8.2, Simcenter 3D below V2506.6000, Simcenter Femap below V2506.0002, Simcenter STAR-CCM+ below V2602, Solid Edge SE2025, Solid Edge SE2026, and Tecnomatix Plant Simulation below V2504.0008. Those fixed versions matter because this is not a single isolated app defect; it is a platform-level trust problem with reach across several product lines.
Affected product families
The spread of affected products tells us a lot about the architectural role of Siemens Analytics Toolkit. This is not just a niche add-on; it is embedded in a family of software used for product lifecycle work, simulation, and software distribution. That makes the vulnerability more interesting than a simple one-off app bug, because the attack surface exists wherever the toolkit is reused.The advisory’s remediation guidance is equally straightforward: update to the latest version available for each product line. Siemens points customers to product-specific fixed releases rather than offering a universal workaround, which is often a sign that the vulnerable component is integrated deeply enough that version-specific servicing is the cleanest path forward. For defenders, that means inventory accuracy matters just as much as patch availability.
- Siemens Software Center: update to V3.5.8.2 or later
- Simcenter 3D: update to V2506.6000 or later
- Simcenter Femap: update to V2506.0002 or later
- Simcenter STAR-CCM+: update to V2602 or later
- Tecnomatix Plant Simulation: update to V2504.0008 or later
- Solid Edge SE2025 and SE2026: update to the Siemens-released fixed versions noted in the advisory
Why certificate validation bugs matter
Certificate validation flaws often get underestimated because they do not always look dangerous in the way a remote code execution bug does. But if a product accepts the wrong certificate, the attacker can impersonate a trusted service, intercept traffic, or influence the client’s view of what endpoint it is talking to. In other words, the attack is not on the application layer first; it is on the assumptions the application makes about the channel itself.That matters a great deal in industrial software ecosystems, where trust relationships are foundational. Engineering tools often talk to update services, analytics endpoints, and backend systems that feed workflows, synchronization, or telemetry. If the software cannot reliably verify the peer certificate, secure communication becomes conditional rather than guaranteed, and conditional trust is exactly what adversaries try to exploit.
Man-in-the-middle at the service layer
A man-in-the-middle attack in this context does not necessarily mean dramatic browser-style interception. It can be subtler. An attacker may be able to present themselves as a legitimate endpoint, influence data exchange, or capture sensitive operational traffic where the client assumes a trusted relationship exists. That is why certificate validation is not merely a compliance checkbox; it is one of the core controls that protects identity in transit.The advisory’s CVSS v3.1 vector also helps explain the risk profile: AV:N/AC:H/PR:N/UI:N/S:U/C:L/I:N/A:N. That indicates a network-reachable issue with low confidentiality impact and no integrity or availability impact scored in the base vector, but the attack complexity is high. Even so, the presence of a network vector and no privilege requirement means the bug is reachable in the broad sense, which is enough to justify attention in exposed or poorly segmented environments.
A second reason this class of flaw deserves attention is that it often sits beneath other defensive assumptions. Organizations may believe they have protected an analytics or update channel with TLS, VPNs, or internal network segmentation. But if the client-side validation is weak, the attacker does not need to defeat the network perimeter; they only need to exploit the trust decision inside the software. That is a much smaller hill to climb.
Product impact across the Siemens ecosystem
The breadth of affected products makes this advisory especially relevant for teams that manage engineering desktops, simulation workstations, and software distribution portals separately. Siemens Software Center is directly relevant to software acquisition and update workflows, while Simcenter and Solid Edge products are embedded in design and engineering operations. That means the vulnerable toolkit can touch both administrative and production-adjacent workflows.For enterprise IT, the biggest risk is not just whether a workstation is vulnerable, but whether the vulnerable endpoint sits on a network path that attackers can realistically influence. For engineering teams, the concern is whether simulation and design data can be trusted if update or service traffic is intercepted. For manufacturers, the stakes can rise further if compromised trust in a toolchain delays approvals, corrupts project state, or undermines the chain of custody on design artifacts.
Enterprise versus engineering-user impact
Enterprise security teams tend to think in terms of exposure, segmentation, and patch compliance. Engineering users tend to think in terms of project continuity, compatibility, and output stability. This advisory forces both groups to meet in the middle, because a security flaw in a core engineering product is not purely an IT concern and not purely an OT concern either. It is a workflow integrity issue.That distinction matters because some organizations still treat engineering software as if it were insulated from standard vulnerability management. It is not. The tools in this advisory are deeply embedded in modern product development, and attackers love software that sits near valuable intellectual property or high-trust update channels. A low-score bug in the wrong place can still be the front door to a much more serious incident.
