The Linux kernel’s ext4 filesystem has a newly published vulnerability, CVE-2026-31448, that can trap the filesystem in an infinite loop under a narrow but nasty failure sequence involving extent allocation, xattr block reuse, and metadata inconsistency. NVD published the record on April 22, 2026, and the issue is already tied to multiple upstream stable fixes, which tells you this is not just a theoretical edge case but a bug that kernel maintainers considered serious enough to patch broadly.
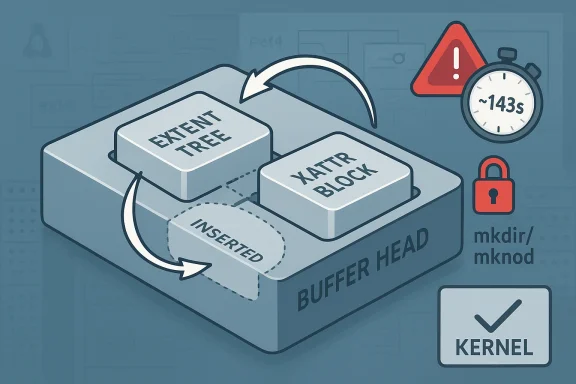
What makes this case interesting is not simply that ext4 can hang, but why it hangs: a partially failed allocation path can leave residual extent-tree state behind, allowing later directory creation operations to reuse a block that has already been reclaimed and repurposed for an xattr block. Once ext4_xattr_block_set and the directory path start contending over the same in-memory buffer head, the code can spin on the same “inserted” state and never release the inode lock, producing a long task stall rather than an immediate crash.
This is the sort of filesystem bug that exposes the sharp edge between data structure consistency and damage limitation. The fix, as described in the record, reflects that distinction: handle clean allocation failures like ENOSPC or EDQUOT normally, but when the code is already operating on corrupted metadata, it should avoid making the situation worse by freeing blocks or altering accounting paths unnecessarily.
Ext4 remains one of the most widely deployed Linux filesystems, especially in general-purpose distributions and server images where administrators value maturity, tooling, and predictable behavior. That popularity cuts both ways: when an ext4 bug lands, it has a habit of showing up everywhere from laptops and VMs to cloud nodes and storage appliances. The filesystem’s longevity also means it carries a long tail of features and fallback paths, which increases the chances that rare error handling code paths become security-relevant.
The CVE record points to a path that begins in mkdir/mknod, where ext4 maps logical blocks to physical ones, then attempts to insert a new extent into the extent tree. The failure mode described in the CVE is especially subtle because the code can reclaim a block with ext4_free_blocks without clearing the corresponding extent-tree state, leaving behind a misleading trail for later operations. That kind of residual state is exactly the sort of thing that turns a rare allocation error into a repeatable hang.
The consequence is not just “filesystem slowdown.” The record says ext4_xattr_block_set can enter a loop and hold the inode lock for roughly 143 seconds, which is long enough to trigger hung-task diagnostics and poison higher-level operations that depend on the inode becoming available again. In practical terms, that means a single bad path can stop directory creation, metadata updates, and other filesystem housekeeping from making forward progress.
The published references on the NVD page also show this issue was already addressed in multiple stable-tree commits on kernel.org, another sign that maintainers treated it as a real operational risk rather than a one-off oddity. For administrators, that usually translates into a simple rule: if your kernel branch has not absorbed the fix, you should assume the vulnerable path may still exist even if you have not seen it in production.
The defect appears to be triggered on a fairly specific branch: the filesystem disabled the huge-file feature when marking the inode dirty, and the extent insertion failed at exactly the wrong time. That matters because it shows the vulnerability is tied to a combination of allocation semantics and feature-state transitions, not merely a random I/O failure. In other words, the bug lives in the uncomfortable space where error handling and metadata mutation overlap.
The CVE text says the loop revolves around the word “inserted,” which suggests the code is cycling over a condition that never transitions to the expected steady state. Once that happens while holding the inode lock, the system may not deadlock in the classical sense, but it behaves similarly from the user’s perspective: the task is blocked, progress stalls, and dependent work backs up behind it. Operationally, that is often just as disruptive as a crash.
That is a classic kernel-maintainer tradeoff: preserve correctness when you can, but when the tree is already suspect, do less. Skipping the free of allocated blocks in the corrupted-metadata case is not a glamorous fix, but it is often the right one because it minimizes the chance of turning a recoverable inconsistency into a much larger integrity problem.
The presence of a syzbot-style stalled-task report in the record reinforces that this bug was reproducible under stress and not merely a speculative audit finding. In kernel security, reproducibility matters because it can separate an academic edge case from a practical DoS primitive. Here, the blocking time described in the report suggests the kernel can be kept busy long enough to become user-visible and service-affecting.
The CVE also hints at a quota-accounting issue when EXT4_GET_BLOCKS_DELALLOC_RESERVE is involved. That detail matters because it shows the bug is not isolated to a single mechanism; once the wrong branch is taken, collateral effects can appear in accounting paths too. Quota bugs are notoriously frustrating because they may not surface immediately, but they can leave administrators with misleading usage reports and users with hard-to-explain write failures later on.
That conservative posture is also a reminder that filesystem fixes are often about preserving invariant boundaries, not just eliminating a specific stack trace. When the bug lives in a partial-failure path, the real challenge is determining which invariants can still be trusted. The answer here appears to be: trust the early ENOSPC and EDQUOT cases, but be suspicious of everything else.
The good news is that this kind of issue is generally patchable through kernel updates rather than requiring user-space changes. The bad news is that many systems only get kernel updates on a slower cadence than browsers or application packages, so the exposure window can be wider than people expect. This is exactly why timely kernel maintenance matters.
The broader implication is that shared-kernel environments amplify low-level filesystem bugs into platform incidents. When the same kernel services many tenants, a “mere” infinite loop becomes a noisy multitenant availability event. That is why host patching and filesystem observability are now part of the security conversation, not just the reliability conversation.
This also explains why the Linux CVE process is often very terse while the underlying fixes are more nuanced. The public record may summarize the issue in a few lines, but the actual engineering work is about preserving invariants across multiple code paths. That is where filesystem maintainers earn their keep.
CVE-2026-31448 is a reminder that the oldest layers of the stack are still the ones most capable of bringing modern systems to a halt. ext4 has earned its reputation by surviving decades of pressure, but that very maturity means its failure paths deserve the same scrutiny as any new feature. The upside is that the bug has a clear shape, a conservative fix strategy, and a straightforward operational answer: patch the kernel, validate your branch, and do not assume that rare means harmless.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
What makes this case interesting is not simply that ext4 can hang, but why it hangs: a partially failed allocation path can leave residual extent-tree state behind, allowing later directory creation operations to reuse a block that has already been reclaimed and repurposed for an xattr block. Once ext4_xattr_block_set and the directory path start contending over the same in-memory buffer head, the code can spin on the same “inserted” state and never release the inode lock, producing a long task stall rather than an immediate crash.
This is the sort of filesystem bug that exposes the sharp edge between data structure consistency and damage limitation. The fix, as described in the record, reflects that distinction: handle clean allocation failures like ENOSPC or EDQUOT normally, but when the code is already operating on corrupted metadata, it should avoid making the situation worse by freeing blocks or altering accounting paths unnecessarily.
 Overview
Overview
Ext4 remains one of the most widely deployed Linux filesystems, especially in general-purpose distributions and server images where administrators value maturity, tooling, and predictable behavior. That popularity cuts both ways: when an ext4 bug lands, it has a habit of showing up everywhere from laptops and VMs to cloud nodes and storage appliances. The filesystem’s longevity also means it carries a long tail of features and fallback paths, which increases the chances that rare error handling code paths become security-relevant.The CVE record points to a path that begins in mkdir/mknod, where ext4 maps logical blocks to physical ones, then attempts to insert a new extent into the extent tree. The failure mode described in the CVE is especially subtle because the code can reclaim a block with ext4_free_blocks without clearing the corresponding extent-tree state, leaving behind a misleading trail for later operations. That kind of residual state is exactly the sort of thing that turns a rare allocation error into a repeatable hang.
The consequence is not just “filesystem slowdown.” The record says ext4_xattr_block_set can enter a loop and hold the inode lock for roughly 143 seconds, which is long enough to trigger hung-task diagnostics and poison higher-level operations that depend on the inode becoming available again. In practical terms, that means a single bad path can stop directory creation, metadata updates, and other filesystem housekeeping from making forward progress.
The published references on the NVD page also show this issue was already addressed in multiple stable-tree commits on kernel.org, another sign that maintainers treated it as a real operational risk rather than a one-off oddity. For administrators, that usually translates into a simple rule: if your kernel branch has not absorbed the fix, you should assume the vulnerable path may still exist even if you have not seen it in production.
How the bug happens
The key to understanding CVE-2026-31448 is to follow the state machine instead of just the symptom. The failure begins when ext4 attempts to attach a newly allocated block to an extent tree during directory creation, then discovers that the insert cannot be completed. At that point, the code path frees the physical block, but the tree may still carry enough stale state to make a later operation believe the block is still a valid candidate.Residual extent-tree data
The CVE description is explicit that the bug involves residual data left behind in the extent tree. That residual state is what allows a subsequent mkdir to reference a block number that was already reclaimed and is now in use by the xattr block, setting up two different logical owners for the same buffer head. In filesystem terms, that is not just a collision; it is a consistency trap that can cause retry logic to believe progress is possible when it is not.The defect appears to be triggered on a fairly specific branch: the filesystem disabled the huge-file feature when marking the inode dirty, and the extent insertion failed at exactly the wrong time. That matters because it shows the vulnerability is tied to a combination of allocation semantics and feature-state transitions, not merely a random I/O failure. In other words, the bug lives in the uncomfortable space where error handling and metadata mutation overlap.
- The failure starts during mkdir/mknod rather than ordinary reads.
- It requires an extent insertion failure after partial progress.
- The stale mapping can be reused by later directory creation.
- The xattr block and directory path can end up referencing the same memory-backed block.
- The result is a livelock-style infinite loop, not necessarily a panic.
Why xattrs get involved
Extended attributes are often where filesystem corner cases become visible, because xattr blocks are packed, shared, and tightly managed. If ext4 believes a physical block still belongs to the extent tree when it has already been reclaimed and assigned elsewhere, the xattr code can end up repeatedly searching for a reusable block that no longer fits the assumptions the algorithm is making. That is the kind of broken invariant that can trap a retry loop.The CVE text says the loop revolves around the word “inserted,” which suggests the code is cycling over a condition that never transitions to the expected steady state. Once that happens while holding the inode lock, the system may not deadlock in the classical sense, but it behaves similarly from the user’s perspective: the task is blocked, progress stalls, and dependent work backs up behind it. Operationally, that is often just as disruptive as a crash.
Why the distinction between clean and dirty failures matters
Jan Kara’s guidance in the record is especially important because it explains the fix philosophy, not just the symptom. For ENOSPC and EDQUOT, the filesystem is still internally consistent, so accounting and reclamation should proceed normally. For other errors, however, the metadata may already be corrupted, and the safest action is to avoid additional changes that could widen the blast radius.That is a classic kernel-maintainer tradeoff: preserve correctness when you can, but when the tree is already suspect, do less. Skipping the free of allocated blocks in the corrupted-metadata case is not a glamorous fix, but it is often the right one because it minimizes the chance of turning a recoverable inconsistency into a much larger integrity problem.
Why this is security-relevant
It is tempting to think of filesystem hangs as reliability bugs rather than security issues, but that distinction has become increasingly porous in the Linux ecosystem. A user-triggerable infinite loop that pins a lock can be enough for a denial-of-service attack, especially in container, multi-user, or appliance environments where a low-privilege actor can create files or directories on a mounted ext4 filesystem. That is why CVE records like this matter even when no memory corruption or code execution is involved.The presence of a syzbot-style stalled-task report in the record reinforces that this bug was reproducible under stress and not merely a speculative audit finding. In kernel security, reproducibility matters because it can separate an academic edge case from a practical DoS primitive. Here, the blocking time described in the report suggests the kernel can be kept busy long enough to become user-visible and service-affecting.
Denial of service versus corruption
The larger security takeaway is that availability bugs are often underestimated. A filesystem that hangs under a crafted sequence can take down a service stack just as effectively as a memory-safety flaw if that stack depends on local writes, temporary file creation, or metadata updates. In cloud and virtualization contexts, that can mean anything from broken CI pipelines to frozen application nodes.- Availability impacts are the most obvious risk.
- Metadata inconsistency can turn a small bug into persistent damage.
- Long inode lock hold times can stall unrelated operations.
- Shared storage or VM images increase the chance of blast radius.
- Stress-test tooling can expose issues before attackers do.
Patch strategy and what it tells us
The fix philosophy described in the CVE is notable because it does not try to force a universal cleanup path. Instead, it treats the error as context-sensitive: when the filesystem is known to be internally sound, it preserves accounting; when metadata corruption is suspected, it avoids speculative cleanup that could deepen the problem. That is a very ext4-style compromise, reflecting years of hard-won experience about how not to make recovery paths worse.A conservative error-handling model
This is a good example of how Linux storage code has evolved. Modern filesystem maintainers often prefer minimal intervention in suspicious states because aggressive repair logic can accidentally rewrite the damage into a more permanent form. In practice, that means the safest path is frequently the least ambitious one.The CVE also hints at a quota-accounting issue when EXT4_GET_BLOCKS_DELALLOC_RESERVE is involved. That detail matters because it shows the bug is not isolated to a single mechanism; once the wrong branch is taken, collateral effects can appear in accounting paths too. Quota bugs are notoriously frustrating because they may not surface immediately, but they can leave administrators with misleading usage reports and users with hard-to-explain write failures later on.
Why “skip freeing” can be the safest option
Skipping a block free sounds counterintuitive until you accept the premise that metadata may already be damaged. If the tree no longer reflects reality, then trying to reconcile it aggressively can reintroduce freed blocks into new paths or create bookkeeping mismatches that are harder to unwind than the original inconsistency. Sometimes the best remediation is to stop digging.That conservative posture is also a reminder that filesystem fixes are often about preserving invariant boundaries, not just eliminating a specific stack trace. When the bug lives in a partial-failure path, the real challenge is determining which invariants can still be trusted. The answer here appears to be: trust the early ENOSPC and EDQUOT cases, but be suspicious of everything else.
Operational impact for enterprises
For enterprise Linux users, the immediate question is less “what is the code path?” and more “where does this matter in production?” The answer is anywhere ext4 is used for writable workloads that create directories, manipulate xattrs, or otherwise exercise metadata-heavy paths. That includes application servers, container hosts, developer workstations, and virtual machine images built on ext4-backed volumes.Server and appliance scenarios
In server environments, ext4 hangs are painful because they can cascade beyond the original process. A blocked inode lock can stall background tasks, delay logging, and interfere with services that expect metadata writes to complete quickly. If the filesystem sits under a database, a package manager, or a configuration-management agent, even a short stall can look like broad system instability.- Configuration management jobs may fail or time out.
- Backup snapshots can become inconsistent.
- Container image unpacking can stall on directory creation.
- Package updates may hang while writing metadata.
- Monitoring tools may misclassify the system as unhealthy.
Consumer and desktop scenarios
On consumer desktops, the most visible symptom is likely a frozen file operation or a desktop application waiting on a blocking metadata call. Because ext4 is default or common on many distributions, users may not realize they are interacting with an enterprise-grade filesystem path until something goes wrong. That invisibility is part of the problem: the bug hides in ordinary actions like creating folders or moving files.The good news is that this kind of issue is generally patchable through kernel updates rather than requiring user-space changes. The bad news is that many systems only get kernel updates on a slower cadence than browsers or application packages, so the exposure window can be wider than people expect. This is exactly why timely kernel maintenance matters.
Competitive and ecosystem implications
Every ext4 security fix has implications beyond ext4 itself because filesystem reliability is part of the broader Linux value proposition. Cloud providers, distro maintainers, appliance vendors, and enterprise support organizations all compete on how quickly they can absorb upstream fixes and how confidently they can tell customers the problem is gone. A CVE like this becomes a test of patch velocity and backport discipline as much as a test of code quality.What it means for distros and vendors
Distro maintainers will need to decide which branches inherit the fix and how to communicate the operational risk. The upstream references shown by NVD indicate the kernel community has already landed multiple stable commits, but downstream timing still matters because many enterprises consume kernel fixes through vendor channels rather than from mainline directly. In that sense, the real competition is over time to safe state.- Fast backports reduce exposure windows.
- Clear advisories help admins prioritize reboots.
- Kernel-lifetime support policies shape patch adoption.
- Appliance vendors may need to validate storage behavior again.
- Container platforms inherit the risk if host kernels lag.
Why this matters in the age of containers
Containers do not eliminate kernel filesystem bugs; they often make them more visible. A host-side ext4 hang can affect every container that depends on the same underlying storage, and workloads that create temporary files or unpack layers can exercise the very directory paths implicated here. That makes CVE-2026-31448 relevant not just to traditional bare-metal admins, but to anyone operating Linux nodes as shared infrastructure.The broader implication is that shared-kernel environments amplify low-level filesystem bugs into platform incidents. When the same kernel services many tenants, a “mere” infinite loop becomes a noisy multitenant availability event. That is why host patching and filesystem observability are now part of the security conversation, not just the reliability conversation.
What this says about ext4 engineering
This CVE also says something about ext4 as a codebase: it is mature, battle-tested, and still full of subtle interactions between extent trees, xattrs, quota bookkeeping, and feature flags. Those interactions are exactly where long-lived filesystems accumulate risk. A code path that has worked for years can become vulnerable once a new feature, a backport, or an uncommon error branch changes the assumptions around it.The cost of deep compatibility
One reason ext4 continues to matter is that it prioritizes compatibility and incremental evolution. That strategy is good for adoption but means old behavior, new behavior, and error-recovery behavior all coexist in one large state machine. When a bug lands, it can feel less like a single defect and more like a fault line between historical design decisions.This also explains why the Linux CVE process is often very terse while the underlying fixes are more nuanced. The public record may summarize the issue in a few lines, but the actual engineering work is about preserving invariants across multiple code paths. That is where filesystem maintainers earn their keep.
Why metadata-heavy paths are dangerous
Directories and extended attributes both live in metadata-heavy territory, where small inconsistencies can trigger complex behavior. The bug described here is a reminder that the most dangerous storage bugs are not always the ones that touch raw data blocks; sometimes they are the ones that confuse the allocator about what is still owned, what is free, and what is only apparently free.- Extent trees encode allocation state.
- Xattr blocks reuse metadata blocks aggressively.
- Error paths can leave stale ownership behind.
- Quota accounting amplifies partial failures.
- Locking turns logical confusion into user-visible stalls.
Strengths and Opportunities
The upside of a bug like this is that it is now documented, understood, and already tied to upstream fixes, which gives operators a path forward. It also reinforces the value of kernel fuzzing and syzbot-style stress testing, since these tools continue to expose bugs that would otherwise remain dormant until a bad day in production.- The issue is well characterized in the public record.
- The fix philosophy is conservative and targeted.
- Multiple upstream references indicate active remediation.
- Administrators can prioritize kernel upgrades rather than broad workarounds.
- The bug strengthens the case for continuous fuzz testing.
- It highlights the importance of metadata-path validation.
- It gives distro vendors a concrete opportunity to improve security communications.
Risks and Concerns
The biggest concern is that filesystem hangs are often dismissed until they affect a real service, and by then the recovery cost is higher. Another risk is that partial-failure logic like this may vary subtly across kernel branches, making it hard for administrators to know whether their specific build still contains the problem without checking vendor advisories or changelogs.- The bug can appear as a hang rather than a crash, delaying detection.
- Residual state may be hard to reproduce outside targeted tests.
- Downstream backports can introduce branch-specific differences.
- Quota side effects may create secondary operational surprises.
- Metadata corruption makes remediation more delicate than a normal retry.
- Long lock holds can cascade into wider service stalls.
- Shared hosts and container nodes expand the possible blast radius.
Looking Ahead
The near-term story will be about how quickly distributions, cloud images, and enterprise kernels absorb the fix and how clearly they communicate risk to customers. Because the CVE is already public and tied to stable commits, the main question is not whether the issue exists, but whether any given deployment has already crossed the line into a safe build. That is the sort of question operators need answered in concrete version terms, not general assurances.What to watch next
- Vendor advisories that map the CVE to specific kernel package versions.
- Distribution backports for long-term-support branches.
- Confirmation of whether container-host images pick up the fix automatically.
- Additional fuzzing reports that probe related ext4 extent/xattr paths.
- Any follow-on CVEs that touch the same error-handling territory.
CVE-2026-31448 is a reminder that the oldest layers of the stack are still the ones most capable of bringing modern systems to a halt. ext4 has earned its reputation by surviving decades of pressure, but that very maturity means its failure paths deserve the same scrutiny as any new feature. The upside is that the bug has a clear shape, a conservative fix strategy, and a straightforward operational answer: patch the kernel, validate your branch, and do not assume that rare means harmless.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center