CVE-2026-31499 is a medium-severity Linux kernel Bluetooth vulnerability published on April 22, 2026, in which the L2CAP connection teardown path can deadlock when delayed work callbacks contend for the same connection lock during cleanup. That plain description understates why it matters. This is not a flashy remote-code-execution bug or a headline-grabbing Bluetooth takeover; it is the kind of kernel concurrency flaw that turns reliability into a security boundary. For WindowsForum readers, the lesson is broader than Linux Bluetooth: modern patch management now lives in the messy overlap between operating systems, firmware-adjacent hardware stacks, cloud images, developer workstations, and vulnerability databases that often lag behind the real fixes.
The National Vulnerability Database currently scores CVE-2026-31499 at 5.5, a medium CVSS 3.1 rating with local attack vector, low complexity, low privileges required, no user interaction, and high availability impact. In ordinary enterprise triage, that combination tends to land below remote execution, privilege escalation, and exposed network-service bugs.
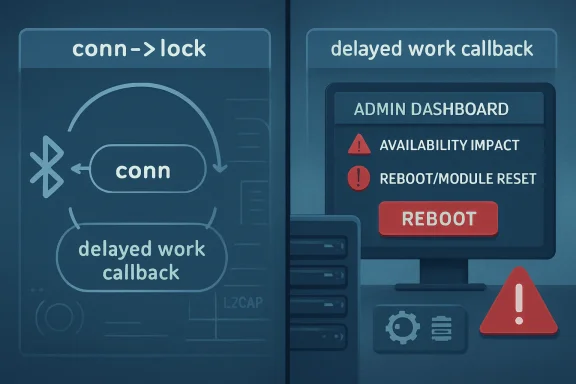
But the availability impact is the point. A deadlock in kernel Bluetooth code can freeze the affected path hard enough that the practical remediation is often a reboot, a module reset, or a kernel update. If the system is a developer laptop, that is annoying; if it is a Linux endpoint used for field diagnostics, kiosk hardware, industrial control adjacency, or a lab system with wireless peripherals, it can become an operational outage.
The vulnerability sits in L2CAP, the Logical Link Control and Adaptation Protocol layer that Bluetooth uses above the controller-facing transport. L2CAP is not a desktop convenience feature bolted onto the side of the kernel. It is part of the plumbing that makes Bluetooth connections usable by higher-level profiles, including audio, HID, and other services that users experience as “my mouse,” “my headset,” or “that sensor gateway.”
That is why CVSS can mislead. CVSS says this is local and medium. Operators hear “Bluetooth can wedge the kernel’s connection teardown logic.” Both are true, but only one tells you what a Monday morning support queue might look like.
That creates the classic AB-BA deadlock pattern. One path holds the connection lock and waits for work to finish; the work path is already running or about to run and waits for the connection lock. Neither side can proceed, because each is waiting for the other to release the thing it needs.
The fix is correspondingly unglamorous: cancel or disable the delayed work before taking the lock, and use
That is how a lot of kernel security work looks from the inside. The dangerous part is not a thousand-line rewrite. It is the placement of a synchronization call relative to a spinlock or mutex, and whether a callback that appears harmless can re-enter the same locking universe from a different direction.
CVE-2026-31499 is currently characterized as local in the NVD vector, and the public description does not establish a remote over-the-air exploit path. That distinction matters. It would be irresponsible to turn a deadlock in connection deletion into a dramatic claim about arbitrary nearby attackers knocking over every Linux laptop in a coffee shop.
Still, Bluetooth’s history argues against complacency. The stack has repeatedly shown that complicated state machines, asynchronous events, controller quirks, and profile negotiation make fertile ground for memory safety and concurrency problems. L2CAP in particular has been a recurring site of bugs because it coordinates connection state, signaling, timers, and channel lifecycle under conditions that are inherently racy.
The conservative reading is simple: this is an availability vulnerability in a kernel subsystem reachable through Bluetooth connection activity under affected versions. That is enough to patch, especially on systems where Bluetooth is enabled by default and users are unlikely to know whether the kernel they booted contains the backport.
That is not how neat vulnerability stories are supposed to look. Administrators like a simple statement: “all versions before X are vulnerable.” The Linux stable ecosystem frequently denies them that comfort. Fixes move through multiple maintained trees, regressions appear in some branches but not others, and the presence or absence of a specific commit matters more than the marketing version number.
This is why kernel CVEs often confuse asset systems. A vulnerability scanner may map by CPE, a distribution may backport the fix without changing the apparent upstream version, and a vendor kernel may contain a patch that the raw kernel number suggests it lacks. Conversely, a system that looks “newer” can be vulnerable if it is on a branch where the fix has not yet landed.
For enterprise Linux, the right question is rarely “what upstream kernel number is this?” The better question is “has my distribution’s kernel package incorporated the patch corresponding to the stable commits for this CVE?” That is less satisfying, but it is how Linux security maintenance actually works.
This does not make CVE-2026-31499 a Windows Bluetooth vulnerability. It does not imply that ordinary Windows 10 or Windows 11 Bluetooth stacks are affected by this Linux kernel bug. The affected component is the Linux kernel’s Bluetooth L2CAP implementation, not the Windows Bluetooth stack.
But Microsoft’s listing reflects a more practical reality: Windows shops are no longer Windows-only shops. A Windows administrator may own developer laptops that run WSL, CI systems that build Linux containers, Hyper-V hosts that run Linux guests, Azure workloads based on Linux images, or endpoint tools that inventory CVEs across mixed fleets. The operating system boundary has become an accounting convenience, not a security boundary.
That is why WindowsForum should care. The modern Microsoft ecosystem is full of Linux, and the modern Windows admin increasingly has to understand when a Linux CVE is relevant, when it is noise, and when it signals a patch dependency buried inside a platform service.
That difference matters because vulnerability relevance depends on reachability. If the vulnerable code is not built, not loaded, not reachable from the environment, or abstracted away by Windows handling the underlying hardware, the operational risk is not the same as on a native Linux install. Asset owners should resist the scanner-driven habit of treating every kernel CVE as equally exploitable everywhere the word “Linux” appears.
Still, WSL belongs in the conversation for a different reason. It has trained Windows-heavy organizations to accept Linux kernels as normal parts of the workstation and developer estate. Once that happens, kernel provenance, update cadence, and component exposure become ordinary IT management questions rather than specialist Linux questions.
So the answer is nuanced. CVE-2026-31499 should not be panic-applied to Windows Bluetooth. But it should prompt mixed-platform teams to ask which Linux kernels they run, who updates them, how quickly vendor fixes arrive, and whether scanners can distinguish between a vulnerable package version and a reachable vulnerable subsystem.
That triad can make the bug seem harmless. It is not stealing secrets. It is not bypassing authentication. It is not granting root. But if the affected system’s purpose depends on staying responsive, a kernel deadlock is not a second-class incident.
In practice, availability often has the shortest path to visible business damage. A deadlocked system stops doing the job it was purchased to do. A user cannot pair a device, an input path disappears, a service that depends on the hardware stack stalls, or an embedded unit needs a physical restart.
The security industry has spent years telling administrators to prioritize “exploitable” bugs, which is sensible. But exploitability is not just shellcode. A reliable local denial of service in kernel space can become a tool for harassment, disruption, or chained failure, especially where local accounts, kiosks, shared lab systems, or untrusted workloads exist.
The dangerous moment is deletion. Creation paths tend to be linear and well tested: allocate, initialize, attach, start. Deletion paths are where the ghosts live: cancel timers, drain work, detach from lists, notify users, release locks, drop references, and hope no callback wakes up halfway through.
That is why this patch’s alignment with
Servers without Bluetooth hardware may still carry a kernel built with Bluetooth support, but practical exposure differs from a laptop with active Bluetooth. Cloud virtual machines generally do not expose a Bluetooth controller. Developer workstations and edge devices are much more plausible candidates for attention.
