Linux has published CVE-2026-31510 for a Bluetooth L2CAP bug that can crash the kernel when
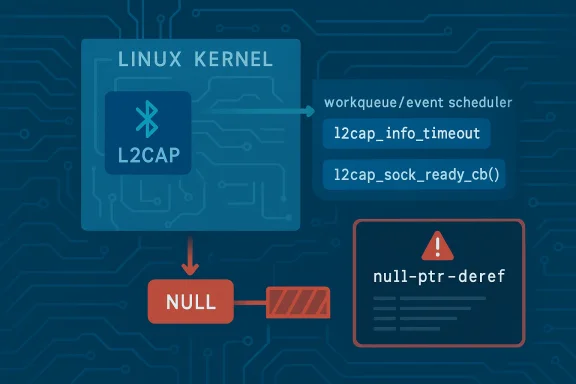
At a glance, this is the kind of kernel flaw that sounds almost trivial: a missing NULL check before dereferencing a pointer. But in the Linux kernel, especially in networking code that runs in asynchronous workqueues, trivial-looking bugs are often the ones that hurt most because they are easy to reach and hard to safely ignore. The CVE description shows the crash surfaced under KASAN with a null-ptr-deref in a Bluetooth workqueue path, which is exactly the sort of failure that kernel sanit expose early.
Bluetooth L2CAP is not a niche toy subsystem. It is the Logical Link Control and Adaptation Protocol layer that helps structure Bluetooth traffic, and it sits below many higher-level Bluetooth services that users, laptops, headsets, and embedded devices rely on. That matters because a bug in this layer can affect not just a single application but the reliability of an entire Bluetooth stack. The kernel is dealing with connection state, socket objects, timing callbacks, and deferred work, which multiplies the chances that a stale or absent pointer becomes a system-wide stability problem.
The record also shows that the fault happened in a workqueue named
Linux kernel CVEs are often assigned conservatively, and the project explicitly says that many are issued once a fix is available and attached to stable work. That context matters here because the presence of a CVE does not necessarily mean dramatic exploitability; it often means the maintainers believe the bug is worth tracking as a security-relevant reliability issue. In a kernel, reliability and security overlap more often than people expect, because a reliable crash in privileged code is still a denial-of-service vector.
The practical risk here is that Bluetooth code often runs in environments where reliability matters more than people realize. Consumer laptops, USB Bluetooth adapters, industrial gateways, automotive systems, and embedded appliances all depend ehavior in different ways. A kernel panic in that stack may be annoyingly intermittent on a desktop, but in a managed device fleet it can become a support burden and a reboot loop. Small kernel crashes rarely stay small once they reach production.
The KASAN trace is especially telling. Sanitizers do not prove exploitability, but they do prove that the code touched memory it should never have touched. Here, the trace lands in
Historically, the Linux kernel has treated these sorts of bugs as security-relevant because they can be triggered through normal control flows and because they affect privileged execution paths. The kernel documentation makes clear that CVEs are often assigned broadly for fixes that may have security implications, even when the immediate symptom is “just” a crash. That philosophy is sensible: in kernel space, a crash is frequently the visible edge of a deeper assumption failure.
The call trace matters because it shows the invalid access was not random. The workqueue path came from
A NULL dereference in kernel space is usually classified first as an availability issue. The system may panic, wedge a subsystem, or at minimum terminate the offending execution path. But a crash in the Bluetooth stack can still be security-relevant if an attacker can provoke it through pairing, connection setup, or device interaction. Even when the immediate outcome is denial of service rather than code execution, denial of service against the kernel is still a meaningful security concern. ([kernel.org](CVEs — The Linux Kernel documentation NVD had not yet assigned a CVSS score when the record was published does not reduce the seriousness. NVD often lags the initial CVE publication, and the Linux kernel community itself does not rely on NVD to decide whether a fix should be tracked. The important fact is that the fix exists, the issue has been documented, and downstream consumers now have a concrete identifier to work from.
What makes this issue interesting is the surrounding context.
The stack trace places the crash inside the Bluetooth connection-start sequence, which suggests the fault may be reachable through a connection timing or teardown interaction rather than direct packet corruption. That is important because timing bugs can be more realistic in the field than they appear in a lab. Device pairing, signal loss, reconnection attempts, and adapter resets all create timing windows where callback state can become stale.
There is also a broader kernel engineering point here: defensive null checking is not a substitute for correct ownership, but it is a necessary last line of defense. Kernel code cannotk will be invoked in the most favorable state. In a subsystem as asynchronous as Bluetooth, belt-and-suspenders validation is not overengineering; it is survival.
Enterprise impact is more nuanced. Many managed fleets use Bluetooth for specialized devices, conferencing hardware, or endpoint peripherals, and some embedded or industrial deployments rely on Bluetooth in ways that are easy to overlook in asset inventories. If a fleet relies on Bluetooth-enabled workflows, a kernel crash in the L2CAP path can ripple out into support tickets, device reconnect loops, or degraded endpoint trust.
The risk profile also depends on how much Bluetooth is actually used. Some workstations almost never touch it; others depend on it daily. That means exposure is not well estimated by kernel version alone. Administrators need to know not just whether the vulnerable code is present, but whether their users or devices are likely to exercise it. Version is necessary; workload context is decisive.
The CVE record’s publication through Microsoft’s Security Updeminder that Linux vulnerabilities increasingly matter to mixed-platform enterprises, not just Linux-only shops. Many Windows-centric organizations still run Linux in infrastructure, virtualization, developer endpoints, or edge devices. When one of those systems carries a kernel Bluetooth bug, it is part of the same enterprise risk conversation as any other endpoint reliability issue.
This kind of fix matters because it keeps the fault from becoming a mystery later. Without the check, users may see sporadic panics that are hard to tie back to Bluetooth. With the check, the kernel protects itself from a dangerous assumption and gives maintainers a much clearer boundary around the valid states of the callback path. That clarity is valuable both for patchingreview.
It also matters because Bluetooth bugs can have a long tail. Even when a desktop user rarely notices the stack, the same code may be used continuously in an embedded or industrial deployment. Stable backports therefore matter as much as upstream fixes. A kernel bug that lingers in an LTS branch is not an academic issue; it is a support and reliability risk for years.
There is a broader lesson here for subsystem maintainers too. Any callback that crosses a timeout, queue, or connection transition should be treateaph may have changed underneath it. That means pointer checks, state checks, and conservative exits are not just defensive coding habits; they are part of the reliability contract. Asynchronous code is where assumptions go to die.
There is also the general risk that timeouts and deferred work introduce repeatability problems. A crash that happens in a workqueue may not reproduce reliably on every boot or every device. That does not make it less serious; it just makes it more annoying to diagnose. Kernel bugs that are annoying to reproduce are often the ones that live longest in production.
The second thing to watch is whether similar pointer-validity assumptions show up in nearby L2CAP callbacks or other Bluetooth state-machine code. When one asynchronous path fails because it trusted a pointer too long, it is often worth asking whether the same pattern exists in sibling routines. The goal is not to panic; it is to prevent the next edge-caseaces.
The third thing to watch is downstream visibility. Microsoft’s Security Update Guide already reflects the CVE, which helps mixed environments keep track of Linux security events. That matters because enterprises increasingly rely on centralized advisory workflows rather than distro-specific mailing lists alone. The more clearly the issue is tracked, the less likely it is to fall through the cracks.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
l2cap_sock_ready_cb touches a sk pointer without first checking whether it is NULL. The published record includes a KASAN-backed null-pointer dereference trace and ties the issue to an l2cap_info_timeout workqueue path, which makes this look like a real kernel safety defect rather than a theoretical edge case. Microsoft’s update guide has already picked up the CVE, and the Linux kernel’s own CVE process notes that fixes are typically assigned once they are already in the stable pipeline. //www.kernel.org/doc/html/latest/process/cve.html)
 Overview
Overview
At a glance, this is the kind of kernel flaw that sounds almost trivial: a missing NULL check before dereferencing a pointer. But in the Linux kernel, especially in networking code that runs in asynchronous workqueues, trivial-looking bugs are often the ones that hurt most because they are easy to reach and hard to safely ignore. The CVE description shows the crash surfaced under KASAN with a null-ptr-deref in a Bluetooth workqueue path, which is exactly the sort of failure that kernel sanit expose early.Bluetooth L2CAP is not a niche toy subsystem. It is the Logical Link Control and Adaptation Protocol layer that helps structure Bluetooth traffic, and it sits below many higher-level Bluetooth services that users, laptops, headsets, and embedded devices rely on. That matters because a bug in this layer can affect not just a single application but the reliability of an entire Bluetooth stack. The kernel is dealing with connection state, socket objects, timing callbacks, and deferred work, which multiplies the chances that a stale or absent pointer becomes a system-wide stability problem.
