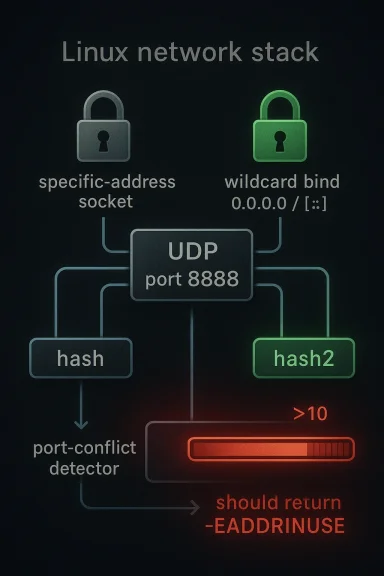
CVE-2026-31503 is a small-looking Linux kernel networking fix with outsized operational significance: UDP’s port-bind conflict detection could miss a collision when the code switched to the newer
What makes the issting is the trigger pattern. The record gives a concrete reproduction sequence: after enough sockets are already bound to the same port on distinct local addresses, the socket hash bucket count crosses the threshold where
UDP bind semantics in Liimple on the surface: a socket binds to a local address and port, and the kernel ensures that no conflicting bind slips through. Under the hood, though, the kernel has to balance correctness and performance, because port lookups happen constantly and the socket tables can become crowded quickly. That is why Linux uses hashing strategies to reduce the cost of collision checks, and why those strategies have to preserve exact bind semantics even as they optimize for scale.
The advisory for CVE-2026-31503 explains that UDP uses two hashes for collision detection: one keyed by local port only, and another keyed by local address plus local port. The switch to
This is the sort of bug that tends to survive for a while be works. A single socket, or even a handful of sockets, may never cross the threshold that activates the alternate path. Once the table is dense enough, however, the kernel’s behavior changes in a way that ordinary testing may not cover. That is why the advisory’s pseudo-code is useful: it shows a realistic bind sequence, not an artificial memory-corruption trick or a contrived packet payload.
The Linux kernel’s own CVE documentation helps explain why issues like this are cataloged even when they do not obviously resemble classic exploit bugs. The kernel team says CVEs are often assigned to fixes that are already in stable trees, and that many kernel bugs are security-relevant because they affect privileged system behavior, not only because they open a direct code-execution path. That philosophy fits this case well: a bind-conflict bypass in a core networking primitive is the kind of kernel defect that can matter operationally even if exploitability is not yet neatly scored.
Historically, networking bugs in the Linux kernel often fall into one of two buckets: memory safety issues or state-machine issues. CVE-2026-31503 belongs firmly to the second category. It is about whether the kernel’s bookkeeping still matches the real world once the lookup strategy changes. In practice, those bugs can be harder to spot than a crash, but they can be just as disruptive because they undermine the kernel’s contract with user space.
The advisory says the current code switches to
The Linux kernel’s stable-backport process is designed for exactly this sort of targeted correction. The kernel docs note that fixes already merged upstream are routinely propagated into stable branches, and maintainers expect patches to be small, understandable, and narrowly scoped when they are intended for long-term support trees. That profile matches this UDP fix: it is a logic correction, not a major rewrite.
That pattern tells us something important: the failure is not tied to one IP family or one exotic socket type. It affects the general bind machinery. That broadens the practical relevance because modern servers often mix IPv4, IPv6, and v4-mapped behavior in the same service stack. If the kernel’s collision logic gets it wrong under one of those combinations, the error can surface in very ordinary deployments.
The Linux community’s own CVE process documentation is relevant here because it emphasizes that kernel CVEs are often assigned conservatively, even when exploitation is not proven. The project recognizes that privileged kernel bugs can be security-relevant simply because they undermine the system’s core guarantees. In other words, a wrong bind result in kernel space is not “just a bug”; it is a trust failure in an enforcement path.
Why
The key technical insight in the CVE record is that
That is why the fix mentions reusing TCP’s existing helper. The TCP path already had the right logic in
The broader lesson is that shared policy should be shared code. When two network protocols have to answer the same question—“is it safe to use this port for this kind of bind?”—the answer should not depend on which subsystem happened to reimplement the logic last. That kind of duplication is a classic source of security and stability regressions.
The kernel documentation on stable releases is instructive here too. It says backports should be precise and that the upstream commit history matters for landing fixes in supported branches. This CVE fits that pattern because the patch is small, portable, and tightly coupled to one semantic mistake.
