CVE-2026-43036 is a medium-severity Linux kernel networking flaw published on May 1, 2026, and modified by NVD on May 8, affecting multiple kernel release lines where TCPv4 GSO handling can read an unsafe IPv4 header field from PF_PACKET-injected traffic. The fix is small, almost boringly so: replace a direct header dereference with
The headline number for CVE-2026-43036 is not dramatic. NVD lists it as CVSS 5.5, with local access, low attack complexity, low privileges required, no user interaction, and high availability impact. In the blunt language of vulnerability triage, that usually means “patch in the next maintenance window unless your exposure model says otherwise.”
That would be a reasonable first reading, but not a complete one. This is a Linux kernel networking bug in code that sits on the path between packet buffers, offload decisions, and device feature negotiation. It was found by syzbot through a KMSAN uninitialized-value warning, not by a polished exploit chain dropped on a mailing list.
The difference matters because CVE-2026-43036 is not being sold as the next world-ending privilege escalation. It is more useful than that. It shows, in miniature, how Linux’s networking performance machinery can become security-relevant when a packet arrives through a path that does not look quite like the path the original code expected.
For WindowsForum readers, the obvious question is why a Linux kernel CVE belongs in the same security conversation as Microsoft’s update ecosystem. The answer is that Microsoft now ships, hosts, supports, or brokers Linux in too many places for “not Windows” to be a meaningful boundary. Azure Linux, AKS nodes, WSL development environments, Linux appliances, security tools, and mixed estates all collapse that distinction.
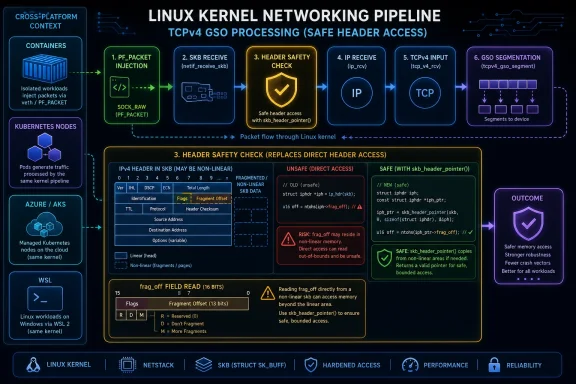
That design is central to modern throughput. It is also a place where the kernel has to make careful decisions about what a packet is, what headers it contains, and which device features are safe to use. In CVE-2026-43036, the relevant logic checks the IPv4
The problem is not that
The kernel’s socket buffer structure, the ubiquitous
The fix uses
That is the sort of patch that can look like mere hygiene. In kernel networking, hygiene is often the security boundary.
That origin story should shape how administrators interpret the advisory. This is not, based on the available public record, a vulnerability with a widely advertised exploit or a demonstrated remote compromise path. It is a kernel bug found by fuzzing, classified by NVD as a local availability issue, and repaired upstream through stable kernel commits.
But dismissing fuzz-found bugs as theoretical has become a bad habit. Many serious kernel vulnerabilities start as a sanitizer complaint, a strange crash, or an unreachable-looking edge case. Fuzzers are good precisely because they do not respect the neat mental model engineers carry around for “normal” packet flows.
PF_PACKET is a particularly interesting ingredient. It provides low-level packet interface access and is used by tools that capture, inject, or inspect traffic. That makes it relevant to administrators because it is not only a hacker toy; it is part of the ecosystem around packet sniffers, monitoring agents, test harnesses, intrusion detection, containers, and network appliances.
The CVSS vector says local privileges are required. In practice, the real risk depends on who can create or influence packets through the affected local paths on a given system. A locked-down server with no untrusted local users, no permissive containers, and no packet-injection workloads has a different exposure profile than a multi-tenant host, a lab box, or a Kubernetes node running workloads with more networking reach than the security team realizes.
