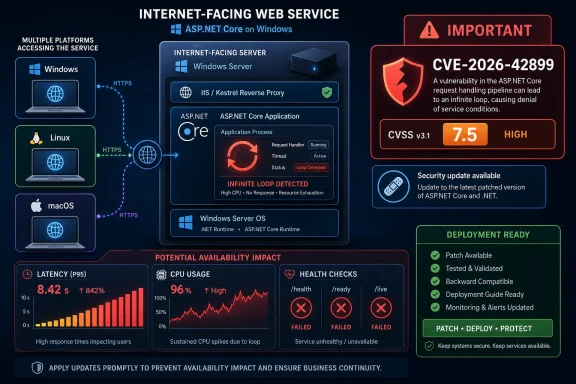
Microsoft disclosed CVE-2026-42899 on May 12, 2026, as an Important-rated ASP.NET Core denial-of-service vulnerability caused by an infinite-loop condition, affecting supported .NET 8.0, .NET 9.0, and .NET 10.0 installations across Windows, Linux, and macOS. The bug is not a data-theft story, not a privilege-escalation story, and not, at least at publication, an active-exploitation story. It is something more familiar to anyone running web workloads at scale: a remote, unauthenticated availability flaw in a platform many organizations treat as plumbing. Microsoft’s fix is available, but the real question for administrators is how quickly “Important” becomes urgent when the affected component sits on the public edge.
The headline severity on CVE-2026-42899 is not Critical, and that matters. Microsoft’s scoring places the vulnerability at CVSS 7.5 for the base score and 6.5 once temporal factors are applied, which reflects a real but bounded risk. There is no confidentiality impact, no integrity impact, and no scope change in the CVSS vector.
But the rest of the vector should keep sysadmins awake enough to patch deliberately rather than lazily. The attack vector is network, attack complexity is low, privileges are not required, and user interaction is not required. That is the shape of a vulnerability that can be attempted directly against exposed services if the vulnerable code path is reachable.
The availability impact is rated high. In plain English, Microsoft is saying that successful exploitation can deny service to the affected ASP.NET Core application or component, even though the advisory does not describe a route to steal secrets or modify data. For public APIs, customer portals, authentication front ends, and internal business apps with thin tolerance for downtime, that distinction is important but not comforting.
The weakness classification is also unusually plain: a loop with an unreachable exit condition, better known as an infinite loop. That is not the exotic cryptographic failure or speculative parser ambiguity that makes for conference-stage drama. It is the old software truth that a single request path, handled badly enough, can turn a server’s availability into an attacker-controlled resource.
CVE-2026-42899 is a useful reminder that “availability” is not the junior member of the security triad when the application is revenue-facing or mission-critical. If a crafted request can push a service into a pathological loop, the blast radius is not measured only in compromised records. It is measured in failed logins, angry customers, exhausted autoscaling budgets, incident bridges, and the awkward realization that a security patch has become a business-continuity issue.
The advisory’s description is sparse, as Microsoft advisories often are at publication. It says that a loop with an unreachable exit condition in ASP.NET Core allows an unauthorized attacker to deny service over a network. That is enough to prioritize the update, but not enough to reverse-engineer the precise vulnerable path from the text alone.
That restraint is intentional. The advisory confirms the existence of the vulnerability and the affected product lines without handing attackers a walk-through. For defenders, however, the lack of implementation detail shifts the work from “block this one pattern” to “patch the runtime and redeploy where necessary.”
That does not make the bug Critical by stealth. The lack of confidentiality and integrity impact is significant, and the unchanged scope suggests the damage remains inside the vulnerable component’s authority. An attacker is not being credited with taking over the machine, escaping trust boundaries, or changing protected resources.
Still, a remote unauthenticated DoS has a different risk profile from a local or post-authentication DoS. A vulnerability that requires a valid account can often be constrained by access controls, monitoring, or rate limits tied to identity. A vulnerability reachable before authentication, or reachable from arbitrary clients over the network, lives closer to the hostile internet.
