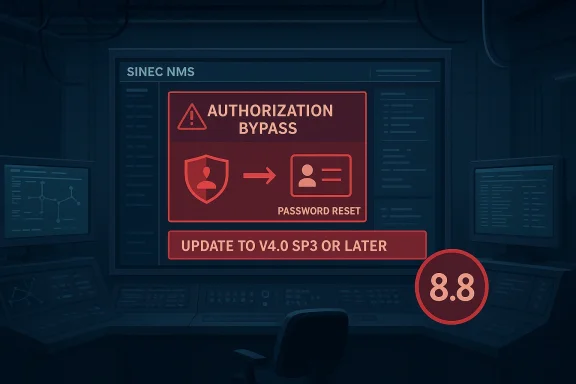
Siemens’ SINEC NMS has landed in the crosshairs of a high-severity authorization bypass flaw, and the practical consequence is hard to ignore: an authenticated remote attacker could potentially reset the password of any arbitrary user account. Siemens says the issue affects versions before V4.0 SP3, and CISA has republished the advisory with a CVSS 3.1 score of 8.8 and the clear recommendation to update to V4.0 SP3 or later
SINEC NMS sits in a sensitive part of the industrial stack. It is a network management platform, which means it can become a control point for visibility, configuration, and administrative authority across connected infrastructure. That makes an authorization flaw here more than a routine application bug; it is a problem in the layer that decides who gets to do what, and that layer is often the real perimeter in industrial environments
The advisory describes CVE-2026-25654 as a failure to properly validate user authorization when processing password reset requests. In practical terms, that means the product may trust a user’s request too much, allowing a logged-in attacker to manipulate account recovery in ways that should have been blocked. The CWE mapping points to CWE-639, Authorization Bypass Through User-Controlled Key, which is one of those defect classes that sounds narrow but can have very broad operational impact when it sits inside an admin or management console
What makes the issue especially important is the combination of reach and privilege. The CVSS vector is AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H, which tells defenders that the flaw is network-reachable, not especially difficult to exploit, requires only low privileges, and can affect confidentiality, integrity, and availability at a high level. In other words, this is not the sort of bug that waits politely for a perfect lab setup; it is the kind of weakness that can become dangerous once an attacker lands inside the right account boundary
Siemens’ guidance is straightforward: update to V4.0 SP3 or later and, until that happens, limit network access to trusted users and systems only. That may sound like ordinary hardening advice, but for a vulnerability in an access-management or network-management product, it is exactly the kind of immediate containment that can reduce the blast radius while patching is arranged
Siemens and CISA both frame the issue in terms that should make defenders pause. Siemens identifies the affected product, the affected version range, and the vendor fix, while CISA republishes the advisory to increase visibility for operators in critical manufacturing and related sectors. That republication matters because industrial advisories often move more slowly through enterprise channels than the risk itself evolves on the ground
The advisory also reflects a broader pattern in industrial software security: the most damaging bugs are often not flashy memory-corruption flaws, but logic errors in how trust is assigned. A password reset workflow is a classic place where those mistakes hide, because reset flows are designed to be helpful. If the product checks the wrong thing, or checks the right thing too late, a user can end up wielding a capability far beyond their intended scope
This is especially concerning in management software because the attacker does not need to attack the field devices directly. If the management plane can be subverted, the attacker may be able to pivot into a trusted administrative workflow and use legitimate-looking actions to alter access, hide activity, or lock out defenders. That is the reason authorization bugs in control-plane tools deserve rapid attention even when they do not involve code execution
The problem is not described as a crash, denial of service, or obscure edge case. Instead, it is a classic trust failure: user authorization is not properly validated during password reset processing. That distinction matters because password reset is one of the highest-value administrative functions in almost any system. Whoever controls account recovery often controls account access, and whoever controls account access often controls the environment
The vulnerability name also gives away the core design issue. Authorization Bypass Through User-Controlled Key usually means the application trusts an identifier, token, or context element that should have been validated against a stricter server-side rule. When that happens, the system may let the user influence whose data or whose account is affected. In a password reset path, that is exactly the kind of flaw that can result in account takeover or mass administrative disruption
A network attack vector means the attacker does not need physical access or local presence on the target host. Low attack complexity suggests the flaw is not gated by rare timing conditions or fragile prerequisites. Low privileges means the adversary does not need to start from the top of the admin ladder. And no user interaction means the attack does not depend on a victim clicking or approving anything. Taken together, those traits make the flaw operationally serious rather than theoretical
That is especially relevant in environments where administrative roles are shared, inherited, or delegated across teams. Industrial networks often have support staff, contractors, and operations personnel using carefully scoped access paths, but those scopes can become weak if the underlying software does not enforce them correctly. A single authorization mistake in a management platform can therefore have an outsized effect on real-world operational boundaries
The advisory’s critical manufacturing relevance also matters. These are not abstract users in a generic SaaS environment; they are organizations whose operations may depend on reliable administrative control over industrial assets. The risk is not simply that someone gets in. It is that they get in through a feature designed to restore trust, and then use that feature to dismantle trust for everyone else
CISA and Siemens both emphasize reducing exposure in the interim. The advisory recommends limiting network access to trusted users and systems only, and more broadly advises organizations to minimize network exposure, place control-system networks behind firewalls, and separate them from business networks. Those measures are not substitutes for the update, but they can reduce the attack surface while patching is planned and validated
