CVE-2026-31429 is a good example of a kernel security issue that looks small on paper but matters because it sits in a hot, widely exercised networking path. The bug is in Linux’s skb head free logic, where a KFENCE-specific allocation detail could cause the kernel to return memory to the wrong slab cache. The fix is deceptively simple: always use the generic
At the center of th_HEAD_CACHE_SIZE
KFENCE changes that assumption in a subts active,
That is where the problem becomes security-relevant. The kernobject back to
The Linux kernel community has long taken a cautious view of CVE assignment. Its oexplains that issues are typically tracked once a fix exists and is tied to stable-tree work, rather than when an abstract bug report first appears. That process is meant to create a concrete patch trail and reduce ambiguity for downstream consumers. In that context, CVE-2026-31429 fits the kernel’s standard model very well: a narrowly scoped bug, a visible fix, and a backport-friendly change that can travel through stable trees.
Most allocator bugs are easy to describe in broad strokes but difficult to reproduce precisely. This one is interesting because the vulnerable condition depends on a combination of small details: a specific head size, KFENCE being enabled, and the skb free path making an allocator-origin decision based on size metadata. That makes the issue feel less dramatic than a classic memory corruption flaw, but not less important.
The key insight is that kernel safevoiding cleverness in the teardown path. If the free side tries too hard to infer provenance, it can end up making the wrong allocator decision under instrumentation or debugging configurations. The safest strategy is often the least specialized one, because a generic free path is less likely to be misled by allocator behavior that changes under sanitizers. That is the core lesson in this CVE.
The dangerous part is not the allocation itself but the free-time classificatg the skb shared-info overhead, the computed end offset can line up with
That kind of bug is especially frustrating in hardened environments because it may only surface whng to be more observably safe. KFENCE exists to catch memory safety problems, but in this case it also altered the semantics in a way that exposed a latent assumption in the skb teardown code. The bug is therefore as much about the fragility of allocator heuristics as it is about skb handling itself.
This is a classic kernel hardening lesson. A fast path may depend on shortcuts for performance, but teardown should usually be the place whe correctness over guesswork. The moment a free routine starts doing allocator detective work, it creates a risk that a debugging mode, a sanitizer, or a rare size alignment will invalidate the logic. That is exactly what happened here.
In this CVE, KFENCE’s behavior is the trigger that turns a harmless-looking size match into a cache misclassification. Because
It is also a reminder that debug and production semantics are not always identical in kernel space. A path tinary allocator assumptions may not be safe under memory instrumentation, and vice versa. That does not mean KFENCE is at fault; it means the code under test did not fully respect allocator abstraction boundaries.
The practical takeaway is that “works in normal testing“correct under hardened runtime conditions.” That distinction matters for long-lived kernels, enterprise builds, and vendor configurations that enable memory debugging selectively. A fix that is robust across allocator variants is far more valuable than one that only behaves correctly in the common case.
That design chonel maintainers usually prefer fixes that reduce special-case behavior in teardown paths, especially if the bug can be eliminated by using a more generic primitive. This approach lowers the chance that future allocator behavior changes, sanitizer modes, or architecture-specific bucket sizes will recreate the same bug in a new form. In short, the patch does not just fix one bug; it also removes an entire class of assumptions.
The result is cleaner code and a morth.
The broader security benefit is reduced brittleness. If a free path is deterministic and allocator-agnostic, it is much harder for a debug mode to provoke a misfree. That means fewer latent bugs, fewer hard-to-diagnose slab warnings, and less risk that a niche configuration turns into an outage trigger.
The networking stack is a particularly sensitive place for this kind of bug because it is both performance-critical and widely exercised. Even a condition that sounds niche can matter if it sits in a path used by packet processing, testing tools, or subsystem-integrated infrastructure like BPF-driven test harnesses. The CVE text explicitly mentions
That has an important operational implication. Bugs that manifest in testing cll be security issues, because those same configurations are often used in CI, lab clusters, and pre-production environments where kernel stability matters. If a bug can break allocator invariants in a testing mode, it can become a blocker for validation pipelines long before it becomes a production incident.