This is where Linux patch management gets messy. Most production systems do not run a kernel downloaded directly from kernel.org with an upstream version number that maps cleanly to NVD’s CPE ranges. Enterprise distributions backport fixes. Cloud kernels carry vendor patches. Appliance vendors freeze branches. Container hosts may be managed by platform release trains rather than by package names that look obvious in a CVE entry.
The safest operational interpretation is not “am I running exactly 6.12.80?” It is “has my kernel vendor shipped the specific fix for TCPv4 GSO
NVD also notes that CVSS 4.0 has not yet been assessed. That is not unusual, but it is a reminder that vulnerability databases lag the engineering reality. The patch exists upstream, the affected ranges have been sketched, and vendors will continue folding the fix into their own supported trees. Waiting for every field in every database to look tidy is rarely a good security practice.
The “are we missing a CPE?” prompt on NVD pages is almost comic in this context. For Linux kernel CVEs, CPEs are a rough map, not the terrain. The real terrain is distribution packaging, kernel flavor, cloud image cadence, and whether your scanners understand backports.
Microsoft’s infrastructure and product portfolio now include substantial Linux responsibility. Azure hosts Linux at enormous scale. AKS depends on Linux node images for many clusters. Azure Linux Container Host has become a first-party Microsoft Linux distribution for cloud-native workloads. WSL made Linux kernels part of everyday developer life on Windows machines. Even Windows shops that never “chose Linux” may be running it indirectly through containers, appliances, CI/CD tools, network monitors, or cloud marketplace images.
That does not mean CVE-2026-43036 is a Windows vulnerability. It is not. It means Microsoft’s update and advisory surface has expanded to cover the systems customers actually run.
This matters for security teams because ownership lines are often blurrier than architecture diagrams admit. The Windows team may own endpoints, the cloud team may own AKS, the platform team may own base images, and developers may own WSL instances that quietly become part of build or test workflows. A kernel CVE listed by MSRC can land in all of those inboxes and still have no single obvious owner.
The right answer is not to panic every time MSRC lists a Linux kernel CVE. The right answer is to treat Microsoft’s presence in the advisory chain as evidence that Linux kernel lifecycle management is now part of the Microsoft estate for many organizations.
But availability is not a second-class security property in network infrastructure. A kernel networking crash on a workstation is irritating. The same class of failure on a virtualization host, container node, routing appliance, packet broker, VPN gateway, or build runner can be an outage.
There is also a subtle operational risk in the phrase “local.” Local kernel bugs are often triaged as lower priority because the attacker already needs some access. That logic is sound for single-user systems and less sound for shared machines. Containers, unprivileged users, CI jobs, and monitoring agents can all provide “local” footholds that are less trusted than the kernel code they may prod.
PF_PACKET makes that boundary especially worth examining. Many systems restrict raw packet capabilities by default, but the real world is full of exceptions. Packet capture tools need elevated permissions. Some containers are granted capabilities for debugging or network functions. Security products often run with exactly the sort of low-level access that would make a networking edge case reachable.
That does not turn CVE-2026-43036 into a confirmed privilege escalation. It does mean administrators should resist the lazy mental shortcut that local equals harmless. In shared and cloud-native systems, local is often where the interesting trust boundaries are.
That sounds obvious after the fact. It is not always obvious in the middle of performance-sensitive networking code where the fastest path is the common path, and the common path has historically worked. Linux networking is full of carefully optimized assumptions because the alternative is leaving performance on the floor for every packet on every machine.
The problem is that the unusual path eventually becomes a security path. Fuzzers construct packets no normal workload would generate. Virtual switches and container networks produce combinations that bare-metal assumptions did not anticipate. Offload features change where segmentation, checksumming, and header mutation happen. Encapsulation stacks headers inside headers until “the IPv4 header” becomes a contextual phrase rather than a stable pointer.
This is why the vulnerability’s description reads like an internal code-review comment rather than a security bulletin. The kernel was reading
Security engineering often advances in exactly this way. Not through a dramatic new mitigation, but through thousands of places where old direct access patterns are replaced by helpers that encode hard-won rules.