The advisory’s CWE classification reinforces that point. User-controlled key flaws are dangerous because they often turn a user-supplied value into a security decision. If the system uses the wrong identifier to authorize a reset, the user may effectively choose the target of their own privilege escalation. That is not merely a bug in workflow logic; it is a direct break in the policy engine
The second thing to watch is whether the vulnerability encourages broader access-control audits. A defect like this often reveals weak assumptions about role separation, delegated administration, and password recovery policy. Even after the patch, defenders should ask whether their user management processes assume too much trust in reset workflows or administrative shortcuts
It is also an opportunity for security teams to revisit how they think about management-plane software. SINEC NMS is not just another web app; it is part of the infrastructure that decides who may manage critical systems. That makes the advisory a useful forcing function for access review, segmentation review, and administrative workflow review
Another concern is patch latency. Industrial change control is real, and it can slow deployments even when the fix is straightforward. That means exposed systems may remain vulnerable longer than anyone wants, especially if the management platform spans multiple sites or if upgrades must be synchronized with maintenance windows
It will also be worth watching whether Siemens customers use this moment to tighten their account recovery and role-assignment processes more broadly. A single authorization bypass is often a symptom of a larger design pattern, and the smartest response is to look for related weaknesses before an attacker does. That means reviewing trust boundaries, delegated rights, and the assumptions embedded in administrative workflows
Source: CISA Siemens SINEC NMS | CISA
 Overview
Overview
SINEC NMS sits in a sensitive part of the industrial stack. It is a network management platform, which means it can become a control point for visibility, configuration, and administrative authority across connected infrastructure. That makes an authorization flaw here more than a routine application bug; it is a problem in the layer that decides who gets to do what, and that layer is often the real perimeter in industrial environmentsThe advisory describes CVE-2026-25654 as a failure to properly validate user authorization when processing password reset requests. In practical terms, that means the product may trust a user’s request too much, allowing a logged-in attacker to manipulate account recovery in ways that should have been blocked. The CWE mapping points to CWE-639, Authorization Bypass Through User-Controlled Key, which is one of those defect classes that sounds narrow but can have very broad operational impact when it sits inside an admin or management console
What makes the issue especially important is the combination of reach and privilege. The CVSS vector is AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H, which tells defenders that the flaw is network-reachable, not especially difficult to exploit, requires only low privileges, and can affect confidentiality, integrity, and availability at a high level. In other words, this is not the sort of bug that waits politely for a perfect lab setup; it is the kind of weakness that can become dangerous once an attacker lands inside the right account boundary
Siemens’ guidance is straightforward: update to V4.0 SP3 or later and, until that happens, limit network access to trusted users and systems only. That may sound like ordinary hardening advice, but for a vulnerability in an access-management or network-management product, it is exactly the kind of immediate containment that can reduce the blast radius while patching is arranged
Background
Industrial security advisories often get dismissed as niche until they intersect with an administrative system that touches many downstream assets. That is the real lesson here. A flaw in SINEC NMS is not just about one password reset screen; it is about whether a user can traverse the boundary between ordinary authenticated access and administrative control over a management platform that may coordinate access to critical operational networksSiemens and CISA both frame the issue in terms that should make defenders pause. Siemens identifies the affected product, the affected version range, and the vendor fix, while CISA republishes the advisory to increase visibility for operators in critical manufacturing and related sectors. That republication matters because industrial advisories often move more slowly through enterprise channels than the risk itself evolves on the ground
The advisory also reflects a broader pattern in industrial software security: the most damaging bugs are often not flashy memory-corruption flaws, but logic errors in how trust is assigned. A password reset workflow is a classic place where those mistakes hide, because reset flows are designed to be helpful. If the product checks the wrong thing, or checks the right thing too late, a user can end up wielding a capability far beyond their intended scope
This is especially concerning in management software because the attacker does not need to attack the field devices directly. If the management plane can be subverted, the attacker may be able to pivot into a trusted administrative workflow and use legitimate-looking actions to alter access, hide activity, or lock out defenders. That is the reason authorization bugs in control-plane tools deserve rapid attention even when they do not involve code execution
Why this kind of bug matters
The advisory’s severity should not be read as a generic warning label. It is a signal that the trust model failed in a place where trust is the product itself. If the system cannot reliably decide who may reset whose password, then every downstream policy decision begins to look weaker, because identity is no longer being enforced with confidence- The flaw affects an authenticated attacker, which makes it more realistic than an unauthenticated remote crash.
- The issue is in the authorization workflow, not in a peripheral feature.
- The impact includes confidentiality, integrity, and availability.
- The remediation is a specific product update, not a vague configuration suggestion.
- The advisory is relevant to critical manufacturing environments with broad operational reach
What Siemens Disclosed
Siemens’ advisory is refreshingly direct. It states that SINEC NMS before V4.0 SP3 contains an authorization bypass vulnerability that could allow an attacker to reset the password of any arbitrary user account. The vendor also recommends updating to the latest version, which in the advisory context is concretely expressed as V4.0 SP3 or laterThe problem is not described as a crash, denial of service, or obscure edge case. Instead, it is a classic trust failure: user authorization is not properly validated during password reset processing. That distinction matters because password reset is one of the highest-value administrative functions in almost any system. Whoever controls account recovery often controls account access, and whoever controls account access often controls the environment
The exploit model in plain English
The advisory indicates that the attacker must already be authenticated, but the privilege requirement is still low. That means defenders should not assume this is safe simply because it is not unauthenticated. In the real world, many intrusions begin with stolen credentials, a compromised contractor account, an abused support login, or an over-permissioned operator profile, and a weakness like this can turn that foothold into something much more dangerousThe vulnerability name also gives away the core design issue. Authorization Bypass Through User-Controlled Key usually means the application trusts an identifier, token, or context element that should have been validated against a stricter server-side rule. When that happens, the system may let the user influence whose data or whose account is affected. In a password reset path, that is exactly the kind of flaw that can result in account takeover or mass administrative disruption
- The affected version boundary is clear: all versions before V4.0 SP3.
- The affected action is password reset processing.
- The likely attacker profile is authenticated remote.
- The recommended fix is upgrade to V4.0 SP3 or later.
- The issue maps to a well-known authorization weakness class, not an exotic exploit chain
Why password reset is a favorite target
Password reset paths are often overlooked because they are designed for convenience and recovery. That convenience can become a liability if the workflow does not re-check identity, scope, and authorization at the server side every time. In a management console, a flawed reset flow can be worse than a typical login bug because it bypasses the normal friction that protects privileged accountsSeverity and Exploitability
The CVSS 3.1 score of 8.8 is the first thing many security teams will notice, and rightly so. That score puts the issue in the high-severity range, but the more useful detail is the vector itself: AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H. That combination is a strong indicator that a relatively modest foothold could become a major problem very quicklyA network attack vector means the attacker does not need physical access or local presence on the target host. Low attack complexity suggests the flaw is not gated by rare timing conditions or fragile prerequisites. Low privileges means the adversary does not need to start from the top of the admin ladder. And no user interaction means the attack does not depend on a victim clicking or approving anything. Taken together, those traits make the flaw operationally serious rather than theoretical
Why high impact matters so much here
The confidentiality, integrity, and availability ratings are all high, which is particularly troubling in a management system. If an attacker can reset arbitrary accounts, they may be able to impersonate administrators, lock out legitimate users, alter access relationships, and interfere with operational visibility. That is a broad blast radius, not a narrow one- Confidentiality risk: unauthorized access to user or administrative data.
- Integrity risk: attacker-controlled password changes and account misuse.
- Availability risk: lockouts, disruption, or administrative confusion.
- Operational risk: the management layer may become untrustworthy.
- Recovery risk: password reset abuse can complicate incident response and forensics
How attackers would likely think about it
An attacker who already has a valid account may see this as a shortcut to broader control. Instead of trying to brute-force or phish an administrator, they may abuse the reset logic to hijack a more powerful account or to undermine access controls in a way that looks legitimate in logs. That is precisely what makes authorization bypass issues so awkward for defenders: they can blur the line between malicious activity and ordinary administrative workIndustrial and Enterprise Impact
For industrial organizations, the significance of this advisory extends beyond IT hygiene. SINEC NMS is part of a management environment that can affect how users and administrators interact with operational networks, so a flaw in account reset handling can become a gateway to broader policy abuse. If credentials are compromised, the attacker may not need to attack individual devices one by one; they may be able to use the management system to reshape access from the centerThat is especially relevant in environments where administrative roles are shared, inherited, or delegated across teams. Industrial networks often have support staff, contractors, and operations personnel using carefully scoped access paths, but those scopes can become weak if the underlying software does not enforce them correctly. A single authorization mistake in a management platform can therefore have an outsized effect on real-world operational boundaries
Enterprise versus plant-floor risk
In enterprise IT, the most obvious concern is account compromise and privilege misuse. In operational technology, the stakes are higher because identity is tied to system availability, change control, and sometimes safety-adjacent processes. A compromised management account can alter who gets to reach which resources, and that can ripple through maintenance workflows, troubleshooting access, and remote administration channelsThe advisory’s critical manufacturing relevance also matters. These are not abstract users in a generic SaaS environment; they are organizations whose operations may depend on reliable administrative control over industrial assets. The risk is not simply that someone gets in. It is that they get in through a feature designed to restore trust, and then use that feature to dismantle trust for everyone else
- Management-plane compromise can affect many downstream systems at once.
- Shared administrative workflows increase the value of a reset flaw.
- Contractors and vendors may widen the practical attack surface.
- Operational access changes can look normal until the damage is already done.
- A management system compromise can outlast a single session or login
Why defenders should care even if the product is segmented
Segmentation helps, but it is not a silver bullet. If the management plane itself is reachable by an authenticated user, and that user can then manipulate passwords or accounts they should not touch, segmentation may only reduce the number of targets—not the seriousness of the compromise. In other words, the flaw is dangerous precisely because it lives inside the protected administrative boundary, not outside itRemediation and Mitigation
Siemens’ primary remediation is simple: update SINEC NMS to V4.0 SP3 or later. That is the cleanest and most reliable answer because the vulnerability is rooted in authorization logic, not a setting that can be safely tweaked around the edges. When the trust model is broken, patching the code path is usually the only durable fixCISA and Siemens both emphasize reducing exposure in the interim. The advisory recommends limiting network access to trusted users and systems only, and more broadly advises organizations to minimize network exposure, place control-system networks behind firewalls, and separate them from business networks. Those measures are not substitutes for the update, but they can reduce the attack surface while patching is planned and validated
Practical response sequence
A sensible response should be methodical, not rushed. The first step is inventory: confirm where SINEC NMS is deployed and which version is running. The second is exposure: determine whether the management interface is broadly reachable or tightly restricted. The third is remediation: schedule the upgrade to V4.0 SP3 or later through a controlled maintenance window. The fourth is review: check for suspicious password reset activity, unusual account changes, and any role shifts that might indicate prior abuse- Identify every SINEC NMS instance in the environment.
- Confirm the installed version and compare it to V4.0 SP3.
- Restrict management access to trusted hosts and users.
- Patch or upgrade to the fixed release as soon as operationally possible.
- Review logs for password reset requests and account changes.
- Revalidate administrative roles and access rules after the upgrade.
What to verify after patching
Patching should not end the process. Organizations should verify that the updated system behaves as expected, especially around password reset and role-based access. If an exploit path existed in production, defenders should also consider whether user accounts were reset or altered before the fix was applied. In high-value environments, post-patch validation matters almost as much as the patch itself- Confirm the version is now V4.0 SP3 or later.
- Review password reset logs for unusual patterns.
- Recheck admin and delegated roles for overreach.
- Limit access to the management plane immediately.
- Preserve logs for incident review if abuse is suspected
Why This Is More Than “Just” a Login Bug
It would be easy to reduce this to a simple account-management issue, but that would miss the strategic significance. In management software, passwords are not just credentials; they are the mechanism by which trust is granted, modified, and revoked. If an attacker can abuse password reset processing, they may be able to reshape the trust structure of the entire environment without ever tripping a classic malware alarmThe advisory’s CWE classification reinforces that point. User-controlled key flaws are dangerous because they often turn a user-supplied value into a security decision. If the system uses the wrong identifier to authorize a reset, the user may effectively choose the target of their own privilege escalation. That is not merely a bug in workflow logic; it is a direct break in the policy engine
The hidden cost of permissive reset design
Password reset systems are often built to reduce friction. That is sensible from a usability standpoint, but it can create an assumption that the user asking for a reset is entitled to it. When that assumption is not validated with care, the feature becomes a security liability. In industrial management tools, where access boundaries are already highly sensitive, the margin for error is extremely thin- Convenience features can become attack primitives.
- Reset workflows often receive less scrutiny than login workflows.
- Authorization checks must be server-side and consistent.
- Management portals deserve the same skepticism as internet-facing apps.
- A low-friction feature is not the same thing as a safe feature.
What Security Teams Should Watch
The first thing to watch is whether organizations move quickly enough from disclosure to action. Industrial patch cycles are often slower than the pace of public advisories, and that lag can be the difference between a contained issue and an internal incident. If SINEC NMS is exposed to broad administrative networks or used as a shared access gateway, delay becomes a tangible risk factorThe second thing to watch is whether the vulnerability encourages broader access-control audits. A defect like this often reveals weak assumptions about role separation, delegated administration, and password recovery policy. Even after the patch, defenders should ask whether their user management processes assume too much trust in reset workflows or administrative shortcuts
Short list of practical watch items
- Is any SINEC NMS instance still running below V4.0 SP3?
- Are password reset requests being logged and reviewed?
- Is the management interface reachable from networks it should not be on?
- Do role assignments allow overly broad administrative reach?
- Has there been any unusual account takeover or lockout behavior?
- Are there adjacent systems that depend on the same trust model?
Broader implications for industrial management software
This advisory is a reminder that industrial security now lives or dies on the correctness of business logic as much as on the strength of cryptography or network segmentation. When a management tool misjudges who may reset whose password, it undermines the assumptions that keep the rest of the environment stable. That is why authorization bugs in industrial platforms deserve rapid, disciplined response and not just a routine ticket in the patch queueStrengths and Opportunities
The strongest part of Siemens’ advisory is its clarity. The affected product, version boundary, vulnerability type, severity, and fix path are all stated plainly, which gives defenders very little ambiguity to work with. That is especially useful in industrial environments, where vague remediation guidance can delay action for weeksIt is also an opportunity for security teams to revisit how they think about management-plane software. SINEC NMS is not just another web app; it is part of the infrastructure that decides who may manage critical systems. That makes the advisory a useful forcing function for access review, segmentation review, and administrative workflow review
- Clear affected version range helps with fast inventory checks.
- The vendor fix is explicit and actionable.
- The advisory supports urgent prioritization with an 8.8 score.
- The issue is understandable to both IT and OT stakeholders.
- It creates a natural moment to review role design and password recovery processes.
- It encourages tighter segmentation around management interfaces.
- It can improve logging and monitoring of privileged actions.
Risks and Concerns
The biggest concern is that authenticated flaws are often underappreciated. Organizations tend to focus on unauthenticated exploits because they sound more dramatic, but a low-privilege, network-reachable authorization bypass can be just as damaging once an attacker has any foothold. In industrial environments, footholds are not rare, and that is what makes this issue seriousAnother concern is patch latency. Industrial change control is real, and it can slow deployments even when the fix is straightforward. That means exposed systems may remain vulnerable longer than anyone wants, especially if the management platform spans multiple sites or if upgrades must be synchronized with maintenance windows
- Patch lag can extend the exposure window.
- Shared admin accounts increase abuse potential.
- Broadly reachable management portals invite misuse.
- Logs may not immediately distinguish abuse from normal admin activity.
- Attackers prefer quiet trust failures over loud crashes.
- Recovery can be messy if account resets were abused before remediation.
- Older administrative workflows may conceal the same flaw in practice.
Looking Ahead
The next question is how quickly affected organizations will treat this as a control-plane event rather than a routine software patch. If SINEC NMS is central to administrative access in a manufacturing or industrial environment, then the cost of waiting can be higher than the cost of testing and deploying the update. In that sense, the advisory is as much about operational discipline as it is about vulnerability managementIt will also be worth watching whether Siemens customers use this moment to tighten their account recovery and role-assignment processes more broadly. A single authorization bypass is often a symptom of a larger design pattern, and the smartest response is to look for related weaknesses before an attacker does. That means reviewing trust boundaries, delegated rights, and the assumptions embedded in administrative workflows
What to keep an eye on
- Adoption speed for V4.0 SP3 and later.
- Any proof-of-concept research or exploitation reporting.
- Signs of password-reset abuse in administrative logs.
- Whether related Siemens management products show similar logic issues.
- Follow-up guidance from Siemens ProductCERT or CISA.
Source: CISA Siemens SINEC NMS | CISA