For enterprises, that means the right k whether an attacker can weaponize the bug in a textbook way. The right question is whether the affected kernel build can be made to misbehave under realistic workloads or test paths, and whether the fix is present in the exact vendor kernel in use. That is the practical way to treat a bug in this class.
The systems most likely to care are infrastructure hosts, test environments, and any fleet that uses KFENCE or comparable hardening features. Those environments are often the ones most likely to surface latent memory-management assumptions, because they are designed to catch exactly these categories of bug. That makes this CVE especially relevant to kernel engineers, CI maintainers, and platfte bespoke kernels before shipping them.
It also matters that Microsoft has included the vulnerability in its Security Update Guide ecosystem, which helps surface Linux kernel issues alongside Windows and Azure-related security data for mixed estates. Microsoft’s Security Update Guide is intended to centralize security risk information, and the company has expanded that model to include broader vulnerability disclosures. For enterprise defenders, that creates a single place to track a Linux kernel issue that might otherwise get lost in a Linux-only workflow.
They should also check whether any packet-processing test harnesses, BPF test environments, or integration suites allocate skb heads at sizes that can intersect with the small-head cache boundary. That may sound academic, bthe kinds of workloads that uncover allocator edge cases before they become production incidents.
The picture is different for embedded devices, routers, appliances, and vendor-supported Linux builds that live for years without broad platform refreshes. In those environments, allocator behavior and backported kernel code can diverge from upstream expectations in subtle ways. A bug that seems obscure in a desktop context can be much more relevant when it lives inside an appliance image that ships with a long support tail.
That is why firmware maintenance still matters. Vendors frequently bundle these fixes into routine updates, and the user may never know the issue existed until a stability problem appears or an audit catches the vulnerable kernel build. Small kernel bugs are ofter longest in embedded ecosystems because they do not look urgent until they become operationally inconvenient.
A stable-looking router or gateway can still carry a kernel bug for months or years if the vendor’s update cadence is slow. That is why embedded arate mention: the risk is not about active exploitation on a workstation, but about a long-lived kernel image retaining a known allocator flaw.
It also demonstrates a healthy stable-process outcome. The bug was identified, a commit landed, and the issue was tracked through the usual kernel security pipeline, which is exactly how a mature open-source project should handle a narrow but real memory-management flaw. The public CVE record gives downstream teams a useful handle for verification and patch management.
The broader opportunity is to treat this as another reminder that debug configurations matter. Teams that build and test kernels should continue to use KFENCE, KASAN, and related tools, because they expose the assumptions that can hide in hot-path code. Finding bugs in test builds is not a nuisance; it is how you prevent them from becoming production incidents.
A second concern is patch lag. Even after the fix is public, vendor kernels and long-term-support branches may take time to absorb it, and that delay can leave production fleets exposed longer than administrators expect. This is one of the recurring headaches of Linux security: the CVE exists before the actual running systems are uniformly protected.
There is also a ecause the issue appears only under particular size and allocation conditions, organizations may never see an obvious symptom until they happen to hit the edge case. That makes it easy for teams to assume the problem is theoretical when it is really just dormant.
It is also worth watching whether the bug prompts broader review of skb free logic and other code paths that try to infer allocator provenance from object size. That kind of audit is one of the useful side effects of a CVE like this: one fix may lead to a wider hardening review, and that can prevent related mistakes from surviving in adjacent code.
