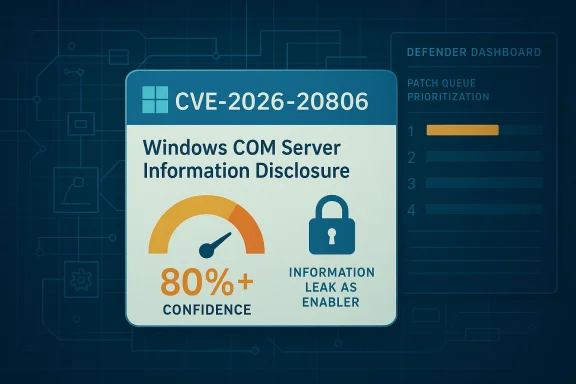
Microsoft’s CVE-2026-20806 entry is a good example of how metadata matters as much as headline severity. The advisory identifies the issue as a Windows COM Server Information Disclosure Vulnerability, but the key phrase in the description is the confidence metric: Microsoft is not just rating impact, it is signaling how certain it is that the flaw exists and how credible the technical details are. That distinction matters because defenders often have to decide whether to patch based on a partial disclosure, a vendor-confirmed bug, or a still-evolving technical theory.
Microsoft’s Security Update Guide has steadily become more than a list of CVEs and fixes. It now functions as a policy surface, an operational map, and in some cases a warning system for defenders trying to separate confirmed risks from speculative ones. The company’s own MSRC blog has explained that vulnerability descriptions are now paired with CVSS and structured language so administrators can better understand what the flaw is, how it behaves, and how much confidence Microsoft has in the underlying claim. That is the context for reading an entry like CVE-2026-20806: it is not just a name, but a confidence-bearing statement about a real weakness in the Windows platform.
The COM Server designation also matters. Component Object Model infrastructure is deeply embedded in Windows, and it is often used by applications, services, shell integrations, and management tooling that were never meant to be edge-facing security products but nonetheless sit in the center of enterprise operations. A weakness in COM server behavior can be especially sensitive because COM often mediates trust boundaries between user-mode components, services, and applications with different integrity levels. Even when the public technical details are sparse, the component name alone tells defenders that the issue may have broad reach inside normal Windows workflows.
Information disclosure vulnerabilities are sometimes underestimated because they do not immediately sound like ransomware, remote code execution, or complete system compromise. But a leak can expose memory addresses, object metadata, paths, tokens, or other internal state that helps an attacker defeat later protections. In other words, an info leak can be the bug that makes the next bug exploitable. That is why Microsoft and the broader security community treat these issues as meaningful even when the visible impact appears modest.
This is also part of a broader 2026 pattern. Windows advisories this year have shown that Microsoft continues to publish vulnerabilities with varying degrees of technical detail, and in several cases the vendor’s public wording itself is an important clue about exploitability, triage priority, and whether the issue is fully understood. That is precisely what the MSRC confidence construct is designed to communicate: not just that a flaw exists, but how confidently Microsoft can say so.
The strongest reading of CVE-2026-20806 is therefore operational, not sensational. This is a vendor-confirmed Windows information disclosure issue in COM Server infrastructure, and the confidence metric says Microsoft considers the underlying vulnerability sufficiently real to publish and classify. For defenders, that means the question is not whether to take it seriously; the question is how much attention to allocate before the public technical narrative becomes more complete.
In practice, the metric acts like a signal amplifier. When confidence is high, organizations can treat the flaw as a concrete engineering problem. When confidence is lower, teams may still track the issue, but they should be more cautious about overcommitting resources to unverified assumptions. That distinction matters especially in Windows security, where component names and vulnerability classes often arrive before full exploit narratives do.
At the same time, defenders should avoid the opposite mistake: assuming that limited detail means limited danger. Sparse disclosure is not the same thing as low risk. In many cases, it simply means the vendor has chosen not to publish the full exploit mechanics.
Information disclosure in COM is particularly interesting because COM often bridges trust zones. One component may be running at a lower privilege level while another runs with elevated rights or handles sensitive data. A leak across that boundary may not be catastrophic by itself, but it can provide the exact foothold needed for later abuse. That is why disclosure bugs in system components often show up in exploitation chains even when they are not the final payload delivery mechanism.
