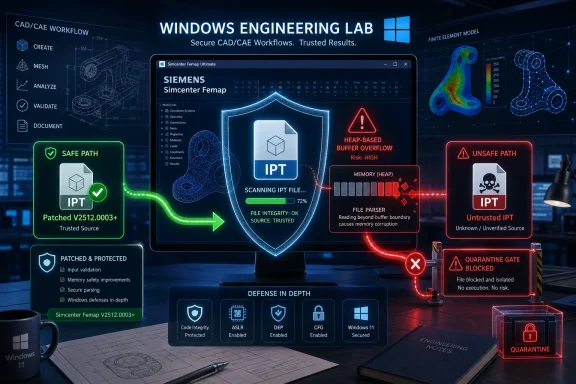
Siemens Simcenter Femap versions before V2512.0003 are affected by CVE-2025-12659, a high-severity heap-based buffer overflow in the Datakit library that can be triggered when a user opens a malicious Autodesk Inventor IPT file, according to Siemens and CISA advisories published in May 2026. The patch is not a theoretical hygiene update for some obscure backend component; it is a reminder that engineering workstations now sit squarely in the same threat model as email clients and browsers. A file parser embedded in a trusted design workflow can become the beachhead. For Windows shops running Femap, the practical answer is simple: update, restrict untrusted file handling, and stop treating CAD/CAE files as harmless business documents.
The uncomfortable part of this advisory is not the CVSS score, though 7.8 is enough to get attention. It is the path to exploitation: a user opens a file that looks like part of the day’s engineering work. No exposed service, no internet-facing appliance, no dramatic zero-click chain is required.
That is why vulnerabilities in engineering software deserve more attention than they often receive in general IT patch cycles. Simcenter Femap is not usually grouped mentally with Outlook, Teams, Chrome, or Adobe Reader, yet it processes complex, externally exchanged files in much the same high-risk pattern. The application is expected to ingest other people’s data, interpret nested structures, and transform them into something useful.
In this case, the vulnerable component is tied to the parsing of IPT files, a format associated with Autodesk Inventor parts. The bug is described as memory corruption and, more specifically, a heap-based buffer overflow. If exploitation succeeds, the attacker’s code runs in the context of the current Femap process, which means the practical damage depends heavily on the privileges and access of the engineer or analyst who opened the file.
That framing matters. This is not “remote code execution” in the magical sense where an attacker simply reaches across the internet and owns a machine. It is remote code execution in the everyday business sense: a crafted file arrives through a supplier, customer, project portal, file share, or email thread, and the user interaction completes the attack.
A parser vulnerability is attractive because it hides inside normal behavior. Opening a model, importing geometry, reviewing a supplied component, or converting project data does not feel like executing code. For an engineer under deadline pressure, the difference between a trusted and untrusted file may be little more than the name of the sender.
Femap’s role also raises the stakes. It is used for finite element modeling and analysis work, which often intersects with aerospace, automotive, energy, industrial machinery, and other critical manufacturing environments. The machines running these tools may have access to proprietary designs, simulation results, license servers, project shares, and internal collaboration systems.
That does not mean every affected workstation is sitting inside a plant control network. In many organizations, it will be a Windows workstation on a corporate engineering VLAN. But the old separation between “office IT” and “engineering operations” has weakened, and the data that moves through CAE environments is often commercially sensitive even when it is not directly safety-critical.
The “local” attack vector can be misleading for non-specialists. It does not mean the attacker needs physical access to the workstation. It means the vulnerable action occurs locally when the file is opened by the user or application. The attacker can still be remote in the ordinary sense if the file is delivered through email, a shared drive, a ticketing system, or a project exchange.
The advisory credits Trend Micro’s Zero Day Initiative, and ZDI’s own notice describes the flaw as an IPT file parsing memory corruption issue caused by insufficient validation of user-supplied data. That is the classic language of a parser that trusts something it should not trust. Once the parser walks past the safe boundary, control of memory can become control of execution.