Finally, teams that rely on hardened kernel testing should make sure KFENCE-enabled runs remain part of their validation strategy. Bugs like this are exactly why those tools exist. They do not just catch memory misuse; they also reveal when the code itself has grown too dependent on assumptions that only hold in the simplest allocator model.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
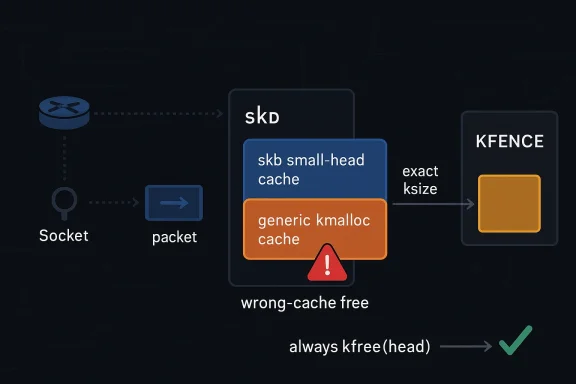
kfree(head) path in skb_kfree_head rather than trying to infer allocator provenance from ksize-style heuristics. That narrow change closes a cross-cache free condition without disturbing the networking stack’s broader behavior, which is exactly the kind of surgical repair stable maintainers prefer. vulnerable code path lives in the Linux kernel’s networking subsystem, specifically the part of the stack that manages socket buffer, or skb, head allocations and teardown. Skb handling is one of the most performance-sensitive parts of the kernel because nearly every packet that crosses a Linux system eventually passes through it. That means even a small ownership or allocator mismatch can have outsized consequences, especially when it interacts with sanitizers and debugging allocators.At the center of th_HEAD_CACHE_SIZE
, which is intentionally set to a non-power-of-two value so it does not collide with commonkmalloc` buckets. On x86_64, the value cited in the CVE description is 704 bytes, and the point of choosing a “weird” size is to make it easier for the kernel to tell whether a given skb head came from the dedicated small-head cache or from a generic allocation path. In ordinary slab allocations, that distinction is stable enough to support cache-specific freeing logic.KFENCE changes that assumption in a subts active,
kfence_ksize reports the exact requested allocation size rather than the slab bucket size. That matters because code that expects a rounded cache size may instead see a precise user-requested value and draw the wrong conclusion about where the object originated. In this case, if a caller allocates skb head data with kzalloc and happens to request exactly the same size as the small-head cache, the normal “which cache did this come from?” heuristic becomes unreliable.That is where the problem becomes security-relevant. The kernobject back to
skb_small_head_cache even though it was originally allocated from a generic kmalloc cache. The result is a slab cross-cache free, which is exactly the kind of allocator integrity error that kernel developers work hard to avoid. The NVD description quotes the failure as a wrong slab cache warning, with the expected cache and actual cache not matching.The Linux kernel community has long taken a cautious view of CVE assignment. Its oexplains that issues are typically tracked once a fix exists and is tied to stable-tree work, rather than when an abstract bug report first appears. That process is meant to create a concrete patch trail and reduce ambiguity for downstream consumers. In that context, CVE-2026-31429 fits the kernel’s standard model very well: a narrowly scoped bug, a visible fix, and a backport-friendly change that can travel through stable trees.
 Why this bug is different from a typical allocator mistake
Why this bug is different from a typical allocator mistake
Most allocator bugs are easy to describe in broad strokes but difficult to reproduce precisely. This one is interesting because the vulnerable condition depends on a combination of small details: a specific head size, KFENCE being enabled, and the skb free path making an allocator-origin decision based on size metadata. That makes the issue feel less dramatic than a classic memory corruption flaw, but not less important.The key insight is that kernel safevoiding cleverness in the teardown path. If the free side tries too hard to infer provenance, it can end up making the wrong allocator decision under instrumentation or debugging configurations. The safest strategy is often the least specialized one, because a generic free path is less likely to be misled by allocator behavior that changes under sanitizers. That is the core lesson in this CVE.
What Actually Went Wrong
The CVE description exain in a way that is unusually clear for a kernel allocator issue. A caller can allocate skb head memory withkzalloc, then pass it through slab_build_skb, which ultimately relies on ksize information during teardown. Under normal slab behavior, the size metadata helps the kernel distinguish between the dedicated skb small-head cache and generic kmalloc caches. Under KFENCE, however, the size information becomes exact in a way that can accidentally mimic the dedicated cache boundary.The dangerous part is not the allocation itself but the free-time classificatg the skb shared-info overhead, the computed end offset can line up with
SKB_SMALL_HEAD_HEADROOM, which then makes skb_kfree_head believe the object belonged to the small-head cache. In reality, the object came from a generic kmalloc cache. The free path then sends it to the wrong destination, and the slab allocator detects the mismatch as a wrong-cache free.That kind of bug is especially frustrating in hardened environments because it may only surface whng to be more observably safe. KFENCE exists to catch memory safety problems, but in this case it also altered the semantics in a way that exposed a latent assumption in the skb teardown code. The bug is therefore as much about the fragility of allocator heuristics as it is about skb handling itself.
The allocator heuristic problem
The whole issue arises because the kernel was trying to infer object origin from s than carrying a more direct ownership signal. That can work when the allocator returns bucketized sizes, but it becomes brittle when instrumentation reports exact sizes. In other words, the problem is not only “KFENCE behaved differently” but also “the free path assumed too much.”This is a classic kernel hardening lesson. A fast path may depend on shortcuts for performance, but teardown should usually be the place whe correctness over guesswork. The moment a free routine starts doing allocator detective work, it creates a risk that a debugging mode, a sanitizer, or a rare size alignment will invalidate the logic. That is exactly what happened here.
Why KFENCE Matters Here
KFENCE is designed to help developers catch bugs by changing allocator behavior in controlled ways. The Linux kernel documentatidebugging facility that can expose invalid frees and other memory misuse conditions in a way that normal operation might not. In practice, that means KFENCE can make hidden assumptions visible, which is valuable for testing but also a source of surprising edge cases.In this CVE, KFENCE’s behavior is the trigger that turns a harmless-looking size match into a cache misclassification. Because
kfence_ksize returns the exact requested size, a request that happens to equal the skb small-head cache size can blur the line between a dedicated skb cache and a generic kmalloc cache. That is a subtle interaction, and the sort of thing that tends to survive long enough to become a maintenance headache.It is also a reminder that debug and production semantics are not always identical in kernel space. A path tinary allocator assumptions may not be safe under memory instrumentation, and vice versa. That does not mean KFENCE is at fault; it means the code under test did not fully respect allocator abstraction boundaries.
Why sanitizer interactions are security issues
Sanitizers and hardening features often expose code that was never written with those modes in mind. That is not a flaw in the sanitizer; it is a sign that the original code relied on behavior that was too implicit. In security terms, any path that can produce a wrong-cache free or similar allocator integrity violation deserves careful attention, because allocator invariants are foundational to the kernel’s memory model.The practical takeaway is that “works in normal testing“correct under hardened runtime conditions.” That distinction matters for long-lived kernels, enterprise builds, and vendor configurations that enable memory debugging selectively. A fix that is robust across allocator variants is far more valuable than one that only behaves correctly in the common case.
The Fix: Simpler, Safer, More Generic
The upstream fix is straightforward: always callkfree(head) in skb_kfree_head. That eliminates allocator-specific misclassification logic and lets the generic free path handle the object according to the allocator’s own bookkeeping. The patch deliberately avoids trying to preserve a special-case decision based on size or cache identity, because that was the very logic that KFENCE broke.That design chonel maintainers usually prefer fixes that reduce special-case behavior in teardown paths, especially if the bug can be eliminated by using a more generic primitive. This approach lowers the chance that future allocator behavior changes, sanitizer modes, or architecture-specific bucket sizes will recreate the same bug in a new form. In short, the patch does not just fix one bug; it also removes an entire class of assumptions.
The result is cleaner code and a morth.
kfree is the natural partner for heap allocations whose origin may be ambiguous or may vary under instrumentation, and using it here means the skb teardown logic no longer needs to second-guess allocator provenance. That is a much better long-term posture for a hot kernel path.Why generic free paths age better
Generic memory mannd to survive allocator evolution better than cache-specific guesses. As the kernel adds more debug facilities, more hardened configurations, and more architecture-specific behavior, code that relies on a direct free rather than an inferred one usually ages more gracefully. This is one reason stable backporters favor small patches with clear semantics.The broader security benefit is reduced brittleness. If a free path is deterministic and allocator-agnostic, it is much harder for a debug mode to provoke a misfree. That means fewer latent bugs, fewer hard-to-diagnose slab warnings, and less risk that a niche configuration turns into an outage trigger.
