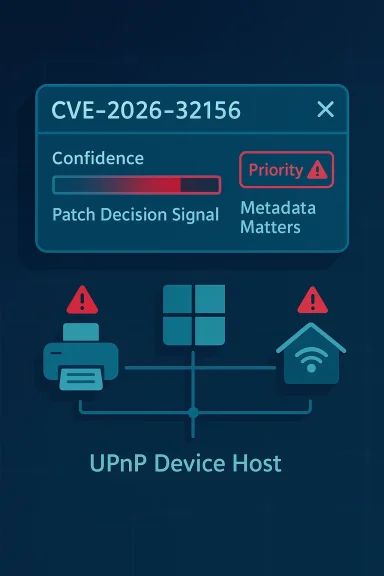
Microsoft’s CVE-2026-32156 entry is another reminder that metadata matters in Windows security, especially when Microsoft is talking about a Windows UPnP Device Host Remote Code Execution Vulnerability and attaching a confidence signal to the advisory. In Microsoft’s own framework, that metric is meant to measure how certain the company is that the vulnerability exists and how credible the technical details are, which makes it more than just an administrative label. It changes how defenders should interpret urgency, even when the public page is sparse on low-level exploit mechanics.
The UPnP Device Host is one of those Windows components that sits in the background until it suddenly becomes important. It helps Windows discover and interact with networked devices that expose Universal Plug and Play services, which means it occupies an awkward but significant place between convenience and exposure. When a component like that is assigned a remote code execution issue, the first question is not just “what broke?” but “how much can we trust what Microsoft is telling us about the bug today?”
Microsoft’s confidence metric is designed to answer that second question. The company has used similar framing across prior advisories, where the public label tells you the class of flaw and the confidence language tells you whether the issue is confirmed, strongly supported, or still partly inferential. That distinction matters because defenders are often forced to make patching decisions before every exploit primitive is public. In this case, the labeling strongly suggests Microsoft believes the issue is real enough to act on, even if it has not published a full exploit narrative.
There is also a broader historical pattern here. Windows network discovery and device-management features have long been security-sensitive because they combine broad functionality, system-level privileges, and network exposure. Microsoft has repeatedly had to harden services such as RDP, DNS, WSD, SMB, and other discovery-oriented stacks after they were found to be remotely abusable. The result is a familiar modern Windows security truth: the parts of the operating system that make it easier for devices to find each other can also become attractive targets for attackers.
That tension is exactly why a CVE like this deserves attention beyond its immediate advisory line. Even if the public details remain thin, the combination of remote code execution, a core Windows service, and a Microsoft confidence indicator typically means the vulnerability belongs on the same operational shortlist as other high-priority Windows fixes. For enterprises, that often translates to accelerated validation, targeted rollout, and a willingness to make patch sequencing decisions before all the technical breadcrumbs are available.
In practical terms, the confidence metric helps separate three categories of advisories. Some are fully confirmed with clear mechanics. Others are acknowledged, but the technical picture is still incomplete. A third category is more speculative and may be based on partial analysis, research leads, or internal validation rather than a fully public proof path. The metric is Microsoft’s way of telling defenders where on that continuum a CVE sits.
In other words, the confidence metric becomes a decision accelerator. It tells administrators whether they are dealing with a confirmed bug, a suspected issue, or something in between. That helps when patch windows are tight and resources are limited.
Microsoft’s wording in the broader MSRC ecosystem has historically served a similar purpose: to distinguish between “we know this exists” and “we think this is likely.” When the vendor is explicit about confidence, it is usually a sign that the entry should be treated as actionable, not theoretical. That is exactly the kind of nuance that matters for large environments.
The UPnP Device Host service is part of Windows’ internal machinery for handling these interactions. It is not the kind of feature most users think about daily, but it can matter in homes, small offices, and enterprises where printers, media devices, gateways, or IoT-style devices are discovered over the network. Components like this often end up in the “quietly ubiquitous” category, which is precisely why they are security-sensitive.
A remote code execution flaw in such a component is particularly worrying because it can potentially be triggered from the network without requiring a user to open a file or launch an app. That does not mean every UPnP issue is wormable or internet-facing, but it does mean defenders should think carefully about where the service is enabled and how reachable it is.
