Upwind’s new partnership with Microsoft signals a clear market shift: runtime-first security is moving from specialized add‑ons into Azure’s native procurement and operational flow, promising real‑time protection, prioritized vulnerability guidance, and a tighter path to enterprise deployment through the Azure Marketplace and Microsoft’s partner programs.
The headline here is straightforward: Upwind — a company positioning itself as a “runtime‑first” cloud security vendor — has announced a partnership with Microsoft to deliver an integrated runtime security experience for Azure workloads that is available through the Azure Marketplace, carries co‑sell status, and is eligible for Microsoft Azure Consumption Commitment decrements. That combination is designed to simplify procurement and accelerate adoption for enterprise customers running containerized, serverless, and other cloud‑native workloads on Azure.
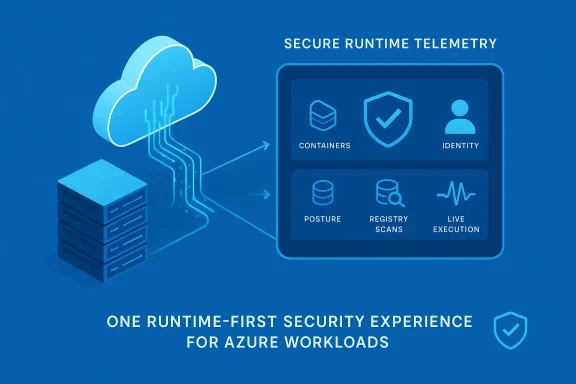
Upwind’s announcement frames the product as a single, unified experience that merges runtime protection, posture management, and vulnerability detection. The integration is presented as deeply aligned with Azure services: the platform ingests Azure cloud audit logs, maps to cloud posture frameworks, pulls in Azure Container Registry (ACR) scan results, and accelerates onboarding for cloud assets — effectively collapsing workflows that often require multiple tools and hours of manual correlation into a single pane of glass.
Gartner’s recent industry positioning — runtime visibility as a critical control for dynamic cloud environments — is quoted in the release to justify the runtime‑first approach, and Upwind promises further expansion of the integration to cover identity protection, external internet exposure, and GenAI workloads in the coming months. These road‑map items are notable and reflect where customers and vendors see the next wave of cloud risk.
Upwind’s release also lists awards and analyst placement (Frost & Sullivan, GigaOm, Gartner mentions, QKS Group SPARK Matrix™, ISMG, Latio), and a near‑perfect Gartner Peer Insights rating in CNAPP. These are relevant market signals; at the same time, buyers should consult those analyst reports directly (and look for the methodology and sample size) to understand how those rankings were derived and whether they reflect long‑term technical differentiation or short‑term vendor momentum.
That said, the announcement mixes product claims, customer testimonials, and vendor‑reported growth metrics that require independent verification. Enterprises should conduct thorough pilots focusing on performance, compatibility, telemetry governance, and integration with existing Microsoft security investments. Key questions remain around long‑term operational scale, overlap with Defender for Cloud, and the practical detail of upcoming capabilities (identity, internet exposure, and GenAI protections). These are not blockers — they are the exact things a risk‑aware buyer should validate during evaluation.
For Azure security teams willing to test runtime‑first approaches, Upwind’s Marketplace presence and partner alignment make it easy to get started; the technical and commercial architecture described in the announcement is promising. But the usual discipline applies: test in production‑like conditions, validate resource impacts and detection fidelity, and lock down telemetry and contractual controls before wide rollout. If the vendor’s future roadmap delivers on identity and GenAI protections with the same depth as its runtime detection claims, this partnership could reshape how enterprises think about cloud workload security inside Azure.
Source: StreetInsider Upwind Partners with Microsoft to Deliver Runtime Security for Azure Workloads
 Background / Overview
Background / Overview
The headline here is straightforward: Upwind — a company positioning itself as a “runtime‑first” cloud security vendor — has announced a partnership with Microsoft to deliver an integrated runtime security experience for Azure workloads that is available through the Azure Marketplace, carries co‑sell status, and is eligible for Microsoft Azure Consumption Commitment decrements. That combination is designed to simplify procurement and accelerate adoption for enterprise customers running containerized, serverless, and other cloud‑native workloads on Azure.Upwind’s announcement frames the product as a single, unified experience that merges runtime protection, posture management, and vulnerability detection. The integration is presented as deeply aligned with Azure services: the platform ingests Azure cloud audit logs, maps to cloud posture frameworks, pulls in Azure Container Registry (ACR) scan results, and accelerates onboarding for cloud assets — effectively collapsing workflows that often require multiple tools and hours of manual correlation into a single pane of glass.
