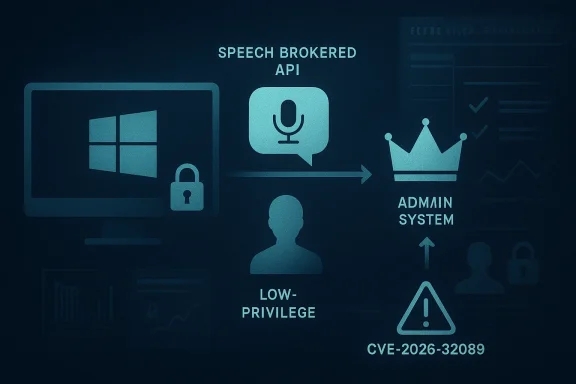
Microsoft has assigned CVE-2026-32089 to a Windows Speech Brokered API elevation-of-privilege issue, signaling another local privilege-escalation flaw in a Windows component that handles privileged speech-related interactions. The entry’s wording suggests the vulnerability is already considered real enough to warrant a public CVE, but the public record available at this stage appears thin on root-cause detail and exploitation context. That combination matters: when Microsoft names a CVE but has not yet exposed much technical depth, defenders have to plan for the possibility of a practical local attack path even before exploitability is fully understood.
The most important thing to understand about CVE-2026-32089 is that it lives in a familiar and often underappreciated category: local elevation of privilege. These flaws do not usually begin with a remote foothold. Instead, they assume the attacker has some form of authenticated presence on the machine already, then look for a way to cross a boundary and become more powerful, often all the way to SYSTEM or administrator. That makes them especially relevant in enterprise environments where a low-privilege account compromise can be the first step in a much larger intrusion.
Microsoft’s naming also places this issue in the long tail of Windows Speech Brokered API security problems. A similar phrasing appeared years ago in CVE-2020-1395, which NVD described as an elevation-of-privilege vulnerability in the way the Windows Speech Brokered API handles objects in memory. That earlier record is useful context because it shows Microsoft has previously had to harden this area, and because repeated exposure in the same subsystem often suggests a design surface that deserves extra scrutiny. (nvd.nist.gov)
The new CVE arrives at a time when Microsoft has become more transparent about publishing vulnerability data through the Security Update Guide, while also expanding machine-readable formats such as CSAF. That broader disclosure posture helps customers automate triage, but it also means defenders now see many more issues earlier in their lifecycle, often before the technical story is fully fleshed out. In practical terms, security teams are increasingly asked to move from certainty to preparedness much faster than they used to.
The specific metric text supplied with this CVE focuses on confidence and technical credibility. In plain English, that is Microsoft’s way of saying: how sure are we that the vulnerability exists, and how much do we really know about how it works? When those answers are strong, urgency rises. When the technical details are limited, the score can still be high, but defenders need to pair patching with caution, validation, and monitoring.
The Windows Speech Brokered API is an especially interesting target surface because brokered APIs are meant to mediate access between less-trusted code and more privileged system functionality. In principle, that architecture improves safety by placing a controlled intermediary between the caller and the underlying resource. In practice, any brokered boundary becomes a very attractive target for race conditions, object confusion, reference-counting mistakes, and handle validation errors. Those are exactly the kinds of faults that can translate into privilege escalation.
Historically, Microsoft has tended to publish these issues with limited public detail until patch day or until researchers independently analyze the fix. That is a sensible defensive posture, but it creates a familiar asymmetry: defenders must act on sparse data, while offensive researchers may later reconstruct the bug class from the patch. That lag is normal, but it is never comfortable. It is also why the confidence metric matters almost as much as the CVE itself.
There is another important historical lesson here. Microsoft has repeatedly used the Security Update Guide and MSRC blog ecosystem to provide the first authoritative signal that a vulnerability exists, even when the technical narrative remains intentionally general. Earlier Microsoft disclosures on other EoP issues show a consistent pattern: the company may describe the bug class, the affected surface, and the mitigation urgency without fully publishing the exploit primitive. That gives customers a chance to patch quickly while preserving some room for coordinated disclosure.
This is where defenders should be disciplined. A high-confidence vulnerability means the safe assumption is that an attacker can find a route through it, even if the first public write-up has not appeared yet. In other words, the absence of a PoC should not be mistaken for absence of risk. The gap between disclosure and exploitation is often measured in days, not months.
The public language tied to this CVE does not yet identify a specific memory corruption primitive, synchronization bug, or type-confusion issue. That is not unusual for a fresh Microsoft CVE entry. It does mean, however, that analysts should treat the bug class as local, authenticated, and potentially reliable until evidence proves otherwise. The older CVE-2020-1395 record shows the same component has already been associated with memory-handling weaknesses, which makes this new issue more interesting than a random one-off. (nvd.nist.gov)
Enterprises should also consider the surrounding access model. A local EoP might look less alarming than remote code execution, but once malware or a malicious insider lands on a machine, EoP is often the difference between a contained incident and full compromise. That distinction matters for response planning because many blue teams still prioritize perimeter threats over local privilege escalation. In 2026, that is a risky habit.
The company’s response history also shows that some EoP bugs are connected to design choices, not just coding mistakes. A brokered API, a privileged service, or a helper process can become a recurring point of weakness if it processes attacker-influenced input without enough isolation. When that happens, patching one bug helps, but long-term resilience requires architectural hardening. That is the more expensive lesson, and the one vendors rarely get to announce with fanfare.
There is a second historical pattern worth noting. When Microsoft does not publish much detail at first, the surrounding ecosystem often fills the gap with partial analysis, third-party references, and eventually patch diffing. That means defenders are often operating in a moving target environment where certainty grows over time. For now, the safest approach is to act on the confirmed existence of the issue, not on the incomplete story around it.
The impact is not limited to domain environments, though they are often the most sensitive. A successful EoP on a workstation can expose browser tokens, cached credentials, local secrets, and management tooling. On servers, especially those used for automation or application hosting, the consequences can be worse because privilege often maps directly to broad operational trust. In that sense, the “local only” label is misleadingly modest.
Enterprises should also think in terms of blast radius. A single patched machine is good. A fleet-wide response process is better. If the vulnerability truly affects a broad range of supported Windows versions, which is typical for brokered API issues, then the operational challenge becomes consistency, not just urgency. The best patch is the one that reaches every relevant endpoint quickly.
That means the consumer takeaway is not “this only affects admins.” It is “if malware gets a foothold, this could help it take over the machine.” For many users, the practical defense is to keep Windows fully updated, avoid untrusted downloads, and maintain reputable endpoint protection. Those are basic measures, but EoP bugs like this are a reminder that basics still matter.
There is also a secondary consumer risk in shared-family environments. A standard user account may look harmless, but if a less-privileged account is compromised, the attacker may use the vulnerability to pivot into the rest of the system. That can expose personal files, saved passwords, and browser data. In modern Windows environments, the boundary between “just one account” and “the whole device” is often thinner than people assume.
Organizations should use a layered approach. First, confirm whether the patch is available for all supported builds in your environment. Next, test the update on representative systems with speech-related features, accessibility tools, or enterprise software that could interact with the brokered API. Finally, deploy in phases while watching for abnormal behavior. That workflow is slower than blanket panic, but faster than waiting for a proof-of-concept blog post.
Microsoft’s broader transparency work around CSAF and the Security Update Guide is helpful here because it encourages a more machine-friendly response process. The more automatically you can map CVEs to assets, the less likely a high-impact bug will sit unnoticed in a backlog. Visibility is not remediation, but it is a prerequisite for remediation.
A second likely scenario involves chaining. An attacker may first compromise a user through a different bug or social engineering trick, then use this CVE to obtain stronger privileges. That makes the issue more relevant to incident response teams than to perimeter-only defenders. The most dangerous vulnerabilities are often the ones that do not look catastrophic in isolation.
For threat hunters, the lack of public exploit detail should not imply a lack of signals. Unusual child processes, unexpected speech-related service behavior, repeated broker failures, or privilege changes following low-privilege activity all deserve attention. The goal is not to predict the exact exploit, but to catch the behavioral fingerprints of abuse. That is how mature defenders stay ahead of incomplete disclosures.