Microsoft has a long history of patching adjacent Windows services that interact with remote or semi-trusted inputs. The broader lesson is consistent: system plumbing is attack surface. When the plumbing speaks to the network, the risk rises sharply.
That is why the RCE label matters even when the public advisory is light on details. A remote code execution issue in a Windows service can, depending on context, lead to lateral movement, persistence, credential theft, or broader enterprise compromise. The exact blast radius depends on whether the service is exposed locally, on a LAN, or beyond the firewall, but the strategic implication is the same: this is not a cosmetic patch.
This is why patch urgency often rises when the vulnerable component is part of the operating system itself. A flaw in a Windows service is harder to contain than a flaw in a third-party app, because the service may be present across a standardized fleet and integrated into baseline images. The more widely deployed the component, the more costly delay becomes.
Microsoft’s previous RCE advisories show the same pattern. When the company believes a networking or parsing bug can be turned into code execution, it usually wants customers to prioritize deployment quickly, especially if the component is reachable from commonly used network paths. That context should guide how CVE-2026-32156 is read.
This pattern is familiar from earlier Windows advisories. Microsoft has repeatedly used concise CVE pages to notify defenders while withholding exploit mechanics that could help attackers. In many cases, the company later expands the guidance once more is known, but the first public version is intentionally brief. That means defenders must learn to read between the lines without over-reading them.
That is why the right operational response is not to wait for a technical explainer before acting. It is to treat the advisory as a credible vendor-confirmed issue and move into validation, inventory, and patch planning. The absence of exploit notes does not reduce the significance of a Windows RCE in a service like UPnP Device Host.
If anything, the lack of detail can increase urgency because defenders have less time to reason about exploit complexity. When Microsoft is confident enough to publish a CVE and label it as RCE, the conservative assumption is that the issue matters until proven otherwise. In Windows operations, assuming benignity is often the more expensive mistake.
That history matters because it shapes how experienced defenders interpret new advisories. A component like UPnP Device Host sits in a family of features that are intended to make life easier for users, peripherals, and device ecosystems. But the more data a system consumes from the network, the more chances there are for an attacker to weaponize malformed packets, object graphs, metadata, or parser edge cases.
For this reason, defenders should not be surprised that a service tied to device discovery has surfaced as a vulnerability class worthy of attention. It fits the long-running Windows pattern where convenience features eventually require hardening. Microsoft’s own update history shows this dynamic again and again.
The second lesson is that public confidence signals have become increasingly important because the security ecosystem moves faster than disclosure details do. A modern enterprise cannot afford to treat “we do not know everything yet” as equivalent to “we can ignore it.” That is especially true when the vendor already says the flaw exists and is meaningful enough to fix.
That can be especially relevant in environments with rich device ecosystems. Home networks with smart TVs, printers, media boxes, or consumer IoT gear can provide more opportunities for discovery traffic. In enterprise networks, the exposure may depend on which Windows features are enabled by policy, image baseline, or application dependency.
The third task is contextual risk evaluation. If the service is running on servers, workstations, or shared systems that are exposed to untrusted networks, the urgency rises. If the environment has flat network segments or heavy east-west traffic, the chance of internal exploitation may also be higher.
A mature response does not assume that a single CVE is isolated. It asks whether this vulnerability could be chained with privilege escalation, credential theft, or lateral movement. In many modern intrusions, the first foothold is less important than the speed with which attackers can convert that foothold into meaningful control.
A vulnerability can be high severity and low confidence if the technical picture is still evolving. It can also be moderate severity but high confidence if the bug is well understood but limited in scope. The confidence signal is therefore a useful realism check, especially for teams that are trying to separate actionable advisories from speculative leads.
That is especially important in Windows environments where many advisories land at once. The security team may be balancing browser fixes, kernel issues, authentication problems, and application-layer patches. Confidence can become a tie-breaker when several vulnerabilities look similar on paper but differ in how sure Microsoft is about their reality.
This is why security teams should read Microsoft advisories as layered information. The label says what kind of bug it is. The severity says how bad it could be. The confidence metric says how certain Microsoft is that the bug exists and is understood well enough to justify immediate action. That three-part reading is more accurate than treating the CVE number as a standalone alarm.
Another strength is the practical applicability of the guidance. Teams can begin hardening and patching without waiting for a public exploit proof. That shortens the window during which a vulnerability exists in a kind of security limbo, visible enough to worry about but not yet well enough explained to prioritize confidently.
A second concern is the uncertainty gap. When public technical details are sparse, defenders may underestimate the issue, while attackers may independently discover enough to weaponize it. That asymmetry is one reason Microsoft’s confidence metric matters so much: it tells defenders not to mistake disclosure restraint for unreality.
Another thing to watch is whether this CVE is part of a broader cluster of Windows service hardening in the same update cycle. Microsoft often fixes several related bugs across discovery, privilege, and service-hosting components in the same month. If that pattern holds, CVE-2026-32156 may be one piece of a larger operational hardening story rather than an isolated curiosity.
The larger lesson is that modern Windows defense increasingly depends on reading the metadata as carefully as the bug class. When Microsoft says it is confident a vulnerability exists, that is not bureaucratic color; it is a warning label. And in a service as network-adjacent as UPnP Device Host, that warning should be taken seriously.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Overview
Overview
The UPnP Device Host is one of those Windows components that sits in the background until it suddenly becomes important. It helps Windows discover and interact with networked devices that expose Universal Plug and Play services, which means it occupies an awkward but significant place between convenience and exposure. When a component like that is assigned a remote code execution issue, the first question is not just “what broke?” but “how much can we trust what Microsoft is telling us about the bug today?”Microsoft’s confidence metric is designed to answer that second question. The company has used similar framing across prior advisories, where the public label tells you the class of flaw and the confidence language tells you whether the issue is confirmed, strongly supported, or still partly inferential. That distinction matters because defenders are often forced to make patching decisions before every exploit primitive is public. In this case, the labeling strongly suggests Microsoft believes the issue is real enough to act on, even if it has not published a full exploit narrative.
There is also a broader historical pattern here. Windows network discovery and device-management features have long been security-sensitive because they combine broad functionality, system-level privileges, and network exposure. Microsoft has repeatedly had to harden services such as RDP, DNS, WSD, SMB, and other discovery-oriented stacks after they were found to be remotely abusable. The result is a familiar modern Windows security truth: the parts of the operating system that make it easier for devices to find each other can also become attractive targets for attackers.
That tension is exactly why a CVE like this deserves attention beyond its immediate advisory line. Even if the public details remain thin, the combination of remote code execution, a core Windows service, and a Microsoft confidence indicator typically means the vulnerability belongs on the same operational shortlist as other high-priority Windows fixes. For enterprises, that often translates to accelerated validation, targeted rollout, and a willingness to make patch sequencing decisions before all the technical breadcrumbs are available.
What the Microsoft confidence metric actually signals
The most important thing to understand is that this is not a score of exploitability in the classic sense. It is a signal about confidence: how sure Microsoft is that the vulnerability exists and how credible the available technical detail is. That is different from saying the flaw is already weaponized, widely exploited, or easy to reproduce.In practical terms, the confidence metric helps separate three categories of advisories. Some are fully confirmed with clear mechanics. Others are acknowledged, but the technical picture is still incomplete. A third category is more speculative and may be based on partial analysis, research leads, or internal validation rather than a fully public proof path. The metric is Microsoft’s way of telling defenders where on that continuum a CVE sits.
Why defenders should care
A high-confidence advisory means security teams can treat the issue as operationally real, not hypothetical. That is especially relevant when the affected surface is a Windows service that may be present on many systems by default. It also affects triage, because patching decisions can be justified on confidence alone even before full exploit writeups arrive.In other words, the confidence metric becomes a decision accelerator. It tells administrators whether they are dealing with a confirmed bug, a suspected issue, or something in between. That helps when patch windows are tight and resources are limited.
Microsoft’s wording in the broader MSRC ecosystem has historically served a similar purpose: to distinguish between “we know this exists” and “we think this is likely.” When the vendor is explicit about confidence, it is usually a sign that the entry should be treated as actionable, not theoretical. That is exactly the kind of nuance that matters for large environments.
- Confirmed existence matters as much as severity.
- Sparse technical detail does not automatically mean low risk.
- Vendor confidence often outweighs speculation from third parties.
- Patch priority should reflect both impact and certainty.
- Attackers benefit when defenders wait for perfect clarity.
Why UPnP Device Host remains a security-relevant Windows component
UPnP is designed to make device discovery and service interaction easier. That convenience has always been a double-edged sword because discovery protocols, by nature, widen the number of entities a system will talk to and the number of messages it will parse. Any parsing bug in that chain can quickly become a remote attack path.The UPnP Device Host service is part of Windows’ internal machinery for handling these interactions. It is not the kind of feature most users think about daily, but it can matter in homes, small offices, and enterprises where printers, media devices, gateways, or IoT-style devices are discovered over the network. Components like this often end up in the “quietly ubiquitous” category, which is precisely why they are security-sensitive.
Discovery features and attack surface
Discovery services have a known pattern: they accept network input, process device metadata, and translate that into local system behavior. That workflow is useful, but it creates a parser-rich, protocol-heavy environment where memory corruption, logic bugs, or trust boundary failures can become serious.A remote code execution flaw in such a component is particularly worrying because it can potentially be triggered from the network without requiring a user to open a file or launch an app. That does not mean every UPnP issue is wormable or internet-facing, but it does mean defenders should think carefully about where the service is enabled and how reachable it is.
Microsoft has a long history of patching adjacent Windows services that interact with remote or semi-trusted inputs. The broader lesson is consistent: system plumbing is attack surface. When the plumbing speaks to the network, the risk rises sharply.
- Discovery protocols tend to be parser-heavy.
- Parser-heavy services are more prone to memory safety bugs.
- Network exposure can make a flaw remotely triggerable.
- Background services often run with elevated privileges.
- Ubiquity makes even obscure bugs enterprise-relevant.
How remote code execution changes the calculus
A remote code execution vulnerability is more serious than many other classes because it can cross the boundary from data processing into arbitrary attacker control. If the attacker can send crafted network traffic and cause code to run, then the system is no longer merely unstable or leaking information; it is potentially fully compromised.That is why the RCE label matters even when the public advisory is light on details. A remote code execution issue in a Windows service can, depending on context, lead to lateral movement, persistence, credential theft, or broader enterprise compromise. The exact blast radius depends on whether the service is exposed locally, on a LAN, or beyond the firewall, but the strategic implication is the same: this is not a cosmetic patch.
The enterprise impact is different from the consumer impact
For home users, the most likely risk is device exposure on a local network and opportunistic exploitation if the environment contains risky or unknown devices. For enterprises, the concern is much wider. A vulnerable service on many endpoints creates a patch-management problem, and if the flaw is reachable from a business network, the issue can become a pivot point for internal attackers or malware already inside the perimeter.This is why patch urgency often rises when the vulnerable component is part of the operating system itself. A flaw in a Windows service is harder to contain than a flaw in a third-party app, because the service may be present across a standardized fleet and integrated into baseline images. The more widely deployed the component, the more costly delay becomes.
Microsoft’s previous RCE advisories show the same pattern. When the company believes a networking or parsing bug can be turned into code execution, it usually wants customers to prioritize deployment quickly, especially if the component is reachable from commonly used network paths. That context should guide how CVE-2026-32156 is read.
- Network-triggerable flaws are inherently more dangerous.
- Service-level compromise can affect many machines at once.
- Enterprise fleets make patch latency more costly.
- Local attackers may still use the bug as a stepping stone.
- Consumer systems can be exposed by home networks and devices.
What Microsoft’s disclosure style suggests
Microsoft’s security advisories often reveal more through framing than through raw technical depth. When the company identifies a specific component and pairs it with a clear vulnerability class, it is signaling that the issue is sufficiently understood for remediation, even if the public description stays high level. That is especially true when the entry appears in the Security Update Guide rather than in a research blog post.This pattern is familiar from earlier Windows advisories. Microsoft has repeatedly used concise CVE pages to notify defenders while withholding exploit mechanics that could help attackers. In many cases, the company later expands the guidance once more is known, but the first public version is intentionally brief. That means defenders must learn to read between the lines without over-reading them.
Why brevity is not the same as uncertainty
A sparse advisory is not necessarily an uncertain one. It can simply reflect Microsoft’s preference to minimize detail until patching is available and the disclosure posture is mature. The confidence metric is the clue that helps distinguish those cases from advisory entries that are still being validated internally.That is why the right operational response is not to wait for a technical explainer before acting. It is to treat the advisory as a credible vendor-confirmed issue and move into validation, inventory, and patch planning. The absence of exploit notes does not reduce the significance of a Windows RCE in a service like UPnP Device Host.
If anything, the lack of detail can increase urgency because defenders have less time to reason about exploit complexity. When Microsoft is confident enough to publish a CVE and label it as RCE, the conservative assumption is that the issue matters until proven otherwise. In Windows operations, assuming benignity is often the more expensive mistake.
- Brief advisories can still represent serious bugs.
- Public detail scarcity is often a disclosure choice.
- Vendor confidence helps bridge the gap.
- Patch planning should start before full analysis.
- Waiting for exploit proof can be a costly strategy.
Historical context: why this looks familiar
Windows has seen many security issues in components that manage discovery, messaging, and networked services. The pattern is not new. MSRC has repeatedly had to explain that a vulnerable Windows component could permit remote code execution through malformed inputs or crafted network traffic, even when the underlying service was designed for benign interoperability.That history matters because it shapes how experienced defenders interpret new advisories. A component like UPnP Device Host sits in a family of features that are intended to make life easier for users, peripherals, and device ecosystems. But the more data a system consumes from the network, the more chances there are for an attacker to weaponize malformed packets, object graphs, metadata, or parser edge cases.
The lesson from older Windows vulnerabilities
Older Microsoft advisories often showed that remote code execution could emerge from unexpected places: networking stacks, media parsers, device protocols, font handling, and shell integration. The root cause varies, but the security lesson is constant: complexity creates attack surface, and attack surface creates patch debt.For this reason, defenders should not be surprised that a service tied to device discovery has surfaced as a vulnerability class worthy of attention. It fits the long-running Windows pattern where convenience features eventually require hardening. Microsoft’s own update history shows this dynamic again and again.
The second lesson is that public confidence signals have become increasingly important because the security ecosystem moves faster than disclosure details do. A modern enterprise cannot afford to treat “we do not know everything yet” as equivalent to “we can ignore it.” That is especially true when the vendor already says the flaw exists and is meaningful enough to fix.
- Device discovery has always been security-sensitive.
- Complex parsers are a recurring source of RCE.
- Network services widen the blast radius.
- Windows plumbing often becomes a target later than expected.
- Confidence signals now shape remediation priority.
Likely exploitation scenarios and operational exposure
Without public exploit details, the safest analysis is to focus on plausible operational scenarios rather than specific attack recipes. A Windows UPnP Device Host RCE would most likely involve crafted network interaction with the service or with components that delegate to it. The precise trigger is unknown from the public record, but the exposure model is familiar: a vulnerable parser or state machine processes attacker-controlled input and reaches unsafe behavior.That can be especially relevant in environments with rich device ecosystems. Home networks with smart TVs, printers, media boxes, or consumer IoT gear can provide more opportunities for discovery traffic. In enterprise networks, the exposure may depend on which Windows features are enabled by policy, image baseline, or application dependency.
Where defenders should look first
The first task is inventory. Security teams need to know which systems have the relevant Windows feature set, whether the service is enabled, and whether internal segmentation limits who can talk to it. The second task is patch prioritization, especially if the advisory is rated critical or if the confidence signal is strong.The third task is contextual risk evaluation. If the service is running on servers, workstations, or shared systems that are exposed to untrusted networks, the urgency rises. If the environment has flat network segments or heavy east-west traffic, the chance of internal exploitation may also be higher.
A mature response does not assume that a single CVE is isolated. It asks whether this vulnerability could be chained with privilege escalation, credential theft, or lateral movement. In many modern intrusions, the first foothold is less important than the speed with which attackers can convert that foothold into meaningful control.
- Inventory affected systems before rollout.
- Check service exposure across network segments.
- Prioritize patching for broadly deployed endpoints.
- Assess lateral-movement risk inside flat networks.
- Look for chained exploit potential in enterprise environments.
Microsoft’s confidence metric versus CVSS and severity
It is easy to confuse Microsoft’s confidence language with severity scoring, but they are not the same thing. CVSS tries to quantify impact and exploitability. Microsoft’s confidence metric tells you how much faith the vendor has in the existence and quality of the underlying vulnerability information. That means the two signals complement one another rather than overlap fully.A vulnerability can be high severity and low confidence if the technical picture is still evolving. It can also be moderate severity but high confidence if the bug is well understood but limited in scope. The confidence signal is therefore a useful realism check, especially for teams that are trying to separate actionable advisories from speculative leads.
Why this distinction matters in patch queues
Patch queues are always constrained. Administrators have limited time, limited maintenance windows, and limited tolerance for breaking changes. A confidence signal helps resolve uncertainty about whether a patch should move up the queue now or wait for more evidence. In effect, it reduces the risk of underreacting to a real flaw.That is especially important in Windows environments where many advisories land at once. The security team may be balancing browser fixes, kernel issues, authentication problems, and application-layer patches. Confidence can become a tie-breaker when several vulnerabilities look similar on paper but differ in how sure Microsoft is about their reality.
This is why security teams should read Microsoft advisories as layered information. The label says what kind of bug it is. The severity says how bad it could be. The confidence metric says how certain Microsoft is that the bug exists and is understood well enough to justify immediate action. That three-part reading is more accurate than treating the CVE number as a standalone alarm.
- Severity and confidence answer different questions.
- High confidence increases operational trust.
- Low confidence does not equal low danger.
- Patch queues benefit from this distinction.
- Enterprise triage improves when signals are read together.
Strengths and Opportunities
The most encouraging aspect of Microsoft’s handling is that it gives defenders a clear operational signal even when the technical detail is limited. That is useful in a world where patch teams need to act before attackers finish their own reverse engineering. It also shows that Microsoft’s disclosure framework has matured beyond simple severity labels.Another strength is the practical applicability of the guidance. Teams can begin hardening and patching without waiting for a public exploit proof. That shortens the window during which a vulnerability exists in a kind of security limbo, visible enough to worry about but not yet well enough explained to prioritize confidently.
- Confidence labeling improves triage.
- Vendor confirmation reduces ambiguity.
- Patch planning can start immediately.
- Network service exposure can be audited quickly.
- Fleet management benefits from decisive guidance.
- Security operations gain a clearer prioritization signal.
- Disclosure discipline helps avoid needless exploit detail.
Risks and Concerns
The biggest concern is that a well-placed Windows service bug can become a high-value foothold inside managed environments. Even if the flaw is not directly internet-exposed in every deployment, local network exposure and internal pivoting can still make it serious. If attackers can reach the service from inside the perimeter, the practical risk can be far greater than the casual reading of “device host” suggests.A second concern is the uncertainty gap. When public technical details are sparse, defenders may underestimate the issue, while attackers may independently discover enough to weaponize it. That asymmetry is one reason Microsoft’s confidence metric matters so much: it tells defenders not to mistake disclosure restraint for unreality.
- Internal network exposure can still be dangerous.
- Attackers may exploit the uncertainty gap faster than defenders expect.
- Flat network design increases lateral risk.
- Silent services are easy to overlook in audits.
- Patch fatigue may delay remediation.
- Sparse details can cause dangerous complacency.
- Dependency chains may make rollback difficult if patching is rushed.
Looking Ahead
The next question is whether Microsoft expands the advisory with more technical details, and whether third-party researchers corroborate the issue with independent analysis. That matters because confidence becomes even more useful when it is paired with a clearer picture of attack surface, exploitability, and affected configurations. If more detail emerges, defenders should revisit any assumptions they made during first-round triage.Another thing to watch is whether this CVE is part of a broader cluster of Windows service hardening in the same update cycle. Microsoft often fixes several related bugs across discovery, privilege, and service-hosting components in the same month. If that pattern holds, CVE-2026-32156 may be one piece of a larger operational hardening story rather than an isolated curiosity.
What to watch next
- A possible Microsoft advisory update with more technical detail.
- Independent confirmation from security researchers or vulnerability databases.
- Any evidence of exploitation in the wild.
- Patch mapping differences across Windows editions and builds.
- Whether related Windows discovery services are updated in parallel.
The larger lesson is that modern Windows defense increasingly depends on reading the metadata as carefully as the bug class. When Microsoft says it is confident a vulnerability exists, that is not bureaucratic color; it is a warning label. And in a service as network-adjacent as UPnP Device Host, that warning should be taken seriously.
Source: MSRC Security Update Guide - Microsoft Security Response Center
Last edited: