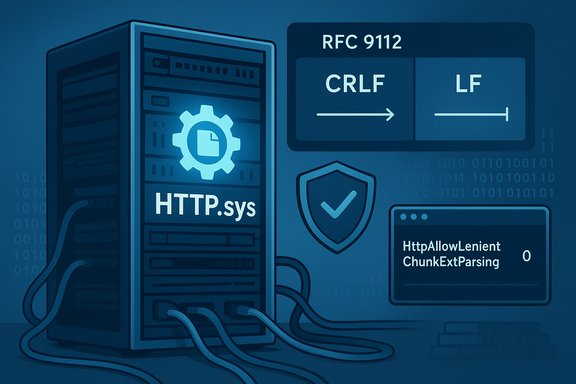
Microsoft’s November 11, 2025 cumulative update for Windows 11 — KB5068865 (OS Build 22631.6199) — closes a subtle but important standards-compliance gap in the Windows HTTP stack (HTTP.sys), aligning chunked-transfer parsing with RFC 9112 and giving administrators an explicit registry toggle to phase in the change where legacy proxies or appliances might otherwise break production traffic.
Microsoft bundles monthly cumulative updates to deliver security fixes, reliability improvements, and occasional targeted functionality changes across Windows servicing branches. The November 11, 2025 release cycle includes multiple KBs for different Windows 11 branches; for the 23H2 family the headline package is KB5068865, which consolidates fixes first staged in October’s preview cycle and folds them into the mainstream cumulative update. The KB explicitly calls out a networking fix in HTTP.sys — the kernel-mode HTTP protocol stack used by IIS and other components — that previously accepted a lone line-feed (LF) within HTTP/1.1 chunk extensions where the HTTP/1.1 standard (RFC 9112) requires a carriage return + line feed (CRLF) sequence. Microsoft provides a registry option to enforce strict RFC-compliant parsing and documents how to enable it. Why this matters: parsing inconsistencies in chunked transfer encoding are a real-world attack vector. When components in an HTTP path disagree about where one request ends and the next begins, attackers can construct inputs that are interpreted differently by a front-end proxy and a back-end server. That difference — known as HTTP request smuggling — can enable access-control bypasses, cache poisoning, credential theft, or injection of responses for other users, depending on topology. Several widely used HTTP libraries and stacks were patched earlier in 2025 for similar lenient parsing bugs (for example, Netty and h11), demonstrating that this class of parsing mismatch is not theoretical.
This is a classic operational trade-off: security hardening versus backward-compatible interoperability. The registry toggle makes the trade explicit and manageable, but it places the onus on administrators to validate end-to-end request flows before enforcing the stricter mode.
KB5068865 (OS Build 22631.6199) is available via Windows Update and the Microsoft Update Catalog; administrators should incorporate it into standard patch cycles while following the staged rollout guidance above to avoid unexpected interoperability regressions.
Source: Microsoft Support November 11, 2025—KB5068865 (OS Build 22631.6199) - Microsoft Support
 Background / Overview
Background / Overview
Microsoft bundles monthly cumulative updates to deliver security fixes, reliability improvements, and occasional targeted functionality changes across Windows servicing branches. The November 11, 2025 release cycle includes multiple KBs for different Windows 11 branches; for the 23H2 family the headline package is KB5068865, which consolidates fixes first staged in October’s preview cycle and folds them into the mainstream cumulative update. The KB explicitly calls out a networking fix in HTTP.sys — the kernel-mode HTTP protocol stack used by IIS and other components — that previously accepted a lone line-feed (LF) within HTTP/1.1 chunk extensions where the HTTP/1.1 standard (RFC 9112) requires a carriage return + line feed (CRLF) sequence. Microsoft provides a registry option to enforce strict RFC-compliant parsing and documents how to enable it. Why this matters: parsing inconsistencies in chunked transfer encoding are a real-world attack vector. When components in an HTTP path disagree about where one request ends and the next begins, attackers can construct inputs that are interpreted differently by a front-end proxy and a back-end server. That difference — known as HTTP request smuggling — can enable access-control bypasses, cache poisoning, credential theft, or injection of responses for other users, depending on topology. Several widely used HTTP libraries and stacks were patched earlier in 2025 for similar lenient parsing bugs (for example, Netty and h11), demonstrating that this class of parsing mismatch is not theoretical. What Microsoft changed in KB5068865
The technical change (concise)
- The Windows HTTP.sys request parser was corrected so it no longer accepts a single line break (LF) within HTTP/1.1 chunk extensions as if it were the required CRLF terminator.