There is a deeper lesson here for Windows administrators. Many organizations have improved macro controls, script blocking, and browser isolation, only to leave specialized document and model formats lightly governed. Attackers do not need Office macros if a more trusted engineering format gets them the same foothold.
Still, “update to the latest version” is rarely simple in engineering environments. Femap deployments may be pinned to project validation requirements, add-ins, solver compatibility, automation scripts, or licensing arrangements. A version bump that looks minor to security may look operationally risky to the simulation team.
That tension is real, but it should not become an excuse for indefinite delay. The affected versions are those before V2512.0003, and the vulnerability is tied to a common workflow: opening files. If an organization cannot patch immediately, it should compensate deliberately rather than relying on informal caution.
The minimum compensating control is to restrict the handling of untrusted IPT files until the update is in place. That means not merely telling users to “be careful,” but changing file intake patterns, scanning sources, quarantining unsolicited samples, and routing supplier-provided files through controlled review systems.
There is a tendency in vulnerability coverage to reserve urgency for PLCs, HMIs, remote access gateways, and industrial protocol stacks. Those are obviously important. But design and simulation environments are upstream of production, maintenance, and certification decisions, and they often contain information an adversary would love to steal or manipulate.
The risk model is not only ransomware, though ransomware remains an obvious concern. A compromised engineering workstation can expose design IP, customer models, analysis reports, and internal credentials. In a targeted scenario, it can also become a staging point into adjacent systems that were never meant to be internet-facing but are reachable from the engineering desktop.
CISA’s standard defensive language about minimizing network exposure, isolating control systems, using secure remote access, and performing impact analysis can feel repetitive. In this case, repetition is the point. The workstation that opens the malicious file may be the soft bridge between a supplier-facing collaboration workflow and more sensitive industrial assets.
File format interoperability is a major selling point for tools like Femap. Customers expect them to consume data from a wide variety of CAD and CAE environments. The commercial value of broad compatibility, however, comes with a security cost: every additional translator expands the parsing surface.
This is not unique to Siemens. The design and simulation software world has a long history of vulnerabilities in file importers, from mesh and model formats to neutral exchange formats and proprietary CAD containers. The engineering desktop is a museum of complex parsers, many of them built to preserve interoperability across decades of workflows.
For defenders, the library angle changes the inventory question. It is not enough to know whether “Femap is installed.” Teams need to know which versions are present, which file types are routinely opened, which projects exchange IPT files, and whether the update has actually reached the machines doing the risky work.
Engineers open files from vendors. Analysts inspect models from customers. Contractors send revised components. Internal teams exchange exported geometry and solver input files. A security model that depends on never opening untrusted files is not a model; it is a wish.
The better question is whether the organization can make dangerous interaction less likely and less damaging. Files from outside the company should pass through predictable channels, not ad hoc messages. Workstations that process high-risk files should have strong endpoint controls, least-privilege user accounts, and limited lateral movement opportunities.
Application control can help, but only if tuned for the engineering reality. Blocking unknown executables after exploitation is useful; preventing the vulnerable parser from being reached in the first place is better. The fastest near-term win is often procedural: restrict IPT handling to patched systems and require suspicious or unsolicited files to be opened only in controlled environments.
That split ownership is dangerous. The Femap administrator may track licensing and user support, while the security team tracks CVEs and endpoint exposure. If those two worlds do not meet, a high-severity parser bug can linger even after the vendor ships a fix.
Asset management is the unglamorous control that determines whether this advisory is a one-day patch task or a month-long hunt. Administrators need to know where Femap is installed, which versions are running, who uses it, and whether old project workstations or lab machines are still online. In engineering environments, “temporary” analysis machines can become permanent fixtures.
There is also a user education angle, but it should be narrow and practical. Telling users about heap corruption is useless. Telling them that IPT files from unexpected sources must not be opened on unpatched systems is actionable. Better still is removing the choice by updating the software and enforcing intake controls.
CAE software is built to understand complicated, highly structured, and often legacy-laden data. Formats may contain geometry, metadata, references, embedded objects, solver settings, meshes, and vendor-specific extensions. The more expressive the format, the harder it is to parse safely.
Attackers follow complexity. Browser engines, media codecs, PDF readers, decompression libraries, and Office document handlers have all been battlefields for the same reason. Engineering file parsers belong on that list, even if they receive less mainstream attention.
The industry has gradually improved secure development practices around mainstream consumer file types. The industrial and engineering software world is catching up, but the economics are difficult. Customers want compatibility with everything, and every compatibility feature is another place where malformed input can become executable consequence.
But respect for operational reality is not the same as accepting open-ended exposure. A mature response separates systems by urgency and risk. Workstations that routinely receive external IPT files should move first. Systems used only for internal legacy projects may have a different timeline, but they still need a documented plan.
In practice, organizations should pair patch rollout with temporary restrictions. If V2512.0003 cannot be installed immediately everywhere, then unpatched machines should not be allowed to open externally sourced IPT files. If that restriction breaks a workflow, that workflow has just identified itself as part of the risk surface.
The strongest organizations will also use this advisory to review their software intake and supplier exchange process. A secure engineering workflow should not depend on every analyst independently judging whether a file is safe. It should give them a safe default.
But the absence of known exploitation is not a reason to relax. Coordinated disclosure creates a public roadmap. Once the advisory is out, attackers know the affected product, file type, vulnerability class, and fixed version boundary. Even without a public proof of concept, that is useful information.
The exploitability gap cuts both ways. Defenders may have time to patch before commodity exploitation appears, but attackers also have time to build lures tailored to engineering workflows. A fake supplier update, revised bracket model, urgent manufacturing change, or customer-provided part file is more believable than a generic phishing attachment.
That is why file-format RCE bugs are so dangerous in professional software. The lure can be boring, specific, and operationally plausible. The more normal the file looks, the less likely the user is to hesitate.
Verification should include installed version checks and user confirmation for machines that sit outside normal management. If Femap is packaged through enterprise software deployment, the package inventory should be reconciled against endpoint telemetry. If installation is manual, the risk of drift is higher.
Security teams should also look at file associations and default handlers. If double-clicking an IPT file launches Femap on an unpatched system, that is a direct path to exploitation. Where possible, organizations should ensure that only patched systems are registered or approved for handling the affected file type.
Finally, incident response teams should be ready for the mundane indicators of a successful file exploit: suspicious child processes from Femap, unexpected network connections, credential access behavior, or abnormal file encryption and staging. A CAE application spawning shells, script interpreters, or unusual command-line tools should not be treated as normal engineering noise.
Source: CISA Siemens Simcenter Femap | CISA
 A Simulation Workstation Is Still an Attack Surface
A Simulation Workstation Is Still an Attack Surface
The uncomfortable part of this advisory is not the CVSS score, though 7.8 is enough to get attention. It is the path to exploitation: a user opens a file that looks like part of the day’s engineering work. No exposed service, no internet-facing appliance, no dramatic zero-click chain is required.That is why vulnerabilities in engineering software deserve more attention than they often receive in general IT patch cycles. Simcenter Femap is not usually grouped mentally with Outlook, Teams, Chrome, or Adobe Reader, yet it processes complex, externally exchanged files in much the same high-risk pattern. The application is expected to ingest other people’s data, interpret nested structures, and transform them into something useful.
In this case, the vulnerable component is tied to the parsing of IPT files, a format associated with Autodesk Inventor parts. The bug is described as memory corruption and, more specifically, a heap-based buffer overflow. If exploitation succeeds, the attacker’s code runs in the context of the current Femap process, which means the practical damage depends heavily on the privileges and access of the engineer or analyst who opened the file.
That framing matters. This is not “remote code execution” in the magical sense where an attacker simply reaches across the internet and owns a machine. It is remote code execution in the everyday business sense: a crafted file arrives through a supplier, customer, project portal, file share, or email thread, and the user interaction completes the attack.
