CVE-2026-31512 is a reminder that many kernel security bugs are not dramatic memory-smasher headlines, but small validation mistakes sitting in the middle of critical networking code. In this case, the Linux Bluetooth L2CAP path in
What makes this isst that it exists, but that the kernel already had the correct defensive pattern elsewhere. The ERTM reassembly path, specifically the
Microsoft’s Security Update Guide entry le to enterprise defenders even though the problem is in Linux, not Windows. That matters because many organizations now track Linux and Windows CVEs through the same operational workflow, and Microsoft has made a point of surfacing Linux-related CVEs in its update ecosystem for mixed-platform environments. The public record also shows the vulnerability was newly received from kernel.org on April 22, 2026, which is a strong signal that the upstream fix is already part of the stable-kernel security flow.
At a low level, this is an input-length validation failure. The kernel is assuming a packet layout that may not actually be present, and then reading a 16-bit field from the start of the payload as if the buffer were guaranteed to be long enough. That is a basic rule of packet parsing: before you interpret a field, you must verify the bytes exist. The problem is especially relevant in kernel code because a bad read does not just corrupt one user-space process; it can destabilize the networking stack or expose kernel memory behavior that should remain opaque.
The bug is also a good example of why near-duplicate code paths deserve careful review. The Eect guard, which means developers already understood the invariant. But the Enhanced Credit Based Flow Control path apparently missed that check, suggesting either a copy-and-adapt error or a later refactor that failed to preserve the validation step. In kernel maintenance, those near-miss inconsistencies are often where vulnerabilities hide.
The vulnerable path,
Kernel networking code tends to evolve in layers, and the important lesson from this CVE is that security fixes often arrive as consistency repairs. The ERTeady protected the same kind of read by using
Microsoft’s role in surfacing the issue is also part of a broader enterprise trend. Mixed-platform shops increasingly rely on a single vulnerability feed that spans Windows, Linux, Azure, and hybrid infrastructure. That makes a Linux Bluetooth bug relevant not because it affects Windows directly, but because it can still matter in environments where Linux hosts, virtual appliances, or edge systems are managed alongside Microsoft products.
The practical result depends on how the surrounding code handles the read, but the security concern is obvious. A kernel read past the valid buffer boundary can cause a crash, trigger undefined behavior, or expose adjacent memory contents indirectly through subsequent processing. Even if is “only” a warning or a malformed packet, the bug still violates the kernel’s contract with packet data. That is enough to justify a CVE in a subsystem this sensitive.
What’s useful here is that the fix does not appear to require a redesign. The advisory says the ERTM reassembly path already does the right thing, which means the patch is mostly about aligning one code path with an existing standard. In security engineering, those are often the cleanest fixes: add the missinroven path, and keep the protocol behavior intact. That lowers regression risk while closing the flaw.
The bug is subtle because the code is not obviously doing something strange.
-ndition failure**, not a math bug.
That makes this CVE less about a novel attack primitive and more about a gap between expected and actual consistency. In secure kernel code, consistency is often the whole game. If one branch assumes validated data and another branch does not, an attacker will naturally look for the weaker branch. The kernel now appears to be closing that gap.
The Role of
`ps of those helpers that looks unremarkable until you remember what it is doing. It ensures that enough bytes are present in the linear area of the socket buffer to safely access the requested data. In practice, that means it helps avoid speculative or accidental reads past what has actually been received and validated.
This matters because Bluetootht always dealing with perfectly formed, already-linearized data. Network stacks often handle packets in fragments or in layouts that require careful pulling and validation before direct access. That is why a function like
In that sense, the patch is not just about stopping one read past the buffer. It is about reasserting an architectural rule across multiple packet-handling paths. That sort of consistency is one of the quiet pillars of secure kernel development.
Consumer impact is harder to pin down because it depends heavily on usage patterns.are not thinking about L2CAP internals when they pair headphones or a keyboard. But the kernel does not care whether the packet came from a casual user or an embedded device in the field; if the packet reaches the vulnerable path and is short enough to trip the bug, the same flawed read can occur. The real distinction is not consumer versus enterprise so much as exposure versus non-exposure.
Administrators also need to remember that kernel CVEs can matter even when the visible symptom seems small. A warning, an OOB read, or a packea nuisance, but those symptoms can still be a stepping stone to more serious stability or information-handling issues. In a privileged networking path, small mistakes deserve the same seriousness as larger ones.
