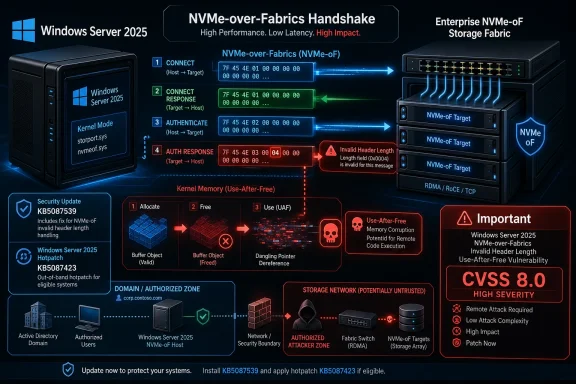
Microsoft disclosed CVE-2026-34332 on May 12, 2026, as an Important Windows Kernel-Mode Driver remote code execution vulnerability affecting Windows Server 2025 and Server Core, fixed by KB5087539 or hotpatch KB5087423, with a CVSS 3.1 base score of 8.0 and customer action required. The interesting part is not that Windows has another kernel bug; it is that this one sits at the intersection of network storage, kernel memory safety, and the uneasy promise of server hotpatching. Microsoft says exploitation is unlikely, but the advisory describes enough of the path to make this more than a routine line item for administrators who run Windows Server 2025 in modern storage environments.
CVE-2026-34332 is not the kind of vulnerability that should send every Windows desktop user sprinting for the update button in a panic. The affected products Microsoft lists are Windows Server 2025 and Windows Server 2025 Server Core, both on x64. That narrows the blast radius considerably.
But it also sharpens the concern. Server Core is exactly where many organizations put roles they want stripped down, automated, and left alone. Windows Server 2025 is also the generation Microsoft wants enterprises to treat as the forward-looking platform for hybrid infrastructure, security baselines, and update modernization.
The vulnerability is a use-after-free flaw in Windows Kernel-Mode Drivers. Microsoft’s description says an authorized attacker can execute code over a network, but its FAQ adds two important constraints: the attacker needs low privileges, and exploitation requires a user to initiate a connection to a malicious server controlled by the attacker.
That combination is why the bug lands in the awkward middle ground of Patch Tuesday triage. It is not a wormable unauthenticated network RCE. It is also not a purely local privilege escalation bug that can be delayed behind internet-facing emergency fixes. It is a network-reachable kernel memory flaw with user interaction and domain context baked into the attack story.
NVMe over Fabrics is designed to extend NVMe’s low-latency storage model across a network fabric. In practice, it belongs to the world of high-performance storage arrays, converged infrastructure, and data center systems where servers connect to storage targets rather than local disks. That means CVE-2026-34332 is probably irrelevant to many ordinary Windows installations, but potentially more interesting in environments that are explicitly built around performance and centralization.
The attack path Microsoft describes is also asymmetric in a way defenders should notice. The target system must initiate a connection to an attacker-controlled server. That makes the exploit less convenient than a direct inbound attack, but it does not make it theoretical. Attackers who already have a beachhead in a domain, or who can influence storage discovery, configuration, scripts, or administrator behavior, may be able to arrange the conditions Microsoft describes.
This is why the CVSS vector deserves a careful reading rather than a quick glance at the 8.0 score. Attack vector is network, attack complexity is low, privileges required are low, user interaction is required, and the impact to confidentiality, integrity, and availability is high. The shape of the score tells us this is not a drive-by internet bug, but it is serious once an attacker is inside the right operational lane.
In user-mode applications, that can be bad enough. In kernel-mode drivers, the stakes are higher because the vulnerable code runs with privileges ordinary processes do not have. A successful exploit in this class can mean code execution in a security context that undermines the boundary between application compromise and operating system compromise.
Microsoft’s advisory says the vulnerability can lead to remote code execution, not merely denial of service. That matters. Some malformed protocol parsing bugs crash a service and ruin an administrator’s day; this one is assessed as capable of running code, with high impact across confidentiality, integrity, and availability.
The mitigating factor is not the weakness class but the choreography. The attacker must be authorized on the domain and must wait for a user to connect to the malicious server. In other words, CVE-2026-34332 looks less like a first-stage perimeter break and more like a post-compromise or lateral-movement enabler in environments where storage protocols and domain trust intersect.
The advisory’s confidence metric is also telling. The CVSS vector includes “RC:C,” meaning report confidence is complete. Microsoft is not merely acknowledging a rumor or an incomplete report. It is publishing a confirmed vulnerability with a concrete affected component class, weakness type, exploit condition, and patch path.
That distinction matters because attackers read the same advisory structure defenders do. The public information does not hand over exploit code, but it does reveal that a malformed NVMe-oF handshake response with an invalid header length is part of the bug’s trigger surface. For skilled vulnerability researchers, that is enough to focus attention.
Enterprises should therefore avoid the common mistake of equating “unlikely” with “unimportant.” The more accurate reading is that Microsoft does not expect broad, easy exploitation in the near term. That still leaves room for targeted interest in data centers, managed service environments, storage-heavy deployments, and organizations where Windows Server 2025 is already part of production infrastructure.
The fixed build numbers differ: the standard update moves Windows Server 2025 to build 10.0.26100.32860, while the hotpatch path lists 10.0.26100.32772. That split is not unusual in Microsoft’s newer servicing world, but it does mean administrators should verify outcome by build number and update history rather than assuming that “patched” is a single universal state.
For Windows Server 2025 fleets, this is where patch management becomes more than a compliance checkbox. If systems are eligible for hotpatching, administrators need to understand whether the deployed hotpatch actually remediates the CVE in their configuration. If systems are on the conventional cumulative update track, they need the standard security update and whatever reboot window the organization normally requires.
The vulnerability also reinforces why Server Core is not a substitute for servicing. A reduced user interface and smaller installed footprint are valuable, but they do not eliminate kernel-mode driver attack surface. If the server participates in the affected storage path, minimalism does not make the bug disappear.
Storage fabrics are especially sensitive because they collapse performance, trust, and availability into the same operational plane. A malicious or impersonated storage endpoint is not merely another server; it can become part of the handshake sequence for systems that expect storage responses to be fast, valid, and boring. Bugs live in the gap between those expectations and hostile input.
CVE-2026-34332 is therefore a useful reminder that “remote” does not always mean “internet-facing.” A vulnerability can be remote because the malicious data crosses a network, while still requiring internal placement, domain access, or a tricked administrative workflow. Those are exactly the conditions many real intrusions create before defenders realize the incident has become serious.
This is also where segmentation earns its keep. Storage networks, management networks, and general-purpose user networks should not be casually interchangeable. If a low-privileged domain user can induce high-value servers to initiate sensitive storage connections to untrusted endpoints, the problem is larger than one CVE.
The lack of reported exploitation helps reduce emergency pressure, but the affected product list makes asset inventory unusually important. This is not a Windows 10, Windows 11, and every supported server release problem. It is a Windows Server 2025 problem, including Server Core. That specificity should make detection easier for mature shops, and more embarrassing for shops that still do not know where their newest server OS is deployed.
Administrators should look for Windows Server 2025 systems that use or test NVMe-oF, participate in storage fabric pilots, or sit in lab environments that are quietly connected to production identity. Early adoption environments often have weaker monitoring and looser change control than mature production clusters, precisely because they are considered “not fully live” until the day they suddenly are.
The other risk is third-party abstraction. Many administrators do not think in terms of NVMe-oF handshakes; they think in terms of storage appliances, vendor dashboards, hyperconverged stacks, and automation. If those layers cause Windows Server 2025 machines to initiate the relevant connections, the exposure may exist even when no one has manually configured a feature by name in months.
The second line of defense is to reduce the chance that a malicious storage endpoint ever becomes part of a legitimate workflow. That means reviewing who can configure storage targets, which systems can initiate NVMe-oF sessions, and whether storage-related traffic is constrained to expected networks. If this sounds like network hygiene rather than vulnerability management, that is the point.
The third line is monitoring for the weirdness that would precede exploitation. Unexpected outbound connections from Windows Server 2025 systems to unfamiliar storage endpoints should be rare. So should configuration changes that introduce new storage targets outside a known change window. Those signals are more useful than waiting for a clean exploit signature that may not exist yet.
Finally, organizations should treat “user interaction required” as a mitigation only if they understand which user is involved. In a server context, the “user” may be an administrator, service operator, automation account, or process performing a connection workflow. Human caution helps, but architecture helps more.
That tension is not hypocrisy; it is the reality of operating systems. Windows has to support new hardware paths, storage models, compatibility layers, and data center protocols. Every new high-performance interface expands the amount of privileged code that must parse untrusted or semi-trusted input correctly.
For defenders, the lesson is to stop treating kernel vulnerabilities as a single bucket. A Win32k local privilege escalation, a storage driver RCE, a network stack bug, and a filesystem parsing flaw all live near the kernel, but their operational risks differ sharply. The useful question is not “kernel or not?” but “which workflow brings attacker-controlled data to privileged code?”
CVE-2026-34332 answers that question with unusual clarity. The workflow is an NVMe-oF connection handshake. The attacker’s role is a malicious server prepared before the connection. The victim condition is a Windows Server 2025 machine that initiates the relevant connection under circumstances an attacker can influence.
This is where a good vulnerability-management program proves its value. It does not merely sort CVEs by score. It routes them to the teams that understand the affected workflow. A kernel-mode driver RCE tied to NVMe-oF should land in front of Windows administrators, storage engineers, network segmentation owners, and incident responders.
The remediation itself may be straightforward, but the validation is not. After patching, teams should confirm that the server build number matches Microsoft’s fixed build for the update path used. They should also confirm that storage connectivity still behaves as expected, especially in clusters or high-availability arrangements where a reboot or driver update can expose brittle dependencies.
The worst outcome would be to delay the patch because the vulnerability is “unlikely,” then discover months later that a storage pilot, lab fabric, or automation path quietly created the exact preconditions Microsoft described. The second-worst outcome would be to patch blindly and break a critical storage workflow because no one tested the path that made the server valuable in the first place.
That combination suggests a threat model closer to targeted enterprise intrusion than mass exploitation. An attacker who has no access and no way to induce a connection has a hard time using this bug. An attacker already operating inside a domain, with knowledge of storage workflows or the ability to influence them, has a much more interesting opportunity.
This is why the bug should matter to defenders even if it never becomes a headline-grabbing zero-day. Many damaging intrusions are not built from one spectacular exploit. They are assembled from footholds, credentials, misconfigurations, trusted workflows, and vulnerabilities that turn limited access into control over higher-value systems.
The kernel-mode nature of the flaw raises the ceiling of what could happen after successful exploitation. The NVMe-oF requirement narrows the set of likely targets. Together, those facts make CVE-2026-34332 a classic enterprise-risk CVE: too specific for panic, too privileged for complacency.
That second task is harder, and therefore more valuable. It forces organizations to map the seam between identity, storage, and server configuration. It also forces a conversation about whether storage fabrics are isolated as critical infrastructure or treated as just another reachable internal service.
The advisory’s “not exploited” status buys time for orderly remediation. It does not justify neglect. Once the patch is public, the race changes from “does anyone know?” to “who can reproduce enough of the bug to matter?” Microsoft has provided enough technical contour for defenders to prioritize intelligently, and enough for attackers to become curious.
The best response is not alarmism. It is a clean inventory, timely update deployment, storage-path validation, and a hard look at whether low-privileged domain access can influence high-value server connections.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Microsoft’s “Important” Label Hides a Very Server-Specific Risk
Microsoft’s “Important” Label Hides a Very Server-Specific Risk
CVE-2026-34332 is not the kind of vulnerability that should send every Windows desktop user sprinting for the update button in a panic. The affected products Microsoft lists are Windows Server 2025 and Windows Server 2025 Server Core, both on x64. That narrows the blast radius considerably.But it also sharpens the concern. Server Core is exactly where many organizations put roles they want stripped down, automated, and left alone. Windows Server 2025 is also the generation Microsoft wants enterprises to treat as the forward-looking platform for hybrid infrastructure, security baselines, and update modernization.
The vulnerability is a use-after-free flaw in Windows Kernel-Mode Drivers. Microsoft’s description says an authorized attacker can execute code over a network, but its FAQ adds two important constraints: the attacker needs low privileges, and exploitation requires a user to initiate a connection to a malicious server controlled by the attacker.
That combination is why the bug lands in the awkward middle ground of Patch Tuesday triage. It is not a wormable unauthenticated network RCE. It is also not a purely local privilege escalation bug that can be delayed behind internet-facing emergency fixes. It is a network-reachable kernel memory flaw with user interaction and domain context baked into the attack story.
The NVMe-oF Detail Is the Real Plot Twist
Microsoft’s most revealing note is that exploitation involves a specially crafted NVMe over Fabrics response message during the connection handshake process, containing an invalid header length value. That sentence does a lot of work. It points away from the broad, vague “kernel driver” bucket and toward a specific class of enterprise infrastructure: networked storage.NVMe over Fabrics is designed to extend NVMe’s low-latency storage model across a network fabric. In practice, it belongs to the world of high-performance storage arrays, converged infrastructure, and data center systems where servers connect to storage targets rather than local disks. That means CVE-2026-34332 is probably irrelevant to many ordinary Windows installations, but potentially more interesting in environments that are explicitly built around performance and centralization.