The obvious places are Azure virtual machines, Linux servers, and Kubernetes nodes. The less obvious places are network appliances, backup products, EDR components, NAS devices, hypervisor adjuncts, developer laptops running WSL, GitHub Actions or Azure DevOps runners, and containers whose host kernel is someone else’s responsibility until it suddenly is not.
Containers deserve special emphasis because they are often misunderstood in vulnerability conversations. A container image does not ship its own Linux kernel in the normal case. It shares the host kernel. That means rebuilding an application image will not fix a host kernel CVE. Updating the node image, host OS, managed cluster version, or underlying platform is the part that matters.
In AKS and similar managed environments, the patch plan is usually less about compiling a kernel and more about tracking node image releases, maintenance windows, upgrade channels, and whether node pools have actually been rotated. A cluster can show that an update is available while still running old nodes because workloads, budgets, or operational caution delayed the rollout.
WSL is another edge case. For most consumer and developer systems, CVE-2026-43036 is unlikely to be the highest-risk item on the board. But enterprises that use WSL in development workflows should treat its kernel as a managed component, not as a magical Linux bubble inside Windows. If developers can run packet tooling, privileged containers, or custom networking experiments, the distinction becomes more than academic.
That is why kernel CVEs need environmental scoring in practice. The base score says this is not a remote unauthenticated worm. Your architecture decides whether it is a routine maintenance item or a meaningful risk to shared infrastructure.
The most conservative reading is to patch affected systems on the next normal kernel maintenance cycle, prioritizing multi-user systems, container hosts, network appliances, and machines where untrusted code can exercise packet interfaces. That is not glamorous advice, but it matches the vulnerability.
Security teams should also be careful with scanner output. If a scanner keys only on upstream version ranges, it may flag patched vendor kernels as vulnerable or miss backported fixes under unfamiliar package names. Conversely, if a cloud image release note says the fix is present but nodes have not been recycled, the dashboard may look better than reality.
The real control is evidence. Confirm the running kernel, confirm the vendor package or image version, confirm the fix landed in that stream, and confirm the machine actually rebooted into the patched kernel. Kernel patching remains one of the places where “installed” and “running” are dangerously different verbs.
The practical effect is that administrators see more medium-severity kernel items with terse descriptions and upstream commit links. Some are exploitable in meaningful ways. Some are mostly sanitizer findings that harden obscure paths. Many sit in the uncomfortable middle where the impact is real but heavily dependent on configuration and reachability.
This forces a shift in how teams consume vulnerability feeds. Treating every kernel CVE as a fire drill is unsustainable. Treating them as noise is reckless. The better pattern is to group them by subsystem, affected kernel stream, exposed capability, and vendor patch availability.
CVE-2026-43036 belongs in the networking and packet-buffer bucket. It should raise the priority of systems that process untrusted local packet injection or run shared workloads with enhanced network capabilities. It should not cause the same response as a remotely reachable pre-authentication flaw in a default service.
That kind of nuanced triage is harder than counting CVSS scores. It is also the only way to survive modern kernel vulnerability disclosure without either burning out or missing the bug that matters.
CVE-2026-43036 is unlikely to be remembered as the Linux kernel scare of 2026, and that is probably appropriate. Its importance is quieter: a fuzzed packet path exposed an unsafe assumption, the kernel fixed it with a safer header-access helper, and the advisory now flows through ecosystems that include Microsoft as well as traditional Linux vendors. The future of patch management will look more like this, not less: cross-platform, cloud-shaped, noisy, and dependent on teams that can tell the difference between a modest bug and a modest bug in exactly the wrong place.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
skb_header_pointer() before checking frag_off. But that is exactly why this CVE matters. It is a reminder that modern kernel security increasingly turns on whether old assumptions about packet layout still survive in fuzzed, virtualized, containerized, offloaded networking stacks.
 A Medium CVE With a Kernel-Sized Lesson
A Medium CVE With a Kernel-Sized Lesson
The headline number for CVE-2026-43036 is not dramatic. NVD lists it as CVSS 5.5, with local access, low attack complexity, low privileges required, no user interaction, and high availability impact. In the blunt language of vulnerability triage, that usually means “patch in the next maintenance window unless your exposure model says otherwise.”That would be a reasonable first reading, but not a complete one. This is a Linux kernel networking bug in code that sits on the path between packet buffers, offload decisions, and device feature negotiation. It was found by syzbot through a KMSAN uninitialized-value warning, not by a polished exploit chain dropped on a mailing list.
The difference matters because CVE-2026-43036 is not being sold as the next world-ending privilege escalation. It is more useful than that. It shows, in miniature, how Linux’s networking performance machinery can become security-relevant when a packet arrives through a path that does not look quite like the path the original code expected.
For WindowsForum readers, the obvious question is why a Linux kernel CVE belongs in the same security conversation as Microsoft’s update ecosystem. The answer is that Microsoft now ships, hosts, supports, or brokers Linux in too many places for “not Windows” to be a meaningful boundary. Azure Linux, AKS nodes, WSL development environments, Linux appliances, security tools, and mixed estates all collapse that distinction.
The Bug Lives Where Fast Networking Meets Fragile Assumptions
The vulnerable code path sits in the Linux networking stack’s GSO feature checking. GSO, or Generic Segmentation Offload, is one of those performance mechanisms that most administrators benefit from without thinking about it. Instead of forcing the kernel to segment every large packet before handing it to a network device, GSO allows larger packets to move through parts of the stack and be segmented later, often by hardware or lower-level software paths.That design is central to modern throughput. It is also a place where the kernel has to make careful decisions about what a packet is, what headers it contains, and which device features are safe to use. In CVE-2026-43036, the relevant logic checks the IPv4
frag_off field while deciding whether to clear certain features related to packet ID mangling.The problem is not that
frag_off is exotic. It is a routine IPv4 header field used in fragmentation handling. The problem is how the code got to it.The kernel’s socket buffer structure, the ubiquitous
skb, is flexible by necessity. Packet data may be linear in memory, split across fragments, adjusted by encapsulation, pulled or pushed by layers of the stack, or manufactured by less conventional injection paths. Directly asking for an IPv4 header with helpers such as ip_hdr() or inner_ip_hdr() can be safe when the packet layout matches the assumptions those helpers rely on. It can become unsafe when the packet entered through PF_PACKET paths and the header offset does not guarantee a safe direct dereference.The fix uses
skb_header_pointer(), a helper designed for exactly this class of problem. If the requested bytes are already safely accessible in the linear data area, it can return a pointer. If not, it can copy the needed header bytes into a temporary buffer. The practical point is simple: before reading frag_off, make sure the header is actually readable in the form the code expects.That is the sort of patch that can look like mere hygiene. In kernel networking, hygiene is often the security boundary.
Syzbot Found the Smoke Before Anyone Reported the Fire
CVE-2026-43036 comes out of the now-familiar pipeline of automated kernel bug discovery. Syzbot, the public continuous fuzzing system built around syzkaller, reported a KMSAN warning involving an uninitialized value ingso_features_check(), reached through netif_skb_features(). KMSAN, the Kernel Memory Sanitizer, is designed to catch uses of uninitialized memory inside the kernel.That origin story should shape how administrators interpret the advisory. This is not, based on the available public record, a vulnerability with a widely advertised exploit or a demonstrated remote compromise path. It is a kernel bug found by fuzzing, classified by NVD as a local availability issue, and repaired upstream through stable kernel commits.
But dismissing fuzz-found bugs as theoretical has become a bad habit. Many serious kernel vulnerabilities start as a sanitizer complaint, a strange crash, or an unreachable-looking edge case. Fuzzers are good precisely because they do not respect the neat mental model engineers carry around for “normal” packet flows.
PF_PACKET is a particularly interesting ingredient. It provides low-level packet interface access and is used by tools that capture, inject, or inspect traffic. That makes it relevant to administrators because it is not only a hacker toy; it is part of the ecosystem around packet sniffers, monitoring agents, test harnesses, intrusion detection, containers, and network appliances.
The CVSS vector says local privileges are required. In practice, the real risk depends on who can create or influence packets through the affected local paths on a given system. A locked-down server with no untrusted local users, no permissive containers, and no packet-injection workloads has a different exposure profile than a multi-tenant host, a lab box, or a Kubernetes node running workloads with more networking reach than the security team realizes.
NVD’s Version Ranges Are a Starting Point, Not a Patch Plan
NVD’s initial analysis lists affected Linux kernel CPE ranges that span several branches: versions from 4.7 up to, but not including, 6.12.81; versions from 6.13 up to, but not including, 6.18.22; versions from 6.19 up to, but not including, 6.19.12; and Linux 7.0 release candidates rc1 through rc6. That spread is wide enough to trigger alarms in vulnerability dashboards and ambiguous enough to frustrate administrators who do not run vanilla upstream kernels.This is where Linux patch management gets messy. Most production systems do not run a kernel downloaded directly from kernel.org with an upstream version number that maps cleanly to NVD’s CPE ranges. Enterprise distributions backport fixes. Cloud kernels carry vendor patches. Appliance vendors freeze branches. Container hosts may be managed by platform release trains rather than by package names that look obvious in a CVE entry.
The safest operational interpretation is not “am I running exactly 6.12.80?” It is “has my kernel vendor shipped the specific fix for TCPv4 GSO
frag_off handling?” That answer may be visible in a distribution security notice, a changelog entry, a package version, a cloud image release note, or a kernel commit reference.NVD also notes that CVSS 4.0 has not yet been assessed. That is not unusual, but it is a reminder that vulnerability databases lag the engineering reality. The patch exists upstream, the affected ranges have been sketched, and vendors will continue folding the fix into their own supported trees. Waiting for every field in every database to look tidy is rarely a good security practice.
The “are we missing a CPE?” prompt on NVD pages is almost comic in this context. For Linux kernel CVEs, CPEs are a rough map, not the terrain. The real terrain is distribution packaging, kernel flavor, cloud image cadence, and whether your scanners understand backports.
Microsoft’s Interest Is Not Accidental
The user-provided source points to Microsoft’s Security Update Guide entry for CVE-2026-43036. That might seem odd to anyone who still thinks of Microsoft security advisories as Windows-only artifacts. In 2026, it is not odd at all.Microsoft’s infrastructure and product portfolio now include substantial Linux responsibility. Azure hosts Linux at enormous scale. AKS depends on Linux node images for many clusters. Azure Linux Container Host has become a first-party Microsoft Linux distribution for cloud-native workloads. WSL made Linux kernels part of everyday developer life on Windows machines. Even Windows shops that never “chose Linux” may be running it indirectly through containers, appliances, CI/CD tools, network monitors, or cloud marketplace images.
That does not mean CVE-2026-43036 is a Windows vulnerability. It is not. It means Microsoft’s update and advisory surface has expanded to cover the systems customers actually run.
This matters for security teams because ownership lines are often blurrier than architecture diagrams admit. The Windows team may own endpoints, the cloud team may own AKS, the platform team may own base images, and developers may own WSL instances that quietly become part of build or test workflows. A kernel CVE listed by MSRC can land in all of those inboxes and still have no single obvious owner.
The right answer is not to panic every time MSRC lists a Linux kernel CVE. The right answer is to treat Microsoft’s presence in the advisory chain as evidence that Linux kernel lifecycle management is now part of the Microsoft estate for many organizations.
This Is an Availability Bug Until Your Environment Makes It More Interesting
NVD’s vector gives CVE-2026-43036 no confidentiality or integrity impact and a high availability impact. That is a specific claim: the expected consequence is a crash, fault, warning, or denial-of-service style condition, not data theft or direct modification. For many teams, that distinction will move it below remote code execution, privilege escalation, and internet-facing service flaws.But availability is not a second-class security property in network infrastructure. A kernel networking crash on a workstation is irritating. The same class of failure on a virtualization host, container node, routing appliance, packet broker, VPN gateway, or build runner can be an outage.
There is also a subtle operational risk in the phrase “local.” Local kernel bugs are often triaged as lower priority because the attacker already needs some access. That logic is sound for single-user systems and less sound for shared machines. Containers, unprivileged users, CI jobs, and monitoring agents can all provide “local” footholds that are less trusted than the kernel code they may prod.
PF_PACKET makes that boundary especially worth examining. Many systems restrict raw packet capabilities by default, but the real world is full of exceptions. Packet capture tools need elevated permissions. Some containers are granted capabilities for debugging or network functions. Security products often run with exactly the sort of low-level access that would make a networking edge case reachable.
That does not turn CVE-2026-43036 into a confirmed privilege escalation. It does mean administrators should resist the lazy mental shortcut that local equals harmless. In shared and cloud-native systems, local is often where the interesting trust boundaries are.
The Patch Is Small Because the Kernel Has Learned This Lesson Before
The repair pattern in CVE-2026-43036 is familiar to kernel developers: do not directly dereference packet header data unless you have established that the bytes are present and safely accessible. Use the helper that understands non-linear socket buffers. Make the code robust whether packet data is already linear or must be copied into a scratch buffer.That sounds obvious after the fact. It is not always obvious in the middle of performance-sensitive networking code where the fastest path is the common path, and the common path has historically worked. Linux networking is full of carefully optimized assumptions because the alternative is leaving performance on the floor for every packet on every machine.
The problem is that the unusual path eventually becomes a security path. Fuzzers construct packets no normal workload would generate. Virtual switches and container networks produce combinations that bare-metal assumptions did not anticipate. Offload features change where segmentation, checksumming, and header mutation happen. Encapsulation stacks headers inside headers until “the IPv4 header” becomes a contextual phrase rather than a stable pointer.
This is why the vulnerability’s description reads like an internal code-review comment rather than a security bulletin. The kernel was reading
iph->frag_off to decide whether to clear mangleid_features. The header access relied on offsets that were not always safe. The fix was to ask for the header through the correct abstraction.Security engineering often advances in exactly this way. Not through a dramatic new mitigation, but through thousands of places where old direct access patterns are replaced by helpers that encode hard-won rules.
Windows Admins Should Read This as a Supply-Chain Signal
For a Windows-heavy administrator, the actionable part of CVE-2026-43036 is not to start hand-auditing Linux kernel networking code. It is to inventory where Linux kernels exist inside a supposedly Windows-centered estate.The obvious places are Azure virtual machines, Linux servers, and Kubernetes nodes. The less obvious places are network appliances, backup products, EDR components, NAS devices, hypervisor adjuncts, developer laptops running WSL, GitHub Actions or Azure DevOps runners, and containers whose host kernel is someone else’s responsibility until it suddenly is not.
Containers deserve special emphasis because they are often misunderstood in vulnerability conversations. A container image does not ship its own Linux kernel in the normal case. It shares the host kernel. That means rebuilding an application image will not fix a host kernel CVE. Updating the node image, host OS, managed cluster version, or underlying platform is the part that matters.
In AKS and similar managed environments, the patch plan is usually less about compiling a kernel and more about tracking node image releases, maintenance windows, upgrade channels, and whether node pools have actually been rotated. A cluster can show that an update is available while still running old nodes because workloads, budgets, or operational caution delayed the rollout.
WSL is another edge case. For most consumer and developer systems, CVE-2026-43036 is unlikely to be the highest-risk item on the board. But enterprises that use WSL in development workflows should treat its kernel as a managed component, not as a magical Linux bubble inside Windows. If developers can run packet tooling, privileged containers, or custom networking experiments, the distinction becomes more than academic.