It will also be worth tracking whether the Windows Speech Brokered API becomes a recurring discussion point in future Microsoft advisories. If this CVE is one of several similar issues, then the story becomes larger than a single patch cycle. At that point, Microsoft may need to refine the subsystem more broadly, not just close one hole at a time.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Overview
Overview
The most important thing to understand about CVE-2026-32089 is that it lives in a familiar and often underappreciated category: local elevation of privilege. These flaws do not usually begin with a remote foothold. Instead, they assume the attacker has some form of authenticated presence on the machine already, then look for a way to cross a boundary and become more powerful, often all the way to SYSTEM or administrator. That makes them especially relevant in enterprise environments where a low-privilege account compromise can be the first step in a much larger intrusion.Microsoft’s naming also places this issue in the long tail of Windows Speech Brokered API security problems. A similar phrasing appeared years ago in CVE-2020-1395, which NVD described as an elevation-of-privilege vulnerability in the way the Windows Speech Brokered API handles objects in memory. That earlier record is useful context because it shows Microsoft has previously had to harden this area, and because repeated exposure in the same subsystem often suggests a design surface that deserves extra scrutiny. (nvd.nist.gov)
The new CVE arrives at a time when Microsoft has become more transparent about publishing vulnerability data through the Security Update Guide, while also expanding machine-readable formats such as CSAF. That broader disclosure posture helps customers automate triage, but it also means defenders now see many more issues earlier in their lifecycle, often before the technical story is fully fleshed out. In practical terms, security teams are increasingly asked to move from certainty to preparedness much faster than they used to.
The specific metric text supplied with this CVE focuses on confidence and technical credibility. In plain English, that is Microsoft’s way of saying: how sure are we that the vulnerability exists, and how much do we really know about how it works? When those answers are strong, urgency rises. When the technical details are limited, the score can still be high, but defenders need to pair patching with caution, validation, and monitoring.
Background
Windows elevation-of-privilege bugs are not new, and they are rarely glamorous. They are, however, one of the most effective building blocks in a real intrusion chain. An attacker who already has a foothold as a standard user can use an EoP to gain access to sensitive data, disable defenses, tamper with services, or plant persistence that survives basic cleanup. That is why even “local only” flaws routinely get strong attention from enterprise defenders.The Windows Speech Brokered API is an especially interesting target surface because brokered APIs are meant to mediate access between less-trusted code and more privileged system functionality. In principle, that architecture improves safety by placing a controlled intermediary between the caller and the underlying resource. In practice, any brokered boundary becomes a very attractive target for race conditions, object confusion, reference-counting mistakes, and handle validation errors. Those are exactly the kinds of faults that can translate into privilege escalation.
Historically, Microsoft has tended to publish these issues with limited public detail until patch day or until researchers independently analyze the fix. That is a sensible defensive posture, but it creates a familiar asymmetry: defenders must act on sparse data, while offensive researchers may later reconstruct the bug class from the patch. That lag is normal, but it is never comfortable. It is also why the confidence metric matters almost as much as the CVE itself.
There is another important historical lesson here. Microsoft has repeatedly used the Security Update Guide and MSRC blog ecosystem to provide the first authoritative signal that a vulnerability exists, even when the technical narrative remains intentionally general. Earlier Microsoft disclosures on other EoP issues show a consistent pattern: the company may describe the bug class, the affected surface, and the mitigation urgency without fully publishing the exploit primitive. That gives customers a chance to patch quickly while preserving some room for coordinated disclosure.
Why the Speech Brokered API matters
The speech stack is not the kind of subsystem that average users think about every day. That can make it easy to underestimate. But “quiet” platform components often carry significant privilege or interact with protected services, which is exactly why they become useful stepping stones for attackers. A weakness in an intermediary layer can be more valuable than a flashy browser bug if it reliably converts a low-privilege session into a privileged one.- Brokered interfaces often sit at trusted boundaries.
- Privilege transitions magnify the impact of logic flaws.
- Rarely used components can receive less adversarial attention from defenders.
- Attackers value reliable local escalation as a post-exploitation tool.
- Microsoft historically treats these bugs as serious even without remote reachability.
What Microsoft’s wording implies
The wording supplied by the vulnerability record suggests confidence in existence, but not necessarily confidence in exploitability by the public today. That distinction is subtle but important. A confirmed bug can still be hard to weaponize, and a poorly understood issue can still be urgent if it sits in a sensitive path and affects many supported Windows versions.This is where defenders should be disciplined. A high-confidence vulnerability means the safe assumption is that an attacker can find a route through it, even if the first public write-up has not appeared yet. In other words, the absence of a PoC should not be mistaken for absence of risk. The gap between disclosure and exploitation is often measured in days, not months.
Confidence versus exploitability
The metric text you supplied is effectively a reminder that confidence and impact are different axes. A bug can be well confirmed and still take time to reproduce in a lab. Conversely, a poorly documented issue can still be dangerous if the likely root cause is obvious from the affected subsystem. For operational response, this means patching decisions should not wait for perfect clarity.- High confidence raises the priority of remediation.
- Sparse technical detail increases the value of vendor patching.
- Attackers can still reverse engineer fixes after release.
- Enterprise response should assume proof-of-concept work may follow.
- Logging and detection matter even when details are scarce.
Technical Context and Likely Attack Surface
Windows Speech Brokered API vulnerabilities typically matter because brokered components translate caller actions into privileged work. That translation layer is where security assumptions can fail. If the broker mishandles objects in memory, trusts a stale pointer, or allows an attacker to influence execution order, the result may be an elevation path that is difficult to spot from the outside.The public language tied to this CVE does not yet identify a specific memory corruption primitive, synchronization bug, or type-confusion issue. That is not unusual for a fresh Microsoft CVE entry. It does mean, however, that analysts should treat the bug class as local, authenticated, and potentially reliable until evidence proves otherwise. The older CVE-2020-1395 record shows the same component has already been associated with memory-handling weaknesses, which makes this new issue more interesting than a random one-off. (nvd.nist.gov)
Enterprises should also consider the surrounding access model. A local EoP might look less alarming than remote code execution, but once malware or a malicious insider lands on a machine, EoP is often the difference between a contained incident and full compromise. That distinction matters for response planning because many blue teams still prioritize perimeter threats over local privilege escalation. In 2026, that is a risky habit.
Local attacker assumptions
Microsoft’s vulnerability taxonomy for EoP issues usually implies an authenticated local attacker or an attacker who can already execute code on the target. That means the exploit chain may begin elsewhere, but the privilege jump happens here. For defenders, that creates a two-stage problem: prevent initial access and harden against escalation if access is gained.- User-level compromise may be enough to start exploitation.
- Lateral movement often relies on privilege escalation next.
- Service accounts and standard user sessions can be attractive targets.
- Endpoint hardening should assume post-compromise escalation attempts.
- Security tooling should flag suspicious broker interactions.
Historical Pattern in Microsoft EoP Issues
Microsoft has a long track record of treating local privilege escalation seriously, even when the vulnerable code path is obscure. That is because EoP bugs are frequently used in the real world as the final stage of an intrusion. They may not dominate headlines the way internet-facing remote code execution flaws do, but in incident response they often explain how an intruder turned a foothold into durable control.The company’s response history also shows that some EoP bugs are connected to design choices, not just coding mistakes. A brokered API, a privileged service, or a helper process can become a recurring point of weakness if it processes attacker-influenced input without enough isolation. When that happens, patching one bug helps, but long-term resilience requires architectural hardening. That is the more expensive lesson, and the one vendors rarely get to announce with fanfare.
There is a second historical pattern worth noting. When Microsoft does not publish much detail at first, the surrounding ecosystem often fills the gap with partial analysis, third-party references, and eventually patch diffing. That means defenders are often operating in a moving target environment where certainty grows over time. For now, the safest approach is to act on the confirmed existence of the issue, not on the incomplete story around it.
