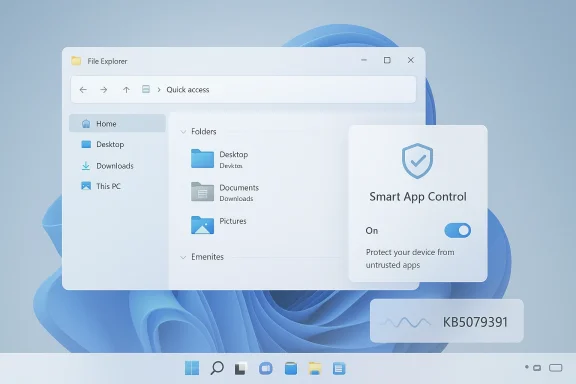
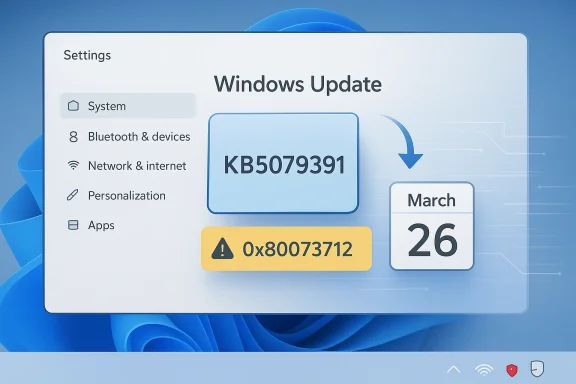
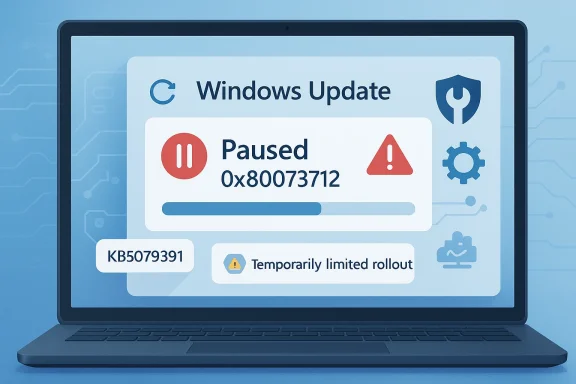
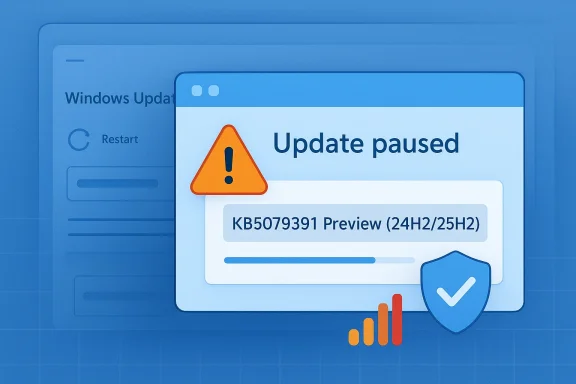
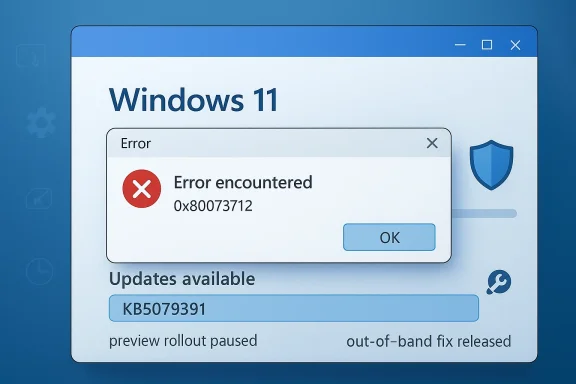
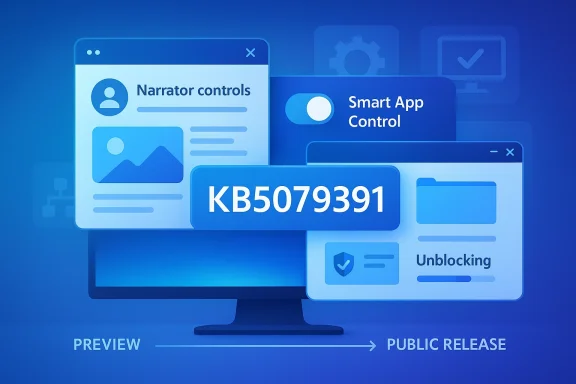
Microsoft’s latest Windows 11 servicing wave is now moving from preview to public release, and the result is a broad quality update that touches accessibility, security controls, File Explorer, Settings, display handling, and device management. Reportedly arriving as KB5079391 for Windows 11 24H2 and 25H2, the package continues Microsoft’s pattern of shipping the same monthly improvements across both branches, which share a servicing model introduced with the 25H2 rollout. That shared branch matters because it keeps feature parity tighter than the old “major version” cadence, while also making every monthly patch more consequential for both home users and enterprises.