The biggest operational mistake would be to overfit the response to CVSS. A medium score does not mean “ignore until the next quarterly cycle” if your estate includes Linux endpoints with Bluetooth enabled and users who depend on wireless input devices. Conversely, it does not mean emergency maintenance for headless Linux servers in a data center with no Bluetooth path.
The best response is boring and targeted: confirm whether vendor kernels include the patch, prioritize endpoints and edge systems with Bluetooth enabled, validate that reboot policies actually activate the new kernel, and suppress or defer findings only where the vulnerable path is demonstrably unreachable.
This is especially true for long-term-support distributions. A system may report an older kernel baseline while carrying dozens or hundreds of backported security patches. A scanner that keys only on the upstream version can produce false positives. A scanner that trusts package metadata blindly can miss locally compiled kernels, custom modules, or unsupported vendor images.
The CVE also shows the lag built into public enrichment. The CVE was received from kernel.org on April 22, 2026, while NIST’s initial analysis and CPE additions appeared on April 28, 2026. That is not scandalous; it is normal. But it means the first several days of operational response often happen before the neat database fields are complete.
For IT teams, the answer is to treat NVD as one layer. Pair it with distribution security trackers, kernel package changelogs, vendor advisories, and actual system inventory. If you manage Microsoft-adjacent Linux through Azure or enterprise tooling, include Microsoft’s security metadata as another signal, not as the sole source of truth.
L2CAP sits in the middle of that complexity. It has to multiplex channels, manage signaling, react to timeouts, handle identity-address updates, and clean up state when connections disappear. A race in teardown is exactly the sort of bug one expects in such a subsystem.
The uncomfortable truth is that wireless convenience stacks are now part of the trusted computing base. A laptop’s Bluetooth implementation is not merely a consumer feature; it is kernel code parsing and coordinating state based on events that may originate outside the machine. Even when a particular CVE is local, the subsystem’s security posture deserves attention.
This is why turning off unused Bluetooth remains a legitimate hardening measure. It is not a cure-all and it is not always practical, but reducing exposed subsystems is still one of the oldest security ideas that works. If a production Linux system does not need Bluetooth, it should not have Bluetooth enabled simply because the default image included it.
That unevenness makes communication harder. Security teams want clear categories; operations teams want practical exceptions; executives want to know whether this is “a Microsoft issue,” “a Linux issue,” or “not our problem.” The honest answer may be all three, depending on the estate.
For a Windows-heavy organization, the right framing is not “Linux Bluetooth bug threatens Windows.” That is wrong. The right framing is “our Microsoft-centered environment may still contain Linux kernels in places our old patch model does not see.” That is the more durable lesson.
The same logic applies beyond Bluetooth. The past decade has filled Windows shops with Linux-based network appliances, container hosts, Kubernetes nodes, developer subsystems, Android-derived devices, and cloud images. A vulnerability program that still treats Linux as someone else’s platform is already out of date.
Those questions matter more than whether the CVE appeared in a Microsoft guide, a Linux stable commit, or a scanner dashboard. Branding tells you where the information surfaced. Reachability tells you whether the bug can hurt you.
For endpoint fleets, the practical work is to deploy the vendor-provided kernel update and verify reboot completion. Linux kernel patches do not protect a running system until the fixed kernel is booted, and many endpoint programs are weaker at reboot enforcement on Linux than on Windows. A patched package sitting on disk is not the same as a patched kernel in memory.
For servers, administrators should separate theoretical package exposure from hardware reality. If Bluetooth is disabled, absent, or removed from the kernel configuration, risk drops substantially. But exceptions should be documented rather than guessed, because future hardware changes, image reuse, or module loading can invalidate assumptions.
For CVE-2026-31499, that means knowing whether the relevant stable patches are present, not merely whether the version string looks newer than some threshold. Kernel version arithmetic can be deceptive when fixes are backported across multiple branches.
This is where small vendors often struggle. A product team may freeze on a kernel series, cherry-pick hardware enablement patches, and treat Bluetooth as a commodity subsystem that does not need active attention. Then a deadlock fix lands upstream, the CVE gets a medium score, and nobody is quite sure whether the product’s private tree contains the bad ordering.
The answer is process, not panic. Maintain a bill of materials for kernel provenance. Track stable commit backports. Test Bluetooth teardown and reconnect scenarios on affected hardware. Make kernel updates part of product maintenance rather than an emergency exercise performed only when a CVE number appears.
Linux kernel findings are notorious for this. Containers may report userland packages but share the host kernel. Dormant boot entries may contain vulnerable kernels that are not currently booted. Live systems may run a kernel older than the latest installed package because nobody rebooted. Distribution backports may make upstream version comparisons wrong.
The right response is not to dismiss the scanner. It is to enrich the finding. Check the running kernel, the installed kernel packages, the distribution advisory, the actual Bluetooth exposure, and whether the fix commit is included. Only then decide whether the item is a patch task, a reboot task, a configuration task, or an acceptable false positive.
This is also a good moment to audit how your tools handle Linux in Windows-centric environments. If your vulnerability program beautifully tracks Windows cumulative updates but poorly understands Linux kernel backports, it will overreact to some bugs and miss others.
It is, however, a reminder that availability bugs in kernel subsystems deserve real triage. The affected code is low-level, the impact can be a deadlock, and the version mapping spans multiple kernel branches. That combination is exactly where sloppy asset data produces bad decisions.
The most concrete takeaways are straightforward:
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
 A Medium CVE Can Still Be a Hard Stop
A Medium CVE Can Still Be a Hard Stop
The National Vulnerability Database currently scores CVE-2026-31499 at 5.5, a medium CVSS 3.1 rating with local attack vector, low complexity, low privileges required, no user interaction, and high availability impact. In ordinary enterprise triage, that combination tends to land below remote execution, privilege escalation, and exposed network-service bugs.But the availability impact is the point. A deadlock in kernel Bluetooth code can freeze the affected path hard enough that the practical remediation is often a reboot, a module reset, or a kernel update. If the system is a developer laptop, that is annoying; if it is a Linux endpoint used for field diagnostics, kiosk hardware, industrial control adjacency, or a lab system with wireless peripherals, it can become an operational outage.
The vulnerability sits in L2CAP, the Logical Link Control and Adaptation Protocol layer that Bluetooth uses above the controller-facing transport. L2CAP is not a desktop convenience feature bolted onto the side of the kernel. It is part of the plumbing that makes Bluetooth connections usable by higher-level profiles, including audio, HID, and other services that users experience as “my mouse,” “my headset,” or “that sensor gateway.”
That is why CVSS can mislead. CVSS says this is local and medium. Operators hear “Bluetooth can wedge the kernel’s connection teardown logic.” Both are true, but only one tells you what a Monday morning support queue might look like.
The Bug Is Small Because Kernel Bugs Usually Are
The technical failure is beautifully mundane. The functionl2cap_conn_del() cancels delayed work items for info_timer and id_addr_timer while holding conn->lock. The delayed work functions themselves, l2cap_info_timeout() and l2cap_conn_update_id_addr(), also try to acquire that same lock.That creates the classic AB-BA deadlock pattern. One path holds the connection lock and waits for work to finish; the work path is already running or about to run and waits for the connection lock. Neither side can proceed, because each is waiting for the other to release the thing it needs.
The fix is correspondingly unglamorous: cancel or disable the delayed work before taking the lock, and use
disable_delayed_work_sync() so that the work cannot simply be rearmed after cancellation. The kernel change also aligns the L2CAP teardown behavior with the pattern already used in hci_conn_del(), which is a clue that this is less a novel design insight than a consistency repair.That is how a lot of kernel security work looks from the inside. The dangerous part is not a thousand-line rewrite. It is the placement of a synchronization call relative to a spinlock or mutex, and whether a callback that appears harmless can re-enter the same locking universe from a different direction.
Bluetooth Remains a Kernel Attack Surface, Even When the Bug Is Local
Bluetooth vulnerabilities occupy an awkward place in security planning. They are physical-proximity bugs, but they are not always “local” in the way administrators use the word. A malicious USB device requires insertion; a malicious local user requires an account; a Bluetooth-adjacent attack may require being nearby with a radio and the right timing.CVE-2026-31499 is currently characterized as local in the NVD vector, and the public description does not establish a remote over-the-air exploit path. That distinction matters. It would be irresponsible to turn a deadlock in connection deletion into a dramatic claim about arbitrary nearby attackers knocking over every Linux laptop in a coffee shop.
Still, Bluetooth’s history argues against complacency. The stack has repeatedly shown that complicated state machines, asynchronous events, controller quirks, and profile negotiation make fertile ground for memory safety and concurrency problems. L2CAP in particular has been a recurring site of bugs because it coordinates connection state, signaling, timers, and channel lifecycle under conditions that are inherently racy.
The conservative reading is simple: this is an availability vulnerability in a kernel subsystem reachable through Bluetooth connection activity under affected versions. That is enough to patch, especially on systems where Bluetooth is enabled by default and users are unlikely to know whether the kernel they booted contains the backport.
The Version Matrix Is the Real Story
The NVD change history is more interesting than the score. Its affected CPE list points to Linux kernel 6.14, ranges from 6.13.8 up to but not including 6.14, release candidates for 7.0, versions from 6.19 up to but not including 6.19.11, versions from 6.14.1 up to but not including 6.18.21, versions from 6.12.20 up to but not including 6.13, and versions from 6.6.84 up to but not including 6.7.That is not how neat vulnerability stories are supposed to look. Administrators like a simple statement: “all versions before X are vulnerable.” The Linux stable ecosystem frequently denies them that comfort. Fixes move through multiple maintained trees, regressions appear in some branches but not others, and the presence or absence of a specific commit matters more than the marketing version number.
This is why kernel CVEs often confuse asset systems. A vulnerability scanner may map by CPE, a distribution may backport the fix without changing the apparent upstream version, and a vendor kernel may contain a patch that the raw kernel number suggests it lacks. Conversely, a system that looks “newer” can be vulnerable if it is on a branch where the fix has not yet landed.
For enterprise Linux, the right question is rarely “what upstream kernel number is this?” The better question is “has my distribution’s kernel package incorporated the patch corresponding to the stable commits for this CVE?” That is less satisfying, but it is how Linux security maintenance actually works.
Microsoft’s Presence Is a Sign of the Times
The user-facing source here is Microsoft’s Security Update Guide, which may seem odd for a Linux Bluetooth kernel flaw. It is not. Microsoft now operates enough Linux-adjacent infrastructure — Azure Linux, Linux images in Azure, WSL-related developer workflows, container hosts, and security tooling that tracks non-Windows CVEs — that Linux kernel vulnerabilities routinely matter inside Microsoft-run estates.This does not make CVE-2026-31499 a Windows Bluetooth vulnerability. It does not imply that ordinary Windows 10 or Windows 11 Bluetooth stacks are affected by this Linux kernel bug. The affected component is the Linux kernel’s Bluetooth L2CAP implementation, not the Windows Bluetooth stack.
But Microsoft’s listing reflects a more practical reality: Windows shops are no longer Windows-only shops. A Windows administrator may own developer laptops that run WSL, CI systems that build Linux containers, Hyper-V hosts that run Linux guests, Azure workloads based on Linux images, or endpoint tools that inventory CVEs across mixed fleets. The operating system boundary has become an accounting convenience, not a security boundary.
That is why WindowsForum should care. The modern Microsoft ecosystem is full of Linux, and the modern Windows admin increasingly has to understand when a Linux CVE is relevant, when it is noise, and when it signals a patch dependency buried inside a platform service.
WSL Is Not the Same Risk, But It Is Part of the Same Conversation
It is tempting to drag WSL into every Microsoft-and-Linux security discussion. That should be done carefully. WSL 2 uses a Microsoft-provided Linux kernel for its virtualized environment, but typical WSL usage does not expose Linux Bluetooth L2CAP in the same way as a native Linux laptop with Bluetooth hardware managed by the Linux kernel.That difference matters because vulnerability relevance depends on reachability. If the vulnerable code is not built, not loaded, not reachable from the environment, or abstracted away by Windows handling the underlying hardware, the operational risk is not the same as on a native Linux install. Asset owners should resist the scanner-driven habit of treating every kernel CVE as equally exploitable everywhere the word “Linux” appears.
Still, WSL belongs in the conversation for a different reason. It has trained Windows-heavy organizations to accept Linux kernels as normal parts of the workstation and developer estate. Once that happens, kernel provenance, update cadence, and component exposure become ordinary IT management questions rather than specialist Linux questions.
So the answer is nuanced. CVE-2026-31499 should not be panic-applied to Windows Bluetooth. But it should prompt mixed-platform teams to ask which Linux kernels they run, who updates them, how quickly vendor fixes arrive, and whether scanners can distinguish between a vulnerable package version and a reachable vulnerable subsystem.
Deadlocks Are Availability Bugs With Security Paperwork
Availability vulnerabilities have always had a strange status. They are security issues by definition when an attacker can deny service, but they often compete poorly for attention against code execution and data theft. CVE-2026-31499 is a textbook example: no confidentiality impact, no integrity impact, but high availability impact.That triad can make the bug seem harmless. It is not stealing secrets. It is not bypassing authentication. It is not granting root. But if the affected system’s purpose depends on staying responsive, a kernel deadlock is not a second-class incident.
In practice, availability often has the shortest path to visible business damage. A deadlocked system stops doing the job it was purchased to do. A user cannot pair a device, an input path disappears, a service that depends on the hardware stack stalls, or an embedded unit needs a physical restart.
The security industry has spent years telling administrators to prioritize “exploitable” bugs, which is sensible. But exploitability is not just shellcode. A reliable local denial of service in kernel space can become a tool for harassment, disruption, or chained failure, especially where local accounts, kiosks, shared lab systems, or untrusted workloads exist.
The Locking Lesson Is Older Than Bluetooth
The specific names in this CVE are Bluetooth-specific, but the bug pattern is general. Kernel code is full of asynchronous work: timers, delayed work queues, callbacks, teardown paths, and state machines that continue to run while another part of the subsystem believes it is shutting things down.The dangerous moment is deletion. Creation paths tend to be linear and well tested: allocate, initialize, attach, start. Deletion paths are where the ghosts live: cancel timers, drain work, detach from lists, notify users, release locks, drop references, and hope no callback wakes up halfway through.
cancel_delayed_work_sync() sounds final, but synchronization primitives are only safe in the locking context for which they were designed. If the work being waited on needs a lock already held by the waiter, the code has built a trap. disable_delayed_work_sync() adds another guarantee by preventing rearming, but even that is only correct if placed outside the lock cycle.That is why this patch’s alignment with
hci_conn_del() is notable. Kernel maintainers are not just fixing one path; they are making one teardown pattern resemble another known-good teardown pattern. Consistency is a security property when humans maintain millions of lines of concurrent code.The Patch Is Simple; The Fleet Decision Is Not
For a single Linux laptop, the guidance is easy: update to a kernel package that includes the fix, reboot into it, and move on. For a fleet, the decision tree is messier. You need to know distribution branch, kernel flavor, hardware exposure, Bluetooth enablement, local user model, and whether the affected systems are desktops, servers, appliances, or cloud guests.Servers without Bluetooth hardware may still carry a kernel built with Bluetooth support, but practical exposure differs from a laptop with active Bluetooth. Cloud virtual machines generally do not expose a Bluetooth controller. Developer workstations and edge devices are much more plausible candidates for attention.
The biggest operational mistake would be to overfit the response to CVSS. A medium score does not mean “ignore until the next quarterly cycle” if your estate includes Linux endpoints with Bluetooth enabled and users who depend on wireless input devices. Conversely, it does not mean emergency maintenance for headless Linux servers in a data center with no Bluetooth path.
The best response is boring and targeted: confirm whether vendor kernels include the patch, prioritize endpoints and edge systems with Bluetooth enabled, validate that reboot policies actually activate the new kernel, and suppress or defer findings only where the vulnerable path is demonstrably unreachable.
Vulnerability Databases Are Maps, Not the Territory
The NVD entry’s CPE mapping is useful, but it is not a substitute for vendor advisories. CPEs try to describe affected software configurations in a standardized way. Linux distributions try to maintain stable user-facing kernel versions while backporting fixes. Those two worlds do not always line up.This is especially true for long-term-support distributions. A system may report an older kernel baseline while carrying dozens or hundreds of backported security patches. A scanner that keys only on the upstream version can produce false positives. A scanner that trusts package metadata blindly can miss locally compiled kernels, custom modules, or unsupported vendor images.
The CVE also shows the lag built into public enrichment. The CVE was received from kernel.org on April 22, 2026, while NIST’s initial analysis and CPE additions appeared on April 28, 2026. That is not scandalous; it is normal. But it means the first several days of operational response often happen before the neat database fields are complete.
For IT teams, the answer is to treat NVD as one layer. Pair it with distribution security trackers, kernel package changelogs, vendor advisories, and actual system inventory. If you manage Microsoft-adjacent Linux through Azure or enterprise tooling, include Microsoft’s security metadata as another signal, not as the sole source of truth.
The Bluetooth Stack Keeps Paying Interest on Complexity
Bluetooth has always promised convenience by hiding complexity. Pair the device, hear the audio, move the mouse, sync the sensor. Beneath that simplicity is a sprawling protocol family with legacy modes, low-energy behavior, controller firmware differences, host stack policy, and profiles that age at different speeds.L2CAP sits in the middle of that complexity. It has to multiplex channels, manage signaling, react to timeouts, handle identity-address updates, and clean up state when connections disappear. A race in teardown is exactly the sort of bug one expects in such a subsystem.
The uncomfortable truth is that wireless convenience stacks are now part of the trusted computing base. A laptop’s Bluetooth implementation is not merely a consumer feature; it is kernel code parsing and coordinating state based on events that may originate outside the machine. Even when a particular CVE is local, the subsystem’s security posture deserves attention.
This is why turning off unused Bluetooth remains a legitimate hardening measure. It is not a cure-all and it is not always practical, but reducing exposed subsystems is still one of the oldest security ideas that works. If a production Linux system does not need Bluetooth, it should not have Bluetooth enabled simply because the default image included it.
The Enterprise Risk Is Uneven by Design
CVE-2026-31499 is unlikely to affect every organization with equal force. It is more relevant to Linux desktop fleets than to conventional Windows desktops. It is more relevant to native Linux on laptops than to WSL development shells. It is more relevant to edge devices and field systems than to ordinary cloud instances.That unevenness makes communication harder. Security teams want clear categories; operations teams want practical exceptions; executives want to know whether this is “a Microsoft issue,” “a Linux issue,” or “not our problem.” The honest answer may be all three, depending on the estate.
For a Windows-heavy organization, the right framing is not “Linux Bluetooth bug threatens Windows.” That is wrong. The right framing is “our Microsoft-centered environment may still contain Linux kernels in places our old patch model does not see.” That is the more durable lesson.
The same logic applies beyond Bluetooth. The past decade has filled Windows shops with Linux-based network appliances, container hosts, Kubernetes nodes, developer subsystems, Android-derived devices, and cloud images. A vulnerability program that still treats Linux as someone else’s platform is already out of date.
Patch Triage Should Follow Reachability, Not Branding
The smartest remediation plan starts with exposure. Does the system run an affected Linux kernel branch? Does it include the relevant Bluetooth code? Is Bluetooth enabled? Is there actual Bluetooth hardware? Are untrusted local users present? Would a deadlock cause meaningful disruption?Those questions matter more than whether the CVE appeared in a Microsoft guide, a Linux stable commit, or a scanner dashboard. Branding tells you where the information surfaced. Reachability tells you whether the bug can hurt you.
For endpoint fleets, the practical work is to deploy the vendor-provided kernel update and verify reboot completion. Linux kernel patches do not protect a running system until the fixed kernel is booted, and many endpoint programs are weaker at reboot enforcement on Linux than on Windows. A patched package sitting on disk is not the same as a patched kernel in memory.
For servers, administrators should separate theoretical package exposure from hardware reality. If Bluetooth is disabled, absent, or removed from the kernel configuration, risk drops substantially. But exceptions should be documented rather than guessed, because future hardware changes, image reuse, or module loading can invalidate assumptions.
The Fix Also Warns Against Homegrown Kernel Drift
Custom kernels complicate this CVE more than they solve it. Enthusiasts, appliance vendors, and performance-sensitive shops sometimes carry patched or self-built kernels for good reasons. But every deviation from a vendor kernel creates a responsibility to track stable fixes at commit granularity.For CVE-2026-31499, that means knowing whether the relevant stable patches are present, not merely whether the version string looks newer than some threshold. Kernel version arithmetic can be deceptive when fixes are backported across multiple branches.
This is where small vendors often struggle. A product team may freeze on a kernel series, cherry-pick hardware enablement patches, and treat Bluetooth as a commodity subsystem that does not need active attention. Then a deadlock fix lands upstream, the CVE gets a medium score, and nobody is quite sure whether the product’s private tree contains the bad ordering.
The answer is process, not panic. Maintain a bill of materials for kernel provenance. Track stable commit backports. Test Bluetooth teardown and reconnect scenarios on affected hardware. Make kernel updates part of product maintenance rather than an emergency exercise performed only when a CVE number appears.
Scanner Noise Will Be Worse Than the Bug
For many organizations, CVE-2026-31499 will first appear as a scanner finding. That finding may be correct, partially correct, or irrelevant. The scanner may see a CPE range, an installed package, a container base image, or a kernel string that no longer reflects the running kernel.Linux kernel findings are notorious for this. Containers may report userland packages but share the host kernel. Dormant boot entries may contain vulnerable kernels that are not currently booted. Live systems may run a kernel older than the latest installed package because nobody rebooted. Distribution backports may make upstream version comparisons wrong.
The right response is not to dismiss the scanner. It is to enrich the finding. Check the running kernel, the installed kernel packages, the distribution advisory, the actual Bluetooth exposure, and whether the fix commit is included. Only then decide whether the item is a patch task, a reboot task, a configuration task, or an acceptable false positive.
This is also a good moment to audit how your tools handle Linux in Windows-centric environments. If your vulnerability program beautifully tracks Windows cumulative updates but poorly understands Linux kernel backports, it will overreact to some bugs and miss others.
The Practical Reading of CVE-2026-31499 Is Narrow but Not Small
For administrators, this CVE should land in the “patch in the normal kernel maintenance window, accelerate for exposed endpoints” category. It is not a known mass-exploitation event based on the public information available. It is not a Windows Bluetooth flaw. It is not a reason to disable Bluetooth across every device without context.It is, however, a reminder that availability bugs in kernel subsystems deserve real triage. The affected code is low-level, the impact can be a deadlock, and the version mapping spans multiple kernel branches. That combination is exactly where sloppy asset data produces bad decisions.
The most concrete takeaways are straightforward:
- Systems running affected Linux kernel branches should receive vendor kernel updates that include the L2CAP deadlock fix.
- Linux endpoints, edge devices, and appliances with Bluetooth enabled deserve higher priority than headless servers without Bluetooth hardware.
- Windows systems are not directly affected by this Linux kernel L2CAP flaw, but Microsoft-managed environments may still surface it through Linux images, Azure assets, or mixed-fleet security tooling.
- WSL should not be treated as equivalent to a native Linux Bluetooth host without evidence that the vulnerable Bluetooth path is reachable.
- Kernel package installation is not enough; administrators must confirm that systems have rebooted into the fixed kernel.
- Scanner findings should be validated against distribution advisories and running-kernel state, because upstream version strings and backported fixes often diverge.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center