Why repeated subsystem issues matter
Repeated security problems in a subsystem do not automatically prove a systemic flaw, but they do raise the odds that the area deserves deeper review. A brokered API can be especially risky because it merges privilege boundaries with complex state. The more stateful the design, the more likely a synchronization or object-lifecycle bug becomes exploitable.- Repeated issues can indicate architectural pressure points.
- Privileged helper processes expand the attack surface.
- Memory safety and state management remain perennial risks.
- Subsystem history can help prioritize internal review.
- Patch diffs may reveal broader design assumptions.
Enterprise Impact
For enterprise administrators, CVE-2026-32089 is the kind of issue that belongs on the “patch promptly, then verify exposure” list. The strongest reason is simple: local privilege escalation flaws tend to become much more valuable after the first stage of compromise. If an attacker lands through phishing, stolen credentials, or a different unpatched vulnerability, this CVE may provide the next rung up the ladder.The impact is not limited to domain environments, though they are often the most sensitive. A successful EoP on a workstation can expose browser tokens, cached credentials, local secrets, and management tooling. On servers, especially those used for automation or application hosting, the consequences can be worse because privilege often maps directly to broad operational trust. In that sense, the “local only” label is misleadingly modest.
Enterprises should also think in terms of blast radius. A single patched machine is good. A fleet-wide response process is better. If the vulnerability truly affects a broad range of supported Windows versions, which is typical for brokered API issues, then the operational challenge becomes consistency, not just urgency. The best patch is the one that reaches every relevant endpoint quickly.
Deployment realities
Large organizations rarely suffer from a lack of patches. They suffer from patch timing, compatibility fear, and incomplete asset visibility. That makes Microsoft’s confirmation of the issue only the first step. The next step is identifying which systems actually expose the speech stack, which users have local execution paths, and which machines are too brittle to restart casually.- Validate device inventory before and after remediation.
- Prioritize exposed endpoints with interactive users.
- Treat privileged workstations as high-value targets.
- Watch for delayed patching in remote or offline systems.
- Confirm that third-party security tools still function after updates.
Consumer Impact
For consumers, the immediate risk profile is narrower but still real. A home user generally needs to be running something malicious already before a local EoP matters. But that “already” is exactly where today’s malware ecosystem lives. Commodity malware frequently arrives through fake installers, macro abuse, drive-by downloads, or trojanized utilities, then tries to escalate once it lands.That means the consumer takeaway is not “this only affects admins.” It is “if malware gets a foothold, this could help it take over the machine.” For many users, the practical defense is to keep Windows fully updated, avoid untrusted downloads, and maintain reputable endpoint protection. Those are basic measures, but EoP bugs like this are a reminder that basics still matter.
There is also a secondary consumer risk in shared-family environments. A standard user account may look harmless, but if a less-privileged account is compromised, the attacker may use the vulnerability to pivot into the rest of the system. That can expose personal files, saved passwords, and browser data. In modern Windows environments, the boundary between “just one account” and “the whole device” is often thinner than people assume.
What home users should focus on
- Install Windows updates promptly.
- Avoid untrusted installers and cracked software.
- Use standard accounts where possible.
- Keep Defender or another trusted AV active.
- Restart after updating so fixes are fully applied.
Patch Strategy and Response Prioritization
From a response standpoint, CVE-2026-32089 should be handled as a priority local escalation issue rather than a curiosity. That is especially true if Microsoft’s update guide associates it with a broad set of supported Windows releases, which is common for platform-level bugs. Even if exploitation is not publicly documented today, the prudent assumption is that it may become easier to understand once patch details are examined.Organizations should use a layered approach. First, confirm whether the patch is available for all supported builds in your environment. Next, test the update on representative systems with speech-related features, accessibility tools, or enterprise software that could interact with the brokered API. Finally, deploy in phases while watching for abnormal behavior. That workflow is slower than blanket panic, but faster than waiting for a proof-of-concept blog post.
Microsoft’s broader transparency work around CSAF and the Security Update Guide is helpful here because it encourages a more machine-friendly response process. The more automatically you can map CVEs to assets, the less likely a high-impact bug will sit unnoticed in a backlog. Visibility is not remediation, but it is a prerequisite for remediation.