That is why enterprise defenders should treat COM-related info leaks as enablers, not just nuisances. Even if the CVE does not grant code execution, it may help an attacker get there.
This matters because vulnerability management teams often have to act before all details are public. They need to decide whether to patch immediately, stage validation first, or wait for more context from Microsoft and third-party researchers. In the case of a Windows platform issue with a confidence signal, the conservative answer is usually to prioritize analysis quickly and not assume the absence of a PoC equals the absence of risk.
This is why Microsoft’s confidence language should be treated as an operational cue. It tells defenders where the vendor has enough evidence to stand behind the advisory, which in turn tells teams where they should invest triage time.
Microsoft’s own vulnerability taxonomy has repeatedly shown that disclosure issues can be tied to kernel behavior, browser features, document processing, graphics subsystems, and service components. The lesson is consistent: the leak itself may not be the final objective, but it often makes exploitation easier, more reliable, or stealthier. That is why a Windows COM Server disclosure should not be read in isolation.
The broader point is that Microsoft’s current advisory style reflects a more mature understanding of this dynamic. By clearly identifying a vulnerability class and confidence level, the company is helping defenders see beyond the surface description. That is especially important when the public does not yet have a full exploit narrative.
Large environments often struggle with exactly this kind of advisory. A vulnerability with limited detail can create delays because teams want more certainty before they interrupt change windows. But the MSRC confidence metric is designed to reduce that hesitation. If Microsoft is confident enough to label the bug and publish it, defenders should be confident enough to inventory and stage fixes.
Enterprise defenders should also document why the issue was prioritized. That record is useful later if auditors ask why the organization moved fast on a vulnerability with limited technical detail. The answer, in this case, is simple: the vendor’s own confidence signal made the advisory actionable.
Consumers also tend to patch more slowly or inconsistently than managed fleets. That makes any public Windows vulnerability worth paying attention to, even if the raw class is not as dramatic as remote code execution. In practice, many consumer compromises begin with a local foothold, a malicious attachment, or a browser-delivered payload that does not need a final exploit to be dangerous.
For home users, the best defense remains straightforward. Keep Windows updated, avoid unsupported builds, and be cautious with untrusted software that might interact with COM components in unexpected ways. A security update that looks routine may be more important than it appears at first glance.
Consumers do not need to overanalyze every CVE, but they should recognize that Microsoft’s confidence-bearing advisories deserve quick patching, especially when they affect core Windows subsystems.
The difference is that info disclosure often acts as a force multiplier. It can make other flaws more exploitable and can expose the kind of internal detail that advanced attackers value most. In that sense, it is less flashy but sometimes more useful than a bug that simply crashes a process.
This is why defenders should not rate bugs only by immediate end-state. A clean, quiet leak inside a trusted component may be the precursor to something much worse. That makes patch sequencing a strategic decision, not a clerical one.
A final concern is uneven interpretation across teams. Security analysts may treat the advisory as meaningful, while application owners see only a vague Windows entry. Without clear internal messaging, that gap can slow response. The confidence metric is supposed to reduce that gap, but it only works if organizations understand what it means.
Enterprises should also watch for any related Windows advisories in the same release cycle that touch COM, RPC, shell, or interprocess communication. Vulnerabilities in those areas often cluster because they share common design patterns and trust boundaries. If additional bugs appear nearby, CVE-2026-20806 may end up looking less like an isolated leak and more like part of a broader hardening theme.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Background
Background
Microsoft’s Security Update Guide has steadily become more than a list of CVEs and fixes. It now functions as a policy surface, an operational map, and in some cases a warning system for defenders trying to separate confirmed risks from speculative ones. The company’s own MSRC blog has explained that vulnerability descriptions are now paired with CVSS and structured language so administrators can better understand what the flaw is, how it behaves, and how much confidence Microsoft has in the underlying claim. That is the context for reading an entry like CVE-2026-20806: it is not just a name, but a confidence-bearing statement about a real weakness in the Windows platform.The COM Server designation also matters. Component Object Model infrastructure is deeply embedded in Windows, and it is often used by applications, services, shell integrations, and management tooling that were never meant to be edge-facing security products but nonetheless sit in the center of enterprise operations. A weakness in COM server behavior can be especially sensitive because COM often mediates trust boundaries between user-mode components, services, and applications with different integrity levels. Even when the public technical details are sparse, the component name alone tells defenders that the issue may have broad reach inside normal Windows workflows.