The File Parser Has Become the New Perimeter
Security teams have spent years hardening network edges, identity systems, and endpoint controls, but specialized engineering software often remains outside the highest-tempo patch conversation. The workflows are messy, the software is expensive, the licensing is delicate, and the systems may be tied to long-running projects that administrators are reluctant to disturb. That is exactly why attackers like file-format bugs.A parser vulnerability is attractive because it hides inside normal behavior. Opening a model, importing geometry, reviewing a supplied component, or converting project data does not feel like executing code. For an engineer under deadline pressure, the difference between a trusted and untrusted file may be little more than the name of the sender.
Femap’s role also raises the stakes. It is used for finite element modeling and analysis work, which often intersects with aerospace, automotive, energy, industrial machinery, and other critical manufacturing environments. The machines running these tools may have access to proprietary designs, simulation results, license servers, project shares, and internal collaboration systems.
That does not mean every affected workstation is sitting inside a plant control network. In many organizations, it will be a Windows workstation on a corporate engineering VLAN. But the old separation between “office IT” and “engineering operations” has weakened, and the data that moves through CAE environments is often commercially sensitive even when it is not directly safety-critical.
A High-Severity Bug With a Very Human Trigger
CVE-2025-12659 is rated high severity under CVSS 3.1, with the familiar pattern for file-handling RCE bugs: local attack vector, low complexity, no privileges required, user interaction required, and high impact on confidentiality, integrity, and availability. In plainer English, the attacker needs the victim to open the booby-trapped file, but the exploit is not described as requiring unusual conditions once that happens.The “local” attack vector can be misleading for non-specialists. It does not mean the attacker needs physical access to the workstation. It means the vulnerable action occurs locally when the file is opened by the user or application. The attacker can still be remote in the ordinary sense if the file is delivered through email, a shared drive, a ticketing system, or a project exchange.
The advisory credits Trend Micro’s Zero Day Initiative, and ZDI’s own notice describes the flaw as an IPT file parsing memory corruption issue caused by insufficient validation of user-supplied data. That is the classic language of a parser that trusts something it should not trust. Once the parser walks past the safe boundary, control of memory can become control of execution.
There is a deeper lesson here for Windows administrators. Many organizations have improved macro controls, script blocking, and browser isolation, only to leave specialized document and model formats lightly governed. Attackers do not need Office macros if a more trusted engineering format gets them the same foothold.
Siemens’ Fix Is Narrow, but the Lesson Is Broad
Siemens’ recommendation is straightforward: update Simcenter Femap to V2512.0003 or later. That is the right center of gravity. Workarounds can reduce risk, but a parser bug in a complex desktop application ultimately needs a vendor fix.Still, “update to the latest version” is rarely simple in engineering environments. Femap deployments may be pinned to project validation requirements, add-ins, solver compatibility, automation scripts, or licensing arrangements. A version bump that looks minor to security may look operationally risky to the simulation team.
That tension is real, but it should not become an excuse for indefinite delay. The affected versions are those before V2512.0003, and the vulnerability is tied to a common workflow: opening files. If an organization cannot patch immediately, it should compensate deliberately rather than relying on informal caution.
The minimum compensating control is to restrict the handling of untrusted IPT files until the update is in place. That means not merely telling users to “be careful,” but changing file intake patterns, scanning sources, quarantining unsolicited samples, and routing supplier-provided files through controlled review systems.
CISA’s Republication Puts an Engineering Bug in the Industrial Frame
CISA’s republication of the Siemens advisory places the issue in the critical manufacturing sector, with worldwide deployment and Siemens’ headquarters in Germany. That classification can sound bureaucratic, but it is useful. It reminds readers that CAE tools are part of the industrial software estate, not just productivity software for a niche desktop audience.There is a tendency in vulnerability coverage to reserve urgency for PLCs, HMIs, remote access gateways, and industrial protocol stacks. Those are obviously important. But design and simulation environments are upstream of production, maintenance, and certification decisions, and they often contain information an adversary would love to steal or manipulate.
The risk model is not only ransomware, though ransomware remains an obvious concern. A compromised engineering workstation can expose design IP, customer models, analysis reports, and internal credentials. In a targeted scenario, it can also become a staging point into adjacent systems that were never meant to be internet-facing but are reachable from the engineering desktop.