- Microsoft added an explicit registry parameter, HttpAllowLenientChunkExtParsing, under HKLM\SYSTEM\CurrentControlSet\Services\Http\Parameters that lets administrators control the behavior:
- Setting the value to 0 forces strict RFC 9112-compliant parsing (reject or strictly parse LF-only inputs).
- A value of 1 preserves the legacy lenient behavior (accept LF-only terminations).
- The KB instructs administrators to use that key when turning on strict parsing in environments where front-end proxies might rely on the older, lenient behavior.
Registry key examples
Administrators can apply strict parsing via either reg.exe or PowerShell. Examples:- reg.exe (elevated):
- reg add "HKLM\SYSTEM\CurrentControlSet\Services\Http\Parameters" /v HttpAllowLenientChunkExtParsing /t REG_DWORD /d 0 /f
- PowerShell (elevated):
- Set-ItemProperty -Path "HKLM:\SYSTEM\CurrentControlSet\Services\Http\Parameters" -Name "HttpAllowLenientChunkExtParsing" -Value 0 -Type DWord
Standards and precedent: RFC 9112 and previous vendor fixes
RFC 9112 requirement
RFC 9112 (the modern HTTP/1.1 specification) defines the grammar for chunked transfer encoding and requires that the chunk-size and any chunk extensions be terminated by a CRLF pair (carriage return + line feed). Parsers that accept lone LF characters in place of CRLF are non-compliant and create the exact desynchronization conditions exploited in request-smuggling attacks. Conforming to the RFC removes this ambiguity at the HTTP stack level.Independent parallels: Netty and h11
This isn’t an isolated issue. In 2025 multiple popular HTTP stacks were found to accept LF-only terminations or otherwise be lenient in chunk parsing:- Netty (a widely used Java networking framework) fixed a chunk-extension parsing flaw that accepted an LF as terminating the chunk-size line; the vulnerability was tracked as CVE-2025-58056 and addressed in patched Netty releases. That advisory explicitly draws the link between LF acceptance and request smuggling when proxies parse differently.
- The Python h11 library was patched (CVE-2025-43859) for similar leniency in chunked body parsing; the h11 advisory documents how accepting imperfect terminators can be abused in certain proxy topologies.
Practical impact and compatibility considerations
Who is affected
- Public-facing servers and internal services that rely on Windows’ HTTP stack (IIS, HTTP.sys-driven user-mode servers, and any service using the HTTP Server API) are the primary audience for this change.
- Environments that place reverse proxies, load balancers, web application firewalls (WAFs), or other middleboxes in front of HTTP.sys-based back ends should pay special attention: if any intermediary historically accepted LF-only chunk extensions, enabling strict parsing could reveal incompatibilities.
- The issue is most consequential in multi-hop topologies where front-ends and back-ends use different HTTP parsing implementations or configurations. Standalone servers with no proxies are less likely to be impacted.
Compatibility trade-offs
Microsoft includes the registry toggle because real-world deployments sometimes include appliances or vendor stacks that historically tolerated non-compliant inputs. Turning on strict parsing without testing can break such paths; conversely, leaving lenient parsing enabled maintains compatibility but preserves the desynchronization risk that enables request smuggling.This is a classic operational trade-off: security hardening versus backward-compatible interoperability. The registry toggle makes the trade explicit and manageable, but it places the onus on administrators to validate end-to-end request flows before enforcing the stricter mode.
Recommendations for administrators — staged, test-first deployment
Summary checklist (immediate)
- Inventory HTTP.sys endpoints and list front-end proxies/load balancers that terminate HTTP/1.1 chunked requests.
- Apply KB5068865 through your normal patch channels (Windows Update, WSUS, Microsoft Update Catalog).
- Create a small, representative pilot group (non-production front-end/back-end combinations).
- Enable strict parsing on pilot machines by setting HttpAllowLenientChunkExtParsing = 0.
- Run functional regression tests, including synthetic request-smuggling test cases and real application flows.
- If compatibility issues appear, coordinate with the proxy/load-balancer vendor to obtain an update or apply an interim normalization rewrite on the front end.
- If vendor fixes aren’t available, consider deploying a canonicalization proxy that rewrites chunked encodings to strictly CRLF-terminated forms before passing traffic to HTTP.sys back ends.
- After successful pilot validation, expand the rollout in waves while monitoring logs, WAF alerts, and application errors.
Step-by-step pilot example (recommended)
- Select a non-production environment that mimics production front-end and back-end interactions.
- Install KB5068865 on the back-end HTTP.sys hosts.
- Set registry value to 0 on one or two hosts:
- reg add "HKLM\SYSTEM\CurrentControlSet\Services\Http\Parameters" /v HttpAllowLenientChunkExtParsing /t REG_DWORD /d 0 /f
- Reboot the test hosts.
- Perform acceptance tests:
- Regular application flows (login, file upload/download, API endpoints).
- Simulated request-smuggling checks (use safe, non-malicious test routines that differentiate LF vs CRLF handling).
- Monitor for 4xx/5xx responses or connection resets from the back-end; such failures indicate the front end may be sending non-compliant chunk terminators.
- If failures show, collect packet captures and normalized request logs to identify the exact mismatch.
- Coordinate with the intermediary vendor to remediate or plan for a controlled mitigation.
Detection and mitigation beyond the registry toggle
Detection
- Deploy WAF and IDS/IPS rules that flag irregular chunked-encoding terminators or unexpected byte sequences around chunk boundaries.
- Instrument front-end proxies and back-end servers to capture and log raw request boundaries for a sampling window; compare what the proxy forwards with what the back end receives.
- Use active scanning or controlled red-team checks to attempt safe, non-exploitive request boundary tests between your front ends and back ends post-change.
Mitigation
- Where vendor updates are available for intermediary appliances, apply them promptly.
- Use canonicalization proxies (that explicitly reformat chunked encodings to CRLF) for immediate normalization while vendor updates are pursued.
- Maintain the registry toggle in lenient mode only as a temporary compatibility bridge; prioritize remediation and move toward strict parsing to reduce long-term exposure.
Strengths and benefits of Microsoft’s approach
- Standards alignment. Enforcing RFC 9112-compliant parsing eliminates a well-understood desynchronization vector at the OS level, shrinking the attack surface for request-smuggling attacks. Aligning a kernel-mode HTTP stack with the RFC is a durable security improvement.
- Operational control. The inclusion of an explicit registry toggle recognizes real-world heterogeneity. It allows operators to pilot changes and avoid immediate breakage, which is critical for large or legacy environments where appliance updates can lag.
- Predictable deployment. The fix is distributed as a standard monthly cumulative, meaning most organizations can manage it with their existing update pipelines (WSUS, Intune, Microsoft Update Catalog), reducing operational friction for patching at scale.
- Precedent and ecosystem parity. Other major HTTP stacks were already hardened in 2025 (Netty, h11), so Microsoft’s change reduces cross-stack inconsistency and helps create a uniform expectation for request parsing across the web ecosystem.
Risks, limitations, and caveats
- Compatibility breakage. The most immediate risk is interoperability failures with reverse proxies, load balancers, CDNs, or vendor appliances that historically allowed lenient chunk parsing. In high-throughput web farms, even a small number of incompatible intermediaries can cause widespread application errors if strict parsing is turned on without testing.
- Detection complexity. Request-smuggling attempts can be subtle and may blend into normal traffic; detection requires careful logging and sometimes packet-level inspection. Administrators should not assume that the lack of obvious alerts means the absence of risk.
- No single silver bullet. Enabling strict parsing reduces one class of desynchronization vulnerability but does not substitute for robust WAF rules, up-to-date proxies, and secure application design. Comprehensive mitigation requires network, application, and stack-level defenses.
- Lack of public exploitation data in the KB. Microsoft’s KB does not state that this specific HTTP.sys parsing bug was being actively exploited in the wild at the time of the update. That absence of public exploit reports should not be viewed as a guarantee of safety; many vulnerabilities are weaponized only after patches are issued. Treat this as a proactive hardening.
- Vendor coordination needed. Where middleboxes are incompatible, remediation depends on vendors issuing fixes or customers deploying alternative normalization approaches; that can be a lengthy operational project for large enterprises.
Cross-checks and independent verification
To validate the KB’s technical claims:- Microsoft’s official KB for November 11, 2025 (KB5068865) documents the HTTP.sys fix and the registry toggle. That page is the authoritative source for the change and the recommended registry configuration.
- RFC 9112 explicitly defines the CRLF requirement for chunk-size/extension termination in HTTP/1.1; the standard language supports Microsoft’s description of the parsing discrepancy.
- Multiple independent vulnerability advisories and vendor advisories from 2025 show the same class of parsing leniency (Netty, h11), demonstrating both exploit precedent and the operational rationale for moving parsers toward strict RFC compliance. Those advisories underscore why the Windows change is necessary and consistent with prior ecosystem hardenings.
- Community and administrator guidance (pilot recommendations, rollout checklists) corroborate the practical steps Microsoft suggests, and independent community summaries reiterate the need for staged rollout and proxy vendor coordination.
Action plan (concise, prioritized)
- Inventory: Map HTTP.sys-backed servers and upstream intermediaries (CDNs, load balancers, WAFs, reverse proxies).
- Patch: Schedule KB5068865 deployment into a controlled pilot ring; do not skip patching for back-end hosts simply because the toggle exists — the fix should be installed even if lenient parsing remains temporarily enabled.
- Pilot strict mode: On 1–5 representative hosts, set HttpAllowLenientChunkExtParsing = 0 and reboot.
- Test: Run full functional tests and targeted chunked-encoding boundary tests; collect packet captures and logs.
- Remediate: If incompatibilities appear, coordinate with intermediary vendors or apply canonicalization proxies; keep strict mode disabled until issues are resolved.
- Rollout: Expand strict mode in waves, continuing to monitor telemetry and WAF/IDS alerts.
- Harden: Update WAF rules and detection signatures to flag malformed chunk sequences and potential smuggling attempts.
- Document: Record rollout decisions, detection signatures, and recovery steps in runbooks for on-call teams.
Final assessment
KB5068865 is a necessary and well-scoped hardening of Windows’ HTTP stack that aligns HTTP.sys with RFC 9112 and the broader ecosystem trend toward stricter chunked-encoding parsing. The change reduces a realistic and previously exploited class of HTTP parsing mismatch — the request-smuggling vector — and Microsoft’s inclusion of a registry toggle is a pragmatic accommodation for real-world interoperability constraints. Administrators should treat the update as both urgent and manageable: urgent because the underlying risk is tangible and has known precedents; manageable because Microsoft supplies both the patch and an operational mechanism to phase in strict parsing without immediate global breakage. The operational burden is real: large environments must budget time for pilots, vendor coordination, and possibly appliance updates or proxy normalization. But the long-term security payoff — removing a persistent desynchronization vector across diverse HTTP stacks — makes the effort worthwhile. Apply the KB, run careful pilots, and move towards strict parsing as the default posture for HTTP.sys-backed services.KB5068865 (OS Build 22631.6199) is available via Windows Update and the Microsoft Update Catalog; administrators should incorporate it into standard patch cycles while following the staged rollout guidance above to avoid unexpected interoperability regressions.
Source: Microsoft Support November 11, 2025—KB5068865 (OS Build 22631.6199) - Microsoft Support