The practical lesson is that patch management has become less about operating system identity and more about asset function. If Bluetooth is active, the device is in scope. If the kernel build includes the vulnerable function, the machine is in scope. If the vendor has backported the fix, the version number alone may not tell you the whole story.
The important historical pattern is that these flaws are rarely brand-new conceptual failures. More often, they are inconsistencies between two code paths that should have evolved together. In thssembly path already used the right validation pattern, which suggests the security issue came from a missed parallel update rather than a fundamental misunderstanding of Bluetooth framing. That is the kind of bug that survives because the system is complex, not because anyone intentionally wrote unsafe code.
This also explains why public CVEs can appear shortly after a fix lands. The upstream community wants a durable record that downstream vendors can map to their own builds. For defenders, that means the real task is not just reading theng whether the specific vendor kernel carries the backport. That is a more annoying answer, but it is the accurate one.
That do should be trivialized. In a kernel, even a narrow out-of-bounds read can be security-relevant because it occurs in privileged code and may be reachable through regular device interaction. But the narrowness also means defenders should expect a straightforward patch train rather than a prolonged engineering saga.
In operational terms, that means the remediation task about distribution rollout and firmware availability than about compatibility testing at scale. Enterprise teams still need to test, but the technical shape of the fix suggests a modest regression surface. That is good news, because it makes adoption easier once vendor kernels are available.
That specificity is also what makes the CVE actionable. A security record that clearly identif read, and the missing size validation lets patch teams map the issue to source, stable branches, or vendor advisories with much less ambiguity. In a mixed enterprise environment, that clarity saves time.
For administrators, that means the next step is not abstract analysis but practical inventory work. Bluetooth-enabled endpoints, embedded Linux devices, and any systems relying on vendor kernels should be checked against the patched code path. The cleaner the asset inventory, the faster the remediation cycle will be. That is the real lesson of most kernel CVEs: knowing what you run matters as much as knowing what the bug is.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
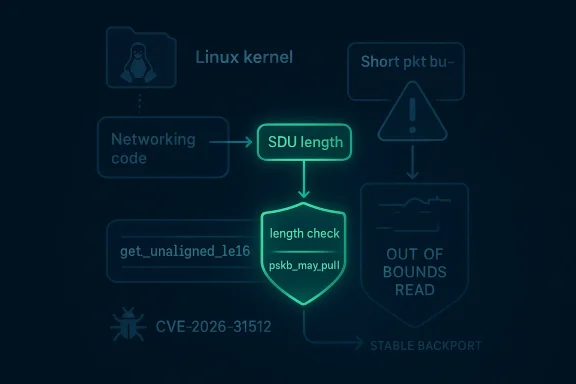
l2cap_ecred_data_rcv() reads the SDU length field before confirming that the incoming packet actually contains the two bytes required for that read, which can lead to an out-of-bounds access on short packets. The fix is straightforward in concept: apply the same pskb_may_pull()-style validation that the ERTM reassembly path already uses before dereferencing the length field. The result is a classic kernel-hardening patch: narrow, surgical, and easy to underestimate if you only look at the surface description. oth vulnerabilities in the Linux kernel rarely stay interesting for long because the technical root cause is usually visible almost immediately once the relevant function is identified. That is exactly the case here. The CVE record says the bug lives in l2cap_ecred_data_rcv(), where get_unaligned_le16() is called on skb->data without first checking that the socket buffer actually has at least L2CAP_SDULEN_SIZE bytes available. When skb->len is less than 2, the code can read past valid packet data, which is the kind of bug kernel developers usually treat as a must-fix even if exploitability is not yet fully characterized.What makes this isst that it exists, but that the kernel already had the correct defensive pattern elsewhere. The ERTM reassembly path, specifically the
L2CAP_SAR_START case in l2cap_reassemble_sdu(), already calls pskb_may_pull() before reading the SDU length. In other words, the kernel itself had a nearby example of the right thing to do, and the vulnerability arose because the Enhanced Credit Based Flow Control path did not follow that established pattern. That kind of inconsistency is one reason protocol bugs survive code review: the logic is almost the same, but not quite.Microsoft’s Security Update Guide entry le to enterprise defenders even though the problem is in Linux, not Windows. That matters because many organizations now track Linux and Windows CVEs through the same operational workflow, and Microsoft has made a point of surfacing Linux-related CVEs in its update ecosystem for mixed-platform environments. The public record also shows the vulnerability was newly received from kernel.org on April 22, 2026, which is a strong signal that the upstream fix is already part of the stable-kernel security flow.
 Why this bug matters technically
Why this bug matters technically
At a low level, this is an input-length validation failure. The kernel is assuming a packet layout that may not actually be present, and then reading a 16-bit field from the start of the payload as if the buffer were guaranteed to be long enough. That is a basic rule of packet parsing: before you interpret a field, you must verify the bytes exist. The problem is especially relevant in kernel code because a bad read does not just corrupt one user-space process; it can destabilize the networking stack or expose kernel memory behavior that should remain opaque.The bug is also a good example of why near-duplicate code paths deserve careful review. The Eect guard, which means developers already understood the invariant. But the Enhanced Credit Based Flow Control path apparently missed that check, suggesting either a copy-and-adapt error or a later refactor that failed to preserve the validation step. In kernel maintenance, those near-miss inconsistencies are often where vulnerabilities hide.
- The flaw is in Bluetooth L2CAP packet parsing.
- The vulnerable function reads the SDU length before checkinThe correct pattern already exists in the ERTM reassembly path.
- The bug is narrow, but it touches privileged kernel networking code.
- The fix is a validation guard, not a redesign.
Background
Bluetooth in Linux is not a monolithic block of code; it is a layered stack, and L2CAP sits at a foundational point in that stack. L2CAP handles multiplexing, segmentation, and reassembly, which means it often has to make decisions about packet structure before higher layers can safely consume the data. That is precisely why length checks matter so much here. A small mistake in L2CAP can propagate upward into logic that assumes the buffer was already validated.The vulnerable path,
l2cap_ecred_data_rcv(), is part of the Enhanced Credit Based Flow Control model, which is one of the mechanisms usdata efficiently and in a controlled fashion. The SDU length is not decorative metadata; it is the field that tells the stack how much data to expect and how to assemble it. If the kernel reads that field from a packet that is too short, it may be consulting a value that does not actually exist. That is the sort of mistake that can lead to information disclosure, warning conditions, or a crash depending on the exact surrounding code and build configuration.Kernel networking code tends to evolve in layers, and the important lesson from this CVE is that security fixes often arrive as consistency repairs. The ERTeady protected the same kind of read by using
pskb_may_pull(), which forces enough data into the linear portion of the skb before dereference. The presence of that guard elsewhere strongly suggests the missing check in the ECred path was an oversight rather than a design choice. That is reassuring in one sense, because it makes the fix straightforward, but it is also a reminder that code duplication in protocol stacks creates maintenance risk.How Linux kernel CVEs are typically handled
Linux kernel CVEs often appear in public after the relevant fix has already landed in stable branches. That makes the publication backward to outsiders, but it is a deliberate part of the kernel’s security workflow. The idea is to tie a CVE to an actionable change rather than to a vague description of a bug. In practical terms, that helps vendors backport fixes and helps administrators verify whether their downstream kernel includes the correction.Microsoft’s role in surfacing the issue is also part of a broader enterprise trend. Mixed-platform shops increasingly rely on a single vulnerability feed that spans Windows, Linux, Azure, and hybrid infrastructure. That makes a Linux Bluetooth bug relevant not because it affects Windows directly, but because it can still matter in environments where Linux hosts, virtual appliances, or edge systems are managed alongside Microsoft products.
Why Bluetooth bugs still matter in 2026
Bluetooth vulnerabilities can be easy to dismiss because many enterprise administrators focus on wired networking, cloud services, or browser-facing attack surfaces. But Bluetooth remains present in laptops, embedded systems, industrial devices, kiosks, field equipment, and consumer gear that finds its way into business workflows. Even where the risk is not high-volume or internet-facing, the presence of a kernel parsing flaw still matters because local wireless attack surfaces are a real part of modern endpoints.- Bluetooth code often lives on endpoints that are physically near users and devices.
- L2CAP is a core protocol layer, not an optional add-on.
- Length checks are especially important in framing and reassembly paths.
- Kernel bugs can be relevant even when they areitable.
- Enterprise exposure depends heavily on hardware inventory and device policy.
What the Vulnerability Actually Does
The heart of CVE-2026-31512 is simple:l2cap_ecred_data_rcv() trusts that the skb contains enough bytes to read the SDU length, and that trust is not justified when the packet is shorter than two bytes. The CVE description explicitly calls out get_unaligned_le16() being used on skb->data without first verifying L2CAP_SDULEN_SIZE. That means the function can step outside the valid data region and inspect memory it should never have touched.The practical result depends on how the surrounding code handles the read, but the security concern is obvious. A kernel read past the valid buffer boundary can cause a crash, trigger undefined behavior, or expose adjacent memory contents indirectly through subsequent processing. Even if is “only” a warning or a malformed packet, the bug still violates the kernel’s contract with packet data. That is enough to justify a CVE in a subsystem this sensitive.
What’s useful here is that the fix does not appear to require a redesign. The advisory says the ERTM reassembly path already does the right thing, which means the patch is mostly about aligning one code path with an existing standard. In security engineering, those are often the cleanest fixes: add the missinroven path, and keep the protocol behavior intact. That lowers regression risk while closing the flaw.
Buffer-length validation is not optional
Packet parsers live or die by their boundary checks. A kernel can parse millions of valid packets safely, but one malformed short packet can reveal whether the code is disciplined or careless about lengths. This CVE is a textbook example of why the first rule of packet handling is to erence. If a field is supposed to be two bytes long, the code must establish that those two bytes are present before trying to read them.The bug is subtle because the code is not obviously doing something strange.
get_unaligned_le16() is a normal helper for reading a 16-bit little-endian value from unaligned memory. The problem is not the helper itself; it is the assumption that the buffer is long enough. In kernel work, helpers are only as safe as the preconditions around them.-ndition failure**, not a math bug.
get_unaligned_le16()is only safe when enough bytes are present.- Short packets create the out-of-bounds read condition.
- The same validation style already exists in a neighboring path.
- The fix is to establish the buffer length first, then read.
Why the ERTM comparison matters
The advisory’s comparisobly path is important because it shows the kernel already had a blueprint.pskb_may_pull() is used there to ensure the necessary bytes are accessible before reading the SDU length in the start-of-SDU case. That is not just implementation trivia; it is proof that the validation model was known, accepted, and already deployed in another Bluetooth receive path.That makes this CVE less about a novel attack primitive and more about a gap between expected and actual consistency. In secure kernel code, consistency is often the whole game. If one branch assumes validated data and another branch does not, an attacker will naturally look for the weaker branch. The kernel now appears to be closing that gap.
The Role of pskb_may_pull()
`ps of those helpers that looks unremarkable until you remember what it is doing. It ensures that enough bytes are present in the linear area of the socket buffer to safely access the requested data. In practice, that means it helps avoid speculative or accidental reads past what has actually been received and validated.This matters because Bluetootht always dealing with perfectly formed, already-linearized data. Network stacks often handle packets in fragments or in layouts that require careful pulling and validation before direct access. That is why a function like
pskb_may_pull() exists in the first place: it turns an implicit assumption into an explicit check. When code omits that check, it is effectively wagering that theal, and kernel security code should never make that bet.Why linearization is a security boundary
In a packet stack, data may exist in multiple fragments or in a representation that is not yet safe to access directly. Linearization, or ensuring the bytes are present where the code expects them, is a basic safety step. If the code reads from a location before this happens, it can cross from “structured packet parsing” into “raw memory access,” which is exactly the kind of transition that security reviews s is also why the bug is not just theoretical. Kernel developers are not worried only about crashes; they are also trying to preserve the invariant that parsing functions never make reads based on unverified layout assumptions. The moment that invariant weakens, every caller above it becomes harder to trust.pskb_may_pull()ensures the requested bytes are actually accessible.- It protects against fragmented or incomplete skb layouts.
- It is a normal part of safe
- Omitting it turns a buffer read into a guess.
- The vulnerability is a failure to enforce that access boundary.
Why this is a maintainability story too
The best security fixes often improve maintainability because they make the code easier to reason about. A function that begins with a clear pull/validatedit than one that mixes validation and parsing in an ad hoc way. Over time, that kind of structure reduces the chance of future bugs in adjacent paths. That is one reason the ERTM pattern matters so much here.In that sense, the patch is not just about stopping one read past the buffer. It is about reasserting an architectural rule across multiple packet-handling paths. That sort of consistency is one of the quiet pillars of secure kernel development.
Enterprise and Consumer Impact
For enterprises, the first question is not whether Bluetooth sounds glamorous enough to matter. The question is whether affected kernels are running on laptops, rugged devices, kiosks, industrial endpoints, or any other hardware witpport. If the answer is yes, then even a narrow parsing flaw deserves attention because endpoint exposure tends to be distributed and hard to inventory perfectly.Consumer impact is harder to pin down because it depends heavily on usage patterns.are not thinking about L2CAP internals when they pair headphones or a keyboard. But the kernel does not care whether the packet came from a casual user or an embedded device in the field; if the packet reaches the vulnerable path and is short enough to trip the bug, the same flawed read can occur. The real distinction is not consumer versus enterprise so much as exposure versus non-exposure.
Where the risk is likely highest
The highest risk is ptop with Bluetooth disabled or rarely used. It is more likely on systems where Bluetooth is active by design, especially in environments with routine device pairing, field-service peripherals, or embedded control equipment. Those are the places where short malformed packets are more likely to be part of a real attack surface rather than a hypothetical one.Administrators also need to remember that kernel CVEs can matter even when the visible symptom seems small. A warning, an OOB read, or a packea nuisance, but those symptoms can still be a stepping stone to more serious stability or information-handling issues. In a privileged networking path, small mistakes deserve the same seriousness as larger ones.
- Enterprise exposure depends on device policy and Bluetooth usage.
- Consumer exposure depends on whether the vulnerable path is reachable.
- Embedded and field devices may be more exposed than desktops.
- A “small” kernel reaoperational consequences.
- Inventory and patch verification matter more than assumption.
Why mixed-platform teams should care
Microsoft’s publication of the advisory is a good example of why mixed-platform security operations have changed. Teams no longer track Linux, Windows, and cloud assets in separate mental silos; they rely on unified vulnerability dashboards andt makes a Linux Bluetooth CVE relevant to organizations even if their primary endpoint fleet is Windows-heavy, because Linux still sits in laptops, VDI images, appliances, containers, and edge systems managed under the same program.The practical lesson is that patch management has become less about operating system identity and more about asset function. If Bluetooth is active, the device is in scope. If the kernel build includes the vulnerable function, the machine is in scope. If the vendor has backported the fix, the version number alone may not tell you the whole story.
Historical Context
Kernel Bluetooth bugs have a long history of being “small” on paper and meaningful in practice. That is because they often arise at the boundary between externally supplied data and internal protocol state, where one missing guard can compromise the safety of the whole path. The Linux kernel community has spent years tightening these paths because they sit close to hardware and receive traffic from real-world devices that are not always well-behaved.The important historical pattern is that these flaws are rarely brand-new conceptual failures. More often, they are inconsistencies between two code paths that should have evolved together. In thssembly path already used the right validation pattern, which suggests the security issue came from a missed parallel update rather than a fundamental misunderstanding of Bluetooth framing. That is the kind of bug that survives because the system is complex, not because anyone intentionally wrote unsafe code.
Why stable-kernel fixes matter
Linux security work is often carried through stable branches rather than only the mainline tree. That matters because most production sytine upstream kernels; they run downstream distributions that backport fixes selectively. The existence of stable references in the CVE record signals that this bug is being tracked in the normal patch pipeline, which is what administrators should expect for a kernel-level networking issue.This also explains why public CVEs can appear shortly after a fix lands. The upstream community wants a durable record that downstream vendors can map to their own builds. For defenders, that means the real task is not just reading theng whether the specific vendor kernel carries the backport. That is a more annoying answer, but it is the accurate one.
The broader security lesson
This CVE fits a broader 2026 theme in kernel security: the important bugs are often about boundaries, not flashy exploit primitives. Boundaries of length, boundaries of lifetime, boundaries of ownership, and boundaries of state are where kernel code is most likely to go wrong. The Bluetooth L2CAP issue is a good reminder that a check can matter as much as a much more dramatic memory corruption bug.- Older protocols still matter because they remain in real deployments.
- Parallel code paths should preserve the same validation rules.
- Stable backports are critical for real-world remediation.
- A small parsing bug can still justify formal CVE tracking.
- Boundary validation is one of the kernel’s ines.
Patch Significance
From a remediation standpoint, this is the kind of CVE administrators like to see and attackers hate to see. The fix is specific, the behavioral change is limited, and the risk of collateral damage is relatively low compared with a redesign. When the kernel already has a working precedent in a neighboring path, vendors usually have a clean narrative for backporting the patch without extensive functional upheaval.That do should be trivialized. In a kernel, even a narrow out-of-bounds read can be security-relevant because it occurs in privileged code and may be reachable through regular device interaction. But the narrowness also means defenders should expect a straightforward patch train rather than a prolonged engineering saga.
Why the fix should be low-risk
The patch appears to preserve behavior for valid packets while adding a guard for invalid ones. That is usually the ideal shape for a security fix: reject what was never legal, and keep the normal case unchanged. Because the ERTM code already uses the validation model being applied here, the chance of surprising legitimate Bluetooth traffic should be relatively low.In operational terms, that means the remediation task about distribution rollout and firmware availability than about compatibility testing at scale. Enterprise teams still need to test, but the technical shape of the fix suggests a modest regression surface. That is good news, because it makes adoption easier once vendor kernels are available.
- The patch adds a guard, rather than changing proisting code already demonstrates the right validation pattern.
- Valid traffic should continue to behave normally.
- Downstream backports are likely to be manageable.
- Operators should still verify the exact vendor build.
Why the advisory wording matters
The wording in the advisory is precise: the code reads the SDU length before verifying the buffer contains enough bytes. That precision is helpfufenders what sort of review to perform in their own environments. They do not need to guess at some vague Bluetooth instability; they need to confirm whether the affected kernel build contains the missing length check in the Enhanced Credit Based Flow Control receive path.That specificity is also what makes the CVE actionable. A security record that clearly identif read, and the missing size validation lets patch teams map the issue to source, stable branches, or vendor advisories with much less ambiguity. In a mixed enterprise environment, that clarity saves time.
Strengths and Opportunities
This CVE has one major advantage for defenders: it is conceptually simple enough to understand quickly, but concrete enough to act on immediately. The presence of an existing correct pattern in another L2CAP path makes the remediation story cleaner, and the bug’s narrow scope should help vendors backport it without much drama. It also gives security teams a good example of why packet-length validation remains one of the most important habits in kernel coding.- The defect is easy to explain to operators.
- The fix appears tcal.
- Existing code already shows the right validation pattern.
- The issue reinforces good packet-parsing discipline.
- Mixed-platform teams can fold it into a single patch workflow.
- The remediation burden should be moderate rather than massive.
- The CVE can serve as a training example for boundary checks.
Risks and Concerns
The biggest concern is underestimation. Because this is an out-of-bounds read rather than a headline-grabbing execution bug, teams may be tempted to assign it a lower operational priority than it deserves. That would be a mistake, especially on hosts where Bluetooth is active and kernel networking paths are part of daily use. Quiet bugs in privileged code can still create serious risk.- Teams may under-rank it because the bug sounds small.
- Vendor backports may lag behind the public CVE record.
- Many tools wilvious from version numbers alone.
- Bluetooth exposure varies widely by device and policy.
- A kernel read bug can still destabilize the system.
- Mixed fleets make verification harder.
- If overlooked, the issue can linger in long-lived endpoints.
Why visibility is a challenge
This sort of problem is difficult to spot by symptoms alone. There may be no obvious crash, no user-facing failure, and no immediate clue that the kernel read a field it should never have touched. That makes patch verification more important than waiting for operational noise to reveal the problem. In security work, silence is not always reassurance.Looking Ahead
The key question now is how quickly downstream vendors absorb the upstream fix and how clearly they communicate affected build lines. Because the CVE is rnel function and a very specific validation gap, there is little ambiguity about what needs to be changed. The uncertainty is mostly operational: which distribution releases, appliance firmware builds, and cloud images already contain the patch.For administrators, that means the next step is not abstract analysis but practical inventory work. Bluetooth-enabled endpoints, embedded Linux devices, and any systems relying on vendor kernels should be checked against the patched code path. The cleaner the asset inventory, the faster the remediation cycle will be. That is the real lesson of most kernel CVEs: knowing what you run matters as much as knowing what the bug is.
What to watch next
- Vendor advisories for backported fixes in downstream kernels.
- Distribution errto package versions.
- Any follow-up stable commits that touch nearby Bluetooth paths.
- Enterprise guidance on whether Bluetooth exposure warrants temporary mitigation.
- Clarifications from maintainers if additional affected paths are identified.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center