The temporal score reduction is also worth unpacking. Microsoft lists exploit code maturity as unproven, remediation level as official fix, and report confidence as confirmed. That combination means the bug is real and patched, but Microsoft was not reporting public exploit code or known exploitation at the time the advisory was published. It is the classic Patch Tuesday middle ground: confirmed enough to fix now, not yet noisy enough to justify panic.
But “unlikely” is not the same as “irrelevant.” It is a forecast at a point in time, not a guarantee about the next week. Once a patch ships, attackers can compare vulnerable and fixed builds, inspect changed code, and look for the condition Microsoft described. That process is not always fast, but it is routine enough that defenders should treat the publication of a fix as the beginning of a race, not the end of the story.
This is especially true in the .NET world, where many deployments are not updated by a single Windows Update event on a single server. Some applications run framework-dependent and consume a shared runtime. Others are self-contained and must be rebuilt and redeployed before the new runtime code matters. Containerized services may need new base images, new application images, and a rollout through staging before production sees any protection.
The advisory’s “customer action required” flag is therefore doing real work. If your estate includes ASP.NET Core workloads, merely observing that Microsoft released a fix is not remediation. Someone has to confirm which runtimes are installed, which applications carry their own runtime, which container images are pinned, and which servers are still running older servicing levels because they have become too important to reboot casually.
For Windows admins, the familiar patch-management machinery may cover some runtime installations, particularly where the runtime is centrally installed and maintained. But modern .NET deployment patterns complicate the picture. A server can be patched while an application continues to carry an older self-contained runtime. A container host can be current while the image it runs remains stale. A developer workstation can be updated while the CI pipeline continues to build from an old SDK image.
Linux and macOS entries in the advisory are not a footnote. They are a reflection of how ASP.NET Core is actually used: in containers, Kubernetes clusters, cross-platform development environments, and mixed hosting fleets where the Windows team may not own every affected asset. The operational owner of the vulnerable runtime may be the platform team, the application team, the DevOps group, or a vendor.
That is where many .NET vulnerabilities become less about downloading a patch and more about inventory discipline. If you cannot answer which production services run .NET 8, 9, or 10, and whether they are framework-dependent or self-contained, CVE-2026-42899 is not just a patch ticket. It is an audit of whether your runtime supply chain is knowable under pressure.
Infinite-loop DoS bugs have an unpleasant asymmetry. The attacker may need to send only a small amount of input, while the server spends disproportionate CPU time failing to complete the work. If the affected path is available to unauthenticated clients, the economics are even worse for the defender.
The advisory does not state which ASP.NET Core feature or request pattern triggers CVE-2026-42899. That omission limits responsible public analysis. But the general failure mode is familiar to anyone who has debugged a production service locked in a hot loop: threads stop doing useful work, CPU climbs, latency spreads, health checks begin to fail, and autoscaling may amplify cost before it restores stability.
The deeper lesson is that availability bugs sit at the intersection of code correctness and infrastructure design. Patching removes the known flaw. Rate limiting, request-size limits, circuit breakers, concurrency caps, and meaningful health probes reduce the chance that the next unknown flaw becomes a full outage. CVE-2026-42899 is a runtime vulnerability, but production resilience is still an application and platform responsibility.
This is the quiet shift in Microsoft security work: developer frameworks are infrastructure. Kestrel, ASP.NET Core middleware, runtime libraries, serialization paths, HTTP handling, and hosting components are no longer background dependencies that application teams can update at leisure. They are exposed surfaces.
The May 12 advisory underscores that shift without much fanfare. It affects supported .NET lines across operating systems, has an official fix, and requires customer action. It also carries no evidence of exploitation at publication. That combination is precisely what makes it easy to underreact.
Enterprise patching is full of tradeoffs, and not every 7.5 deserves emergency treatment. But public ASP.NET Core endpoints deserve a different queue from dormant developer machines or isolated internal tools. The right response is not “drop everything everywhere.” It is “find the exposed services first, then move with purpose.”
Confirmed report confidence raises urgency in a subtle way. It does not mean exploitation is happening. It means the vendor acknowledges the vulnerability, and the known technical details are credible enough to support a security update. For risk teams, that removes the comfortable excuse that the issue may not be real.
At the same time, confirmed confidence does not imply that attackers have all the details. Microsoft also marks exploit code maturity as unproven and says the vulnerability was not publicly disclosed at release. In other words, the existence of the flaw is confirmed, while public weaponization was not known at publication.
That distinction is essential for sane prioritization. A confirmed, unexploited DoS in ASP.NET Core should not be treated like a wormable remote-code-execution crisis. It also should not sit untouched until the next quarterly maintenance window if it protects an internet-facing service. The advisory’s metrics point to a middle path: controlled urgency.
On servers with shared .NET runtimes, version checks can confirm whether the patched runtime is installed. In self-contained deployments, the application must be rebuilt against the fixed runtime and redeployed. In containers, teams need patched base images and new application images, not merely patched hosts. In managed hosting or platform-as-a-service environments, responsibility may be split between Microsoft, the platform operator, and the application owner.
This is where security advisories collide with organizational charts. The team that receives MSRC alerts may not own the Kubernetes manifests. The team that owns the CI pipeline may not know which CVEs matter to production. The team that manages Windows Server may have no visibility into Linux containers running ASP.NET Core behind an ingress controller.
CVE-2026-42899 is therefore a good forcing function for runtime governance. If you can map the advisory to affected apps in minutes, you are in decent shape. If you need a week of Slack archaeology to determine who owns the runtime version in production, the vulnerability has exposed a management bug as much as a software bug.
The difficulty is that those symptoms also look like ordinary bad traffic, poorly tuned code, or a marketing campaign that worked too well. That ambiguity is why response teams should pair version remediation with telemetry review. If a public ASP.NET Core service has seen unexplained availability events around the disclosure window, it is worth examining logs with the advisory in mind.
Network-layer controls can help, but they are not a substitute for the runtime update. Rate limiting, bot filtering, web application firewall rules, and upstream throttling may reduce exploitability if the trigger pattern is visible or if attacks require repeated requests. But when the vulnerable condition lives in application-framework behavior, generic edge controls may miss the path entirely.
The most practical defensive stance is layered and boring: patch the runtime, redeploy self-contained apps, refresh containers, verify production versions, and keep an eye on availability telemetry. That is not glamorous, but it is how most real security work gets done.
Source: MSRC Security Update Guide - Microsoft Security Response Center
 Microsoft’s “Important” Label Still Describes an Internet-Facing Problem
Microsoft’s “Important” Label Still Describes an Internet-Facing Problem
The headline severity on CVE-2026-42899 is not Critical, and that matters. Microsoft’s scoring places the vulnerability at CVSS 7.5 for the base score and 6.5 once temporal factors are applied, which reflects a real but bounded risk. There is no confidentiality impact, no integrity impact, and no scope change in the CVSS vector.But the rest of the vector should keep sysadmins awake enough to patch deliberately rather than lazily. The attack vector is network, attack complexity is low, privileges are not required, and user interaction is not required. That is the shape of a vulnerability that can be attempted directly against exposed services if the vulnerable code path is reachable.
The availability impact is rated high. In plain English, Microsoft is saying that successful exploitation can deny service to the affected ASP.NET Core application or component, even though the advisory does not describe a route to steal secrets or modify data. For public APIs, customer portals, authentication front ends, and internal business apps with thin tolerance for downtime, that distinction is important but not comforting.
The weakness classification is also unusually plain: a loop with an unreachable exit condition, better known as an infinite loop. That is not the exotic cryptographic failure or speculative parser ambiguity that makes for conference-stage drama. It is the old software truth that a single request path, handled badly enough, can turn a server’s availability into an attacker-controlled resource.
The Bug Is Boring in the Way Production Incidents Are Boring
Denial-of-service vulnerabilities rarely command the same attention as remote code execution or credential theft, because they do not promise the cinematic payoff of shells, domain compromise, or mass exfiltration. That bias is understandable, but it can be dangerous. The operational cost of a reliable DoS can be immediate, measurable, and public.CVE-2026-42899 is a useful reminder that “availability” is not the junior member of the security triad when the application is revenue-facing or mission-critical. If a crafted request can push a service into a pathological loop, the blast radius is not measured only in compromised records. It is measured in failed logins, angry customers, exhausted autoscaling budgets, incident bridges, and the awkward realization that a security patch has become a business-continuity issue.
The advisory’s description is sparse, as Microsoft advisories often are at publication. It says that a loop with an unreachable exit condition in ASP.NET Core allows an unauthorized attacker to deny service over a network. That is enough to prioritize the update, but not enough to reverse-engineer the precise vulnerable path from the text alone.
That restraint is intentional. The advisory confirms the existence of the vulnerability and the affected product lines without handing attackers a walk-through. For defenders, however, the lack of implementation detail shifts the work from “block this one pattern” to “patch the runtime and redeploy where necessary.”
The CVSS Vector Tells a Sharper Story Than the Severity Word
Security teams often read the severity word first and the vector string second, if they read the vector at all. CVE-2026-42899 is a case where that habit can mislead. “Important” sounds like a second-tier problem; the vector says remote, unauthenticated, low-complexity, no-click, high-availability impact.That does not make the bug Critical by stealth. The lack of confidentiality and integrity impact is significant, and the unchanged scope suggests the damage remains inside the vulnerable component’s authority. An attacker is not being credited with taking over the machine, escaping trust boundaries, or changing protected resources.
Still, a remote unauthenticated DoS has a different risk profile from a local or post-authentication DoS. A vulnerability that requires a valid account can often be constrained by access controls, monitoring, or rate limits tied to identity. A vulnerability reachable before authentication, or reachable from arbitrary clients over the network, lives closer to the hostile internet.
The temporal score reduction is also worth unpacking. Microsoft lists exploit code maturity as unproven, remediation level as official fix, and report confidence as confirmed. That combination means the bug is real and patched, but Microsoft was not reporting public exploit code or known exploitation at the time the advisory was published. It is the classic Patch Tuesday middle ground: confirmed enough to fix now, not yet noisy enough to justify panic.
“Exploitation Unlikely” Is Not a Permission Slip
Microsoft’s exploitability assessment says exploitation is unlikely, and the advisory marks the issue as not publicly disclosed and not exploited at original publication. Those are useful signals. They should influence triage, especially in organizations drowning in patch queues.But “unlikely” is not the same as “irrelevant.” It is a forecast at a point in time, not a guarantee about the next week. Once a patch ships, attackers can compare vulnerable and fixed builds, inspect changed code, and look for the condition Microsoft described. That process is not always fast, but it is routine enough that defenders should treat the publication of a fix as the beginning of a race, not the end of the story.
This is especially true in the .NET world, where many deployments are not updated by a single Windows Update event on a single server. Some applications run framework-dependent and consume a shared runtime. Others are self-contained and must be rebuilt and redeployed before the new runtime code matters. Containerized services may need new base images, new application images, and a rollout through staging before production sees any protection.
The advisory’s “customer action required” flag is therefore doing real work. If your estate includes ASP.NET Core workloads, merely observing that Microsoft released a fix is not remediation. Someone has to confirm which runtimes are installed, which applications carry their own runtime, which container images are pinned, and which servers are still running older servicing levels because they have become too important to reboot casually.
Supported .NET Lines Get the Fix, but Deployment Models Decide the Work
The affected product table names .NET 8.0, .NET 9.0, and .NET 10.0 installations on Windows, Linux, and macOS. Microsoft lists fixed build numbers 8.0.27, 9.0.16, and 10.0.8. That spread matters because ASP.NET Core is not only a Windows server technology anymore, and it has not been for a long time.For Windows admins, the familiar patch-management machinery may cover some runtime installations, particularly where the runtime is centrally installed and maintained. But modern .NET deployment patterns complicate the picture. A server can be patched while an application continues to carry an older self-contained runtime. A container host can be current while the image it runs remains stale. A developer workstation can be updated while the CI pipeline continues to build from an old SDK image.
Linux and macOS entries in the advisory are not a footnote. They are a reflection of how ASP.NET Core is actually used: in containers, Kubernetes clusters, cross-platform development environments, and mixed hosting fleets where the Windows team may not own every affected asset. The operational owner of the vulnerable runtime may be the platform team, the application team, the DevOps group, or a vendor.
That is where many .NET vulnerabilities become less about downloading a patch and more about inventory discipline. If you cannot answer which production services run .NET 8, 9, or 10, and whether they are framework-dependent or self-contained, CVE-2026-42899 is not just a patch ticket. It is an audit of whether your runtime supply chain is knowable under pressure.
Infinite Loops Are a Small Bug Class With Large Operational Teeth
The CWE entry behind this vulnerability is CWE-835: loop with unreachable exit condition. In ordinary development terms, that means execution can enter a loop that does not terminate as expected. In security terms, the danger comes when an attacker can trigger that behavior repeatedly or cheaply enough to consume server resources.Infinite-loop DoS bugs have an unpleasant asymmetry. The attacker may need to send only a small amount of input, while the server spends disproportionate CPU time failing to complete the work. If the affected path is available to unauthenticated clients, the economics are even worse for the defender.
The advisory does not state which ASP.NET Core feature or request pattern triggers CVE-2026-42899. That omission limits responsible public analysis. But the general failure mode is familiar to anyone who has debugged a production service locked in a hot loop: threads stop doing useful work, CPU climbs, latency spreads, health checks begin to fail, and autoscaling may amplify cost before it restores stability.
The deeper lesson is that availability bugs sit at the intersection of code correctness and infrastructure design. Patching removes the known flaw. Rate limiting, request-size limits, circuit breakers, concurrency caps, and meaningful health probes reduce the chance that the next unknown flaw becomes a full outage. CVE-2026-42899 is a runtime vulnerability, but production resilience is still an application and platform responsibility.
Patch Tuesday Keeps Turning Developer Frameworks Into Front-Line Infrastructure
For years, Patch Tuesday coverage naturally centered on Windows clients, Windows Server, Office, Exchange, and browsers. That made sense when the most visible Microsoft security blast radius sat in desktop and server products. But ASP.NET Core advisories now belong in the same operational conversation, because the framework is often the public face of an organization’s services.This is the quiet shift in Microsoft security work: developer frameworks are infrastructure. Kestrel, ASP.NET Core middleware, runtime libraries, serialization paths, HTTP handling, and hosting components are no longer background dependencies that application teams can update at leisure. They are exposed surfaces.
The May 12 advisory underscores that shift without much fanfare. It affects supported .NET lines across operating systems, has an official fix, and requires customer action. It also carries no evidence of exploitation at publication. That combination is precisely what makes it easy to underreact.
Enterprise patching is full of tradeoffs, and not every 7.5 deserves emergency treatment. But public ASP.NET Core endpoints deserve a different queue from dormant developer machines or isolated internal tools. The right response is not “drop everything everywhere.” It is “find the exposed services first, then move with purpose.”
The “Confirmed” Report Confidence Cuts Both Ways
The text the user highlighted from the advisory concerns report confidence, one of the temporal CVSS metrics. For CVE-2026-42899, Microsoft marks report confidence as confirmed. That means defenders should not treat the advisory as speculative or rumor-driven.Confirmed report confidence raises urgency in a subtle way. It does not mean exploitation is happening. It means the vendor acknowledges the vulnerability, and the known technical details are credible enough to support a security update. For risk teams, that removes the comfortable excuse that the issue may not be real.
At the same time, confirmed confidence does not imply that attackers have all the details. Microsoft also marks exploit code maturity as unproven and says the vulnerability was not publicly disclosed at release. In other words, the existence of the flaw is confirmed, while public weaponization was not known at publication.
That distinction is essential for sane prioritization. A confirmed, unexploited DoS in ASP.NET Core should not be treated like a wormable remote-code-execution crisis. It also should not sit untouched until the next quarterly maintenance window if it protects an internet-facing service. The advisory’s metrics point to a middle path: controlled urgency.
The Real Remediation Test Is Whether Your Apps Actually Move
The official fix exists. That is the easy part. The harder part is proving that the fix has reached every place vulnerable ASP.NET Core code can run.On servers with shared .NET runtimes, version checks can confirm whether the patched runtime is installed. In self-contained deployments, the application must be rebuilt against the fixed runtime and redeployed. In containers, teams need patched base images and new application images, not merely patched hosts. In managed hosting or platform-as-a-service environments, responsibility may be split between Microsoft, the platform operator, and the application owner.
This is where security advisories collide with organizational charts. The team that receives MSRC alerts may not own the Kubernetes manifests. The team that owns the CI pipeline may not know which CVEs matter to production. The team that manages Windows Server may have no visibility into Linux containers running ASP.NET Core behind an ingress controller.
CVE-2026-42899 is therefore a good forcing function for runtime governance. If you can map the advisory to affected apps in minutes, you are in decent shape. If you need a week of Slack archaeology to determine who owns the runtime version in production, the vulnerability has exposed a management bug as much as a software bug.
Defenders Should Watch for Symptoms, Not Just Version Numbers
Patching is the primary fix, but operational monitoring still matters. A denial-of-service vulnerability may leave traces before anyone identifies it as exploitation. CPU spikes, thread-pool exhaustion, request latency, abnormal error rates, repeated requests to the same endpoint family, and load balancer health-check failures can all become early indicators.The difficulty is that those symptoms also look like ordinary bad traffic, poorly tuned code, or a marketing campaign that worked too well. That ambiguity is why response teams should pair version remediation with telemetry review. If a public ASP.NET Core service has seen unexplained availability events around the disclosure window, it is worth examining logs with the advisory in mind.
Network-layer controls can help, but they are not a substitute for the runtime update. Rate limiting, bot filtering, web application firewall rules, and upstream throttling may reduce exploitability if the trigger pattern is visible or if attacks require repeated requests. But when the vulnerable condition lives in application-framework behavior, generic edge controls may miss the path entirely.
The most practical defensive stance is layered and boring: patch the runtime, redeploy self-contained apps, refresh containers, verify production versions, and keep an eye on availability telemetry. That is not glamorous, but it is how most real security work gets done.
The May 2026 Advisory Rewards Teams That Know Their Runtime Estate
The most concrete lesson from CVE-2026-42899 is that ASP.NET Core patching is now an asset-management exercise as much as a vulnerability-management exercise. The advisory is specific enough to act on, but broad enough to catch organizations that have lost track of where .NET actually runs.- Microsoft released the CVE-2026-42899 advisory on May 12, 2026, for an ASP.NET Core denial-of-service vulnerability caused by an infinite-loop condition.
- The vulnerability is rated Important with a CVSS 3.1 base score of 7.5 and a temporal score of 6.5.
- The attack requires no privileges and no user interaction, and Microsoft rates the attack complexity as low over the network.
- Microsoft says the issue was not publicly disclosed and not exploited at the time of original publication, with exploitation assessed as unlikely.
- Fixed builds are listed as .NET 8.0.27, .NET 9.0.16, and .NET 10.0.8 across supported Windows, Linux, and macOS installations.
- Self-contained applications and containerized services may require rebuilds and redeployments before the patched runtime is actually in use.
Source: MSRC Security Update Guide - Microsoft Security Response Center