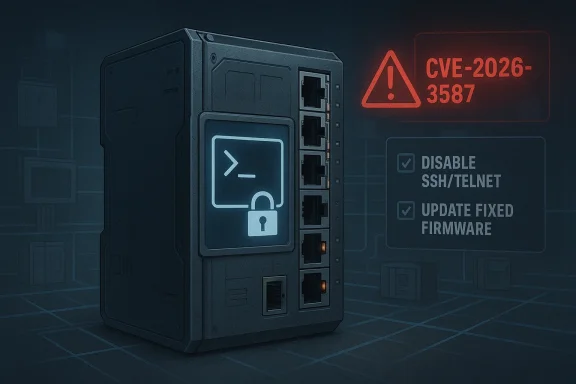
WAGO’s industrial managed switches are facing a serious security problem that reads like a classic OT nightmare: an unauthenticated remote attacker may be able to abuse a hidden function in the CLI prompt, break out of the restricted interface, and potentially gain full device compromise. The affected firmware spans multiple Lean Managed Switch and Industrial Managed Switch families, with fixed releases already identified by the vendor. WAGO’s own advisory, referenced through VDE-2026-020 and the associated CSAF record, also recommends reducing exposure by disabling SSH and Telnet where possible, underscoring how quickly an interface designed for administration can become an attack surface if it is reachable from the wrong network segment.
Industrial switches are often treated as plumbing until something goes wrong. In plant networks, water utilities, building automation systems, and factory floors, these devices sit at the intersection of IT and OT, carrying traffic that can include engineering workstations, PLCs, HMIs, historians, remote support links, and sometimes even safety-adjacent control data. That makes a flaw in the management plane more than an appliance bug; it becomes a potential bridge into an operational environment that was supposed to be segmented, hardened, and quiet.
WAGO’s managed switch line is well known in industrial automation circles because the company occupies a practical middle ground between commodity networking and control-system integration. Its 852-series devices are deployed where reliability, deterministic behavior, and remote serviceability matter. The advisory’s wording matters here: the issue is not simply a crash or a cosmetic privilege quirk, but a route from a restricted CLI into deeper control, which is precisely the kind of failure that can undermine trust in a device used as a network boundary.
The disclosure also lands in a broader OT security pattern that has become increasingly familiar over the last several years: a hidden or undocumented function, an overly permissive management path, or a command interpreter that assumes “local only” in theory but is reachable remotely in practice. Once an attacker can interact with a management prompt, even a narrow gap can become a broad compromise path if the device exposes privileged internals that were never meant for untrusted users.
The most important takeaway from the WAGO case is that the risk is not limited to a single hardware SKU or one firmware branch. The advisory enumerates many hardware variants and fixed firmware versions, which suggests a shared code base or shared CLI logic across a family of products. In industrial environments, that is exactly how vulnerabilities scale: one flaw in a common management layer becomes a fleet-wide exposure.
In practical terms, this is worse than a simple authentication bypass. It means the attacker may not need credentials, stolen secrets, or a preexisting foothold inside the plant network. If SSH or Telnet exposure is present, the attacker’s entry point may be as simple as a routable management port and a device with vulnerable firmware.
That distinction is important because it tells defenders where the attack surface lives. Some devices appear to expose the CLI through remote management services, while others still permit access locally through serial management. The threat model changes immediately depending on whether the management plane is reachable from a routed network, a jump host, or only a physically attached cable in a locked cabinet.
That is why a vulnerability in a switch CLI is strategically serious. In an office environment, a compromised access switch is bad. In an OT environment, it can be the difference between a contained incident and a site-wide outage. The consequence is not just confidentiality loss but the possibility of manipulating the network trust model that everything else depends on.
A disciplined update program should therefore treat the patched firmware as the primary response. In industrial settings, that means change windows, rollback plans, configuration backups, and validation on representative hardware before broad rollout. The older the equipment, the more care is required, but the more important it is to remove a remotely reachable management defect.
That said, these are mitigations, not cures. They may break workflows, complicate remote support, or force on-site access that some organizations are not prepared to handle. But in the short term, reducing the exposure of an unauthenticated remote attack path is the right priority when patching cannot happen immediately.
From a governance perspective, this kind of advisory is also a reminder that inventory discipline matters. If you cannot quickly identify where the vulnerable firmware lives, you cannot measure risk or prove remediation. In large organizations, the most expensive part of the response is often not the patch itself but finding every device that needs it.
That tension is why the advisory’s mitigation path is useful. Disabling remote services can buy time when the site cannot immediately patch, but it also highlights how much industrial networking still depends on convenience features that were never meant to be treated as hard security boundaries.
The most worrying part is that industrial devices often have a long service life. That means vulnerable firmware may remain in the field far longer than equivalent office IT appliances would. Longevity is a security liability when update cycles are slow and inventories are incomplete.
This is why defenders should not read the advisory too narrowly. Even if the exploit does not directly execute arbitrary code in the usual sense, control over a managed switch can still be sufficient for serious operational harm. The network layer is often where stealth and leverage are cheapest for the attacker.
That perception matters competitively because buyers compare vendor maturity as much as feature lists. If one supplier appears more transparent about management-plane hardening than another, security-conscious customers may favor the one that can explain its controls clearly. Transparency has become a selling point, not just a compliance posture.
This advisory could also push some organizations to revisit their assumption that a switch’s management plane can be exposed on a general-purpose admin network without consequence. If the CLI itself can be escaped via a hidden function, then the question is not whether the device is “managed,” but whether its management surface has been adequately minimized.
Logs and telemetry may be limited on many industrial switches, so network monitoring becomes especially valuable. Unexpected management sessions, serial-like command patterns over TCP, or unusual configuration changes should be treated as high-priority indicators. Even if you cannot directly confirm exploitation from the device alone, you may still be able to spot the surrounding behavior.
It is also likely that this disclosure will reinforce a larger industrial security trend: customers now expect proof that management interfaces are designed for least privilege from the start. The market is moving toward smaller attack surfaces, stricter defaults, and more explicit hardening options, especially for devices that sit at the edge of critical infrastructure.
Source: CISA WAGO GmbH & Co. KG Industrial Managed Switches | CISA
 Background
Background
Industrial switches are often treated as plumbing until something goes wrong. In plant networks, water utilities, building automation systems, and factory floors, these devices sit at the intersection of IT and OT, carrying traffic that can include engineering workstations, PLCs, HMIs, historians, remote support links, and sometimes even safety-adjacent control data. That makes a flaw in the management plane more than an appliance bug; it becomes a potential bridge into an operational environment that was supposed to be segmented, hardened, and quiet.WAGO’s managed switch line is well known in industrial automation circles because the company occupies a practical middle ground between commodity networking and control-system integration. Its 852-series devices are deployed where reliability, deterministic behavior, and remote serviceability matter. The advisory’s wording matters here: the issue is not simply a crash or a cosmetic privilege quirk, but a route from a restricted CLI into deeper control, which is precisely the kind of failure that can undermine trust in a device used as a network boundary.
The disclosure also lands in a broader OT security pattern that has become increasingly familiar over the last several years: a hidden or undocumented function, an overly permissive management path, or a command interpreter that assumes “local only” in theory but is reachable remotely in practice. Once an attacker can interact with a management prompt, even a narrow gap can become a broad compromise path if the device exposes privileged internals that were never meant for untrusted users.
The most important takeaway from the WAGO case is that the risk is not limited to a single hardware SKU or one firmware branch. The advisory enumerates many hardware variants and fixed firmware versions, which suggests a shared code base or shared CLI logic across a family of products. In industrial environments, that is exactly how vulnerabilities scale: one flaw in a common management layer becomes a fleet-wide exposure.
What the Advisory Says
The core finding is straightforward, even if the implementation details are not publicly dissected in full: an unauthenticated remote attacker can exploit a hidden function in the CLI prompt to escape the restricted interface and reach a privileged environment. WAGO and the linked CERT-VDE advisory identify the issue as CVE-2026-3587, and the vendor notes that the impact can lead to complete compromise of the device.Why the wording matters
The phrase hidden function is doing a lot of work here. It usually implies a command path that is not part of the normal documented operator workflow, which often means it was intended for service, diagnostics, development, or factory use. If such a path is reachable without authentication, the attack surface is already too wide; if it also permits escaping a restricted shell or menu, the security boundary is effectively gone.In practical terms, this is worse than a simple authentication bypass. It means the attacker may not need credentials, stolen secrets, or a preexisting foothold inside the plant network. If SSH or Telnet exposure is present, the attacker’s entry point may be as simple as a routable management port and a device with vulnerable firmware.
Device families affected
The advisory lists both Lean Managed Switch and Industrial Managed Switch families, including several 852-series variants and multiple firmware versions predating the patched releases. WAGO’s mitigation guidance separately distinguishes between models that should have SSH/Telnet disabled to eliminate the vector and those for which those services should be turned off to leave CLI access only via RS232.That distinction is important because it tells defenders where the attack surface lives. Some devices appear to expose the CLI through remote management services, while others still permit access locally through serial management. The threat model changes immediately depending on whether the management plane is reachable from a routed network, a jump host, or only a physically attached cable in a locked cabinet.
- Lean Managed Switches are advised to have SSH and Telnet deactivated to remove the attack vector.
- Industrial Managed Switches should also have SSH and Telnet disabled so the CLI is only accessible locally via RS232.
- Fixed firmware is available for each affected product family, and operators are expected to update rather than rely on mitigations alone.
Why This Is Dangerous in OT Networks
Industrial networks do not fail safely when management trust is broken. A compromised switch can intercept traffic, reroute commands, suppress visibility, or become a pivot point into higher-value assets such as controllers and supervisory systems. Even when a vendor bug does not directly enable code execution on process controllers, the management infrastructure itself is often enough to create broad operational risk.A switch is not “just” a switch
A managed switch is often the first real enforcement layer between enterprise IT and the control network. It may carry VLANs, ACLs, remote monitoring, mirror ports, and out-of-band administration access. If an attacker gains control of that device, they can potentially shape traffic in ways that are difficult for defenders to notice until availability or integrity has already been affected.That is why a vulnerability in a switch CLI is strategically serious. In an office environment, a compromised access switch is bad. In an OT environment, it can be the difference between a contained incident and a site-wide outage. The consequence is not just confidentiality loss but the possibility of manipulating the network trust model that everything else depends on.
Hidden service paths create asymmetric risk
The most troubling part of the WAGO issue is the asymmetry between the apparent simplicity of the flaw and the breadth of the blast radius. A hidden function in a prompt sounds small. In reality, small management-plane bugs can produce outsized consequences because they sit upstream of many other protections.- They may bypass role-based access assumptions.
- They may expose low-level configuration hooks.
- They may allow lateral movement from a management subnet into the device runtime.
- They may undermine any segmentation that assumes the CLI is only reachable by trusted admins.
- They may be exploitable long before defenders notice abnormal process behavior.
Remediation and Mitigation
WAGO’s guidance is refreshingly direct: update to the fixed firmware versions wherever possible, and use service reduction as a temporary exposure control. For the affected product groups, the vendor explicitly identifies fixed versions such as V1.2.1.S1, V1.2.3.S1, V1.2.8.S1, V1.1.9.S1, V1.0.6.S1, V1.2.0.S1, and V1.2.5.S1, depending on the hardware family.The firmware-first answer
Firmware updates are the only durable fix because they remove the vulnerable code path, not merely the exposure to it. That matters in OT because compensating controls can be brittle. A switch that sits on a maintenance subnet today may be reachable from a contractor laptop tomorrow, and a policy that depends on perfect service isolation often fails during emergencies or after routine changes.A disciplined update program should therefore treat the patched firmware as the primary response. In industrial settings, that means change windows, rollback plans, configuration backups, and validation on representative hardware before broad rollout. The older the equipment, the more care is required, but the more important it is to remove a remotely reachable management defect.
Temporary risk reduction
WAGO’s advice to disable SSH and Telnet is practical, even if it is not ideal for every site. Where those services are disabled, the CLI exposure shrinks dramatically. On industrial managed switches, the vendor notes that this leaves CLI access only via RS232, which is a meaningful reduction in remote attack surface.That said, these are mitigations, not cures. They may break workflows, complicate remote support, or force on-site access that some organizations are not prepared to handle. But in the short term, reducing the exposure of an unauthenticated remote attack path is the right priority when patching cannot happen immediately.
Practical response steps
- Inventory every WAGO switch model and firmware build in the environment.
- Compare each unit against the vendor’s fixed firmware matrix.
- Disable SSH and Telnet where operationally feasible.
- Restrict management access with segmentation and ACLs.
- Schedule firmware upgrades with testing and rollback support.
Enterprise Impact vs. Plant-Floor Reality
The enterprise side of the house may view this as another patch-management item. The plant floor experiences it as a potential interruption to uptime, remote maintenance, and vendor support. Those are not the same problem, and security teams that ignore the difference usually get resistance from operations.Enterprise IT perspective
For enterprise security teams, the key concern is that a managed switch vulnerability can become a bridge from routine infrastructure into a sensitive network segment. If a centralized IT-OT convergence architecture uses shared tools for monitoring and administration, a compromised switch may also expose credentials, visibility, or traffic patterns that help an attacker move laterally.From a governance perspective, this kind of advisory is also a reminder that inventory discipline matters. If you cannot quickly identify where the vulnerable firmware lives, you cannot measure risk or prove remediation. In large organizations, the most expensive part of the response is often not the patch itself but finding every device that needs it.
OT and plant-floor perspective
Operators on the plant side care first about uptime, second about change risk, and third about security headlines. A managed switch patch can mean a maintenance window, temporary rerouting, or a service call that requires on-site access. If the device is part of a redundant design, the update may be manageable; if not, the team has to balance exposure against outage tolerance.That tension is why the advisory’s mitigation path is useful. Disabling remote services can buy time when the site cannot immediately patch, but it also highlights how much industrial networking still depends on convenience features that were never meant to be treated as hard security boundaries.
- Security teams want to close the exposure quickly.
- Operations teams want to avoid unplanned downtime.
- Vendors want a standard remediation path that scales across SKUs.
- Integrators need clear guidance on what breaks when services are disabled.
- Everyone needs a repeatable rollback plan before touching production gear.
What This Means for Attackers
The attack scenario described in the advisory is attractive to a wide range of adversaries because it starts remotely and requires no authentication. That makes it valuable not only to targeted intruders but also to opportunistic scanning and mass exploitation if the devices are exposed to the internet or to poorly segmented remote access paths.The likely attacker playbook
A plausible attacker would begin by identifying reachable WAGO management interfaces, then probing for the restricted CLI or service endpoints associated with SSH or Telnet. If the hidden function behaves as described, the attacker could escape into a more privileged context and modify configuration, inspect traffic, or potentially establish durable access.The most worrying part is that industrial devices often have a long service life. That means vulnerable firmware may remain in the field far longer than equivalent office IT appliances would. Longevity is a security liability when update cycles are slow and inventories are incomplete.
Why full compromise matters
“Full compromise” on a switch is not just about admin access to a web panel. It can imply the ability to change configuration, disrupt traffic, isolate assets, or tamper with management visibility. In OT environments, a compromised switch can be used to hide other malicious activity by making the network itself less observable.This is why defenders should not read the advisory too narrowly. Even if the exploit does not directly execute arbitrary code in the usual sense, control over a managed switch can still be sufficient for serious operational harm. The network layer is often where stealth and leverage are cheapest for the attacker.
Competitive and Market Implications
Every industrial vendor disclosure does more than force patching. It also reshapes purchasing conversations, qualification checklists, and the way buyers evaluate management-plane design. WAGO is not alone in this space, but issues like this reinforce a market truth: buyers increasingly want evidence that “hidden” functions are either eliminated or tightly controlled.Trust as a product feature
In industrial networking, trust is part of the product. Customers expect not only performance and ruggedness, but also conservative security engineering, explicit hardening guidance, and a clear response path when issues emerge. WAGO’s publication of fixed firmware and mitigations is the right move, but the presence of a hidden function in a remotely reachable prompt can still affect perceptions.That perception matters competitively because buyers compare vendor maturity as much as feature lists. If one supplier appears more transparent about management-plane hardening than another, security-conscious customers may favor the one that can explain its controls clearly. Transparency has become a selling point, not just a compliance posture.
Procurement and architecture consequences
Procurement teams will likely ask sharper questions about management interfaces, default services, and the availability of serial-only recovery or administration paths. Architects may respond by narrowing where remote CLI access is allowed, increasing use of jump hosts, or insisting that remote management be disabled by policy unless explicitly required.This advisory could also push some organizations to revisit their assumption that a switch’s management plane can be exposed on a general-purpose admin network without consequence. If the CLI itself can be escaped via a hidden function, then the question is not whether the device is “managed,” but whether its management surface has been adequately minimized.
Detection, Exposure Review, and Operational Hardening
The hardest part of industrial advisories is often not the patch note but the discovery phase. You need to know where the vulnerable hardware sits, how it is managed, whether remote services are enabled, and whether a supposedly air-gapped segment is actually reachable through shared infrastructure.What defenders should look for
Start by locating every WAGO 852-series switch in the environment and mapping firmware versions against the vendor’s fixed builds. Then review whether SSH or Telnet is enabled, whether those services are restricted to specific hosts, and whether any jump server or remote support path could still reach the device. Because the advisory highlights a CLI prompt escape, look not only at internet exposure but also at internal trust boundaries.Logs and telemetry may be limited on many industrial switches, so network monitoring becomes especially valuable. Unexpected management sessions, serial-like command patterns over TCP, or unusual configuration changes should be treated as high-priority indicators. Even if you cannot directly confirm exploitation from the device alone, you may still be able to spot the surrounding behavior.
Hardening priorities
- Remove remote management exposure whenever possible.
- Segment switch administration away from general user networks.
- Restrict access to approved jump hosts and vendor support channels.
- Maintain offline backups of known-good configuration.
- Document recovery procedures before changing firmware in production.
Strengths and Opportunities
WAGO’s response shows a few important strengths: the company identified fixed firmware, published mitigations, and tied the issue to formal advisory channels rather than leaving customers to guess. That transparency gives operators something concrete to act on, which is critical in OT where uncertainty can paralyze response.- Fixed firmware is clearly identified for affected product lines.
- The mitigation guidance is specific rather than vague.
- The advisory acknowledges the remote attack surface directly.
- Customers can narrow exposure by disabling SSH and Telnet.
- RS232-only CLI access on some models meaningfully reduces remote risk.
- Formal advisory publication helps asset owners track remediation.
- The issue is framed in a way that supports fleet-wide inventory review.
Risks and Concerns
The downside is that a hidden-function escape in a CLI is exactly the sort of issue that can be overlooked during routine hardening because it is not visible in normal workflows. If an organization assumes the management plane is “internal” and therefore safe, this vulnerability could remain exploitable far longer than it should.- Remote authentication is not required, which lowers attacker friction.
- Hidden functions are often poorly documented and hard to audit.
- Many industrial environments have weak inventory visibility.
- Remote access paths frequently accumulate exceptions over time.
- Firmware updates can be slow in production OT networks.
- Disabling SSH/Telnet may disrupt legitimate maintenance workflows.
- A compromised switch can have outsized network-wide consequences.
Looking Ahead
The next question is not whether this advisory is serious; it is how quickly operators can translate the vendor’s guidance into actual reduction of exposure. For most organizations, that means an inventory sprint, a services review, and a firmware rollout plan. The longer the vulnerable firmware remains deployed with remote management enabled, the more attractive the target becomes.It is also likely that this disclosure will reinforce a larger industrial security trend: customers now expect proof that management interfaces are designed for least privilege from the start. The market is moving toward smaller attack surfaces, stricter defaults, and more explicit hardening options, especially for devices that sit at the edge of critical infrastructure.
- Verify whether any WAGO switch is exposed through SSH or Telnet.
- Confirm firmware against the fixed versions listed by the vendor.
- Prioritize devices that sit between enterprise and OT segments.
- Validate maintenance procedures before disabling remote services.
- Coordinate patching with operations, not after the fact.
Source: CISA WAGO GmbH & Co. KG Industrial Managed Switches | CISA
Last edited: