Microsoft’s new Copilot Tasks marks a deliberate pivot from conversational assistants to autonomous, scheduled work — a cloud‑first agent that does rather than just answers. Announced on February 26, 2026, as a research preview, Copilot Tasks runs in its own sandboxed cloud environment with a dedicated browser and compute, accepts natural‑language instructions for one‑off or recurring jobs, and reports back when tasks are complete. The company positions Tasks as a safer, enterprise‑friendly alternative to the recent wave of local, developer‑facing agent frameworks — notably the open, local‑first OpenClaw — while acknowledging the tradeoffs that come from leaving a device’s full surface area off the table.
However, the tradeoff is meaningful: without device access, Tasks can’t do everything a local agent can. Power users and developers who need deep system integration will keep tinkering with OpenClaw‑style frameworks, and security teams will continue to hunt for ways to govern those deployments. The launch also exposes a practical engineering challenge: turning high‑level demos into reliable, auditable, and scalable features requires excellent connector engineering, careful rights management, and complete transparency about logging and retention.
For IT teams, the sensible posture is not reflexive adoption or outright rejection, but controlled experimentation paired with strict governance. Demand auditability, insist on least‑privilege connectors, and require human‑in‑the‑loop confirmation for any financial or contractual action. For power users, understand the limitations of cloud sandboxes and weigh whether local agents justify their maintenance and risk overhead.
In short: Copilot Tasks doesn’t eliminate the agentic future — it shapes it. It offers a middle path that brings many of the productivity gains of autonomous agents to a wider audience while making the job of risk management tractable for organizations. Whether it becomes the dominant model will depend on Microsoft’s execution around enterprise controls, transparency, and connector breadth. If those pieces fall into place, Tasks could be the feature that turns agentic AI from an experimental developer curiosity into a mainstream workplace tool.
Conclusion
Copilot Tasks is a milestone: a major vendor taking agentic AI seriously while answering security critiques with architecture and process. It’s not a silver bullet — no agent is — but it is a measured, enterprise‑minded approach that shifts the conversation from whether autonomous agents are possible to how we operate them safely, transparently, and productively. The next months of previews and enterprise pilots will tell us whether Microsoft can deliver the missing governance pieces at scale, and whether the rest of the ecosystem adapts to a future where AIs not only converse, but do actual work for us.
Source: MakeUseOf Microsoft just announced its answer to OpenClaw, and it actually looks pretty great
 Background
Background
Why "agentic AI" is the story of the moment
The industry has been racing from chat to action. Early chatbots proved large language models could be conversational partners; agentic systems aim to take multi‑step actions across apps and services with minimal human orchestration. That shift has produced powerful productivity gains, but also a torrent of security debate: local agents like OpenClaw demonstrated how useful and dangerous an assistant with full device access can be, prompting warnings, scanners, and emergency fixes from security teams. Microsoft’s Copilot Tasks arrives squarely into that debate as a product designed to make agentic capabilities broadly useful while controlling the blast radius of what an automated agent can touch.The announcement in brief
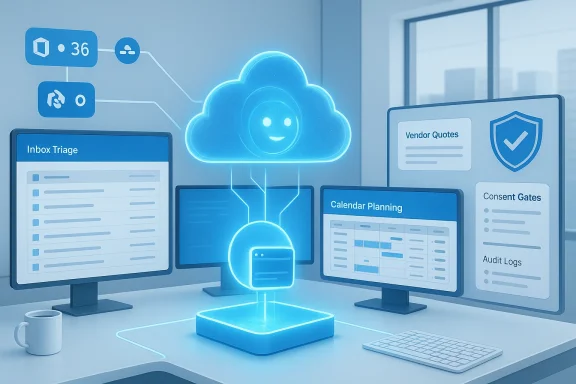
Microsoft’s Copilot team described Tasks as “AI that doesn’t just talk to you, but works for you.” The product is entering a limited research preview with a waitlist; Microsoft says it will expand access over the coming weeks as it collects real‑world feedback. Early marketing materials and demos show Tasks performing scheduling, vendor comparison and booking, inbox triage, syllabus‑to‑study‑plan conversion, and automated slide generation from emails and attachments. Critically, Microsoft emphasizes consent gates: the agent will ask before taking “meaningful actions” such as spending money or sending messages on a user’s behalf.How Copilot Tasks works: a technical overview
Cloud sandbox with its own browser and compute