CISA’s standard defensive language about minimizing network exposure, isolating control systems, using secure remote access, and performing impact analysis can feel repetitive. In this case, repetition is the point. The workstation that opens the malicious file may be the soft bridge between a supplier-facing collaboration workflow and more sensitive industrial assets.
The Datakit Detail Matters Because Supply Chains Are Made of Libraries
The advisory identifies the vulnerable path as involving the Datakit library. That matters because modern engineering applications are ecosystems of parsers, importers, exporters, and translation components. A product’s attack surface is not limited to code written under the brand name on the splash screen.File format interoperability is a major selling point for tools like Femap. Customers expect them to consume data from a wide variety of CAD and CAE environments. The commercial value of broad compatibility, however, comes with a security cost: every additional translator expands the parsing surface.
This is not unique to Siemens. The design and simulation software world has a long history of vulnerabilities in file importers, from mesh and model formats to neutral exchange formats and proprietary CAD containers. The engineering desktop is a museum of complex parsers, many of them built to preserve interoperability across decades of workflows.
For defenders, the library angle changes the inventory question. It is not enough to know whether “Femap is installed.” Teams need to know which versions are present, which file types are routinely opened, which projects exchange IPT files, and whether the update has actually reached the machines doing the risky work.
User Interaction Is Not a Comforting Mitigation
The phrase “user interaction required” often causes risk to be downgraded in practice. That is a mistake for this class of vulnerability. In professional file-exchange workflows, user interaction is not an obstacle; it is the business process.Engineers open files from vendors. Analysts inspect models from customers. Contractors send revised components. Internal teams exchange exported geometry and solver input files. A security model that depends on never opening untrusted files is not a model; it is a wish.
The better question is whether the organization can make dangerous interaction less likely and less damaging. Files from outside the company should pass through predictable channels, not ad hoc messages. Workstations that process high-risk files should have strong endpoint controls, least-privilege user accounts, and limited lateral movement opportunities.
Application control can help, but only if tuned for the engineering reality. Blocking unknown executables after exploitation is useful; preventing the vulnerable parser from being reached in the first place is better. The fastest near-term win is often procedural: restrict IPT handling to patched systems and require suspicious or unsolicited files to be opened only in controlled environments.
Windows Defenders Need to Watch the Boring Apps
For WindowsForum readers, the advisory lands in familiar territory: the weakest link is often the application nobody thinks about until it breaks. Security teams have mature processes for Microsoft Patch Tuesday, browsers, VPN clients, and endpoint agents. Specialized engineering applications may sit on a separate cadence, owned operationally by engineering and only partially visible to central IT.That split ownership is dangerous. The Femap administrator may track licensing and user support, while the security team tracks CVEs and endpoint exposure. If those two worlds do not meet, a high-severity parser bug can linger even after the vendor ships a fix.
Asset management is the unglamorous control that determines whether this advisory is a one-day patch task or a month-long hunt. Administrators need to know where Femap is installed, which versions are running, who uses it, and whether old project workstations or lab machines are still online. In engineering environments, “temporary” analysis machines can become permanent fixtures.
There is also a user education angle, but it should be narrow and practical. Telling users about heap corruption is useless. Telling them that IPT files from unexpected sources must not be opened on unpatched systems is actionable. Better still is removing the choice by updating the software and enforcing intake controls.
The Pattern Around Femap Is Bigger Than One CVE
This is not the first recent Siemens Simcenter Femap advisory involving file parsing and memory corruption. Previous advisories have covered other crafted file formats and similar code-execution outcomes. That pattern does not mean the product is uniquely bad; it means the product sits in a risky category.CAE software is built to understand complicated, highly structured, and often legacy-laden data. Formats may contain geometry, metadata, references, embedded objects, solver settings, meshes, and vendor-specific extensions. The more expressive the format, the harder it is to parse safely.
Attackers follow complexity. Browser engines, media codecs, PDF readers, decompression libraries, and Office document handlers have all been battlefields for the same reason. Engineering file parsers belong on that list, even if they receive less mainstream attention.
The industry has gradually improved secure development practices around mainstream consumer file types. The industrial and engineering software world is catching up, but the economics are difficult. Customers want compatibility with everything, and every compatibility feature is another place where malformed input can become executable consequence.
Patch Management Has to Respect Engineering Reality Without Surrendering to It
Security teams should avoid treating this as a simple failure if an engineering group cannot patch on day one. Simulation software often supports regulated or contractually constrained workflows. A patch may need validation against project templates, solver integrations, and automation macros before it can be rolled out broadly.But respect for operational reality is not the same as accepting open-ended exposure. A mature response separates systems by urgency and risk. Workstations that routinely receive external IPT files should move first. Systems used only for internal legacy projects may have a different timeline, but they still need a documented plan.
In practice, organizations should pair patch rollout with temporary restrictions. If V2512.0003 cannot be installed immediately everywhere, then unpatched machines should not be allowed to open externally sourced IPT files. If that restriction breaks a workflow, that workflow has just identified itself as part of the risk surface.
The strongest organizations will also use this advisory to review their software intake and supplier exchange process. A secure engineering workflow should not depend on every analyst independently judging whether a file is safe. It should give them a safe default.
The Exploitability Gap Cuts Both Ways
There is no need to exaggerate what is known. The public advisory does not establish that attackers are actively exploiting CVE-2025-12659 in the wild. The requirement for a malicious file and user interaction makes mass exploitation less straightforward than scanning for exposed services.But the absence of known exploitation is not a reason to relax. Coordinated disclosure creates a public roadmap. Once the advisory is out, attackers know the affected product, file type, vulnerability class, and fixed version boundary. Even without a public proof of concept, that is useful information.
The exploitability gap cuts both ways. Defenders may have time to patch before commodity exploitation appears, but attackers also have time to build lures tailored to engineering workflows. A fake supplier update, revised bracket model, urgent manufacturing change, or customer-provided part file is more believable than a generic phishing attachment.
That is why file-format RCE bugs are so dangerous in professional software. The lure can be boring, specific, and operationally plausible. The more normal the file looks, the less likely the user is to hesitate.
The Vendor Patch Is the Start, Not the Finish
Updating to V2512.0003 or later should be the headline action, but it should not be the only one. After patching, administrators should verify deployment, not merely push an installer and assume completion. Engineering machines are often offline, traveling, license-constrained, or excluded from standard endpoint management rings.Verification should include installed version checks and user confirmation for machines that sit outside normal management. If Femap is packaged through enterprise software deployment, the package inventory should be reconciled against endpoint telemetry. If installation is manual, the risk of drift is higher.
Security teams should also look at file associations and default handlers. If double-clicking an IPT file launches Femap on an unpatched system, that is a direct path to exploitation. Where possible, organizations should ensure that only patched systems are registered or approved for handling the affected file type.
Finally, incident response teams should be ready for the mundane indicators of a successful file exploit: suspicious child processes from Femap, unexpected network connections, credential access behavior, or abnormal file encryption and staging. A CAE application spawning shells, script interpreters, or unusual command-line tools should not be treated as normal engineering noise.
The Femap Advisory Turns a CAD File Into a Security Boundary
This advisory is a small story with a large moral: in 2026, the security boundary is often the file a trusted user opens. The most important actions are concrete, near-term, and well within the reach of Windows and engineering IT teams.- Organizations running Siemens Simcenter Femap should update affected installations to V2512.0003 or later as the primary mitigation.
- Unpatched systems should not be used to open IPT files from external, unsolicited, or uncertain sources.
- Security teams should inventory Femap installations rather than assuming engineering software is covered by normal desktop patch reporting.
- Administrators should treat engineering file parsers as high-risk applications when designing endpoint controls and monitoring rules.
- Supplier and customer file-exchange workflows should be routed through controlled channels instead of informal attachment handling.
- Incident responders should watch for abnormal process behavior from Femap, especially child processes and unexpected outbound connections.
Source: CISA Siemens Simcenter Femap | CISA