The most important thing about this update is not any single headline feature, but the way Microsoft is refining Windows 11 as a living platform. The preview version that preceded this release, KB5077241, was framed by Microsoft as a non-security update focused on functionality, performance, and reliability, and this public release appears to carry that same philosophy forward. In other words, the update is part of the broader continuous innovation model Microsoft has been pushing across Windows 11, where smaller changes arrive more frequently rather than being reserved for one giant annual event.
That model gives Microsoft more flexibility, but it also raises the stakes for monthly servicing. Users no longer evaluate Windows updates only by whether they patch vulnerabilities; they now judge them by whether they improve the daily feel of the OS, whether they break workflows, and whether new controls behave predictably. The latest release seems designed to show progress on all three fronts, especially in areas that affect routine use: accessibility, shell behavior, display reliability, and policy management.
There is also a strategic layer here. Windows 11 version 25H2 was announced as an enablement-style release built on the same branch as 24H2, which means Microsoft can deliver many of the same innovations to both versions without forcing users into a dramatic migration cycle. That lowers the friction for IT departments, but it also means the servicing pipeline becomes the real product experience for a large share of the Windows base. For users, the monthly update is no longer background maintenance; it is part of the platform itself.
The public release also helps explain why the build numbers matter so much. According to Microsoft’s March servicing line, 26100 remains the base for Windows 11 24H2, while 26200 tracks 25H2, and both branches have been advancing in parallel. That parallelism is useful because it reduces drift between the consumer and enterprise fleets, but it also means a single servicing issue can span two widely deployed releases almost immediately.
This is not just a cosmetic accessibility change. Richer descriptions can make screenshots, diagrams, and interface-heavy applications more usable for people who depend on assistive tech, while Copilot integration offers a second layer of context when the local model is not enough. The bigger strategic point is that Microsoft is trying to make accessibility a showcase for its AI platform rather than a separate silo of features. That is smart product positioning, though it also creates expectations that these AI-assisted tools will be consistently accurate.
Smart App Control has always represented a tension in Windows design. On one hand, it aims to block untrusted or potentially harmful apps and reduce attack surface; on the other, its earlier deployment model made it feel rigid and hard to revisit once a system state changed. Loosening that requirement makes the feature more usable, but it also suggests Microsoft understands that security controls work best when they are reversible and transparent.
File Explorer has long been one of the most sensitive parts of Windows because it sits at the intersection of file security, shell extensions, preview panes, and user expectations. Even small regressions can cascade into user-visible freezes or odd permission behavior, which is why Microsoft repeatedly returns to this area in quality updates. The new release also includes more flexible sorting for permissions in Advanced Security Settings, which shows the company is still paying attention to management workflows.
That last detail is significant because it shows how Windows is increasingly serving as a storefront for Microsoft services as well as a desktop platform. Consumers may appreciate convenience, but they may also see it as another reminder that the operating system is deeply tied to Microsoft’s ecosystem strategy. The redesigned dialog boxes in Other users, including dark mode support, fit the same pattern: the company is trying to make account management feel more modern and less fragmented.
These kinds of changes often fly under the radar until they fail. High-refresh displays, multi-monitor setups, and USB4 peripherals are precisely where edge-case bugs tend to surface, and Windows has to work across a wild range of hardware quality levels. By investing in these scenarios, Microsoft is signaling that it wants Windows 11 to stay credible on premium hardware as well as mainstream laptops.
These are the kinds of details that never generate social media excitement, but they matter enormously in enterprise environments where consistency is more important than novelty. Group Policy reliability, printer baselines, and policy tagging directly affect the ability of IT teams to standardize behavior across fleets. If those controls are weak, the cost shows up later in help desk tickets, compliance issues, and deployment delays.
The fact that Microsoft is still adjusting WinRE behavior underscores how complex Windows servicing has become in a mixed architecture world. ARM64 is no longer an experimental niche; it is a real production platform for some users, and recovery workflows must work there as reliably as they do on x86 systems. The network-location update fix is equally important because enterprise deployments often depend on non-local update sources and scripted delivery paths.
The next milestone is likely the usual split between early adopter feedback and broader enterprise adoption. Home users will notice whether Narrator feels smarter, whether File Explorer stops behaving oddly, and whether display and sleep behavior improve. IT teams, meanwhile, will care more about Group Policy consistency, update installation reliability, and whether Smart App Control is now easier to govern at scale.
Source: Windows Report https://windowsreport.com/kb5079391...trol-narrator-and-file-explorer-improvements/
 Overview
Overview
The most important thing about this update is not any single headline feature, but the way Microsoft is refining Windows 11 as a living platform. The preview version that preceded this release, KB5077241, was framed by Microsoft as a non-security update focused on functionality, performance, and reliability, and this public release appears to carry that same philosophy forward. In other words, the update is part of the broader continuous innovation model Microsoft has been pushing across Windows 11, where smaller changes arrive more frequently rather than being reserved for one giant annual event.That model gives Microsoft more flexibility, but it also raises the stakes for monthly servicing. Users no longer evaluate Windows updates only by whether they patch vulnerabilities; they now judge them by whether they improve the daily feel of the OS, whether they break workflows, and whether new controls behave predictably. The latest release seems designed to show progress on all three fronts, especially in areas that affect routine use: accessibility, shell behavior, display reliability, and policy management.
There is also a strategic layer here. Windows 11 version 25H2 was announced as an enablement-style release built on the same branch as 24H2, which means Microsoft can deliver many of the same innovations to both versions without forcing users into a dramatic migration cycle. That lowers the friction for IT departments, but it also means the servicing pipeline becomes the real product experience for a large share of the Windows base. For users, the monthly update is no longer background maintenance; it is part of the platform itself.
Why this update matters
The update lands at a time when Microsoft is trying to balance three separate priorities: polish for consumers, manageability for enterprises, and confidence for accessibility-first workflows. The same patch touches Narrator, Smart App Control, File Explorer, Settings, and Windows Recovery Environment behavior, which is a sign that Microsoft is targeting the full stack rather than isolated bug fixes. That breadth is useful, but it also means organizations will want to test the update carefully before blanket deployment.- It reinforces Microsoft’s shift toward monthly platform refinement.
- It keeps 24H2 and 25H2 aligned on the same servicing train.
- It brings visible improvements to everyday Windows 11 workflows.
- It also adds or adjusts features that administrators may need to govern.
From Preview to Public Release
Microsoft’s release pattern has become increasingly familiar: an optional preview update appears first, feedback arrives from Insiders and early adopters, and then the same code path is folded into the broader public rollout. In this case, the preview cadence for March 2026 builds on earlier Release Preview updates that delivered quality improvements before the security cumulative update cycle. That approach gives Microsoft a chance to surface compatibility problems before the update becomes the default path for the mainstream audience.The public release also helps explain why the build numbers matter so much. According to Microsoft’s March servicing line, 26100 remains the base for Windows 11 24H2, while 26200 tracks 25H2, and both branches have been advancing in parallel. That parallelism is useful because it reduces drift between the consumer and enterprise fleets, but it also means a single servicing issue can span two widely deployed releases almost immediately.
What changed from the preview build
The earlier preview emphasized features such as Cross-Device Resume, Smart App Control, and MIDI support, while also refining storage cleanup presentation and fixing usability problems like Start menu glitches and File Explorer freezing. Public release notes typically keep much of that groundwork intact, which is why early testing is so important to Microsoft’s monthly rhythm. Even when the final package is mostly the same, the rollout to general users marks a shift from controlled validation to real-world scale.- Preview builds act as dress rehearsals for the public servicing channel.
- Microsoft uses them to catch compatibility regressions before broad deployment.
- The public release usually confirms the broader feature direction.
- Any preview bugs that survive testing become far more important once the patch hits real devices.
Narrator Gets a Stronger AI-Driven Push
One of the most visible additions in the update is the expanded Narrator experience. Microsoft is pushing richer image descriptions and tighter integration with Copilot, aiming to improve how blind and low-vision users interpret on-screen visuals. On Copilot+ PCs, the descriptions are generated on-device, which is a meaningful detail because it affects both latency and privacy perception.This is not just a cosmetic accessibility change. Richer descriptions can make screenshots, diagrams, and interface-heavy applications more usable for people who depend on assistive tech, while Copilot integration offers a second layer of context when the local model is not enough. The bigger strategic point is that Microsoft is trying to make accessibility a showcase for its AI platform rather than a separate silo of features. That is smart product positioning, though it also creates expectations that these AI-assisted tools will be consistently accurate.
Accessibility and AI as a combined story
The combination of Narrator and Copilot shows where Microsoft wants Windows accessibility to go next. Instead of merely reading interface elements aloud, the OS is trying to interpret what a user is seeing and provide a more human explanation. That can be transformative for image-heavy content, but it must be handled carefully because the wrong description can be more confusing than no description at all.- Rich image descriptions improve visual context.
- Copilot integration adds interactive follow-up.
- On-device generation lowers latency on Copilot+ PCs.
- Accuracy and consistency will determine whether the feature feels trustworthy.
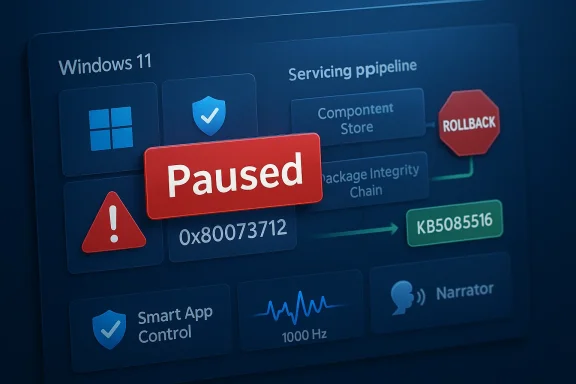
Smart App Control Becomes Less Inflexible
The update’s Smart App Control change may matter more to administrators than to average consumers, but it is one of the most important quality-of-life refinements in the release. Microsoft is allowing users to turn Smart App Control on or off without requiring a clean install, removing one of the feature’s biggest practical annoyances. That matters because security tools are only useful when people can actually manage them without rebuilding a machine.Smart App Control has always represented a tension in Windows design. On one hand, it aims to block untrusted or potentially harmful apps and reduce attack surface; on the other, its earlier deployment model made it feel rigid and hard to revisit once a system state changed. Loosening that requirement makes the feature more usable, but it also suggests Microsoft understands that security controls work best when they are reversible and transparent.
Security posture without the friction
This change is especially meaningful for power users who test software, developers who spin up tools frequently, and organizations that pilot apps before approving them broadly. A control that can be enabled or disabled from Settings > Windows Security > App & Browser Control is easier to document, support, and explain. That sounds mundane, but in endpoint management, mundane usability often decides whether a security feature is adopted or ignored.- Smart App Control is now easier to toggle.
- The feature remains focused on blocking risky apps.
- The new model reduces the need for a clean install.
- Admins get a more practical path for testing and support.
File Explorer and Shell Reliability Continue to Improve
For many users, the most welcome changes in this update will be the subtle ones inside File Explorer and the shell. Microsoft says file unblocking is now more reliable for previews, and it has also improved handling around renaming files with Voice Typing using Win + H. Those are not flashy features, but they are exactly the sort of paper cuts that can turn Windows from efficient to irritating.File Explorer has long been one of the most sensitive parts of Windows because it sits at the intersection of file security, shell extensions, preview panes, and user expectations. Even small regressions can cascade into user-visible freezes or odd permission behavior, which is why Microsoft repeatedly returns to this area in quality updates. The new release also includes more flexible sorting for permissions in Advanced Security Settings, which shows the company is still paying attention to management workflows.
Small fixes with large daily impact
These changes are easy to overlook in a marketing summary, but they can materially improve confidence in the OS. File unblocking issues in preview workflows are the kind of thing that frustrates users who regularly download tools, installers, or documents from shared environments. Voice Typing in rename flows is another example of a feature that looks minor but can be a genuine productivity boost for users with mobility limitations or just busy hands.- More reliable file unblocking reduces workflow friction.
- Win + H support in renaming improves hands-free use.
- Security settings sorting makes audits easier.
- Shell fixes often prevent broader stability complaints.
Settings, Account Management, and the Consumer Experience
Microsoft is also polishing the Settings app and account-related workflows. The About page now has a clearer layout, the Home page device card is more structured, and opening Settings Home appears more reliable. Microsoft 365 Family users can now upgrade plans directly from Settings > Accounts, which is a strong sign that the company wants the OS to be a place where subscription and device management intersect more naturally.That last detail is significant because it shows how Windows is increasingly serving as a storefront for Microsoft services as well as a desktop platform. Consumers may appreciate convenience, but they may also see it as another reminder that the operating system is deeply tied to Microsoft’s ecosystem strategy. The redesigned dialog boxes in Other users, including dark mode support, fit the same pattern: the company is trying to make account management feel more modern and less fragmented.
The line between useful and intrusive
There is a thin line between making Settings more helpful and turning it into a promotional surface. Microsoft seems aware of this tension, which is why the update also includes the ability to disable suggested upgrade prompts. That is a good sign, because the best subscription workflows are the ones that help without feeling coercive.- The About page is easier to scan.
- The Home card is more structured.
- Microsoft 365 Family upgrades are more direct.
- Suggested prompts can be disabled.
Display, Input, and Hardware Behavior
The update contains a set of display and input refinements that matter more than they might initially appear. Microsoft says it now supports monitors reporting refresh rates above 1000 Hz, improves USB4 monitor sleep behavior, and enhances auto-rotation after sleep. It also claims better HDR reliability and more accurate monitor size reporting through WMI APIs, which should help both end users and device inventory tools.These kinds of changes often fly under the radar until they fail. High-refresh displays, multi-monitor setups, and USB4 peripherals are precisely where edge-case bugs tend to surface, and Windows has to work across a wild range of hardware quality levels. By investing in these scenarios, Microsoft is signaling that it wants Windows 11 to stay credible on premium hardware as well as mainstream laptops.
Why these changes matter for power users
For enthusiasts, gamers, and creative professionals, display reliability can be the difference between a smooth desktop and a constant troubleshooting cycle. Better HDR behavior and auto-rotation after sleep are not glamorous changes, but they improve confidence that the OS will behave correctly after suspend, dock, or reconnect events. On the enterprise side, more accurate WMI reporting also helps device management and inventory systems make better decisions.- High-refresh support is important for premium panels.
- USB4 sleep improvements reduce dock-related annoyances.
- Auto-rotation fixes help convertibles and tablets.
- Accurate WMI display data benefits asset management.
Enterprise, Policy, and Manageability Changes
A number of the update’s most practical changes are aimed at managed environments. Microsoft added support for DisableSeamlessLanguageBar in Remote Desktop PowerShell, improved start menu layout application via Group Policy, and tightened Application Control for Business ID tagging. It also updated printer support baselines and improved how updates behave when run from certain network locations.These are the kinds of details that never generate social media excitement, but they matter enormously in enterprise environments where consistency is more important than novelty. Group Policy reliability, printer baselines, and policy tagging directly affect the ability of IT teams to standardize behavior across fleets. If those controls are weak, the cost shows up later in help desk tickets, compliance issues, and deployment delays.
The hidden enterprise value
There is a reason Microsoft keeps polishing these backstage mechanisms. Enterprises are the customers most likely to delay updates if they suspect instability, and the company knows that predictable policy behavior is part of what keeps Windows viable in managed fleets. In that sense, the enterprise fixes here are not auxiliary; they are central to keeping trust intact.- Policy application is more reliable.
- Remote Desktop administration gets a useful update.
- Printer support remains a major compatibility focus.
- Network-path update handling improves deployment resilience.