Unlike local agents that run with the same privileges as the signed‑in user, Copilot Tasks spins up its own cloud‑hosted compute instance and browser session for each task (or set of tasks). That environment is isolated from the user’s device and performs web browsing, form filling, multi‑service orchestration, and document creation using connectors to the user’s Microsoft 365 and authorized third‑party services. When the task finishes, Tasks returns a report summarizing actions taken and artifacts produced. Microsoft frames this as a way to give the agent real-world capabilities while reducing direct exposure of personal devices and local files.Natural language goals and planning
Users describe outcomes in plain language — for example, “Find top‑rated plumbers nearby, compare quotes, and book the best one” — and Copilot Tasks generates a step‑by‑step plan, executes it in the sandbox, and surfaces the results. Tasks supports one‑time runs as well as scheduled or recurring workflows, enabling regular automation like weekly inbox triage or Friday apartment listing checks. The planning component is designed to be interactive: Tasks proposes a plan and asks for refinements or approvals as needed.Consent gates and user control
Microsoft stresses that Tasks is “not autopilot” — the system should ask for consent before carrying out actions with direct downstream consequences. That includes payments, booking commitments, or sending messages. Users can review, pause, or cancel a running task at any time, according to the announcement. This consent model is central to Microsoft’s safety framing and is intended to appeal to organizations worried about unsupervised agents acting on behalf of employees.Use cases and early demos: what Copilot Tasks promises to do
Microsoft’s release included a set of concrete examples that illuminate the product’s intended sweet spots. These are not hypothetical lab experiments — they map to repetitive, multi‑step chores that are prime candidates for automation.- Recurring inbox triage: nightly surfacing of urgent messages with draft replies prepared and automatic unsubscription from unused promotional lists.
- Apartment hunting: weekly scans for new rental listings in a geographic area, followed by automatic scheduling of viewings.
- Study planning: converting a course syllabus into a structured study plan with practice tests and calendar blocks.
- Vendor comparison and booking: identify local contractors, compare quotes, and make a booking after user approval.
- Slide decks from inbox content: turning emails, attachments, and images into presentation slides with charts and talking points.
Copilot Tasks versus OpenClaw: an apples‑to‑architectures comparison
The fundamental architectural split
- Copilot Tasks: cloud‑hosted, sandboxed compute and browser; limited to data and services a user explicitly connects (Microsoft 365 and authorized connectors). Consent gates and centralized controls are baked into the model’s operational story.
- OpenClaw: local‑first agent that runs on a user’s machine, with direct access to local files, developer tools, credentials, and system APIs when permitted. This local access yields extended capabilities — and broad risk. OpenClaw’s rapid adoption drew security warnings precisely because that access can be exploited or misconfigured.
Safety vs. raw capability: the tradeoff
The calculus is straightforward: local agents can do more because they run inside your environment, but they also widen the attack surface. Microsoft argues that by restricting Tasks to cloud execution and explicit connectors, the product is safer for mainstream users and enterprises. OpenClaw and similar local frameworks remain more attractive to developers and power users who need direct file, network, or tool access and are willing to accept (or mitigate) the associated risks. In short: Copilot Tasks sacrifices some power to gain a materially smaller blast radius.Real‑world evidence of OpenClaw’s risk profile
Recent security research and vendor advisories have spotlighted how quickly local agents can become attack vectors. Independent researchers found exposed OpenClaw instances leaking keys and data, and third‑party teams uncovered chains that allowed remote websites to hijack agents running on localhost without extra user action. Those incidents prompted emergency patches and the emergence of security tools designed specifically to scan and mitigate agent exposures. The security community’s response is one of the drivers behind Microsoft’s cloud‑isolated approach.Security analysis: strengths, blind spots, and residual risk
Strengths: containment, governance potential, and consent
- Containment: Tasks’ dedicated cloud environment keeps uncontrolled code off user endpoints, reducing the risk of lateral movement and credential theft from a compromised laptop or desktop.
- Central governance: For organizations that adopt Copilot Tasks at scale, Microsoft can reasonably implement tenant‑level policies, logging, and access controls — features that are far harder to retrofit onto a rogue local agent.
- Consent gates: Requiring explicit approval before meaningful commitments — spending money, booking services, or sending messages — provides a practical guardrail that addresses many user fears.
Residual and newly emergent risks
- Scope creep through connectors: Although Tasks isolates compute, it still needs access to user accounts and connectors to take useful actions. If an attacker injects malicious prompts into a user’s account or misuses OAuth tokens, the agent’s cloud session could still act in unwanted ways within the scope of those permissions. That’s a narrower risk than full local compromise, but still consequential.
- Prompt injection and external manipulation: Agents that browse the web remain vulnerable to malicious or adversarial web content intended to persuade or mislead the agent into inappropriate actions. Sandboxes limit device damage, but not necessarily bad decisions performed within the allowed connectors.
- Audit and compliance gaps at launch: Early previews often ship without enterprise‑grade audit trails, retention policies, or eDiscovery integrations. Organizations with strict compliance regimes will need clarity on how Tasks records actions, stores artifacts, and supports legal holds before enabling it for knowledge workers. Microsoft has signaled these features as priorities, but availability and granularity matter.
- Concentration risk: Putting agent compute in a cloud provider reduces endpoint risk, but concentrates risk in the provider’s infrastructure. Misconfigurations, insider threats, or multi‑tenant bugs could still expose many users. This is a different risk profile rather than the elimination of risk.
How OpenClaw failures changed the calculus
Public disclosures about OpenClaw showed how trivial misconfigurations can cascade — from local port exposure to credential leakage — and how quickly an agent can become a corporate exposure. These incidents underline why many enterprise security teams will prefer an agent that integrates with centralized identity, governance, and logging rather than one running uncontrolled on employee hardware. That doesn’t make cloud agents immune, but it does make governance feasible at scale.Enterprise considerations: adoption checklist
Organizations contemplating Copilot Tasks should evaluate a set of concrete signals before broad deployment. Here are the practical items to watch for and demand from vendors:- Auditability and exportable activity logs that map agent actions back to users and decisions.
- Granular connector controls and permission scopes — ideally with the ability to restrict Tasks to read‑only access for some services.
- Data retention and residency guarantees, plus eDiscovery hooks for legal and regulatory responses.
- Administrative policy controls for tenant‑level enable/disable, whitelisting templates, and per‑user approval requirements.
- Robust monitoring: integrate Task activity with SIEM/XDR platforms to detect anomalous patterns. Microsoft itself has recommended extra endpoint protections where OpenClaw or similar agents are permitted to run.
Developer and power‑user perspective: why OpenClaw still matters
Not every user values a reduced blast radius over full control. Developers and power users prize local agents because they can:- Read and manipulate local files and repositories.
- Execute shell commands and orchestrate developer toolchains.
- Integrate deeply with local services and ephemeral development credentials.
Privacy, legal, and compliance angles
Data access and residency
Because Copilot Tasks necessarily processes content from a user’s accounts to act (emails, calendar, documents), organizations will need clear contracts about how long scraped content is retained, where it is stored, and whether it can be exported for compliance. Early signals from Microsoft indicate that Tasks will integrate with Microsoft 365, but many enterprises require additional assurances — eDiscovery hooks, audit logs, and region‑bound processing — before wide deployment.Who bears liability for automated actions?
Consent gates reduce the risk that the agent will act without approval, but legal exposure for mistaken bookings, payments, or contractual commitments remains a thorny question. Organizations will want contractual indemnities, clear user consent models, and internal policies that define when an agent may accept terms or make commitments on behalf of an employee. These policies must be written with legal and procurement teams, not just IT.Operational recommendations: how to pilot Copilot Tasks safely
- Start small: run Tasks pilots with a controlled group and defined use cases (e.g., inbox triage, calendar digest). Evaluate for accuracy, privacy, and unexpected side effects.