Gartner’s recent industry positioning — runtime visibility as a critical control for dynamic cloud environments — is quoted in the release to justify the runtime‑first approach, and Upwind promises further expansion of the integration to cover identity protection, external internet exposure, and GenAI workloads in the coming months. These road‑map items are notable and reflect where customers and vendors see the next wave of cloud risk.
What exactly did Microsoft and Upwind announce?
The core product claim
- A unified Azure security solution that brings together:
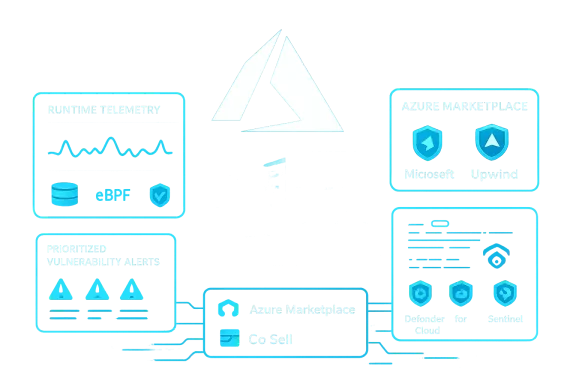
- Runtime protection backed by eBPF‑powered detection for live workload behavior.
- Cloud posture management (CSPM) to track and remediate misconfigurations.
- Vulnerability detection that factors in runtime context to prioritize what’s truly exploitable.
- Availability on the Azure Marketplace, with co‑sell status and Azure Consumption Commitment decrement eligibility — both designed to reduce procurement friction and align Upwind’s commercial model with Microsoft customers’ buying practices.
- Technical alignment includes direct integration with Azure audit logs, ACR scan outputs, and streamlining onboarding of Azure cloud assets so teams gain near‑instant, prioritized, actionable findings rather than siloed alerts.
The runtime angle: eBPF + agentless telemetry
Upwind stresses a hybrid visibility model: agentless discovery combined with eBPF‑powered runtime detection inside Linux‑based workloads. That matters because it allows the product to see both configuration-level risks (the outside‑in view) and live exploitation or anomalous in‑process behavior (the inside‑out view). The vendor frames this as fundamentally different from posture‑only solutions that can leave blind spots in dynamic, ephemeral environments.Why this matters to Azure customers
1) Closing the “what matters now” gap
Traditional vulnerability scanners and posture tools generate enormous volumes of findings. Without runtime context, defenders struggle to prioritize which vulnerabilities are exploitable in production. Upwind’s central promise is to fuse runtime telemetry with vulnerability and posture signals so security teams can focus on issues that are both present in code/configuration and actively exploitable right now. That can materially reduce mean time to detect and respond for real attacks.2) Tighter procurement and operations via Azure Marketplace and co‑sell
Making the solution available on the Azure Marketplace and qualifying it for co‑sell and consumption commitment decrements lowers friction for customers who purchase and deploy via Microsoft channels. For enterprises that operate with strict procurement pipelines tied to Microsoft agreements, that can shave weeks off procurement and make vendor evaluation simpler. The announcement explicitly calls out these commercial alignments as a competitive advantage.3) Serverless and multi‑cloud coverage
The press materials highlight runtime visibility for serverless workloads and a multi‑cloud posture, which is important for organizations that run mixed environments (AKS, Azure Functions, other clouds). Extending runtime detection into serverless containers and function platforms is nontrivial; if Upwind executes on this, it fills a frequently noted blind spot. However, customers should validate the vendor’s serverless coverage model and performance considerations in a proof‑of‑concept before full production deployment.Technical analysis: strengths, design choices, and trade‑offs
Strengths
- Runtime context reduces signal noise. Combining behavioral detection with configuration and vulnerability data should reduce false positives and help prioritize remediation tasks that materially reduce risk. This is the core technical value proposition.
- eBPF as a visibility enabler. eBPF lets agents collect high‑fidelity system and process telemetry in modern Linux workloads with relatively low overhead compared with heavier kernel hooks or instrumentation. For containerized workloads in AKS or other Kubernetes environments, eBPF is now a mainstream, efficient approach to runtime observability. Upwind’s claim of eBPF‑powered detection is therefore aligned with current technical best practice.