The record also shows that the fault happened in a workqueue named
events, during l2cap_info_timeout, while the call trace passed through l2cap_conn_start and then l2cap_sock_ready_cb. That combination suggests the bug is not in some exotic path that only exists in lab conditions. Instead, it lives in a normal lifecycle transition where the kernel is tryingize L2CAP state. In practice, those are exactly the moments where state assumptions are most fragile.Linux kernel CVEs are often assigned conservatively, and the project explicitly says that many are issued once a fix is available and attached to stable work. That context matters here because the presence of a CVE does not necessarily mean dramatic exploitability; it often means the maintainers believe the bug is worth tracking as a security-relevant reliability issue. In a kernel, reliability and security overlap more often than people expect, because a reliable crash in privileged code is still a denial-of-service vector.
Background
Bluetooth in the Linux kernel is a layered system, and L2CAP sits in the middle of that stack as a key transport abstraction. That makes it a natural place for lifecycle mismatches to appear, because socket state, protocol state, and deferred callback state all intersect there. When one of those layers assumes another is already valid, a NULL dereference can happen even if the code path otherwise looks “safe” at first glance.The practical risk here is that Bluetooth code often runs in environments where reliability matters more than people realize. Consumer laptops, USB Bluetooth adapters, industrial gateways, automotive systems, and embedded appliances all depend ehavior in different ways. A kernel panic in that stack may be annoyingly intermittent on a desktop, but in a managed device fleet it can become a support burden and a reboot loop. Small kernel crashes rarely stay small once they reach production.
The KASAN trace is especially telling. Sanitizers do not prove exploitability, but they do prove that the code touched memory it should never have touched. Here, the trace lands in
kasan_byte_accessible after lock_sock_nested during `l2cap_sockeans the kernel was in a lock-sensitive socket operation when the invalid access occurred. That is a strong hint that the bug is about state ordering and pointer validity, not about a wild memory overwrite or a complicated race.Historically, the Linux kernel has treated these sorts of bugs as security-relevant because they can be triggered through normal control flows and because they affect privileged execution paths. The kernel documentation makes clear that CVEs are often assigned broadly for fixes that may have security implications, even when the immediate symptom is “just” a crash. That philosophy is sensible: in kernel space, a crash is frequently the visible edge of a deeper assumption failure.
Why NULL checks still matter in 2026
It is easy to dismiss a missing NULL check as old-fashioned, but modern kernel code is full of deferred execution, reference managemrship. Those patterns make “pointer exists” a temporal statement, not a permanent one. A pointer can be valid when captured, invalid by the time the callback fires, and missing entirely when a connection sequence aborts early. That timing gap is where bugs live.Why Bluetooth bugs deserve attention
Bluetooth is often treated as a convenience feature, but it is now deeply embedded in consumer and enterprise workflows. Headsets, keyboards, peripherals, low-power sensors, and phone tethering all depend on it. If the kernel Bluetooth stack becomes unstable, users do not merely lose a feature; they may lose input devices, audio, or device connectivity in ways that are difficult to diagnose.What the Vulnerability Does
The essence of the bug is simple: befonter insidel2cap_sock_ready_cb, the kernel should verify that it is not NULL. The published description says exactly that. The crash trace suggests that the callback was reached in a context where the socket pointer had not been safely established, and the code continued anyway. That is the classic pattern for a null-ptr-deref in asynchronous networking code.The call trace matters because it shows the invalid access was not random. The workqueue path came from
l2cap_info_timeout, then flowed into nd finally hit l2cap_sock_ready_cb. In other words, the code was performing a connection-state transition, not handling a malformed packet from nowhere. That makes the issue especially important from an operations perspective, because timeout-driven paths are notoriously hard to reproduce and can show up under load, latency, or device churn.A NULL dereference in kernel space is usually classified first as an availability issue. The system may panic, wedge a subsystem, or at minimum terminate the offending execution path. But a crash in the Bluetooth stack can still be security-relevant if an attacker can provoke it through pairing, connection setup, or device interaction. Even when the immediate outcome is denial of service rather than code execution, denial of service against the kernel is still a meaningful security concern. ([kernel.org](CVEs — The Linux Kernel documentation NVD had not yet assigned a CVSS score when the record was published does not reduce the seriousness. NVD often lags the initial CVE publication, and the Linux kernel community itself does not rely on NVD to decide whether a fix should be tracked. The important fact is that the fix exists, the issue has been documented, and downstream consumers now have a concrete identifier to work from.
The shape of the failure
This is not the sort of bug that needs a deep exploit chain to matter. The kernel touched a pointer that should have been validated first, and the resulting failure was immediate enough for KASAN to flag it. That is usually enough to justify urgent patching on systems that use Bluetooth at all. The shorter the causal chain, the more seriously operators should take it.Why a workqueue path is important
Workqueue paths are often more fragile than direct call paths because they are deferred, scheduled, and separated from the original event that created the work. By the time the callback runs, the world may have changed. That is why pointer validity, object lifetime, and cleanup order are such recurring sourcesl.Technical Analysis
The fix described in the CVE is narrow: check whethersk is NULL before using it. Narrow fixes are not inherently boring; in fact, they are often the best kind of kernel fix because they reduce regression risk while directly addressing the fault. A one-line logic change can eliminate an entire class of crash without perturbing the rest of the subsystem.What makes this issue interesting is the surrounding context.
l2cap_sock_ready_cb sounds like a callback that runs when a socket is ready, but callbacks in the kernel often sit on top of subtle object lifetime assumptions. If the socket has already been torn down, or if the state machine has moved on, the callback may still fire while the underlying object is gone or partially initialized. That is the sort of edge case that unit tests often miss but sanitiorg]The stack trace places the crash inside the Bluetooth connection-start sequence, which suggests the fault may be reachable through a connection timing or teardown interaction rather than direct packet corruption. That is important because timing bugs can be more realistic in the field than they appear in a lab. Device pairing, signal loss, reconnection attempts, and adapter resets all create timing windows where callback state can become stale.
There is also a broader kernel engineering point here: defensive null checking is not a substitute for correct ownership, but it is a necessary last line of defense. Kernel code cannotk will be invoked in the most favorable state. In a subsystem as asynchronous as Bluetooth, belt-and-suspenders validation is not overengineering; it is survival.
KASAN’s role
KASAN’s report is valuable because it transforms a potential hidden crash into a reproducible indicator. The trace includes the exact low address range touched by the invalid access and pins the fault to the specific callback path. That sort of evidence is what lets maintainers make a small, targeted fix with confidence.Why the bug is likely backport-friendly
Because the fix is a straightforward NULL check, it should be easy for stable maintainers and vendors to backport to supported kernel streams. That matters a great deal in the Linux ecosystem, where most users are not running the bleeding-edge tree. A safe, surgical patch is far more likely to reach shipping systems quickly than a large structural rework.- The fix is small and easy to audit.
- The crash is tied to a concrete call trace.
- The likely regression risk is low.
- The symptom is easy to understand for operators.
- The patch should be simple to backport.
- The issue reinforces attention to socket lifetime checks.
Impact on Consumers and Enterprises
For consumers, the immediate effect is usually inconvenience rather than catastrophe. A laptop Bluetooth stack crash can mean lost audio, broken keyboards, dead peripherals, or a kernel panichard enough. Most home users will simply want their distro’s next kernel update, but the underlying lesson is that even “peripheral” subsystems can destabilize the whole machine.Enterprise impact is more nuanced. Many managed fleets use Bluetooth for specialized devices, conferencing hardware, or endpoint peripherals, and some embedded or industrial deployments rely on Bluetooth in ways that are easy to overlook in asset inventories. If a fleet relies on Bluetooth-enabled workflows, a kernel crash in the L2CAP path can ripple out into support tickets, device reconnect loops, or degraded endpoint trust.
The risk profile also depends on how much Bluetooth is actually used. Some workstations almost never touch it; others depend on it daily. That means exposure is not well estimated by kernel version alone. Administrators need to know not just whether the vulnerable code is present, but whether their users or devices are likely to exercise it. Version is necessary; workload context is decisive.
The CVE record’s publication through Microsoft’s Security Updeminder that Linux vulnerabilities increasingly matter to mixed-platform enterprises, not just Linux-only shops. Many Windows-centric organizations still run Linux in infrastructure, virtualization, developer endpoints, or edge devices. When one of those systems carries a kernel Bluetooth bug, it is part of the same enterprise risk conversation as any other endpoint reliability issue.
Consumer-facing symptoms
The user will not necessarily see a dramatic security warning. More often, the experience is messy and ordinary: a device disconnects, audio cuts out, pairing fails, or the system becomes unstable after a Bluetooth event. That makes the bug ee, which is exactly why kernel maintenance policies should treat it seriously.Enterprise-facing symptoms
In managed environments, the problem may appear as unstable peripherals, odd logs around Bluetooth reconnect behavior, or rare crashes that are difficult to reproduce on demand. Those are the sorts of incidents that waste engineering time because they look like flaky hardware until someone traces them back into the kernel. The most expensive crashes are often the ones nobody sees twice the same way.Why the Fix Matters
The most encouraging part of this CVE is that the fix is so direct. By checkingsk before use, the kernel converts an unsafe assumption into an explicit guardrail. That is exactly what mature kernel maintenance is supposed to do: preserve the intended behavior when the state is valid and fail safely when it is not.This kind of fix matters because it keeps the fault from becoming a mystery later. Without the check, users may see sporadic panics that are hard to tie back to Bluetooth. With the check, the kernel protects itself from a dangerous assumption and gives maintainers a much clearer boundary around the valid states of the callback path. That clarity is valuable both for patchingreview.
It also matters because Bluetooth bugs can have a long tail. Even when a desktop user rarely notices the stack, the same code may be used continuously in an embedded or industrial deployment. Stable backports therefore matter as much as upstream fixes. A kernel bug that lingers in an LTS branch is not an academic issue; it is a support and reliability risk for years.
There is a broader lesson here for subsystem maintainers too. Any callback that crosses a timeout, queue, or connection transition should be treateaph may have changed underneath it. That means pointer checks, state checks, and conservative exits are not just defensive coding habits; they are part of the reliability contract. Asynchronous code is where assumptions go to die.
What the fix likely prevents
The obvious win is avoidance of the immediate null-ptr-deref. But the less obvious gain is that the fix likely prevents follow-on instability in adjacent code pathn executed after the bad dereference. In kernel networking, once a callback is in a bad state, the damage often spreads faster than the original bug seems to justify.Why minimalism is a strength
Kernel security patches are often strongest when they are boring. A small conditional is easier to audit than a redesign, easier to backport than a refactor, and less likely to introduce new surprises. This CVE appears to fit that ideal pattern.Strengths and Opportunities
This CVE is a good example of how Linux security work can improve robustness with very limited code churn. The issue is specific, the fix is clear, and the operational meaning is easy to explain to both consumers and administrators. That combination makes it a good candidate for fast downstream handling and a useful reminder to review nearby Bluetooth code for similar lifetime assumptions.- The fix is narrow and auditable.
- The crash trace is concrete and reproducible.
- The patch should be stable-backport friendly.
- The bug highlights callback lifetime discipline.
- Operators get a clear reason to patch kernel Bluetooth paths.
- The issue can prompt adjacent code review in iven discovery improves early bug detection.
Risks and Concerns
The biggest concern is underestimation. Because the bug is a null dereference rather than a flashy memory corruption primitive, it may be treated as “just a crash” and pushed down the priority list. That would be a mistake, because kernel crashes in a reachable subsystem can still mean downtime, failed peripherals, and possibly a denial-of-service condition.- The bug may be dismissed as a mere stability issue.
- Repeated Bluetootrigger the crash path**.
- Vendor backports may arrive later than upstream fixes.
- Some fleets may not know they use the affected path.
- Consumers may not realize Bluetooth instability is kernel-level.
- Support teams may misattribute symptoms to hardware.
- Patch gaps in LTS kernels can prolong exposure.
There is also the general risk that timeouts and deferred work introduce repeatability problems. A crash that happens in a workqueue may not reproduce reliably on every boot or every device. That does not make it less serious; it just makes it more annoying to diagnose. Kernel bugs that are annoying to reproduce are often the ones that live longest in production.
Looking Ahead
The immediate next step is straightforward: watch for kernel updates that carry the fix into the stable branches your systems actually use. Because the upstream remedy is a small null check, this should be one of the easier Bluetooth-related CVEs for vendors to backport. But the real-world timeline will depend on distro cadence, hardware vendor kernels, and whether the issue lands in long-term-support packages first.The second thing to watch is whether similar pointer-validity assumptions show up in nearby L2CAP callbacks or other Bluetooth state-machine code. When one asynchronous path fails because it trusted a pointer too long, it is often worth asking whether the same pattern exists in sibling routines. The goal is not to panic; it is to prevent the next edge-caseaces.
The third thing to watch is downstream visibility. Microsoft’s Security Update Guide already reflects the CVE, which helps mixed environments keep track of Linux security events. That matters because enterprises increasingly rely on centralized advisory workflows rather than distro-specific mailing lists alone. The more clearly the issue is tracked, the less likely it is to fall through the cracks.
- Confirm whether your supported kernel branch includes the fix.
- Check whether Bluetooth is enabled on affected devices.
- Review crash logs for
l2cap_info_timeoutorl2cap_sock_ready_cb. - Watch for vendor advisories and backport notes.
- Re-test Bluetooth-dependent workflows after patching.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center