CVSS Does Not Know Your Network Topology
The CVSS score of 5.5 is a useful common language, but it cannot express whether a given organization has granted packet injection capabilities to a tenant workload on an oversubscribed host. It cannot tell whether a lab environment is reachable from production credentials. It cannot know whether a “local” attacker is an employee, a compromised build job, a container breakout attempt, or a red-team foothold.That is why kernel CVEs need environmental scoring in practice. The base score says this is not a remote unauthenticated worm. Your architecture decides whether it is a routine maintenance item or a meaningful risk to shared infrastructure.
The most conservative reading is to patch affected systems on the next normal kernel maintenance cycle, prioritizing multi-user systems, container hosts, network appliances, and machines where untrusted code can exercise packet interfaces. That is not glamorous advice, but it matches the vulnerability.
Security teams should also be careful with scanner output. If a scanner keys only on upstream version ranges, it may flag patched vendor kernels as vulnerable or miss backported fixes under unfamiliar package names. Conversely, if a cloud image release note says the fix is present but nodes have not been recycled, the dashboard may look better than reality.
The real control is evidence. Confirm the running kernel, confirm the vendor package or image version, confirm the fix landed in that stream, and confirm the machine actually rebooted into the patched kernel. Kernel patching remains one of the places where “installed” and “running” are dangerously different verbs.
The Bigger Story Is Kernel CVE Volume, Not This One Bug
CVE-2026-43036 arrives in an era when Linux kernel CVEs are being issued at a pace that can feel overwhelming. The kernel project’s newer CVE assignment practices have made many resolved bugs more visible as CVEs. That is good for transparency and painful for triage.The practical effect is that administrators see more medium-severity kernel items with terse descriptions and upstream commit links. Some are exploitable in meaningful ways. Some are mostly sanitizer findings that harden obscure paths. Many sit in the uncomfortable middle where the impact is real but heavily dependent on configuration and reachability.
This forces a shift in how teams consume vulnerability feeds. Treating every kernel CVE as a fire drill is unsustainable. Treating them as noise is reckless. The better pattern is to group them by subsystem, affected kernel stream, exposed capability, and vendor patch availability.
CVE-2026-43036 belongs in the networking and packet-buffer bucket. It should raise the priority of systems that process untrusted local packet injection or run shared workloads with enhanced network capabilities. It should not cause the same response as a remotely reachable pre-authentication flaw in a default service.
That kind of nuanced triage is harder than counting CVSS scores. It is also the only way to survive modern kernel vulnerability disclosure without either burning out or missing the bug that matters.
The Small Header Read That Should Change the Patch Conversation
The concrete lesson from CVE-2026-43036 is that a small upstream kernel patch can have different operational meanings depending on where Linux sits in the estate. Before this advisory disappears into the next vulnerability digest, teams should translate it into a few checks that are both modest and real.- Systems running affected upstream Linux kernel ranges should move to a vendor kernel or stable release that includes the TCPv4 GSO
frag_offfix. - Administrators should prioritize shared hosts, container nodes, packet-processing systems, and machines where untrusted users or workloads can access low-level networking capabilities.
- Container image rebuilds alone do not remediate this class of issue because the vulnerable component is the host kernel, not the user-space filesystem inside the container.
- Microsoft-centered environments should check Azure Linux, AKS node images, WSL deployments, and third-party Linux appliances rather than assuming a Linux CVE is outside their patch boundary.
- Vulnerability scanners should be validated against vendor backport information and the actually running kernel version, not just package metadata or upstream CPE ranges.
CVE-2026-43036 is unlikely to be remembered as the Linux kernel scare of 2026, and that is probably appropriate. Its importance is quieter: a fuzzed packet path exposed an unsafe assumption, the kernel fixed it with a safer header-access helper, and the advisory now flows through ecosystems that include Microsoft as well as traditional Linux vendors. The future of patch management will look more like this, not less: cross-platform, cloud-shaped, noisy, and dependent on teams that can tell the difference between a modest bug and a modest bug in exactly the wrong place.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center