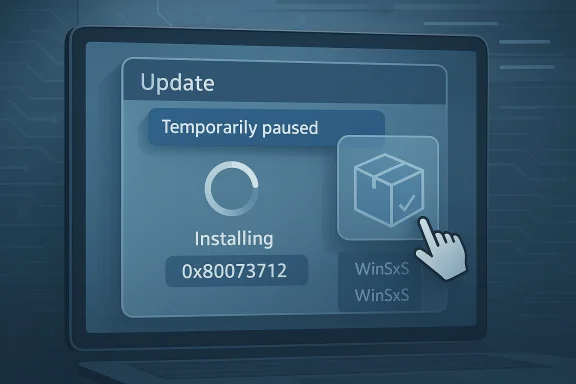
Reliability, Recovery, and Under-the-Hood Stability
Beyond the visible features, Microsoft is also cleaning up the plumbing. The update improves stability in Windows Recovery Environment when running x64 apps on ARM64 devices, and it fixes an issue where .msu updates could fail with ERROR_BAD_PATHNAME from certain network locations. Those sorts of fixes are the backbone of a healthy update cycle because they affect recovery, installation, and maintenance.The fact that Microsoft is still adjusting WinRE behavior underscores how complex Windows servicing has become in a mixed architecture world. ARM64 is no longer an experimental niche; it is a real production platform for some users, and recovery workflows must work there as reliably as they do on x86 systems. The network-location update fix is equally important because enterprise deployments often depend on non-local update sources and scripted delivery paths.
Recovery is a feature, not just a fallback
A lot of users only think about recovery tools after something goes wrong, but Microsoft has to design them as first-class components. If WinRE fails or update install paths behave unpredictably, the entire servicing model becomes less trustworthy. In that sense, these fixes are foundational rather than optional.- WinRE stability helps when systems are under stress.
- ARM64 support remains a strategic priority.
- Update installation reliability is essential for admins.
- Recovery issues can erode confidence in the whole release train.
sfc /scannow matters, even if the change is just the removal of an unnecessary error message. Small cleanups in diagnostics help reduce noise during troubleshooting, which in turn makes support processes more efficient. Less confusion in repair workflows is a real win.Strengths and Opportunities
This update’s biggest strength is its breadth. It makes Windows 11 feel more coherent by touching the places users encounter every day, while also improving the less visible systems that keep enterprise deployments stable. Microsoft is clearly trying to make monthly servicing feel like ongoing product refinement rather than a chore, and that is a promising direction.- Narrator becomes more capable and more AI-aware.
- Smart App Control becomes easier to manage.
- File Explorer and shell reliability get practical improvements.
- Settings becomes clearer and more structured.
- Display support improves for high-end and complex setups.
- Enterprise policy handling gets more predictable.
- Recovery and update reliability improve.
- Microsoft keeps 24H2 and 25H2 aligned on one servicing path.
Risks and Concerns
The main concern is that the update is so broad that it could expose edge-case regressions across multiple subsystems at once. Microsoft has already seen testing-stage reports tied to camera behavior and lock screen quirks in the preview cycle, and that is a reminder that broad servicing releases can create new instability even when their intent is to improve quality. Users and admins will want to watch the first days of rollout closely.- Preview-stage bugs can survive into public rollout.
- Accessibility AI features may face accuracy questions.
- Smart App Control changes could confuse less technical users.
- Display and docking fixes may vary by hardware vendor.
- Enterprise policy changes can behave differently across managed images.
- Any broad monthly update carries a risk of unintended regressions.
- Rollout timing can make troubleshooting harder if issues appear gradually.
Looking Ahead
What happens next will depend less on the feature list itself and more on how the update behaves in the real world. If the rollout is clean, Microsoft gets a much-needed validation of its continuous innovation strategy, especially for accessibility and manageability features. If problems emerge, the same breadth that makes the update attractive will also make remediation more complicated.The next milestone is likely the usual split between early adopter feedback and broader enterprise adoption. Home users will notice whether Narrator feels smarter, whether File Explorer stops behaving oddly, and whether display and sleep behavior improve. IT teams, meanwhile, will care more about Group Policy consistency, update installation reliability, and whether Smart App Control is now easier to govern at scale.
- Watch for any camera or lock screen regressions during rollout.
- Monitor whether Narrator’s image descriptions are consistently accurate.
- Check whether Smart App Control’s new toggle model behaves cleanly.
- Validate display sleep and HDR behavior on multi-monitor systems.
- Confirm policy and Remote Desktop changes in managed environments.
Source: Windows Report https://windowsreport.com/kb5079391...trol-narrator-and-file-explorer-improvements/