Broader Kernel
This CVE is not just about one helper function; it reflects a larger trend in kernel hardening. Modern kernel security work is increasingly about making hidden assumptions explicit and removing clever but fragile heuristics from core paths. That trend shows up in networking, memory management, and synchronization code alike.The networking stack is a particularly sensitive place for this kind of bug because it is both performance-critical and widely exercised. Even a condition that sounds niche can matter if it sits in a path used by packet processing, testing tools, or subsystem-integrated infrastructure like BPF-driven test harnesses. The CVE text explicitly mentions
bpf_test_init as a plausible caller, which is a clue that the problem may surface in developer and validation environments as much as in production traffic paths.That has an important operational implication. Bugs that manifest in testing cll be security issues, because those same configurations are often used in CI, lab clusters, and pre-production environments where kernel stability matters. If a bug can break allocator invariants in a testing mode, it can become a blocker for validation pipelines long before it becomes a production incident.
Reliability is part of security
It is easy to dismiss a wrong-cache free as “just” a stability issue, but kernel reliability is itself a security property. A slab cross-cache free can trigger warnings, crashes, or allocator state corruption, and any of those outcomes can be exploited operationally even if they are not dramatic exploit primitives. The fact that the CVE description cites a specific wrong-cache condition tells you the allocator detected a serious integrity violation, not a harmless bookkeeping mismatch.For enterprises, that means the right k whether an attacker can weaponize the bug in a textbook way. The right question is whether the affected kernel build can be made to misbehave under realistic workloads or test paths, and whether the fix is present in the exact vendor kernel in use. That is the practical way to treat a bug in this class.
Enterprise Impact
For enterprise teams, the biggest concern is not raw exploit novelty but patch coverage and kernel configuration drift. Many organizations run vendor kernels, LTS trees, or appliance images, and those builds may carry allocator settings or debug options that differ from upstream defaults. The practical exposure window therefore depends less on the CVE headline than on whether the vendor has backported thekfree fix.The systems most likely to care are infrastructure hosts, test environments, and any fleet that uses KFENCE or comparable hardening features. Those environments are often the ones most likely to surface latent memory-management assumptions, because they are designed to catch exactly these categories of bug. That makes this CVE especially relevant to kernel engineers, CI maintainers, and platfte bespoke kernels before shipping them.
It also matters that Microsoft has included the vulnerability in its Security Update Guide ecosystem, which helps surface Linux kernel issues alongside Windows and Azure-related security data for mixed estates. Microsoft’s Security Update Guide is intended to centralize security risk information, and the company has expanded that model to include broader vulnerability disclosures. For enterprise defenders, that creates a single place to track a Linux kernel issue that might otherwise get lost in a Linux-only workflow.
What administrators should verify
At minimum, admins should confirm whether their running kernel includes the fix, whether KFENCE is enabled in any validation or staging environments, and whether the vendor kernel has backported the patch rather than simply advertising a newer version number. Version strings can be misleading in stable ecosystems; the real question is whether the code path is corrected in the shipped build.They should also check whether any packet-processing test harnesses, BPF test environments, or integration suites allocate skb heads at sizes that can intersect with the small-head cache boundary. That may sound academic, bthe kinds of workloads that uncover allocator edge cases before they become production incidents.
Consumer and Embedded Impact
For typical desktop users, this is unlikely to be a high-visibility issue. Most consumer systems will never consciously exercise the specific skb head allocation pattern described in the CVE, and many will not run kernels withrmal operation. That means the direct risk to a home laptop is probably low.The picture is different for embedded devices, routers, appliances, and vendor-supported Linux builds that live for years without broad platform refreshes. In those environments, allocator behavior and backported kernel code can diverge from upstream expectations in subtle ways. A bug that seems obscure in a desktop context can be much more relevant when it lives inside an appliance image that ships with a long support tail.
That is why firmware maintenance still matters. Vendors frequently bundle these fixes into routine updates, and the user may never know the issue existed until a stability problem appears or an audit catches the vulnerable kernel build. Small kernel bugs are ofter longest in embedded ecosystems because they do not look urgent until they become operationally inconvenient.
The hidden device risk
Consumer-facing hardware often contains Linux under the hood, even when the user never sees the kernel directly. That creates a mismatch between perceived and actual exposure. The average home user may not need to chase this specific CVE manually, but they do need to keep vendor firmware reasonably current.A stable-looking router or gateway can still carry a kernel bug for months or years if the vendor’s update cadence is slow. That is why embedded arate mention: the risk is not about active exploitation on a workstation, but about a long-lived kernel image retaining a known allocator flaw.
Strengths and Opportunities
The strongest aspect of this fix is its restraint. Rather than layering on more allocator detection logic, it removes the decision entirely and relies on the kernel’s generickfree machinery, which is a cleaner and m That is the kind of fix maintainers like because it lowers future maintenance risk while preserving the intended behavior.It also demonstrates a healthy stable-process outcome. The bug was identified, a commit landed, and the issue was tracked through the usual kernel security pipeline, which is exactly how a mature open-source project should handle a narrow but real memory-management flaw. The public CVE record gives downstream teams a useful handle for verification and patch management.
The broader opportunity is to treat this as another reminder that debug configurations matter. Teams that build and test kernels should continue to use KFENCE, KASAN, and related tools, because they expose the assumptions that can hide in hot-path code. Finding bugs in test builds is not a nuisance; it is how you prevent them from becoming production incidents.
- The patch is small and low-risk to backport.
- It improves allocator correctness without changing skb semantics.
- It reduces dependence on allocator-origin heuristics.
- It is likely to be easy for vendors to carry into stable kernels.
- It strengthens confidence in KFENCE-assisted validation.
- It helps enterprise teams map a Linux issue into their central vulnerability workflow.
- It reinforces the value of generic teardown paths in kernel code.
Risks and Concerns
The main risk is underestimation. A wrong-cache free sounds less exciting than an bug, but allocator integrity failures can still cause crashes, warnings, or harder-to-reproduce corruption, and those effects are serious in infrastructure environments. It is a mistake to equate “small fix” with “small impact.”A second concern is patch lag. Even after the fix is public, vendor kernels and long-term-support branches may take time to absorb it, and that delay can leave production fleets exposed longer than administrators expect. This is one of the recurring headaches of Linux security: the CVE exists before the actual running systems are uniformly protected.
There is also a ecause the issue appears only under particular size and allocation conditions, organizations may never see an obvious symptom until they happen to hit the edge case. That makes it easy for teams to assume the problem is theoretical when it is really just dormant.
- The bug may be hard to reproduce outside specific test conditions.
- The impact may be misread as a benign slab warning.
- Vendor backports may arrive on different schedules.
- Vulnerability scanners may not clearly reflect backported fixes.
- KFENCE-enabled test environments may be especially sensitive to the issue.
- Teams may overlook the problem if they focus only on exploitability headlines.
- Embedded and appliance systems may retain the bug long after upstream fixes.
Looking Ahead
The most important thing to watch next is downstream adoption. Upstream fixes are only the beginning; the real operational story is whether distributions, appliance vendors, and cloud images actually ship the patched code in a timely way. For most organizations, that matters more than the commit date itself. ([kernel.org](CVEs — The Linux Kernel documentationIt is also worth watching whether the bug prompts broader review of skb free logic and other code paths that try to infer allocator provenance from object size. That kind of audit is one of the useful side effects of a CVE like this: one fix may lead to a wider hardening review, and that can prevent related mistakes from surviving in adjacent code.
Finally, teams that rely on hardened kernel testing should make sure KFENCE-enabled runs remain part of their validation strategy. Bugs like this are exactly why those tools exist. They do not just catch memory misuse; they also reveal when the code itself has grown too dependent on assumptions that only hold in the simplest allocator model.
- Confirm the fix is present in your vendor kernel build.
- Check KFENCE-enabled test and staging systems first.
- Validate any packet-processing or BPF test harnesses that allocate skb heads at boundary sizes.
- Watch for stable backports across supported branches.
- Treat allocator warnings as security-relevant signals, not noise.
- Review other teardown paths that make size-based ownership guesses.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center