- Software Center can affect patch and distribution confidence.
- Simcenter products can affect simulation and modeling workflows.
- Solid Edge can affect design workflows and file trust.
- Tecnomatix Plant Simulation can affect manufacturing planning and operational modeling.
- The common denominator is the Analytics Toolkit trust boundary.
How serious is CVE-2025-40745?
The headline CVSS v3.1 score of 3.7 is low, and it would be easy to stop reading there. That would be a mistake. Siemens’ own description makes clear that the flaw can enable remote man-in-the-middle attacks, and the newer CVSS v4.0 score of 6.3 suggests a more meaningful operational concern than the legacy score implies. In security, context often matters more than the headline rating.What makes the issue noteworthy is that it does not require authentication. Siemens explicitly says an unauthenticated remote attacker could abuse the weakness. That combination is always worth attention, particularly when the vulnerable component is part of a service endpoint that may already be assumed to be trustworthy by internal systems.
Why “low confidentiality impact” is not the whole story
The advisory’s confidentiality impact is scored as low, and that is fair as a strict base metric. But low impact does not mean low consequence when the flaw is in a trust mechanism. If an attacker can impersonate a legitimate endpoint, even limited information disclosure can be enough to support follow-on abuse, traffic shaping, or operational reconnaissance.This is also why the attack complexity is important. High complexity usually reduces the chance of mass exploitation, but it does not erase exposure. It often means defenders have a somewhat longer window to patch, yet that window should not become a reason to delay. High-complexity remote bugs in widely deployed software still get abused when the target set is valuable enough. Industrial and engineering software often is.
A nuanced reading of the advisory suggests the main immediate risk is not broad worm-like propagation but targeted abuse against organizations that expose or bridge analytics services across trust zones. That makes the issue particularly relevant for larger engineering enterprises, system integrators, and manufacturers with distributed environments. The more places the toolkit is reachable from, the more interesting it becomes to an attacker.
Siemens’ remediation strategy
Siemens is doing what well-run industrial software vendors should do: publish fixed builds and tell customers to move to the latest supported version. The remediation table in the advisory is clear that the issue has been addressed in current product lines, and the vendor’s recommendation is to upgrade rather than rely on a compensating control alone. That is the right default for a certificate-validation flaw.But the operational reality is more complicated. Many Siemens customers operate long-lived engineering environments where version changes require compatibility testing, document validation, and sometimes coordination with outside contractors. That means patch timing may lag even when the security guidance is clear. The challenge for defenders is to balance speed with the need to preserve engineering continuity.
What defenders should do first
The first response should be inventory, not panic. Organizations need to know which Siemens applications are deployed, which versions are installed, and whether those builds map to the affected ranges in the advisory. After that, they should prioritize systems that are internet-reachable, bridged across trust zones, or exposed in shared engineering environments.A sensible response sequence looks like this:
- Identify every installation of the affected Siemens products.
- Compare installed build numbers against Siemens’ fixed versions.
- Prioritize exposed, shared, or remotely reachable systems.
- Validate the update in a test environment if engineering workflows are sensitive.
- Roll out the fix and confirm the service endpoint behaves correctly after patching.
Organizations should also remember that patching is not only about installation. It is about verifying that the old version is actually gone, that the new version is active, and that any bundled or embedded copy of the affected toolkit has been replaced. In complex engineering environments, version drift is a common source of false confidence. Visible compliance is not the same as actual remediation.
What this says about the industrial software market
This advisory fits a broader industry trend: engineering and industrial software is becoming more interconnected, more service-oriented, and more dependent on secure backend communication. That evolution brings efficiency and cloud-like manageability, but it also enlarges the attack surface. Once a product line relies on internal endpoints and toolkit-mediated trust decisions, certificate handling becomes a business-critical security control.It also highlights the growing importance of shared component governance. A weakness in a toolkit can affect multiple products at once, which is efficient from a development perspective but dangerous from a security perspective. Vendors gain consistency by reusing components; defenders inherit a larger blast radius when that component has a flaw. That tradeoff is central to modern software risk.
Broader competitive and ecosystem implications
For Siemens, the advantage is that it can remediate centrally and communicate the fix across multiple product lines. The downside is equally obvious: if a shared toolkit has a security problem, the company’s reputation can be touched in several markets at once. Engineering software buyers pay close attention to reliability and trust, so even a relatively low-scored flaw can have outsized reputational value.For competitors, incidents like this are both a warning and an opportunity. They are a warning because customers increasingly expect secure-by-default trust handling, transparent advisory language, and predictable patch paths. They are an opportunity because vendors that can prove stronger isolation, clearer component inventories, or better update orchestration may use that posture as a differentiator. In the industrial software market, security maturity is product strategy.
There is also a supply-chain lesson here. Once software portfolios become interdependent enough, a flaw in one shared library or toolkit can resonate across design, simulation, and planning products. That pushes buyers toward better software bills of materials, stronger change management, and clearer vendor accountability. The market is steadily rewarding vendors that can show not only what they ship, but what they embed.
Operational guidance for enterprises
Enterprises should treat this as a targeted but meaningful patching event, not a routine update. Siemens has already delivered the remediation, and the job for operators is to connect the vendor’s version numbers to their own asset inventory as quickly as possible. If the affected software is installed on engineering workstations, update queues should be accelerated, particularly where the endpoint participates in shared services or update channels.The most important practical step is exposure reduction. If a vulnerable system does not need broad network access, it should not have it. If a system can be segmented away from untrusted networks or managed through tighter trust boundaries, that reduces the usefulness of the flaw even before the patch lands. As always in industrial and engineering environments, defense in depth buys time.
Recommended response priorities
- Patch externally reachable or cross-zone systems first.
- Verify whether any affected product is used for software distribution or update management.
- Check whether the Analytics Toolkit is bundled in packaged deployments.
- Review whether certificates are pinned, validated, or inherited from a shared trust store.
- Confirm that logging and monitoring can spot suspicious service-path behavior.
- Document the remediation status for each product family separately.
- Preserve a rollback plan if engineering validation uncovers compatibility issues.
Strengths and Opportunities
The best news in this advisory is that Siemens has already shipped fixes across the affected product families, which gives defenders a clear remediation target rather than a vague “wait for guidance” situation. The second positive is that the advisory is unusually specific about impacted versions, making asset matching much easier for administrators with accurate inventories. The third is that this kind of disclosure encourages better security engineering across a product family, not just in one isolated application. In the long run, that kind of transparency can improve customer trust if vendors follow through consistently.- Clear fixed versions reduce guesswork.
- Affected products are named explicitly.
- The attack path is understandable and testable.
- The issue can be mitigated through standard patch management.
- Security teams can prioritize exposed systems first.
- The advisory reinforces inventory discipline.
- Better component awareness can improve future response.
Risks and Concerns
The biggest concern is that low CVSS scores can lull organizations into delay, especially when the flaw does not sound explosive at first glance. But the advisory makes clear that unauthenticated remote attackers may exploit the weakness for man-in-the-middle attacks, and that is enough to justify serious attention. Another concern is that engineering environments often patch slowly because they fear breaking workflows. That hesitation can become a liability if the vulnerable toolkit remains reachable for too long.- Low base score may cause underreaction.
- Shared toolkit reuse broadens the blast radius.
- Engineering change control can slow remediation.
- Asset inventories may miss embedded copies.
- Certificate issues are easy to overlook during testing.
- Network segmentation may be weaker than assumed.
- Compromise of trust channels can be hard to detect.
Looking Ahead
The next thing to watch is whether Siemens publishes any follow-on guidance that clarifies deployment patterns or recommends additional hardening for customers using the Analytics Toolkit in particularly sensitive environments. Another point to watch is whether downstream vendors or integrators identify embedded copies of the affected toolkit in bundled or customized deployments, because that would widen the practical exposure beyond the named product lines. If that happens, the operational story becomes less about a single advisory and more about ecosystem-wide trust management.It will also be worth watching whether security teams use this advisory as a catalyst to review certificate handling across their broader Siemens estate. Many organizations assume TLS is “solved” once a connection is encrypted, but this bug is a reminder that validation logic is the real gatekeeper. A secure channel is only secure if both ends actually check what they are talking to.
- Confirm installed versions against Siemens’ fixed builds.
- Prioritize internet-facing and cross-zone systems.
- Validate bundled or embedded toolkit copies.
- Review logging for unusual service-path behavior.
- Tighten certificate policy where practical.
- Monitor for any Siemens follow-up hardening guidance.
Source: CISA Siemens Analytics Toolkit | CISA