Suggested response order
- Confirm whether Microsoft has released the fix for your affected Windows builds.
- Inventory endpoints that run supported desktop and server versions.
- Prioritize interactive workstations and privilege-rich server roles.
- Test the update against speech-related and accessibility-dependent workflows.
- Deploy broadly, then verify post-update health and reboot status.
Possible Exploitation Scenarios
Although the public record is sparse, local EoP bugs in brokered APIs usually fit a handful of familiar exploitation patterns. Attackers may try to manipulate timing, force the broker into an inconsistent state, or abuse object lifetime mistakes to gain access to privileged actions. Even when the exact primitive is unknown, those categories help defenders imagine what to monitor.A second likely scenario involves chaining. An attacker may first compromise a user through a different bug or social engineering trick, then use this CVE to obtain stronger privileges. That makes the issue more relevant to incident response teams than to perimeter-only defenders. The most dangerous vulnerabilities are often the ones that do not look catastrophic in isolation.
For threat hunters, the lack of public exploit detail should not imply a lack of signals. Unusual child processes, unexpected speech-related service behavior, repeated broker failures, or privilege changes following low-privilege activity all deserve attention. The goal is not to predict the exact exploit, but to catch the behavioral fingerprints of abuse. That is how mature defenders stay ahead of incomplete disclosures.
Hunting considerations
- Look for suspicious local privilege jumps after user execution.
- Correlate broker crashes with suspicious command lines.
- Watch for odd service restarts or access token anomalies.
- Review telemetry around accessibility or speech-related processes.
- Prioritize alerts involving new admin group membership.
Strengths and Opportunities
Microsoft’s handling of CVE-2026-32089 reflects several strengths in the current disclosure model, and it also creates opportunities for defenders who are ready to act quickly. The main opportunity is to use the early signal to reduce dwell time before any public exploit matures. The other is to treat this as a prompt to review how much trust your environment places in local Windows helper components.- Early vendor acknowledgement gives defenders something concrete to patch against.
- Brokered API scrutiny may surface broader hardening work beyond this one CVE.
- Machine-readable advisory workflows can speed enterprise mapping and response.
- Local EoP focus helps blue teams refine post-compromise monitoring.
- Historical context from CVE-2020-1395 suggests the subsystem is worth reviewing closely. (nvd.nist.gov)
- Patch validation can improve update discipline for other Windows fixes too.
- Telemetry tuning around privilege escalation may pay dividends across multiple attack paths.
Risks and Concerns
The biggest concern is not just that a privilege escalation exists, but that the public details are limited while the subsystem is already known to be security-sensitive. That combination can encourage either complacency or overreaction, neither of which helps. The right posture is disciplined urgency: patch fast, verify carefully, and monitor aggressively.- Sparse technical details make it harder to judge exploitability.
- Local-only framing may cause teams to underestimate real-world risk.
- Brokered API complexity increases the chance of subtle attack paths.
- Enterprise patch lag can leave high-value systems exposed longer than expected.
- Attack chaining can turn a low-privilege foothold into full compromise.
- Legacy and specialized Windows builds may complicate rollout.
- False confidence from “no PoC yet” can delay remediation.
Looking Ahead
The next thing to watch is how much more Microsoft and the broader research community disclose about the bug class. If additional technical detail emerges, defenders will learn whether the issue looks like a memory-safety flaw, a race condition, an object-lifetime bug, or something else entirely. That matters because each category carries different exploitation likelihood and different detection opportunities.It will also be worth tracking whether the Windows Speech Brokered API becomes a recurring discussion point in future Microsoft advisories. If this CVE is one of several similar issues, then the story becomes larger than a single patch cycle. At that point, Microsoft may need to refine the subsystem more broadly, not just close one hole at a time.
Watch list
- Microsoft’s full advisory content and any revision history.
- Third-party analysis of the patch and likely root cause.
- Whether exploit researchers produce a public write-up.
- Any mention of affected Windows versions or build ranges.
- New detection guidance from Microsoft Defender or partner tools.
Source: MSRC Security Update Guide - Microsoft Security Response Center
Last edited: