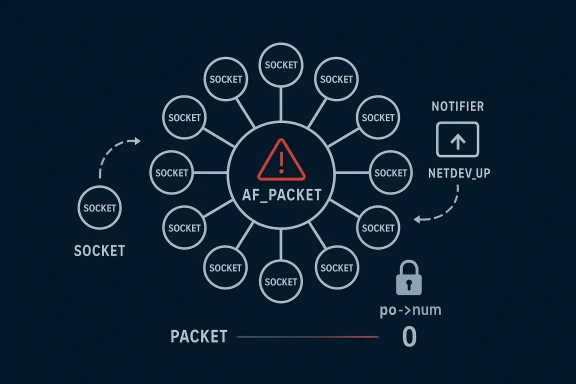
The Linux kernel’s networking stack has a new memory-safety problem on its hands, and this one sits in an especially sensitive place: AF_PACKET fanout teardown. CVE-2026-31504 describes a race in
AF_PACKET fanout is one of those features that rewards performance and flexibility at the cost of complexity. It allows multiple sockets to share packet reception, which is useful in capture, analysis, and load-balancing scenarios. But the more state that is shared, the more careful the kernel has to be about ownership and teardown. The CVE text describes exactly that kind of failure: a socket can be re-linked into a fanout array after release has begun, but the cleanup path does not fully unwind that re-link, so the array can keep a stale pointer.
This matters becaused as a simple logic error in a dead code path. It is a concurrency problem in a live notifier-driven path, which means timing determines whether the flaw appears. That is the worst class of kernel bug from an operator’s perspective: intermittent, hard to reproduce, and capable of turning into a use-after-free if the wrong object is later dereferenced. The file search results underline that networking UAFs are especially sensitive because they mix object lifetime, high concurrency, and hard-to-isolate symptoms.
There is also important context in the kVE process. The kernel documentation notes that CVEs are often assigned once a fix exists and is tied to stable work, and that the project is intentionally cautious about security tracking because almost any kernel bug can become security relevant depending on circumstances. That explains why a targeted race fix like this can receive a CVE even before NVD has enriched it with a final score.
The newly published CVE also appears to have been identified after an additional audit triggered by CVE-2025-38617, which is a reminder that kernel security work is often cumulative. One bug leads maintainers to inspect a nearby lifetime assumption, which turns up another bug in the same subsystem. That is not unusual; in fact, it is one of the most effective ways the kernel community hardens complicated code.
At the center of the problem is a mismatch between the release path and the notifier path.
That re-registration is not harmles, the notifier path can call
The key detail is that
Why
The CVE description makes it clear that
That is a classic kernel hardening move: make the unsafe state impossible instead of trying to clean up after it. It is usually the best fix when the problem is a timing-dependent ownership bug rather than a pure algorithmic mistake. The shorter the race window, the fewer ways the system has to surprise you.
This is why concurrency fixes in the kernel often focus on state visibility rather than just mutex coverage. The lock may be present, but if the wrong field remains stale when another CPU looks, the lock has not fully protected the higher-level invariant.
The danger is compounded by the fact that packet-processing code is hot-path code. Kernel developers are careful not toation where it would damage throughput, so they often rely on narrow invariants and carefully ordered state transitions. That makes fixes like this look deceptively simple: one field change, one window closed, and a race disappears. But the simplicity is the result of a lot of design discipline.
What makes this class of bug especially annoying is that symptoms may not point back to the root cause. Administrators are more likely to see crashes, strange packet behavior, or sporadic instability than a clear message saying “fanout array inconsistency.” The file search results on other networking CVEs make the same general point: operators often experience the aftermath as a system outage, not as a neat security event.
That is why these issues frequently survive until a careful audit or sanitizer-backed review catches them. They depend on timing rather than a single obviously bad pointer assignment. And because the flawed state is transient, conventional testing may miss it unless the system is under stress.
The Linux kernel’s CVE guidance explicitly recognizes this reality: even bugs whose exploitability is not obvious can still merit a CVE once a fix exists. That is the right stance for a codebase where memory safety and availability are inseparable from security posture.
This is the kernel maintenance style operators tend to appreciate. The t a sweeping redesign of packet fanout. It does not alter the entire notifier model. It simply removes the stale precondition that made the race possible. Narrow fixes like this are typically easier to review, easier to backport, and less likely to trigger unrelated regressions.
The patch also preserves the existing behavioral model. That matters because performance-sensitive networking code often carries implicit expectations about how membership and packet distribution work. A fix that breaks fanout semantics would be worse than the bug in some environments. Here, the goal is not to change how AF_PACKET fanout behaves; it is to make teardown honest about the object’s state before another CPU can act on it.
That is good news for downstream users, because a small fix has a much better chance of appearing in long-term support kernels quickly. The practical challenge is not understanding the bug once the description is available; it is confirming whether a vendor kernel or enterprise LTS branch has already absorbed the patch.
In security terms, that is preferable to making the cleanup path more complicated. The fewer places that need to reason about partially torn-down sockets, the fewer future mistakes the subsystem can make. That is exactly the kind of change maintainers like to see in hot networking code.
That broader lesson shows up repeatedly in kernel CVEs. The details vary, but the principle does not. Make the object’s lifecycle obvious, or make the dangerous intermediate state impossible.
The risk grows when the kernel is used in appliances, virtualized hosts, or specialized network services. In those environments, a kernel crash or memory corruption in packet-processing code can have an outsized blast radius. A single host failure may cascade into monitoring blind spots, failed packet capture, service interruption, or cluster instability.
This is the kind of issue that may never affect a desktop user, but can absolutely affect a production network node. That discrepancy is why enterprise triage should be more aggressive than consumer triage. The same bug can be background noise on one machine and a serious outage trigger on another.
Even if you do not think of your environment as “security-sensitive,” a dangling pointer in kernel networking code can still produce downtime. And downtime in enterprise settings is a business event, not just a technical inconvenience.
That does not mean consumer systems are immune. It means the operational blast radius is usually smaller. In kernel security, that distinction matters a lot, because the same code can have radically different consequences depending on deployment model.
That policy is useful here because it explains why a race in packet-release logic is being surfaced as a CVE at all. The bug is not being framed as a theoretical concern with no real-world effect. It is being treated as something that could matter operationally, especially in the kinds of environments where packet fanout is actually used.
It also helps explain the current NVD status. The record notes that NVD assessment was not yet provided at publication time, which is common early in the lifecycle of kernel disclosures. In practice, administrators should not wait for enrichment if the upstream description is already specific enough to identify affected systems.
The second thing to watch is whether this CVE prompts a broader audit of socket teardown and notifier interactions in adjacent networking paths. Once a race like this is found, it often points to a wider pattern: stale state visible to asynchronous callbacks, especially during device lifecycle transitions. That is fertile ground for more hardening work.
The third thing to watch is whether vendors classify the issue as a straightforward stability fix or treat it as a higher-priority security update. Given the object-lifetime implications, the latter would be the safer reading. The file search material strongly suggests that this is not a mere nuisance bug but a real kernel memory-safety risk in a live packet-processing path.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
packet_release where a concurrent NETDEV_UP event can re-register a socket into a fanout group after the release path has already started, leaving a dangling pointer behind in the fanout array. The fix is small but important: zero po->num while bind_lock is still held, closing the window before NETDEV_UP can relink the socket. The issue is already published in NVD and the Microsoft Security Response Center references the upstream kernel fix, which means defenders should treat it as a real patch-management item rather than an academic edge case. x kernel networking bugs are often deceptive. A flaw may look like a narrow race in a subsystem most users never think about, yet still carry real operational consequences because networking code sits on the critical path of so many workloads. That is especially true in packet-processing code, where lifetime rules, notifier callbacks, and fanout or bonding logic can all interact in ways that are hard to test exhaustively.AF_PACKET fanout is one of those features that rewards performance and flexibility at the cost of complexity. It allows multiple sockets to share packet reception, which is useful in capture, analysis, and load-balancing scenarios. But the more state that is shared, the more careful the kernel has to be about ownership and teardown. The CVE text describes exactly that kind of failure: a socket can be re-linked into a fanout array after release has begun, but the cleanup path does not fully unwind that re-link, so the array can keep a stale pointer.
This matters becaused as a simple logic error in a dead code path. It is a concurrency problem in a live notifier-driven path, which means timing determines whether the flaw appears. That is the worst class of kernel bug from an operator’s perspective: intermittent, hard to reproduce, and capable of turning into a use-after-free if the wrong object is later dereferenced. The file search results underline that networking UAFs are especially sensitive because they mix object lifetime, high concurrency, and hard-to-isolate symptoms.
There is also important context in the kVE process. The kernel documentation notes that CVEs are often assigned once a fix exists and is tied to stable work, and that the project is intentionally cautious about security tracking because almost any kernel bug can become security relevant depending on circumstances. That explains why a targeted race fix like this can receive a CVE even before NVD has enriched it with a final score.
The newly published CVE also appears to have been identified after an additional audit triggered by CVE-2025-38617, which is a reminder that kernel security work is often cumulative. One bug leads maintainers to inspect a nearby lifetime assumption, which turns up another bug in the same subsystem. That is not unusual; in fact, it is one of the most effective ways the kernel community hardens complicated code.
 What ting
What ting
At the center of the problem is a mismatch between the release path and the notifier path. packet_release drops a socket from one set of bookkeeping structures, but it does not zero po->num while holding bind_lock. That leaves the socket looking, for a short time, as though it is still bound to the device. If a concurrent NETDEV_UP notifier has already located the socket in sklist, it can re-register the socket into the fanout group before the release path fully finishes its cleanup.That re-registration is not harmles, the notifier path can call
__fanout_link(sk, po), which adds the socket back into f->arr and increments f->num_members, but does not increment f->sk_ref. In other words, the socket is now represented in the fanout array without the matching reference-count protection one would expect from a healthy ownership transition. That is exactly how a stale pointer becomes a use-after-free hazard.The key detail is that
fanout_release does not know this late-arriving re-registration. Once the release path has moved past the point where it believed the socket had been detached, the extra link can survive long enough for another code path to touch freed memory later. The bug is subtle because the failure is not immediate; it is a delayed consequence of a tiny race window.Why po->num matters
The CVE description makes it clear that po->num whether the notifier believes the socket is still eligible to be linked. If po->num remains non-zero after release starts, then NETDEV_UP can still treat the socket as active enough to re-enter the fanout logic. Clearing it under bind_lock changes the state early enough to stop the race from forming.That is a classic kernel hardening move: make the unsafe state impossible instead of trying to clean up after it. It is usually the best fix when the problem is a timing-dependent ownership bug rather than a pure algorithmic mistake. The shorter the race window, the fewer ways the system has to surprise you.
- The socket remains eligible longer than intended.
- The notifier can re-link it after release begins.
- The fanout array may retain a dangling reference.
- The reference count does not get the expected reinforcement.
- The resulting bug is a use-after-free candidate.
Why the notifier is the danger point
NETDEV_UP is the point where a device transition can ctack to revisit socket state. In a healthy design, that is useful and predictable. In a buggy one, it becomes a window for re-entering code that assumed teardown was already finished. The issue here is not that the notifier is inherently wrong; it is that teardown left the socket looking live long enough for the notifier to make the wrong decision.This is why concurrency fixes in the kernel often focus on state visibility rather than just mutex coverage. The lock may be present, but if the wrong field remains stale when another CPU looks, the lock has not fully protected the higher-level invariant.
Why Fanout Bugs Are Hard
Fanout code exists to balance packets across multiple consumers, which means it is inherently stateful. A socket can belong to a group, leave a group, and be reintroduced under different conditions depending on device state. That makes the teardown path just as important as the steady-state path, because it has to preserve the integrity of the membership array while concurrent events are still possible.The danger is compounded by the fact that packet-processing code is hot-path code. Kernel developers are careful not toation where it would damage throughput, so they often rely on narrow invariants and carefully ordered state transitions. That makes fixes like this look deceptively simple: one field change, one window closed, and a race disappears. But the simplicity is the result of a lot of design discipline.
What makes this class of bug especially annoying is that symptoms may not point back to the root cause. Administrators are more likely to see crashes, strange packet behavior, or sporadic instability than a clear message saying “fanout array inconsistency.” The file search results on other networking CVEs make the same general point: operators often experience the aftermath as a system outage, not as a neat security event.
The shape of the race
The race is narrow, but it is real.packet_releaseed its release sequence. The device has to be in a state whereNETDEV_UP` can run the notifier logic. The socket has to still appear bound enough for the re-registration path to think it should be linked again. When those conditions overlap, the bug becomes reachable.That is why these issues frequently survive until a careful audit or sanitizer-backed review catches them. They depend on timing rather than a single obviously bad pointer assignment. And because the flawed state is transient, conventional testing may miss it unless the system is under stress.
- Timing-sensitive failures evade ordinary functional tests.
- State visibility matters as much as lock presence.
- Race windows can be smaller than human intuition expects.
- Re-registration logic is especially risky during teardown.
- Reference-count mismatches often surface later, not immediately.
Why this is not “just” a reliability bug
It would be easy to dismiss the issue as an availability flaw, since the immediate description emphasizes a dangling pointer rather than a proven exploit chain. But that is too casual for a kernel networking UAF. In privileged code, use-after-free conditions are serious regardless of whether an attacker has already turned them into code execution.The Linux kernel’s CVE guidance explicitly recognizes this reality: even bugs whose exploitability is not obvious can still merit a CVE once a fix exists. That is the right stance for a codebase where memory safety and availability are inseparable from security posture.
How the Fix Works
The fix described in the CVE is intentionally surgical. It setspo->num to zero in packet_release while bind_lock is held. That is enough to prevent a concurrent NETDEV_UP notifier from deciding that the socket is still a candidate for re-linking. Once that state is gone, the notifier cannot reintroduce the socket into the fanout array through the stale path.This is the kernel maintenance style operators tend to appreciate. The t a sweeping redesign of packet fanout. It does not alter the entire notifier model. It simply removes the stale precondition that made the race possible. Narrow fixes like this are typically easier to review, easier to backport, and less likely to trigger unrelated regressions.
The patch also preserves the existing behavioral model. That matters because performance-sensitive networking code often carries implicit expectations about how membership and packet distribution work. A fix that breaks fanout semantics would be worse than the bug in some environments. Here, the goal is not to change how AF_PACKET fanout behaves; it is to make teardown honest about the object’s state before another CPU can act on it.
Why the fix is likely backport-friendly
Kernel stable maintainers prefer changes that are obviously correct and limited in scope. The documentation on stable rules makes clear that fixes should already exist upstream, be small, and resolve a real bug. This kind of release-path state correction is exactly the sort of patch that stable trees usually prefer.That is good news for downstream users, because a small fix has a much better chance of appearing in long-term support kernels quickly. The practical challenge is not understanding the bug once the description is available; it is confirming whether a vendor kernel or enterprise LTS branch has already absorbed the patch.
Why the fix is conceptually clean
The best kernel fixes do not fight the race after it has already happened. They remove the false assumption that made the race possible. That is what zeroingpo->num accomplishes here. It changes the observable state before the notifier path can observe the old one.In security terms, that is preferable to making the cleanup path more complicated. The fewer places that need to reason about partially torn-down sockets, the fewer future mistakes the subsystem can make. That is exactly the kind of change maintainers like to see in hot networking code.
- The unsafe re-registration condition disappears earlier.
- The notifier loses the stale signal it depended on.
- The fanout array is less likely to retain a dangling entry.
- Cleanup becomes more deterministic.
- Backporting should be straightforward in principle.
Why this resembles other kernel hardening wins
A lot of kernel hardening is really about making object state transitions less ambiguous. Whether the issue is a race in a receive path, a stale metadata reference, or a broken teardown condition, the pattern is the same: if another thread can see the object in the wrong state, the object is already too risky.That broader lesson shows up repeatedly in kernel CVEs. The details vary, but the principle does not. Make the object’s lifecycle obvious, or make the dangerous intermediate state impossible.
Enterprise Impact
For enterprise operators, the most important question is not whether the bug is elegant. It is whether it can disrupt production. In that sense, this one deserves attention. AF_PACKET and fanout are used in capture, forwarding, analysis, and high-performance packet handling environments, which means the vulnerability can matter in systems that are explicitly tuned for networking workloads.The risk grows when the kernel is used in appliances, virtualized hosts, or specialized network services. In those environments, a kernel crash or memory corruption in packet-processing code can have an outsized blast radius. A single host failure may cascade into monitoring blind spots, failed packet capture, service interruption, or cluster instability.
This is the kind of issue that may never affect a desktop user, but can absolutely affect a production network node. That discrepancy is why enterprise triage should be more aggressive than consumer triage. The same bug can be background noise on one machine and a serious outage trigger on another.
Why operators should not ignore fanout
Fanout is not a fringe feature. It is a deliberate scaling mechanism for packet consumers, and that means it shows up in workloads that care about throughput, observability, and load distribution. If you use AF_PACKET fanout in production, this CVE is directly relevant.Even if you do not think of your environment as “security-sensitive,” a dangling pointer in kernel networking code can still produce downtime. And downtime in enterprise settings is a business event, not just a technical inconvenience.
- Packet inspection stacks may be exposed.
- Capture pipelines may see instability.
- High-throughput hosts can amplify the impact.
- Virtualized infrastructure may inherit the problem indirectly.
- Incident response becomes harder when crashes are intermittent.
Enterprise vs. consumer exposure
Consumer desktop systems are less likely to use AF_PACKET fanout in the first place. For them, the risk may be lower unless they run custom networking software, lab tooling, or packet-capture workloads. Enterprise systems, by contrast, are more likely to have specialized network services, monitoring agents, or virtualization stacks that make the vulnerable code path more realistic.That does not mean consumer systems are immune. It means the operational blast radius is usually smaller. In kernel security, that distinction matters a lot, because the same code can have radically different consequences depending on deployment model.
Relationship to Linux CVE Policy
One of the reasons kernel CVEs can seem surprising is that the Linux project is deliberately conservative about assigning them. The kernel documentation notes that CVEs are often assigned after fixes are available, and that the project generally tracks bugs once the remediation exists and is tied to stable work. That means the CVE count reflects the project’s cautious view of security relevance, not just a narrow definition of exploitability.That policy is useful here because it explains why a race in packet-release logic is being surfaced as a CVE at all. The bug is not being framed as a theoretical concern with no real-world effect. It is being treated as something that could matter operationally, especially in the kinds of environments where packet fanout is actually used.
It also helps explain the current NVD status. The record notes that NVD assessment was not yet provided at publication time, which is common early in the lifecycle of kernel disclosures. In practice, administrators should not wait for enrichment if the upstream description is already specific enough to identify affected systems.
Why NVD lag does not murity teams sometimes misread the absence of a final score as a sign that they can wait. That is a mistake, especially for kernel bugs. The technical description is usually the better guide early on, because it tells you whether the flaw is reachable in your deployment and whether the fix is narrow enough to backport safely.
When the bug lives in networking code, and especially in a use-after-free path, the prudent assumption is that patching is worth doing even before scoring is finalized. The lack of enrichment is an administrative detail, not a risk signal.- Upstream fixes often arrive before vendor advisories.
- NVD enrichment can lag the original disclosure.
- Kernel CVEs may be assigned cautiously but still matter.
- The presence of a fix is often the strongest triage clue.
- Deployment context should drive urgency more than raw labels.
Strengths and Opportunities
The good news is that this is the kind of bug kernel maintainers can usually fix cleanly. The patch is narrow, the behavior change is minimal, and the underlying lesson is easy to reason about once the race is explained. That gives downstream vendors a decent chance of landing it quickly and without drama. It also gives operators a concrete reason to audit packet fanout usage and review their kernel patch levels.- The fix is small and targeted.
- The race condition is easy to explain to maintainers.
- The change should be relatively backport-friendly.
- The bug points to a clear state-visibility failure.
- Operators can map exposure by checking AF_PACKET fanout usage.
- The issue reinforces good lifecycle discipline in networking code.
- The upstream path is already public, which helps validation.
Risks and Concerns
The biggest concern is that this kind of bug can remain hidden in plain sight for a long time. If a system only rarely hits theNETDEV_UP and release overlap, the problem may look like random instability instead of a kernel lifetime violation. That makes incident response harder, and it increases the odds that organizations will underestimate the issue until they see a crash in production.- Older vendor kernels may lag behind upstream.
- The race may be intermittent and hard to reproduce.
- Symptoms may be misattributed to generic network instability.
- Packet-capture and monitoring systems may be especially exposed.
- Systems using fanout in appliances or virtualized stacks may be vulnerable.
- Reference-count bugs can lead to broader memory-safety fallout.
- A “no CVSS yet” status can create false confidence.
Looking Ahead
The first thing to watch is backport coverage. In kernel security, the fix in upstream git matters, but the version that actually ships in vendor kernels matters more. Enterprises should be checking their supported LTS branches, not just the public disclosure, because that is where exposure is determined in practice.The second thing to watch is whether this CVE prompts a broader audit of socket teardown and notifier interactions in adjacent networking paths. Once a race like this is found, it often points to a wider pattern: stale state visible to asynchronous callbacks, especially during device lifecycle transitions. That is fertile ground for more hardening work.
The third thing to watch is whether vendors classify the issue as a straightforward stability fix or treat it as a higher-priority security update. Given the object-lifetime implications, the latter would be the safer reading. The file search material strongly suggests that this is not a mere nuisance bug but a real kernel memory-safety risk in a live packet-processing path.
- Confirm whether your kernel build includes the
po->numzeroing fix. - Check whether AF_PACKET fanout is used in production workloads.
- Review vendor advisories for LTS and enterprise branches.
- Watch for follow-up cleanup in nearby notifier-driven paths.
- Prioritize systems where packet capture or analysis is business-critical.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center