- Limit connector scopes: where possible, grant the agent read‑only or scoped permissions until you’re confident in behavior. Use least‑privilege principles for tokens.
- Integrate with logging: forward Tasks activity to SIEM and retention systems to enable audit and investigation. Require that the vendor expose an audit API.
- Train users and set expectations: agents are powerful but fallible. Educate pilots about common failure modes, and require human sign‑off for financial or contractual steps.
- Monitor for prompt injection: treat web browsing and scraped content as untrusted input, and build templates that validate outputs before any irrevocable action.
Business model, availability, and what Microsoft still needs to clarify
Microsoft has positioned Copilot Tasks as a fundamental evolution of Copilot, but the company left several product questions open at launch:- Licensing and pricing: Will Tasks be part of existing Copilot tiers or require an add‑on SKU? This matters for budgeting and entitlement.
- Connector breadth: How many third‑party services will be supported at launch, and how easy will it be for partners to build vetted connectors? Without rich connectors, Tasks’ usefulness is constrained.
- Enterprise controls: The timing and granularity of tenant admin controls, audit exports, and eDiscovery features will determine whether regulated industries can adopt Tasks at scale. Microsoft signaled these as priorities but provided few specifics at preview.
What to watch next: signals that will determine success
- Availability of tenant‑level audit logs and exportable trails (non‑negotiable for many enterprises).
- Granular admin controls and permission scoping for connectors.
- Public security documentation and third‑party pen‑test results proving the sandbox isn’t porous.
- Pricing clarity and inclusion in Microsoft 365 or Copilot licensing tiers.
- Evidence that prompt injection and web adversarial cases are meaningfully mitigated in real usage.
Final analysis: a pragmatic path to agentic productivity
Copilot Tasks is a thoughtful, pragmatic response to a fast‑escalating industry problem: how to bring the productivity of agentic AI to mainstream users while reducing the worst security and governance risks of local agents. By placing compute in the cloud, enforcing consent gates, and emphasizing controlled connectors, Microsoft has designed an architecture that is immediately attractive to enterprises and cautious consumers. That advantage is real and will matter for regulated environments.However, the tradeoff is meaningful: without device access, Tasks can’t do everything a local agent can. Power users and developers who need deep system integration will keep tinkering with OpenClaw‑style frameworks, and security teams will continue to hunt for ways to govern those deployments. The launch also exposes a practical engineering challenge: turning high‑level demos into reliable, auditable, and scalable features requires excellent connector engineering, careful rights management, and complete transparency about logging and retention.
For IT teams, the sensible posture is not reflexive adoption or outright rejection, but controlled experimentation paired with strict governance. Demand auditability, insist on least‑privilege connectors, and require human‑in‑the‑loop confirmation for any financial or contractual action. For power users, understand the limitations of cloud sandboxes and weigh whether local agents justify their maintenance and risk overhead.
In short: Copilot Tasks doesn’t eliminate the agentic future — it shapes it. It offers a middle path that brings many of the productivity gains of autonomous agents to a wider audience while making the job of risk management tractable for organizations. Whether it becomes the dominant model will depend on Microsoft’s execution around enterprise controls, transparency, and connector breadth. If those pieces fall into place, Tasks could be the feature that turns agentic AI from an experimental developer curiosity into a mainstream workplace tool.
Conclusion
Copilot Tasks is a milestone: a major vendor taking agentic AI seriously while answering security critiques with architecture and process. It’s not a silver bullet — no agent is — but it is a measured, enterprise‑minded approach that shifts the conversation from whether autonomous agents are possible to how we operate them safely, transparently, and productively. The next months of previews and enterprise pilots will tell us whether Microsoft can deliver the missing governance pieces at scale, and whether the rest of the ecosystem adapts to a future where AIs not only converse, but do actual work for us.
Source: MakeUseOf Microsoft just announced its answer to OpenClaw, and it actually looks pretty great