- Azure-native integrations. Ingesting Azure audit logs and ACR scan results makes the offering more useful to Azure customers; those connections reduce the need for additional log‑shipping work. Marketplace availability and co‑sell status also help with governance and procurement.
Risks and trade‑offs
- Vendor claims require independent validation. The press release contains commercial metrics (900% year‑over‑year revenue growth, 200% logo growth, $430M raised) and analyst recognitions. These are important signals but should be treated as company‑reported until independently verified. Enterprises should perform their own diligence and check analyst reports and customer references prior to enterprise roll‑out.
- Performance and stability considerations with eBPF. While eBPF is efficient, its misuse or misconfiguration can introduce kernel‑level complexity. Production customers must benchmark CPU/memory overhead, ensure kernel compatibility across their node images, and confirm support for any custom kernel modules or managed node service plans on AKS. The press materials don’t publish performance figures; that must be tested during pilots.
- Overlap with Microsoft Defender and Sentinel — potential for friction. Azure already provides capabilities through Microsoft Defender for Cloud and integration points to Sentinel. Upwind’s value depends on the depth and quality of telemetry, detection fidelity, and the ease with which it can feed Sentinel/Defender workflows or replace existing tooling. Customers will need to assess how Upwind integrates with Defender for Cloud’s posture features and Sentinel’s analytics, and whether it creates blind spots or redundant alerts in current workflows. The announcement emphasizes integration but does not detail data models or mapping to existing Azure security controls.
- Data residency, privacy, and telemetry governance. Any runtime platform that captures process, network, and container metadata must provide clear controls for telemetry retention, encryption, and where telemetry is stored. Large regulated customers will require contractual guarantees and the ability to host telemetry in-region. The press release doesn’t show contractual detail; procurement teams should demand SOC/ISO attestations and data processing addenda as part of the SOW.
Market and competitive context
CNAPP and the runtime-first trend
Upwind positions itself as a next‑generation CNAPP (Cloud Native Application Protection Platform) with runtime detection at the center. This mirrors an industry trend Gartner and other analysts have described: as cloud deployments grow more dynamic, runtime visibility becomes essential to close gaps left by posture‑only tools. The vendor cites analyst recognition and awards to validate its market momentum. Those recognitions are signals, but buyers should cross‑check these claims against analyst research and peer reviews when making decisions.Where Upwind fits vs. cloud‑native security incumbents
Incumbent providers often split responsibilities across several products: CSPM for posture, SCA (software composition analysis) for dependencies, vulnerability scanners for images, and EDR for endpoints. Upwind’s approach attempts to converge these signals with runtime telemetry. This could be attractive to customers tired of "tool sprawl," but it raises questions:- Does the unified approach scale to the telemetry volumes of global enterprise fleets?
- Can a single product keep pace with deep scanner capabilities and vulnerability research that specialized vendors provide?
- How mature are the integrations with third‑party dev toolchains, CI/CD pipelines, and Azure governance controls?
Commercial implications: co‑sell status and Azure Consumption Commitment decrement
Upwind’s Marketplace listing, co‑sell status, and full Azure Consumption Commitment decrement eligibility are not merely marketing copy; they materially influence procurement:- Co‑sell status typically means Microsoft field sellers can jointly engage and may include joint go‑to‑market motions, which can accelerate enterprise procurement cycles.
- Eligible solutions for Azure Consumption Commitment decrements can be counted against customer commitments to Microsoft, potentially making purchase decisions financially attractive for customers with existing Azure spend agreements.
Real customer signals and analyst recognition — reading between the lines
The announcement cites a Petrofac testimonial describing fast time‑to‑value in strengthening AKS security within hours of onboarding. Vendor case studies and testimonials can show real operational benefits, but readers should interpret them as single data points and seek multiple references across industries and geographies.Upwind’s release also lists awards and analyst placement (Frost & Sullivan, GigaOm, Gartner mentions, QKS Group SPARK Matrix™, ISMG, Latio), and a near‑perfect Gartner Peer Insights rating in CNAPP. These are relevant market signals; at the same time, buyers should consult those analyst reports directly (and look for the methodology and sample size) to understand how those rankings were derived and whether they reflect long‑term technical differentiation or short‑term vendor momentum.
Practical guidance for Azure teams evaluating Upwind
If you are an Azure security owner or platform engineer, here is a pragmatic checklist to evaluate Upwind (or any runtime‑first CNAPP) before enterprise rollout.- Pilot scope and goals
- Define a small, representative set of workloads (AKS clusters, ACR images, serverless functions).
- Agree measurable goals: false positive rate targets, detection latency, prioritized vulnerability reduction.
- Telemetry and integration validation
- Confirm the product ingests Azure audit logs and ACR results as claimed, and verify the mapping to your CSPM findings.
- Test data export to Microsoft Sentinel and Defender for Cloud to ensure alerts, playbooks, and SOAR workflows behave as expected.
- Performance and compatibility testing
- Run performance benchmarks for eBPF probes across node sizes and workload profiles.
- Verify kernel compatibility and support for your managed node OS images.
- Security and compliance due diligence
- Request SOC 2/ISO attestations, data processing agreements, and region controls for telemetry storage.
- Understand how the platform stores, masks, and retains sensitive telemetry (secrets, PII).
- Operational playbooks
- Define who in the SOC will handle runtime alerts and integrate Upwind findings into existing incident response runbooks.
- Ensure DevOps teams have clear remediation ownership for prioritized findings.
- Licensing and procurement confirmation
- Clarify Marketplace license terms, co‑sell benefits, and Azure Consumption Commitment decrement eligibility with Microsoft account teams and procurement.
What to watch next
- Identity and internet exposure coverage. Upwind announced plans to extend its integration to identity protection and internet exposure in the coming months. These areas are frequent vectors for compromise, and the depth of this integration will be a crucial differentiator. Monitor how the vendor maps signals from Entra ID/Identity Protection and external asset scanning into runtime prioritization.
- GenAI workload protections. The press release promises future coverage for GenAI workloads. That’s a logical next step since GenAI systems introduce new data‑flow and model‑serving risk profiles, but specifics will matter: will Upwind protect model serving pipelines, injection risks, prompt leakage, or only the underlying compute workloads? Customers should demand detail and test cases.
- Ecosystem interoperability. Expect more scrutiny on how Upwind meshes with Defender for Cloud, Sentinel, and other SIEM/SOAR systems. Clear, documented event schemas, support for Azure Monitor tables, and native playbook recipes will be differentiators.
Final assessment: pragmatic optimism with guarded diligence
Upwind’s partnership with Microsoft is a meaningful market signal. Delivering a runtime‑first CNAPP through the Azure Marketplace, with co‑sell status and consumption commitment alignment, lowers barriers for large enterprises to pilot and adopt runtime defenses — an important step given the pace and complexity of modern cloud deployments. The combination of eBPF runtime telemetry, Azure audit log and ACR integrations, and a single‑pane approach addresses a well‑documented operational pain: too many signals, too few contextual prioritizations.That said, the announcement mixes product claims, customer testimonials, and vendor‑reported growth metrics that require independent verification. Enterprises should conduct thorough pilots focusing on performance, compatibility, telemetry governance, and integration with existing Microsoft security investments. Key questions remain around long‑term operational scale, overlap with Defender for Cloud, and the practical detail of upcoming capabilities (identity, internet exposure, and GenAI protections). These are not blockers — they are the exact things a risk‑aware buyer should validate during evaluation.
For Azure security teams willing to test runtime‑first approaches, Upwind’s Marketplace presence and partner alignment make it easy to get started; the technical and commercial architecture described in the announcement is promising. But the usual discipline applies: test in production‑like conditions, validate resource impacts and detection fidelity, and lock down telemetry and contractual controls before wide rollout. If the vendor’s future roadmap delivers on identity and GenAI protections with the same depth as its runtime detection claims, this partnership could reshape how enterprises think about cloud workload security inside Azure.
Quick takeaways
- Upwind + Microsoft moves runtime‑first security into the Azure channel and procurement flow.
- The solution promises to combine eBPF runtime detection with posture and vulnerability signals to prioritize exploitable risks.
- Marketplace availability, co‑sell status, and consumption commitment eligibility ease enterprise procurement — but confirm details with your Microsoft account team.
- Validate performance, kernel compatibility, telemetry governance, and Sentinel/Defender integration through real pilots before broad deployment.
Source: StreetInsider Upwind Partners with Microsoft to Deliver Runtime Security for Azure Workloads