Information disclosure vulnerabilities are sometimes underestimated because they do not immediately sound like ransomware, remote code execution, or complete system compromise. But a leak can expose memory addresses, object metadata, paths, tokens, or other internal state that helps an attacker defeat later protections. In other words, an info leak can be the bug that makes the next bug exploitable. That is why Microsoft and the broader security community treat these issues as meaningful even when the visible impact appears modest.
This is also part of a broader 2026 pattern. Windows advisories this year have shown that Microsoft continues to publish vulnerabilities with varying degrees of technical detail, and in several cases the vendor’s public wording itself is an important clue about exploitability, triage priority, and whether the issue is fully understood. That is precisely what the MSRC confidence construct is designed to communicate: not just that a flaw exists, but how confidently Microsoft can say so.
The strongest reading of CVE-2026-20806 is therefore operational, not sensational. This is a vendor-confirmed Windows information disclosure issue in COM Server infrastructure, and the confidence metric says Microsoft considers the underlying vulnerability sufficiently real to publish and classify. For defenders, that means the question is not whether to take it seriously; the question is how much attention to allocate before the public technical narrative becomes more complete.
What the Confidence Metric Really Means
Microsoft’s confidence language exists to help security teams interpret advisories that may have uneven detail quality. The measure reflects how certain Microsoft is about the existence of the vulnerability and how credible the available technical description is. That is useful because public vulnerability records are not all equally mature; some are based on confirmed vendor analysis, while others are initially disclosed with limited exploitation details or partial corroboration.In practice, the metric acts like a signal amplifier. When confidence is high, organizations can treat the flaw as a concrete engineering problem. When confidence is lower, teams may still track the issue, but they should be more cautious about overcommitting resources to unverified assumptions. That distinction matters especially in Windows security, where component names and vulnerability classes often arrive before full exploit narratives do.
Why this matters to defenders
A high-confidence information disclosure bug can justify faster patching than a vague report of “possible leakage.” It also gives security teams permission to move from speculation to planning. The advisory becomes part of the patch queue, not just the watch list.- It reduces uncertainty in prioritization.
- It supports more decisive patch scheduling.
- It helps SOC teams tune detection and threat hunting.
- It gives asset owners a firmer basis for change control.
- It improves communication between security and operations teams.
Confidence and attack planning
For would-be attackers, a high-confidence entry is useful because it tells them the vendor has likely validated the bug class and component. Even if the exact primitive is not public, the entry narrows the search space. That can lower the effort needed to reverse engineer likely code paths. It also can encourage researchers to look for chained attacks that turn one disclosure into a broader compromise.At the same time, defenders should avoid the opposite mistake: assuming that limited detail means limited danger. Sparse disclosure is not the same thing as low risk. In many cases, it simply means the vendor has chosen not to publish the full exploit mechanics.
Why COM Server Bugs Are Hard to Ignore
Windows COM infrastructure sits inside a lot of ordinary system behavior, which is what makes it dangerous when something goes wrong. COM is used for object activation, interprocess communication, shell extensions, administrative functions, and application integration. That makes it both powerful and difficult to isolate. A flaw in a COM server can have consequences that extend far beyond one application or one user session.Information disclosure in COM is particularly interesting because COM often bridges trust zones. One component may be running at a lower privilege level while another runs with elevated rights or handles sensitive data. A leak across that boundary may not be catastrophic by itself, but it can provide the exact foothold needed for later abuse. That is why disclosure bugs in system components often show up in exploitation chains even when they are not the final payload delivery mechanism.
Typical disclosure paths
The exact mechanism in CVE-2026-20806 has not been publicly detailed in the material available here, so caution is warranted. Still, COM-related leaks commonly involve one of a few patterns: memory left readable, metadata exposed through interface marshaling, object state not fully sanitized, or error handling that returns more internal information than it should. Those are educated possibilities, not confirmed facts.- Leaked pointers or addresses.
- Improperly exposed object metadata.
- Sanitization failures in marshaling or serialization.
- Error messages revealing internal state.
- Boundary crossing between lower and higher integrity contexts.
Enterprise exposure is higher than consumer exposure
For consumers, a COM information disclosure may mostly be a local privacy or hardening issue unless it is chained with another vulnerability. For enterprises, the stakes are much higher because COM-enabled applications often live alongside sensitive file shares, identity systems, admin tooling, and remote management workflows. An attacker with limited access may use a disclosure to map memory, understand process behavior, or identify privilege boundaries before moving laterally.That is why enterprise defenders should treat COM-related info leaks as enablers, not just nuisances. Even if the CVE does not grant code execution, it may help an attacker get there.
Reading the Advisory in Practical Terms
The most important practical takeaway from CVE-2026-20806 is that Microsoft’s Security Update Guide is signaling confidence, not merely possibility. The advisory naming convention says this is a Windows COM Server Information Disclosure Vulnerability, and the metadata framing says Microsoft believes the issue is real enough to publish, classify, and support operationally. That combination is stronger than a rumor and less complete than a deeply analyzed exploit writeup.This matters because vulnerability management teams often have to act before all details are public. They need to decide whether to patch immediately, stage validation first, or wait for more context from Microsoft and third-party researchers. In the case of a Windows platform issue with a confidence signal, the conservative answer is usually to prioritize analysis quickly and not assume the absence of a PoC equals the absence of risk.
How to interpret a sparse entry
When public detail is limited, the vendor entry itself becomes the primary source of truth. That means the component name, the vulnerability class, and the confidence language deserve attention. It is a mistake to read “information disclosure” as automatically low severity, especially in Windows where a leak can support exploit chaining.- Confirm which Windows builds are affected in your environment.
- Check whether the COM-related component is exposed on high-value endpoints.
- Review patch status and deployment rings.
- Look for related disclosure bugs or nearby privilege escalation issues.
- Prepare for the possibility that the technical story will expand later.
Why defenders care even before exploit details arrive
Security teams are not only defending against a single CVE; they are defending against the consequences of uncertainty. A confirmed info leak can alter threat modeling, especially if it weakens protections against memory randomization or reveals enough state to make a later exploit more reliable. That is the hidden value of disclosure bugs. They can convert a hard target into a softer one.This is why Microsoft’s confidence language should be treated as an operational cue. It tells defenders where the vendor has enough evidence to stand behind the advisory, which in turn tells teams where they should invest triage time.
Historical Pattern: Information Disclosure as a Chaining Primitive
Windows has a long history of information disclosure vulnerabilities being treated as second-order issues until attackers prove otherwise. That pattern is not unique to Microsoft, but the Windows ecosystem makes it especially visible because of how frequently disclosure bugs sit next to kernel, graphics, shell, or service-layer flaws. The public record over many years shows that leaks often become critical when paired with a second bug.Microsoft’s own vulnerability taxonomy has repeatedly shown that disclosure issues can be tied to kernel behavior, browser features, document processing, graphics subsystems, and service components. The lesson is consistent: the leak itself may not be the final objective, but it often makes exploitation easier, more reliable, or stealthier. That is why a Windows COM Server disclosure should not be read in isolation.
How disclosure affects exploit reliability
A modern exploit rarely depends on one defect alone. Attackers often need an address leak, a timing clue, or a structure hint before they can defeat protections such as ASLR or simply confirm they are interacting with the right object. If COM Server behavior leaks data across a trust boundary, it can give attackers a map of the terrain before they attempt the harder part of the attack.- It may reveal memory layout details.
- It can expose object identifiers or state.
- It may help bypass mitigations.
- It often improves exploit stability.
- It can reduce the number of guesses needed in chaining scenarios.
Historical parallels in Windows security
Windows security history is full of vulnerabilities that looked small at first but became strategically important once chained with another weakness. That does not mean every info leak turns into a major incident. It does mean that the category deserves respect. In large environments, attackers are patient; they are happy to use a low-noise disclosure bug as a reconnaissance step on the way to privilege escalation or persistence.The broader point is that Microsoft’s current advisory style reflects a more mature understanding of this dynamic. By clearly identifying a vulnerability class and confidence level, the company is helping defenders see beyond the surface description. That is especially important when the public does not yet have a full exploit narrative.
Enterprise Impact: Patch Priority, Exposure, and Governance
For enterprises, CVE-2026-20806 is primarily a governance problem before it is a technical one. The issue is less about whether a single workstation leaks sensitive state and more about whether the organization can rapidly identify where COM Server exposure exists and decide how quickly to remediate it. The confidence signal in Microsoft’s entry should push this issue toward the front of the queue even if the practical exploit path is not yet fully public.Large environments often struggle with exactly this kind of advisory. A vulnerability with limited detail can create delays because teams want more certainty before they interrupt change windows. But the MSRC confidence metric is designed to reduce that hesitation. If Microsoft is confident enough to label the bug and publish it, defenders should be confident enough to inventory and stage fixes.
What enterprise teams should do first
The immediate steps are familiar but important. Security and IT operations should identify affected Windows versions, determine whether the relevant COM components are broadly deployed, and assess whether any critical business applications depend on the vulnerable code path. That process should happen quickly, because info disclosure issues are easy to dismiss until they are chained with something else.- Inventory affected Windows endpoints and servers.
- Map COM-dependent business applications.
- Prioritize internet-exposed and highly privileged systems.
- Validate vendor update availability and deployment status.
- Check for related kernel, shell, or IPC hardening issues.
Governance implications
This kind of advisory also tests internal decision-making. If a security team treats all information disclosures as low severity, it will systematically underinvest in bugs that attackers frequently use as enablers. If it overreacts to every sparse advisory, it will waste change windows and erode trust with operations. The confidence metric is useful precisely because it helps balance those extremes.Enterprise defenders should also document why the issue was prioritized. That record is useful later if auditors ask why the organization moved fast on a vulnerability with limited technical detail. The answer, in this case, is simple: the vendor’s own confidence signal made the advisory actionable.
Consumer Impact: Lower Stakes, Still Real
Consumer systems usually face a narrower practical risk from an information disclosure bug than enterprise fleets do, especially when the issue is local and requires user context or a co-located attacker. But “lower stakes” is not “no stakes.” A COM Server disclosure on a personal PC can still expose memory or internal state, and in a worst-case chain it could contribute to a more complete compromise.Consumers also tend to patch more slowly or inconsistently than managed fleets. That makes any public Windows vulnerability worth paying attention to, even if the raw class is not as dramatic as remote code execution. In practice, many consumer compromises begin with a local foothold, a malicious attachment, or a browser-delivered payload that does not need a final exploit to be dangerous.
Why home users should care
A Windows info disclosure can help an attacker learn about the local system, harvest hints for follow-up exploitation, or reduce the randomness that protects memory-safe behavior. Most users will never notice the leak directly. That is part of the problem: the risk can be invisible until it is used in combination with another flaw.For home users, the best defense remains straightforward. Keep Windows updated, avoid unsupported builds, and be cautious with untrusted software that might interact with COM components in unexpected ways. A security update that looks routine may be more important than it appears at first glance.
The quiet nature of disclosure bugs
The challenge with information leaks is that they are often silent. They do not crash the machine, flash an alert, or trigger an obvious degradation in performance. That makes them easy to ignore. But quiet vulnerabilities are not harmless vulnerabilities. They can sit in the background until a broader exploit chain arrives.Consumers do not need to overanalyze every CVE, but they should recognize that Microsoft’s confidence-bearing advisories deserve quick patching, especially when they affect core Windows subsystems.
Comparison With Other Windows Vulnerability Types
CVE-2026-20806 fits into a category that is often treated differently from privilege escalation or code execution bugs, even though it can be strategically important. Microsoft publishes many Windows CVEs each month across memory corruption, elevation of privilege, denial of service, spoofing, and disclosure classes. Among those, information disclosure is frequently the one people postpone because it lacks an obvious “takeover” payload. That instinct is understandable but not always wise.The difference is that info disclosure often acts as a force multiplier. It can make other flaws more exploitable and can expose the kind of internal detail that advanced attackers value most. In that sense, it is less flashy but sometimes more useful than a bug that simply crashes a process.
Disclosure vs. escalation
A privilege escalation vulnerability changes what an attacker can do. A disclosure vulnerability changes what an attacker knows. Both matter, but they matter differently. In many exploitation chains, knowledge comes first. A leak can reveal enough about a process, object, or memory layout to make the escalation path reliable.This is why defenders should not rate bugs only by immediate end-state. A clean, quiet leak inside a trusted component may be the precursor to something much worse. That makes patch sequencing a strategic decision, not a clerical one.
How COM Server issues differ from shell or kernel bugs
COM bugs sit in an awkward middle ground. They are not always as dramatic as kernel flaws, but they are often more entangled with application behavior than simple library bugs. That can make them harder to reason about and harder to scope. When a vulnerability lives in COM infrastructure, it may touch multiple applications or services indirectly, which increases the odds of underestimating exposure.- Kernel bugs often draw immediate attention.
- Shell bugs often feel user-facing and obvious.
- COM bugs can be hidden inside application plumbing.
- Disclosure bugs are easy to dismiss until chained.
- Infrastructure components create broad operational impact.
Strengths and Opportunities
The good news is that Microsoft’s current advisory framework gives defenders more context than older bulletin-era disclosures ever did. The presence of a confidence metric, a component name, and a vulnerability class gives security teams a better basis for action even when technical details are incomplete. That improves prioritization, communication, and response quality.- Better triage from confidence-aware advisories.
- Faster prioritization for confirmed Windows issues.
- Improved communication between security and IT operations.
- Stronger patch governance around ambiguous disclosures.
- More accurate threat modeling for COM-related exposure.
- Earlier detection planning for chained exploit scenarios.
- Greater transparency in Microsoft’s vulnerability handling.
Risks and Concerns
The main risk is underreaction. Because CVE-2026-20806 is an information disclosure issue rather than a full remote compromise, many teams may be tempted to delay action. That would be a mistake if the bug can be chained with other Windows weaknesses or used to weaken exploit mitigations. Low drama does not mean low importance.- Patch delay due to perceived low severity.
- Underestimation of leak-as-enabler scenarios.
- Compatibility caution slowing remediation.
- Incomplete asset inventories hiding exposure.
- Misreading the confidence metric as merely informational.
- Chained exploitation if attackers pair it with another flaw.
- Silent compromise support through leaked internal state.
A final concern is uneven interpretation across teams. Security analysts may treat the advisory as meaningful, while application owners see only a vague Windows entry. Without clear internal messaging, that gap can slow response. The confidence metric is supposed to reduce that gap, but it only works if organizations understand what it means.
Looking Ahead
The most important next step is likely to be either more detailed Microsoft guidance or corroboration from independent researchers that clarifies what the COM Server leak actually exposes. If technical specifics arrive later, they will matter for understanding whether the issue is primarily a local privacy concern, a mitigation bypass, or a stronger exploit primitive. Until then, the best posture is to treat the advisory as real, confirmed, and worth prioritizing.Enterprises should also watch for any related Windows advisories in the same release cycle that touch COM, RPC, shell, or interprocess communication. Vulnerabilities in those areas often cluster because they share common design patterns and trust boundaries. If additional bugs appear nearby, CVE-2026-20806 may end up looking less like an isolated leak and more like part of a broader hardening theme.
What to watch next
- Microsoft clarification on affected Windows builds.
- Any third-party technical analysis of the COM Server leak.
- Follow-on advisories involving IPC or shell components.
- Enterprise patch notes that mention compatibility impact.
- Hunt guidance or mitigation recommendations from Microsoft.
Source: MSRC Security Update Guide - Microsoft Security Response Center
Last edited: