CVE-2026-31450 is a textbook example of how a seemingly narrow kernel race can become a real operational risk: the ext4 filesystem could publish a partially initialized
The bug is especial fast commit path. Fast commits are a performance feature in ext4 designed to reduce latency by logging smaller deltas instead of forcing a full traditional journal transaction every time. The Linux kernel documentation explains that ext4’s journal layer, JBD2, is central to metadata consistency and that fast commits are a special optimization layered on top of that machinery. When a filesystem optimization depends on the integrity of a state transition, a small publish-order mistake can become a crash vector.
The crash described in the CVE record shows the danger clearly: the fast commit flush path can pass the not-yet-safe
What makes this worth attention now is that the issue has already been published into the CVE ecosystem and linked to stable-kernel fixes. The advisory points to several kernel.org stable references, which is usually the sign that upstream maintainers treated the bug as a real correctness issue worthy of backporting rather than a mere cleanup. That matters for operators, because a CVE that has moved into stable channels is the sort of defect that can show up in production distributions before anyone notices it in d
Ext4 is one of the most battle-tested filesystems in Linux, but that does not make it immune to race conditions. In fact, mature filesystems often accumulate more synchronization complexity over time because they have to preserve compatibility while adding performance features such as delayed allocation, journaling optimizations, and fast commit paths. The kernel documentation describes ext4 as a journaling filesystem built on JBD2, with fast commit support layered into the ordered-mode workflow for better latency.
The key architectural point is that JBD2 and ext4 are tightly coupled but not interchangeable. JBD2 handles journal mechanics, while ext4 uses those mechanics to protect metadata and coordinate crash recovery. That means a bug in how ext4 hands off an inode-like structure to JBD2 can propagate far beyond the local helper function. When the handoff is visible to concurrent readers before initialization finishes, the whole state machine becomes vulnerable to mis-sequencing.
This is also why the fix in CVE-2026-31450 is interesting from a kernel engineering perspective. The patch does not redesign ext4’s journal model. Instead, it corrects the publication order by initializing the JBD2 inode first and only then publishing the pointer with
The bug demonstrates a recurring lesson in storage code: liveness and safety are not the same thing. A pointer can be non-NULL and still not be safe for use if the object it refers to has not reached a valid steady state. For ext4, which must support high-concurrency write workloads, the difference between “allocated” and “ready” is the sort of distinction thailesystem survives a stress test or falls over in the middle of fsync processing.
At the heart of the issue is the order in which
That kind of bug is especially treacherous because it does not require malformed input. It only requires timing. If the fast commit flush path reaches the structure at the wrong moment, the code path can drift into
The use of
The
The result is a classseemingly valid pointer with a non-valid* embedded dependency. Those are the bugs that usually evade casual testing because they require contention, CPU interleaving, and just the right writeback conditions. In production, though, “rare” often means “eventually.”
The stack trace matters because it shows a user-visible operation,
This makes theow correctness footnote. It sits in the category of bugs that can turn a legitimate synchronization request into a kernel crash, which is operationally serious even when no attacker is involved. Reliability bugs in core filesystems often become security bugs in practice because they can produce denial of service, data loss, or recovery failure.
That does not mean fast commits are flawed as a concept. It means the implementation has to be exact about what is visible when. In this case, the correct answer was to ensure initialization completed before publication, which is the sort of fix that restores the original design intent rather than rewriting it.
That approach is important bhange minimal. There is no new global lock, no heavy serialization across ext4, and no redesign of the fast commit pipeline. Instead, the fix restores the invariant that a non-NULL pointer means a usable object, which is exactly what readers had been assuming all along.
The fact that the bug has stable references indicates that kernel maintainers considered it important enough to move into supported brong clue that the fix is not just theoretical hygiene. It is the sort of change distributions will want to carry into long-term builds for real users.
The advisory is also useful because it helps teams distinguish between exploit-driven urgency and operational urgency. This is not a remote code execution headline, but it is tch for systems that depend on ext4, heavy journaling activity, or frequent sync semantics. In the real world, downtime* is often the first security impact that administrators feel.
The fix is also straightforward for patch management teams to explain. This is not a sprawling backport with broad architectural consequences. It is a targeted publication-order correction, which makes it easier for v Linux distributions to validate, ship, and document. That usually speeds adoption compared with more invasive storage changes.
There is also a trust issue. When storage bugs hit production, users may blame the application, the hardware, or the hypervisor before they ever suspect the filesystem. That ambiguity slows incident response and makes clean postmortems harder, which is exactly why early patching cosystem and Competitive Implications
Every filesystem CVE subtly reshapes how operators think about risk. Ext4’s long history gives it a strong reputation, but reputation is not immunity, and this bug shows that even foundational code still depends on precise concurrency discipline. In pryers and admins will continue to compare filesystems not just on features, but on the perceived maturity of their correctness model.
This is also where the broader Linux ecosystem becomes visible. Microsoft’s vulnerability publication process surfaced the CVE, while the fix and technical explanation live in the Linux kernel ecosystem. That split is increasingly normal in a world where enterprise fleets are hybrid, cloud-connected, and dependent on upstream open-source infrastructure even when the business itself is not “Linux-first.”
The bigger competitive point is that modern filesystems are all being pushed toward more sophisticated state handling. Fast commits, compression, delayed allocation, and aggressive writeback all increase the synchronization surface. Any filesystem that claims performance advantages now has to prove it can keep those features correct, not just fast.
That perspective is useful because it explains why narrow bugs still get broad attention. They may not headline a cyber incident response playbook, but they aaintenance pipelines, especially where storage availability and data integrity are contractual obligations.
The next thing to watch is how quickly downstream Linux vendors incorporate the fix into long-term kernel streams. Because the issue is already tied to stable references, there is a good chance many maintained branches will pick it up without drama. Still, enterprise environments actual kernel build rather than assuming a vendor has already synchronized with upstream.
Another thing worth monitoring is whether additional ext4 fast commit corner cases appear around inode publication or journal object lifetime. Whenever a subsystem fix relies on publication ordering, it is worth asking whether neighboring paths use the same assumptions. One fixed race often reveals another nearby one.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
jinode, and a concurrent reader could then follow that pointer into code that assumes the embedded i_vfs_inode is already valid. The result is not just theoretical instability. The reported failure path can crash the kernel during fast commit flush handling, which makes this bug relevant to both reliability and security-minded operations. The published advisory and upstream explanation show that the fix is deliberately small, but the consequences of the bug are anything but. VE sits at the intersection of memory ordering, filesystem metadata lifetime, and concurrent journal handling. In practical terms, ext4’s ext4_inode_attach_jinode used to assign ei->jinode before calling jbd2_journal_init_jbd_inode, which meant another CPU could observe a non-NULL pointer before the attached journal inode was fully initialized. That race is subtle, but in kernel space subtle races are often the most dangerous because they violate assumptions that other code treats as already proven.The bug is especial fast commit path. Fast commits are a performance feature in ext4 designed to reduce latency by logging smaller deltas instead of forcing a full traditional journal transaction every time. The Linux kernel documentation explains that ext4’s journal layer, JBD2, is central to metadata consistency and that fast commits are a special optimization layered on top of that machinery. When a filesystem optimization depends on the integrity of a state transition, a small publish-order mistake can become a crash vector.
The crash described in the CVE record shows the danger clearly: the fast commit flush path can pass the not-yet-safe
jinode into jbd2_wait_inode_data, which then dereferences i_vfs_inode->i_mapping. If i_vfs_inode is not ready, the kernel can fault while walking page-cache state. In other words, this is not just about a bad pointer; it is about publishing a compound object before the kernel can safely reliants.What makes this worth attention now is that the issue has already been published into the CVE ecosystem and linked to stable-kernel fixes. The advisory points to several kernel.org stable references, which is usually the sign that upstream maintainers treated the bug as a real correctness issue worthy of backporting rather than a mere cleanup. That matters for operators, because a CVE that has moved into stable channels is the sort of defect that can show up in production distributions before anyone notices it in d
Ext4 is one of the most battle-tested filesystems in Linux, but that does not make it immune to race conditions. In fact, mature filesystems often accumulate more synchronization complexity over time because they have to preserve compatibility while adding performance features such as delayed allocation, journaling optimizations, and fast commit paths. The kernel documentation describes ext4 as a journaling filesystem built on JBD2, with fast commit support layered into the ordered-mode workflow for better latency.
The key architectural point is that JBD2 and ext4 are tightly coupled but not interchangeable. JBD2 handles journal mechanics, while ext4 uses those mechanics to protect metadata and coordinate crash recovery. That means a bug in how ext4 hands off an inode-like structure to JBD2 can propagate far beyond the local helper function. When the handoff is visible to concurrent readers before initialization finishes, the whole state machine becomes vulnerable to mis-sequencing.
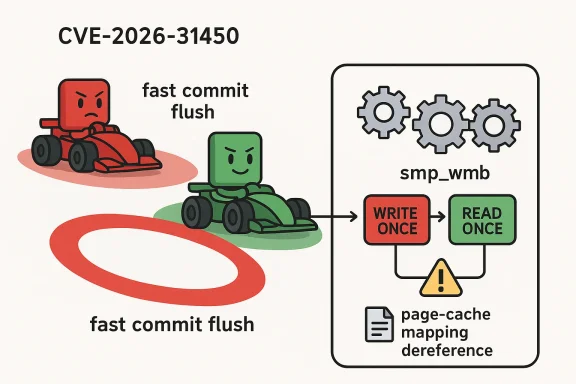
This is also why the fix in CVE-2026-31450 is interesting from a kernel engineering perspective. The patch does not redesign ext4’s journal model. Instead, it corrects the publication order by initializing the JBD2 inode first and only then publishing the pointer with
WRITE_ONCE, guarded by smp_wmb. That pattern is a classic Linux-kerr: initialize fully, enforce write ordering, then expose the pointer to readers who use READ_ONCE.The bug demonstrates a recurring lesson in storage code: liveness and safety are not the same thing. A pointer can be non-NULL and still not be safe for use if the object it refers to has not reached a valid steady state. For ext4, which must support high-concurrency write workloads, the difference between “allocated” and “ready” is the sort of distinction thailesystem survives a stress test or falls over in the middle of fsync processing.
 What Actually Went Wrong
What Actually Went Wrong
At the heart of the issue is the order in which ei->jinode became visible to other CPUs. The vulnerable sequence allowed the pointer to be stored before jbd2_journal_init_jbd_inode finished initializing the object. That means a racing reader could observe an apparentlow it, and hit fields that were still unset or inconsistent.That kind of bug is especially treacherous because it does not require malformed input. It only requires timing. If the fast commit flush path reaches the structure at the wrong moment, the code path can drift into
jbd2_wait_inode_data with an incomplete object graph underneath it. In kernel terms, that is enough to turn a rare racecrash on sufficiently stressed systems.The Race Window
The vulnerability is not about “bad ext4 data” in the usual sense. It is about the publication window between object creation and object readiness. The CVE description explicitly says readers could see a non-NULLjinode while i_vfs_inode was still unset, which is exactly the kind of half-construrrency bugs love.The use of
smp_wmb in the fix is important because it forces the kernel to respect the ordering of writes across CPUs. Combined with WRITE_ONCE, it prevents the compiler and processor from reordering the visibility of the pointer ahead of the initialization sequence. That is the right remedy when the problem is not a missing lock, but a missing o- The bug depends on timing, not input validation.- The failure mode is a visibility race.
- The vulnerable object is published before it is fully initialized.
- The fix uses memory-order primitives rather than heavy locking.
- Readers are expected to fetch the pointer with
READ_ONCE.
The
jinode is not just an internal convenience structure. It bridges ext4 inode state and JBD2 journal machinery, so if it is exposed too early, a caller may assume the journal-side link is safe when it is not. That matters because once the fast commit flush path hands the structure to jbd2_wait_inode_data, the code expects normal filesystem invariants to already hold.The result is a classseemingly valid pointer with a non-valid* embedded dependency. Those are the bugs that usually evade casual testing because they require contention, CPU interleaving, and just the right writeback conditions. In production, though, “rare” often means “eventually.”
Fast Commit and Why the Crash Surst commits are designed to improve performance by logging only the minimal set of metadata changes needed to recover recent updates. That makes them attractive for workloads where latency matters, but it also means the flush and recovery paths are under more pressure to make correct assumptions about object state. The kernel documentation positions fast commits as a performance feature tightly integrated with ext4’s ordered journaling model, not as a separate subsystem.
The practical consequence is that a bug in the metadata handoff can surface at fsync time, not just during mount or recovery. The CVE’s crash trace shows exactly that: the fault emerges duringext4_fc_commit and then bubbles through filemap_fdatawait_range_keep_errors and ext4_sync_file. That is a strong signal that ordinary application activity can trip the defect under the right conditiFault AppearsThe stack trace matters because it shows a user-visible operation,
fdatasync, reaching the bad path. That means this is not an obscure background-only defect. A database, mail server, VM storage stack, or any application that relies heavily on sync semantics could potentially intersect with the vulnerable path if the timing lines up.This makes theow correctness footnote. It sits in the category of bugs that can turn a legitimate synchronization request into a kernel crash, which is operationally serious even when no attacker is involved. Reliability bugs in core filesystems often become security bugs in practice because they can produce denial of service, data loss, or recovery failure.
- Fast commit reduces latency by lo- The flush path is therefore critical to correctness.
fdatasynccan reach the vulnerable code path.- A crash in this path can disrupt real workloads.
- The bug is triggered by concurrency, not malformed user data.
Performance Features Can Tighten the Error Budget
Oserves attention is that performance features often shrink the margin for error. The faster a filesystem tries to publish, flush, and recover state, the less room there is for implicit assumptions about object readiness. Ext4 has earned a reputation for stability precisely because its maintainers are careful, but this CVE shows how even well-understood code can become fragile when new optimization paths are layered on top.That does not mean fast commits are flawed as a concept. It means the implementation has to be exact about what is visible when. In this case, the correct answer was to ensure initialization completed before publication, which is the sort of fix that restores the original design intent rather than rewriting it.
First, Publish Second
The remediation is refreshingly direct. According to the CVE description, the kernel now initializes the JBD2 inode first, then usessmp_wmb and WRITE_ONCE to publish ei->jinode only after the structure is fully ready. Readers are expected to fetch that pointer with READ_ONCE, which aligns the consuming side with the new publication discipline.That approach is important bhange minimal. There is no new global lock, no heavy serialization across ext4, and no redesign of the fast commit pipeline. Instead, the fix restores the invariant that a non-NULL pointer means a usable object, which is exactly what readers had been assuming all along.
Why Memory Barriers Are the Right Tool
In keory barriers are often the right answer when the bug is about ordering rather than mutual exclusion.smp_wmb ensures that writes before the barrier become visible before writes after it, which prevents another CPU from seeing the pointer before the object has been initialized. That is especially valuable in hot paths where adding a full lock would be more disruptive than the bug itself.WRITE_ONCE and READ_ONCE matter just as much because they tell reader-side code that the value is being deliberately shared across CPUs. This combination does not merely patch one crash. It establishes a publication contract that future readers can rely on without inventing ad hoc assumptions.- Initialize the JBD2 inode before exposing the pointer.
- Use memory ordering to prevent r.
- Publish the pointer atomically with
WRITE_ONCE. - Consume it with
READ_ONCEto preserve the contract. - Keep the fix surgical to reduce regression risk.
Why the Patch Is Low-Noise but High-Value
This kind of fix is easy to underestimate because the code delta small synchronization fixes often carry the highest value because they eliminate undefined behavior at its source. A race like this can sit dormant for a long time, then explode only when enough concurrency and writeback pressure line up in production.The fact that the bug has stable references indicates that kernel maintainers considered it important enough to move into supported brong clue that the fix is not just theoretical hygiene. It is the sort of change distributions will want to carry into long-term builds for real users.
Why This Matters to Enterprise Linux Teams
For enterprise operators, CVE-2026-31450 is a reminder that *filesystem correctness is infrastructur in the sync path can interrupt services, force remediation work, and trigger recovery procedures that are every bit as costly as a traditional vulnerability response. In mixed environments, these issues also matter because Linux storage nodes often sit under application stacks that non-Linux teams depend on but do not directly monitor.The advisory is also useful because it helps teams distinguish between exploit-driven urgency and operational urgency. This is not a remote code execution headline, but it is tch for systems that depend on ext4, heavy journaling activity, or frequent sync semantics. In the real world, downtime* is often the first security impact that administrators feel.
Practical Impact Areas
The most exposed environments are likely to be systems that push ext4 hard under concurrency. Databases, virtualized storage, build systems, log collectors, and other wads are natural candidates for hitting fast commit and fsync paths often enough to matter. The fact that the crash trace appears duringfdatasync makes the risk more concrete than a speculative race buried in initialization code.The fix is also straightforward for patch management teams to explain. This is not a sprawling backport with broad architectural consequences. It is a targeted publication-order correction, which makes it easier for v Linux distributions to validate, ship, and document. That usually speeds adoption compared with more invasive storage changes.
- High write concurrency increases exposure.
- Sync-heavy workloads make the bug more reachable.
- Downtime is a realistic operational consequence.
- The patch is narrow enough to backport cleanly.
- Vendor kernels still need explicit verumer Versus Enterprise Exposure
There is also a trust issue. When storage bugs hit production, users may blame the application, the hardware, or the hypervisor before they ever suspect the filesystem. That ambiguity slows incident response and makes clean postmortems harder, which is exactly why early patching cosystem and Competitive Implications
Every filesystem CVE subtly reshapes how operators think about risk. Ext4’s long history gives it a strong reputation, but reputation is not immunity, and this bug shows that even foundational code still depends on precise concurrency discipline. In pryers and admins will continue to compare filesystems not just on features, but on the perceived maturity of their correctness model.
This is also where the broader Linux ecosystem becomes visible. Microsoft’s vulnerability publication process surfaced the CVE, while the fix and technical explanation live in the Linux kernel ecosystem. That split is increasingly normal in a world where enterprise fleets are hybrid, cloud-connected, and dependent on upstream open-source infrastructure even when the business itself is not “Linux-first.”
What Rivals Gain Indirectly
Competing filesystems do not “win” because ext4 has a bug, but they do benefit from the simple fact that administrators compare operational confidence across options. If a filesystem has fewer visible corner-case defectafer, even when the underlying code is just as complex. That is especially true in conservative environments where stability matters more than niche performance gains.The bigger competitive point is that modern filesystems are all being pushed toward more sophisticated state handling. Fast commits, compression, delayed allocation, and aggressive writeback all increase the synchronization surface. Any filesystem that claims performance advantages now has to prove it can keep those features correct, not just fast.
- Reliability perception matters as much as feature lists.
- Small kernel bugs can influence operator preference over time.
- Hybrid enterprises need advisory coordination across vendors.
- Fast paths increase the burden on correctness engineering.
- Mature filesystems still need active hardening.
Why This Is Bigger Than One CVE
CVE-2026-31450 is a reminder that the modern kernel is a system of systems. A pointer publication buelper can propagate into journal logic, page-cache access, and sync behavior at the user boundary. That is why vendors, distro maintainers, and enterprise teams increasingly treat kernel patching as a supply-chain process rather than a simple package update task.That perspective is useful because it explains why narrow bugs still get broad attention. They may not headline a cyber incident response playbook, but they aaintenance pipelines, especially where storage availability and data integrity are contractual obligations.
Strengths and Opportunities
The good news is that this CVE has a clear root cause, a surgical fix, and a publication trail that should make backporting manageablferent situation from a mystery crash with no stable explanation. It also gives operators a concrete marker for version verification rather than forcing them to infer safety from symptom absence.- Clear race condition, not an opaque failure.
- Narrow patch surface.
- Good fit for stable backports.
- Easy to explain to operations teams.
- Improves confidence in ext4 fast commit handling.
- Reif
READ_ONCE/WRITE_ONCE. - Strengthens kernel concurrency discipline overall.
Risks and Concerns
The biggest concern is that race bugs are notoriously hard to reproduce in controlled testing. A system may look perfectly healthy until a particular workload, CPU schedule, or I/O burst exposes the flawed ordering. Thaf symptoms is not the same as the absence of exposure.- Rare timing windows can evade QA.
- Production load can make the bug more likely than lab tests suggest.
- Older vendor kernels may lag on the fix.
- Sync-intensive services may be more exposed than they realize.
- Crash symptoms can be misattributed to hardwares.
- Backport status must be verified per distribution.
- Recovery-time failures can be expensive even when rare.
The next thing to watch is how quickly downstream Linux vendors incorporate the fix into long-term kernel streams. Because the issue is already tied to stable references, there is a good chance many maintained branches will pick it up without drama. Still, enterprise environments actual kernel build rather than assuming a vendor has already synchronized with upstream.
Another thing worth monitoring is whether additional ext4 fast commit corner cases appear around inode publication or journal object lifetime. Whenever a subsystem fix relies on publication ordering, it is worth asking whether neighboring paths use the same assumptions. One fixed race often reveals another nearby one.
ndor kernel advisories that explicitly map the fix.
- Backport notes for long-term support branches.
- Any follow-on ext4 fast commit race reports.
- Verification that production images include the patched build.
- Reports from high-concurrency storage workloads.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center