That is particularly true in enterprise environments where patch management is already tied to kernel maintenance windows. A bug that changes bind semantics can break production in ways that do not map cleanly to traditional vulnerability scoring. Operational impact may be more important than a theoretical exploit number here.
A consumer who runs a few daemons on a laptop may never notice this bug. But a homelab owner with containers, VPN endpoints, media servers, and IPv6 enabled could absolutely wind up in the territory where the hash-slot threshold matters. That makes this a good example of a vulnerability that is “low drama” on paper but still relevant to technically advanced users.
That is why it is a mistake to dismiss networking CVEs as “enterprise only.” The broader the role of the machine, the broader the impact of a port-binding mistake. The issue is especially relevant for users who rely on predictable daemon startup, scripted failover, or service supervision.
This matters because stable kernel maintainers usually want patches that do one thing well and avoid broader semantic changes. A fix that consolidates the decision logic is easier to audit than one that tries to duplicate the logic in another file and hopes both copies stay synchronized. In that sense, the patch is not just correct; it is maintainable.
It is also worth watching whether similar hash-threshold logic exists elsewhere in the network stack. Once one protocol path is found to mishandle a wildcard bind under alternate lookup conditions, it is reasonable to ask whether neighboring code has the same class of mismatch. Kernel fixes often become a template for adjacent audits, and this one is a strong candidate for that kind of review.
Ultimately, CVE-2026-31503 is a reminder that correctness in the Linux networking stack is a security property in its own right. A bind that succeeds when it should fail can be every bit as disruptive as a more dramatic flaw, because it corrupts the assumptions that services, orchestrators, and failover systems build on. The fix is small, the lesson is large, and the practical value lies in getting the patch into the field before the wrong bind turns into the wrong outage.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
hash2 lookup path, allowing a wildcard bind such as [::]:8888 or 0.0.0.0:8888 to succeed even though specific-address sockets were already occupying that port. The advisory describes the flaw as affecting both IPv6 and IPv4 wildcard binds, including IPv4-mapped wildcard cases, and notes that the TCP side already has the correct helper logic, which the UDP fix reuses after renaming and moving it into a shared header ic example of a boundary-condition regression in a kernel fast path. The code chooses between udptable->hash and udptable->hash2 depending on bucket pressure, but the wildcard conflict check was not mirrored correctly once hash2 became active. That means the kernel could accept a bind it should have rejected with -EADDRINUSE, which is not just a correctness problem: it can break service isolation, confuse daemons that assume exclusive port ownership, and create hard-to-diagnose networking behavior under load.What makes the issting is the trigger pattern. The record gives a concrete reproduction sequence: after enough sockets are already bound to the same port on distinct local addresses, the socket hash bucket count crosses the threshold where
hash2 becomes active, and the wildcard bind suddenly slips through. The threshold matters because it means the failure is state-dependent, not universal; systems with light socket churn may never notice it, while busy hosts, service meshes, container nodes, and multi-homed servers are more likely to run into the bad path.
 Background
Background
UDP bind semantics in Liimple on the surface: a socket binds to a local address and port, and the kernel ensures that no conflicting bind slips through. Under the hood, though, the kernel has to balance correctness and performance, because port lookups happen constantly and the socket tables can become crowded quickly. That is why Linux uses hashing strategies to reduce the cost of collision checks, and why those strategies have to preserve exact bind semantics even as they optimize for scale.The advisory for CVE-2026-31503 explains that UDP uses two hashes for collision detection: one keyed by local port only, and another keyed by local address plus local port. The switch to
hash2 happens when a hash-slot count exceeds 10, which is a sensible performance optimization in busy environments. The problem is that wildcard binds depend on conflict detection across all addresses on a port, and a hash function chosen for performance can quietly weaken the conflict check if the bind logic is not careful enough.This is the sort of bug that tends to survive for a while be works. A single socket, or even a handful of sockets, may never cross the threshold that activates the alternate path. Once the table is dense enough, however, the kernel’s behavior changes in a way that ordinary testing may not cover. That is why the advisory’s pseudo-code is useful: it shows a realistic bind sequence, not an artificial memory-corruption trick or a contrived packet payload.
The Linux kernel’s own CVE documentation helps explain why issues like this are cataloged even when they do not obviously resemble classic exploit bugs. The kernel team says CVEs are often assigned to fixes that are already in stable trees, and that many kernel bugs are security-relevant because they affect privileged system behavior, not only because they open a direct code-execution path. That philosophy fits this case well: a bind-conflict bypass in a core networking primitive is the kind of kernel defect that can matter operationally even if exploitability is not yet neatly scored.
Historically, networking bugs in the Linux kernel often fall into one of two buckets: memory safety issues or state-machine issues. CVE-2026-31503 belongs firmly to the second category. It is about whether the kernel’s bookkeeping still matches the real world once the lookup strategy changes. In practice, those bugs can be harder to spot than a crash, but they can be just as disruptive because they undermine the kernel’s contract with user space.
Overview
At the center of the vulnerability is a mismatch between where the kernel looks for conflicts and what kind of bind is being attempted. A specific-address bind, such asfd00::3:8888, naturally interacts with a narrower set of entries than a wildcard bind, which must respect all sockets already holding the port. If the kernel uses the wrong lookup path when the table is crowded, it can fail to notice a conflict that should have blocked the bind.The advisory says the current code switches to
hash2 once hslot->count > 10. That is a useful optimization for narrow-address lookups, but it also raises a subtle problem: the wildcard bind conflict check must remain broad enough to catch all relevant existing sockets. The report shows that before the bucket gets crowded, the code correctly returns -EADDRINUSE; after one more socket pushes the bucket past the threshold, the wildcard bind can unexpectedly succeed. That is the heart of the bug.Why wildcard bindrd binds are not just another address form. They are a promise that the socket intends to listen broadly, across all local interfaces for the selected port. That means the kernel has to be stricter, not looser, when deciding whether the port is already in use. A failure in that logic can let two components believe they own the same port, which is a recipe for packet delivery confusion, service startup failures, or inconsistent failover behavior.
Why the threshold matters
The threshold of 10 is important because it means the bug is not rooted in a permanently broken algorithm. Instead, the kernel behaves correctly until the density of sockets tips it onto a different code path. That is often the worst kind of bug from an operator’s perspective because it creates a split-brain effect: one environment or one moment in time works, while another almost identical setup fails in a way that is difficult to reproduce.The Linux kernel’s stable-backport process is designed for exactly this sort of targeted correction. The kernel docs note that fixes already merged upstream are routinely propagated into stable branches, and maintainers expect patches to be small, understandable, and narrowly scoped when they are intended for long-term support trees. That profile matches this UDP fix: it is a logic correction, not a major rewrite.
The Failure Mode
The advisory’s example sequence is the clearest evidence of how the bug behaves in practice. Ten sockets bind tofd00::1 through fd00::10 on port 8888, then a wildcard bind is attempted. At that point the kernel still detects the conflict correctly. Once another socket is added, pushing the relevant hash slot count higher, the next wildcard bind on the same port can succeed unexpectedly. The same pattern applies to IPv4 wildcard binds and IPv4-mapped wildcard addresses su`.That pattern tells us something important: the failure is not tied to one IP family or one exotic socket type. It affects the general bind machinery. That broadens the practical relevance because modern servers often mix IPv4, IPv6, and v4-mapped behavior in the same service stack. If the kernel’s collision logic gets it wrong under one of those combinations, the error can surface in very ordinary deployments.
What makes it operationally tricky
This kind of bug rarely announces itself with a crash. Instead, it appears as an apparently legitimate bind succeeding when it should have failed, and the real damage may show up later when a service fails to receive traffic, another service binds unexpectedly, or a restart sequence behaves differently than before. Those are the kinds of failures administrators often misattribute to configuration drift or race conditions in userspace.The Linux community’s own CVE process documentation is relevant here because it emphasizes that kernel CVEs are often assigned conservatively, even when exploitation is not proven. The project recognizes that privileged kernel bugs can be security-relevant simply because they undermine the system’s core guarantees. In other words, a wrong bind result in kernel space is not “just a bug”; it is a trust failure in an enforcement path.
Why this resembles a service-affecting bug
If a daemon expectsbind to fail for a port already in use, and the kernel says yes when it should say no, the application may proceed under false assumptions. That can lead to service overlap, broken hot-standby patterns, partial outage during failover, or packet loss that looks like random instability. In clustered or orchestrated environments, the harm can be multiplied because more than one component may react to the same incorrect result.- Wildcard binds must be stricter than specific-address binds.
- Dense socket tables can trigger alternate lookup paths.
- The failure can be silent rather than crash-driven.
- IPv4, IPv6, and v4-mapped addresses are all implicated.
- The operational symptom may be misbinding, not a kernel panic.
Why hash2 Changes the Risk
The key technical insight in the CVE record is that hash2 is keyed by local address and local port, while the original hash is keyed by local port only. That difference is useful for scaling, but it also means the kernel must carefully preserve the semantics of wildcard conflict detection when it switches between them. If the wrong hash path is used for a wildcard bind, the lookup cand miss an existing occupant of the port.That is why the fix mentions reusing TCP’s existing helper. The TCP path already had the right logic in
inet_use_bhash2_on_bind, and the patch renames it to inet_use_hash2_on_bind while moving it to inet_hashtables.h so UDP can call the same decision logic. That is a strong sign that the bug was not unique to UDP’s concept of binding, but rather to duplication and inconscol implementations.Reuse is the right fix here
Kernel engineers usually prefer to unify policy checks instead of re-implementing them independently in multiple subsystems. That reduces drift, improves auditability, and makes it less likely that one protocol family quietly diverges from another. In this case, reusing the TCP helper is not just code cleanup; it is a correctness repair that makes the bind decision consistent across stacks.The broader lesson is that shared policy should be shared code. When two network protocols have to answer the same question—“is it safe to use this port for this kind of bind?”—the answer should not depend on which subsystem happened to reimplement the logic last. That kind of duplication is a classic source of security and stability regressions.
Why the bug escaped earlier
A likely reason is that the failure only appears once the hash-slot count crosses a threshold. That means the bug can hide in development and test environments that do not produce enough socket churn to trigger the alternate path. It also means regressions can slip in when a clean-looking optimization is added without revalidating all the bind edge cases.The kernel documentation on stable releases is instructive here too. It says backports should be precise and that the upstream commit history matters for landing fixes in supported branches. This CVE fits that pattern because the patch is small, portable, and tightly coupled to one semantic mistake.
Enterprise Impact
For enterprise fleets, the most important issue is not whether the bug sounds dramatic; it is whether it can upset infrastructure that depends on exclusive port binding. The answer is yes. Load balancers, service managers, container platforms, multicast-heavy systems, and failover-capable daemons all rely on predictable bind behavior. If a wildcard bind succeeds when it should fail, the result can be service overlap or a startup path that behaves differently under load than it does in the lab.Where the risk is highest
The risk is greatest on hosts with dense socket usage, many listening services, or network orchestration layers that bring sockets up and down repeatedly. That includes edge gateways, Kubernetes nodes, multi-tenant appliances, and systems running virtualization or SDN components. These are environments where a port conflict may not just affect one local process; it can ripple through routing, service discovery, or health-check logic.- Multi-service gateways are especially sensitive.
- Container hosts may hit the threshold more easily.
- Failover daemons depend on exclusive binds.
- IPv6-heavy deployments should not assume immunity.
- Mixed v4/v6 stacks may surface the issue differently.
Why this matters even without a CVSS score
NVD had not yet provided a final score at publication time, and that should not be read as a sign that the issue is harmless. The NVD record for fresh kernel CVEs often lags the upstream fix and stable references, especially while enrichment is still underway. In practice, administrators should prioritize the actual kernel behavior and whether their workloads exercise the affected path, not wait for a database to fully normalize the advisory.That is particularly true in enterprise environments where patch management is already tied to kernel maintenance windows. A bug that changes bind semantics can break production in ways that do not map cleanly to traditional vulnerability scoring. Operational impact may be more important than a theoretical exploit number here.
Consumer Impact
For most consumer desktops and laptops, the direct risk is likely lower than in server or appliance environments. Typical home systems do not create the same density of listeners or service-management churn that pushes the kernel into the problematic path. That said, consumer Linux boxes used as home routers, homelab nodes, NAS systems, or small-office servers are a different story.A consumer who runs a few daemons on a laptop may never notice this bug. But a homelab owner with containers, VPN endpoints, media servers, and IPv6 enabled could absolutely wind up in the territory where the hash-slot threshold matters. That makes this a good example of a vulnerability that is “low drama” on paper but still relevant to technically advanced users.
The hidden consumer angle
The modern consumer Linux ecosystem is more diverse than it used to be. Many people run lightweight servers on commodity hardware, or use Linux as a router, firewall, or virtual machine host at home. In those cases, a kernel bind bug can have the same practical effect as it would in a small business: a service that starts when it should not, or a service that fails to claim a port because the kernel has become inconsistent about conflict detection.That is why it is a mistake to dismiss networking CVEs as “enterprise only.” The broader the role of the machine, the broader the impact of a port-binding mistake. The issue is especially relevant for users who rely on predictable daemon startup, scripted failover, or service supervision.
The Fix and Why It Fits Stable Kernels
The report says the TCP helperinet_use_bhash2_on_bind already had the correct check, and the fix for this CVE renames it to inet_use_hash2_on_bind and moves it into inet_hashtables.h so UDP can extbook stable-tree patch: small, mechanical, easy to reason about, and directly tied to the misbehavior described in the advisory.This matters because stable kernel maintainers usually want patches that do one thing well and avoid broader semantic changes. A fix that consolidates the decision logic is easier to audit than one that tries to duplicate the logic in another file and hopes both copies stay synchronized. In that sense, the patch is not just correct; it is maintainable.
Why the naming change matters
Renaming the helper frominet_use_bhash2_on_bind to inet_use_hash2_on_bind is more than cosmetic. It signals that the function is no longer a TCP-specific detail but a shared policy check for when the alternate hash should be used during bind operations. That makes the code’s intent clearer and reduces the chance of future protocol-specific drift.Why moving it to a header matters
Moving the helper intoinet_hashtables.h makes it available to UDP without forcing each subsystem to carry its own version of the same logic. That is a maintainability win, but it is also a correctness win because it ensures TCP and UDP use the same criteria. When a security or correctness check is duplicated, divergence is almost inevitable over time. Centralizing the logic is the cleaner answer.Strengths and Opportunities
The strongest thing about this fix is that it resolves a concrete kernel contract failure without disturbing the broader networking stack. It also gives maintainers a reusable helper that can be shared across protocols, which reduces the odds of the same bug pattern reappearing in a different place. In other words, this is not only a patch; it is a cleanup that improves the architecture.- The fix is narrowly scoped.
- It reuses existing TCP logic instead of inventing a new path.
- It addresses both IPv4 and IPv6 wildcard behavior.
- It reduces protocol-specific duplication.
- It is likely to backport cleanly.
- It improves long-term maintainability.
- It strengthens bind semantics under load.
Risks and Concerns
The main concern is underestimation. Because the bug does not obviously look like memory corruption or remote code execution, teams may mentally downgrade it. That would be a mistake, since a bind-conflict bypass can still break service ownership, defeat failover assumptions, and cause operational instability in busy systems.- Patch lag may persist across vendor kernels.
- Dense service environments are more exposed.
- The bug can be silent rather than crashing.
- IPv6 and v4-mapped cases widen the surface.
- Containerized and orchestrated systems may hide the symptom.
- Administrators may misdiagnose the issue as a userspace bug.
- Threshold-dependent behavior is easy to miss in testing.
bind at all. Silent misbinding is often more damaging operationally than an obvious refusal to start.Looking Ahead
The next thing to watch is how quickly downstream vendors fold the fix into their supported kernel lines. Because the issue is narrow and the helper is shared, this should be a relatively straightforward backport for distributors that track stable kernel updates closely. The real determinant of exposure will be patch uptake, not the complexity of the code change.It is also worth watching whether similar hash-threshold logic exists elsewhere in the network stack. Once one protocol path is found to mishandle a wildcard bind under alternate lookup conditions, it is reasonable to ask whether neighboring code has the same class of mismatch. Kernel fixes often become a template for adjacent audits, and this one is a strong candidate for that kind of review.
- Verify whether your vendor kernel includes the fix.
- Check multi-address bind behavior on busy hosts.
- Review any service that depends on exclusive port ownership.
- Pay special attention to IPv6 and v4-mapped wildcard binds.
- Watch for similar threshold-based lookup decisions elsewhere.
Ultimately, CVE-2026-31503 is a reminder that correctness in the Linux networking stack is a security property in its own right. A bind that succeeds when it should fail can be every bit as disruptive as a more dramatic flaw, because it corrupts the assumptions that services, orchestrators, and failover systems build on. The fix is small, the lesson is large, and the practical value lies in getting the patch into the field before the wrong bind turns into the wrong outage.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center