The attack path Microsoft describes is also asymmetric in a way defenders should notice. The target system must initiate a connection to an attacker-controlled server. That makes the exploit less convenient than a direct inbound attack, but it does not make it theoretical. Attackers who already have a beachhead in a domain, or who can influence storage discovery, configuration, scripts, or administrator behavior, may be able to arrange the conditions Microsoft describes.
This is why the CVSS vector deserves a careful reading rather than a quick glance at the 8.0 score. Attack vector is network, attack complexity is low, privileges required are low, user interaction is required, and the impact to confidentiality, integrity, and availability is high. The shape of the score tells us this is not a drive-by internet bug, but it is serious once an attacker is inside the right operational lane.
Use-After-Free Still Haunts the Kernel
A use-after-free bug is one of those vulnerability classes that sounds academic until it appears in the kernel. The basic pattern is old: software frees a chunk of memory, then later continues to use a pointer to that memory as if it still owned it. If an attacker can influence what occupies that memory afterward, stale assumptions become executable consequences.In user-mode applications, that can be bad enough. In kernel-mode drivers, the stakes are higher because the vulnerable code runs with privileges ordinary processes do not have. A successful exploit in this class can mean code execution in a security context that undermines the boundary between application compromise and operating system compromise.
Microsoft’s advisory says the vulnerability can lead to remote code execution, not merely denial of service. That matters. Some malformed protocol parsing bugs crash a service and ruin an administrator’s day; this one is assessed as capable of running code, with high impact across confidentiality, integrity, and availability.
The mitigating factor is not the weakness class but the choreography. The attacker must be authorized on the domain and must wait for a user to connect to the malicious server. In other words, CVE-2026-34332 looks less like a first-stage perimeter break and more like a post-compromise or lateral-movement enabler in environments where storage protocols and domain trust intersect.
“Exploitation Unlikely” Is Not a Permission Slip
Microsoft rates exploitation of the latest software release as unlikely, and says the vulnerability was not publicly disclosed or exploited at publication. That is welcome news, especially on a Patch Tuesday that already gives administrators plenty to test. But exploitation-likelihood labels are not risk absolution; they are one input into scheduling.The advisory’s confidence metric is also telling. The CVSS vector includes “RC:C,” meaning report confidence is complete. Microsoft is not merely acknowledging a rumor or an incomplete report. It is publishing a confirmed vulnerability with a concrete affected component class, weakness type, exploit condition, and patch path.
That distinction matters because attackers read the same advisory structure defenders do. The public information does not hand over exploit code, but it does reveal that a malformed NVMe-oF handshake response with an invalid header length is part of the bug’s trigger surface. For skilled vulnerability researchers, that is enough to focus attention.
Enterprises should therefore avoid the common mistake of equating “unlikely” with “unimportant.” The more accurate reading is that Microsoft does not expect broad, easy exploitation in the near term. That still leaves room for targeted interest in data centers, managed service environments, storage-heavy deployments, and organizations where Windows Server 2025 is already part of production infrastructure.
Hotpatching Gets a Security Test, Not a Victory Lap
The remediation table lists KB5087539 as the standard security update and KB5087423 as a security hotpatch update. Both require a reboot according to Microsoft’s affected product data, which is a reminder that the word hotpatch does not magically erase operational planning. Even when update technology improves, kernel-level fixes still demand care.The fixed build numbers differ: the standard update moves Windows Server 2025 to build 10.0.26100.32860, while the hotpatch path lists 10.0.26100.32772. That split is not unusual in Microsoft’s newer servicing world, but it does mean administrators should verify outcome by build number and update history rather than assuming that “patched” is a single universal state.
For Windows Server 2025 fleets, this is where patch management becomes more than a compliance checkbox. If systems are eligible for hotpatching, administrators need to understand whether the deployed hotpatch actually remediates the CVE in their configuration. If systems are on the conventional cumulative update track, they need the standard security update and whatever reboot window the organization normally requires.
The vulnerability also reinforces why Server Core is not a substitute for servicing. A reduced user interface and smaller installed footprint are valuable, but they do not eliminate kernel-mode driver attack surface. If the server participates in the affected storage path, minimalism does not make the bug disappear.
Storage Fabrics Turn Trust Into Attack Surface
The phrase “authorized attacker on the domain” can lull defenders into thinking the vulnerability is already behind the moat. That view belongs to an older network model. In 2026, domain authorization is often exactly what attackers obtain early, then stretch through lateral movement, delegated access, misconfigured service accounts, and administrative tooling.Storage fabrics are especially sensitive because they collapse performance, trust, and availability into the same operational plane. A malicious or impersonated storage endpoint is not merely another server; it can become part of the handshake sequence for systems that expect storage responses to be fast, valid, and boring. Bugs live in the gap between those expectations and hostile input.
CVE-2026-34332 is therefore a useful reminder that “remote” does not always mean “internet-facing.” A vulnerability can be remote because the malicious data crosses a network, while still requiring internal placement, domain access, or a tricked administrative workflow. Those are exactly the conditions many real intrusions create before defenders realize the incident has become serious.
This is also where segmentation earns its keep. Storage networks, management networks, and general-purpose user networks should not be casually interchangeable. If a low-privileged domain user can induce high-value servers to initiate sensitive storage connections to untrusted endpoints, the problem is larger than one CVE.
The Patch Tuesday Noise Makes This Easy to Miss
May 2026’s Microsoft Patch Tuesday is large enough that many teams will triage by severity, exploitation status, and asset exposure. That is rational. It is also how a server-specific kernel RCE can fall through the cracks when it is rated Important rather than Critical.The lack of reported exploitation helps reduce emergency pressure, but the affected product list makes asset inventory unusually important. This is not a Windows 10, Windows 11, and every supported server release problem. It is a Windows Server 2025 problem, including Server Core. That specificity should make detection easier for mature shops, and more embarrassing for shops that still do not know where their newest server OS is deployed.
Administrators should look for Windows Server 2025 systems that use or test NVMe-oF, participate in storage fabric pilots, or sit in lab environments that are quietly connected to production identity. Early adoption environments often have weaker monitoring and looser change control than mature production clusters, precisely because they are considered “not fully live” until the day they suddenly are.
The other risk is third-party abstraction. Many administrators do not think in terms of NVMe-oF handshakes; they think in terms of storage appliances, vendor dashboards, hyperconverged stacks, and automation. If those layers cause Windows Server 2025 machines to initiate the relevant connections, the exposure may exist even when no one has manually configured a feature by name in months.
The Practical Defense Is Boring, Which Is Why It Works
The first line of defense is to apply the appropriate Microsoft update. That sounds obvious, but with Server 2025, hotpatch eligibility, cumulative update baselines, and maintenance windows can produce a surprising amount of ambiguity. Security teams should ask for evidence of installed KBs or fixed build numbers, not just “the May updates are done.”The second line of defense is to reduce the chance that a malicious storage endpoint ever becomes part of a legitimate workflow. That means reviewing who can configure storage targets, which systems can initiate NVMe-oF sessions, and whether storage-related traffic is constrained to expected networks. If this sounds like network hygiene rather than vulnerability management, that is the point.
The third line is monitoring for the weirdness that would precede exploitation. Unexpected outbound connections from Windows Server 2025 systems to unfamiliar storage endpoints should be rare. So should configuration changes that introduce new storage targets outside a known change window. Those signals are more useful than waiting for a clean exploit signature that may not exist yet.
Finally, organizations should treat “user interaction required” as a mitigation only if they understand which user is involved. In a server context, the “user” may be an administrator, service operator, automation account, or process performing a connection workflow. Human caution helps, but architecture helps more.
The Windows Server 2025 Lesson Is Bigger Than One CVE
CVE-2026-34332 arrives at a moment when Microsoft is trying to make Windows Server feel more cloud-like in its servicing and more modern in its security posture. Hotpatching, secured-core assumptions, virtualization-based protections, and improved defaults all push in that direction. But kernel driver bugs remain a stubbornly traditional kind of risk.That tension is not hypocrisy; it is the reality of operating systems. Windows has to support new hardware paths, storage models, compatibility layers, and data center protocols. Every new high-performance interface expands the amount of privileged code that must parse untrusted or semi-trusted input correctly.
For defenders, the lesson is to stop treating kernel vulnerabilities as a single bucket. A Win32k local privilege escalation, a storage driver RCE, a network stack bug, and a filesystem parsing flaw all live near the kernel, but their operational risks differ sharply. The useful question is not “kernel or not?” but “which workflow brings attacker-controlled data to privileged code?”
CVE-2026-34332 answers that question with unusual clarity. The workflow is an NVMe-oF connection handshake. The attacker’s role is a malicious server prepared before the connection. The victim condition is a Windows Server 2025 machine that initiates the relevant connection under circumstances an attacker can influence.
The Patch Belongs on the Storage Calendar, Not Just the Security Calendar
For many organizations, the security team will see CVE-2026-34332 before the storage team does. That is a coordination problem. The people who understand NVMe-oF exposure, storage zoning, target discovery, and operational dependency may not be the same people who read MSRC advisories at release time.This is where a good vulnerability-management program proves its value. It does not merely sort CVEs by score. It routes them to the teams that understand the affected workflow. A kernel-mode driver RCE tied to NVMe-oF should land in front of Windows administrators, storage engineers, network segmentation owners, and incident responders.
The remediation itself may be straightforward, but the validation is not. After patching, teams should confirm that the server build number matches Microsoft’s fixed build for the update path used. They should also confirm that storage connectivity still behaves as expected, especially in clusters or high-availability arrangements where a reboot or driver update can expose brittle dependencies.
The worst outcome would be to delay the patch because the vulnerability is “unlikely,” then discover months later that a storage pilot, lab fabric, or automation path quietly created the exact preconditions Microsoft described. The second-worst outcome would be to patch blindly and break a critical storage workflow because no one tested the path that made the server valuable in the first place.
The CVSS Score Says “High,” but the Scenario Says “Targeted”
A base score of 8.0 is serious, but not self-explanatory. The vulnerability earns that score because the potential impact is high across confidentiality, integrity, and availability. It does not climb higher because exploitation requires low privileges and user interaction.That combination suggests a threat model closer to targeted enterprise intrusion than mass exploitation. An attacker who has no access and no way to induce a connection has a hard time using this bug. An attacker already operating inside a domain, with knowledge of storage workflows or the ability to influence them, has a much more interesting opportunity.
This is why the bug should matter to defenders even if it never becomes a headline-grabbing zero-day. Many damaging intrusions are not built from one spectacular exploit. They are assembled from footholds, credentials, misconfigurations, trusted workflows, and vulnerabilities that turn limited access into control over higher-value systems.
The kernel-mode nature of the flaw raises the ceiling of what could happen after successful exploitation. The NVMe-oF requirement narrows the set of likely targets. Together, those facts make CVE-2026-34332 a classic enterprise-risk CVE: too specific for panic, too privileged for complacency.
Windows Admins Get a Narrow Warning With Broad Implications
The concrete action is simple: patch Windows Server 2025 and Server Core systems using the applicable May 2026 security update path. The broader action is to understand where Windows servers are making storage connections and whether those connections can be steered by someone who should not have that power.That second task is harder, and therefore more valuable. It forces organizations to map the seam between identity, storage, and server configuration. It also forces a conversation about whether storage fabrics are isolated as critical infrastructure or treated as just another reachable internal service.
The advisory’s “not exploited” status buys time for orderly remediation. It does not justify neglect. Once the patch is public, the race changes from “does anyone know?” to “who can reproduce enough of the bug to matter?” Microsoft has provided enough technical contour for defenders to prioritize intelligently, and enough for attackers to become curious.
The best response is not alarmism. It is a clean inventory, timely update deployment, storage-path validation, and a hard look at whether low-privileged domain access can influence high-value server connections.
The May 2026 Server Patch That Rewards Teams Who Know Their Fabric
CVE-2026-34332 is a small entry in a large Patch Tuesday, but it rewards organizations that can connect security advisories to real architecture. The teams that know where Windows Server 2025 is deployed, how it talks to storage, and which update path it follows will handle this cleanly. The teams that rely on severity labels alone will have to guess.- Microsoft disclosed CVE-2026-34332 on May 12, 2026, and rated it Important with a CVSS 3.1 base score of 8.0.
- The affected platforms listed by Microsoft are Windows Server 2025 and Windows Server 2025 Server Core on x64.
- The vulnerability is a use-after-free flaw in Windows Kernel-Mode Drivers that can allow remote code execution over a network.
- Microsoft says exploitation requires an authorized attacker on the domain and a user-initiated connection to a malicious server.
- The exploit scenario involves a crafted NVMe-oF response during a connection handshake, making storage architecture central to real-world risk.
- Administrators should validate remediation through KB5087539 or KB5087423 installation status and the corresponding fixed build numbers.
Source: MSRC Security Update Guide - Microsoft Security Response Center