CVE-2026-43172 is a newly published Linux kernel vulnerability disclosed on May 6, 2026, affecting Intel’s iwlwifi driver, where malformed firmware reporting for 22000-series wireless hardware could trigger an out-of-bounds array access during shared-memory parsing. The bug is narrow, technical, and not yet scored by NVD, but it is also the kind of flaw that explains why kernel security has become less about dramatic exploits and more about distrust at every hardware boundary. For WindowsForum readers, the Microsoft angle is not that Windows itself owns the bug; it is that Microsoft’s vulnerability ecosystem increasingly mirrors the messy, shared reality of modern client computing. The lesson is simple: firmware-facing driver code is now part of the security perimeter, even when the exploit story is boring.
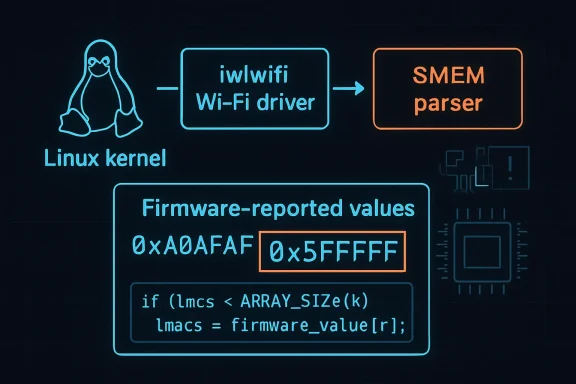
On paper, CVE-2026-43172 is almost aggressively unglamorous. The Linux kernel’s Intel Wi-Fi driver, iwlwifi, parses a firmware-provided shared-memory configuration for the 22000 series, and the vulnerable path assumed the firmware would never claim three LMACs when the hardware does not have three. If that impossible value appeared, the driver could index beyond the bounds of the array holding LMAC configuration.
That is not the sort of vulnerability that lends itself to a splashy demo. There is no public exploit chain in the advisory text, no remote worm scenario, no breathless claim that coffee-shop Wi-Fi is suddenly hostile to every laptop in the room. The record is still awaiting NVD enrichment, meaning there is no official NVD CVSS score or completed vector analysis as of the May 6 publication.
But dismissing it as “just another bounds check” misses the point. The most interesting thing about CVE-2026-43172 is not its likely severity; it is the boundary it exposes. A kernel driver asked firmware for a description of the device’s internal layout, accepted a value that hardware reality says should not exist, and used it in a way that could overrun an array.
That is the modern driver problem in miniature. The operating system is not merely talking to hardware anymore. It is negotiating with firmware blobs, device microcontrollers, tables, notifications, and platform-specific declarations that arrive from below the operating system’s traditional trust line.
A warning says, in effect, “this should not happen.” A check says, “this is input, and input lies.” Security engineering lives in the space between those two sentences.
LMAC, or lower MAC, is one of those hardware/firmware terms most users never see unless their Wi-Fi card has started filling
The vulnerable scenario is almost absurd: firmware reports three LMACs even though the relevant hardware does not have three. Yet many real vulnerabilities begin with precisely that kind of impossible state. Not because the impossible state is expected in normal hardware, but because robust code must survive values that normal hardware would never produce.
That is why this CVE belongs in the security database rather than only in a driver changelog. The security boundary is not “can retail Intel hardware spontaneously invent a third LMAC?” The boundary is whether privileged kernel code safely handles malformed data from the device firmware path.
The answer is that Microsoft’s platform surface is no longer reducible to Windows NT plus Win32. Microsoft ships, supports, documents, and secures a broad estate that includes Linux components, cloud hosts, container infrastructure, Azure images, WSL-adjacent workflows, and products that depend on upstream open-source software. A Linux kernel CVE can therefore become relevant to Microsoft customers without being a Windows kernel bug.
That distinction matters because security feeds have trained administrators to equate “Microsoft advisory” with “Patch Tuesday Windows update.” CVE-2026-43172 is not that. The primary remediation path is the Linux kernel stable update stream, not a cumulative update for Windows 11.
Still, its appearance in Microsoft’s vulnerability guide is useful. It reminds administrators that the advisory layer has become cross-platform, while remediation remains platform-specific. You may learn about the issue from Microsoft, but you fix it through your Linux distribution, kernel vendor, appliance vendor, cloud image maintainer, or embedded platform supplier.
For WindowsForum readers running Hyper-V hosts, WSL development boxes, Azure Linux workloads, home-lab Proxmox nodes, or dual-boot laptops, that distinction is not academic. The security workflow increasingly starts in one vendor’s database and ends in another vendor’s package manager.
That kind of fix is easy to underrate. In security operations, big patches feel serious and small patches feel routine. In kernel development, the opposite is often true: the best security patches are frequently small because the dangerous assumption is concentrated in one unchecked edge case.
The original logic apparently compared against a related firmware memory configuration array, while the unsafe access described in the CVE concerns the runtime shared-memory configuration array. The corrected test uses the array that is actually at risk. That is a classic kernel bug shape: a check exists, but it checks the wrong thing closely enough that the code looks defended at first glance.
This is also why automated vulnerability summaries often flatten the story. “Out-of-bounds access in iwlwifi” is true, but incomplete. The interesting failure is that the parser trusted a topology value from firmware because the hardware topology was assumed to constrain it.
The fix teaches a more durable rule: when parsing a structure, validate against the destination you are about to write or read, not against a nearby structure that happens to be conceptually related. Kernel code does not get partial credit for intent.
That does not mean every Intel Wi-Fi system is equally exposed. The CVE description specifically names the 22000 series SMEM parsing path, and the vulnerable condition depends on firmware reporting an invalid LMAC count. Administrators should resist the temptation to generalize the issue into “Intel Wi-Fi is unsafe” or “all Linux Wi-Fi is vulnerable.”
But broad deployment changes the patching calculus. A low-drama kernel bug in a common driver can still appear across fleets because the driver ships by default, loads automatically, and sits in the kernel. Nobody had to install a risky third-party agent for the code to exist.
The operational problem is also asymmetric. Most end users will never know whether their laptop’s wireless card falls into the affected family or whether their distribution has already absorbed the stable fix. They will simply install kernel updates when offered, reboot, and move on. Enterprises, on the other hand, need to know which kernel trains carry the patch, which images still boot older kernels, and whether any Linux endpoints are pinned to long-term kernels with delayed backports.
This is where kernel CVEs differ from application CVEs. You cannot usually remediate them by replacing one package and restarting one process. You patch the kernel, regenerate boot artifacts if needed, reboot into the corrected kernel, and verify that the old vulnerable kernel is not still the default entry in the bootloader.
The absence of a score should not be read as reassurance. It means the bureaucratic machinery has not finished classifying the issue. It does not mean the flaw is exploitable, non-exploitable, critical, or irrelevant.
At the same time, mature teams should not inflate every unscored kernel CVE into an emergency. The description here points to a malformed firmware-reported configuration value, not to a documented remote attacker path. Without additional evidence, the conservative reading is that this is a robustness and memory-safety fix in a privileged driver path, deserving timely patching but not panic.
The hard part is communicating that middle position. Security culture is bad at moderation. Vulnerability feeds produce either red sirens or background noise, while most real engineering risk lives somewhere in between.
CVE-2026-43172 belongs in that middle zone. It is a kernel memory-safety bug, so it deserves respect. It has no NVD score and no public exploitation claim in the available advisory text, so it does not deserve theatrical incident-response language.
The iwlwifi stack is a particularly visible example because Intel Wi-Fi on Linux depends on firmware files distributed separately from the driver. The driver loads firmware through the kernel’s firmware loader infrastructure, and distributions usually package those firmware blobs through
CVE-2026-43172 is fixed in kernel driver code, not by asking users to manually copy a new firmware blob into
A modern OS has to assume that low-level components can send malformed, stale, unexpected, or maliciously influenced data. Even if the normal commercial hardware never does so, the parser still has to be written as though it might. That is not paranoia; it is the baseline for memory-safe systems in a world full of opaque device firmware.
This is also where the industry’s trust model remains awkward. Firmware is privileged enough to shape the machine but opaque enough that most administrators cannot meaningfully inspect it. The kernel is therefore left to enforce sanity at the boundary, one bounds check at a time.
This is normal for Linux kernel security in 2026. A patch may be written and backported as a correctness fix, a robustness fix, or a driver fix, and only later acquire a CVE identifier. The CVE system is not always the starting gun; sometimes it is the filing cabinet catching up.
That can frustrate enterprise vulnerability management tools. Scanners speak CVE, while kernel maintainers speak commits, subsystem trees, stable series, and distribution kernel builds. Mapping one world to the other is often the real work.
Administrators who only ask “is CVE-2026-43172 present?” may get a less useful answer than those who ask “which kernel build am I booted into, and does my vendor’s changelog include the iwlwifi SMEM parsing fix?” The former depends on scanner coverage. The latter aligns with how the fix actually ships.
The boring operational truth is that Linux security remains heavily distribution-mediated. Ubuntu, Debian, Fedora, Arch, SUSE, Red Hat, Oracle, Canonical, appliance vendors, cloud providers, and OEM image maintainers may all backport the same fix under different kernel version strings. Upstream commit IDs are the common language, but deployed systems rarely run upstream vanilla kernels.
The practical question is not whether CVE-2026-43172 threatens Windows 11 Wi-Fi networking. Based on the available information, it does not describe a Windows WLAN driver vulnerability. The practical question is whether your environment includes Linux systems using Intel wireless hardware and kernels that predate the relevant fix.
For home-lab users, that might mean a NUC-style box, a Framework laptop, a ThinkPad running Fedora, or a test machine that spends months on a pinned kernel because “it works.” For enterprises, it might mean developer workstations, Linux-based field devices, mobile engineering kits, or internal appliances built on standard distributions.
The mistake would be to filter the issue out simply because it appeared through a Microsoft page but names Linux. Cross-platform vulnerability visibility is useful only if teams have cross-platform ownership. Otherwise, the advisory becomes another orphaned alert.
Microsoft’s security guide increasingly functions like a broad radar screen. Radar is not a mechanic. It tells you something exists; it does not install the kernel, reboot the host, or confirm that the fixed image is running.
There is little justification, from the public description alone, for emergency weekend maintenance across all Linux endpoints. The flaw requires a particular driver path and a malformed firmware-reported condition, and there is no public advisory text indicating active exploitation. Security teams should avoid converting uncertainty into drama.
But there is also little justification for ignoring it. It is an out-of-bounds access in kernel driver code. It has upstream stable fixes. It touches a common wireless driver. Those facts are sufficient to put it into the next available maintenance window.
The more interesting remediation question is whether your organization can even answer the inventory question quickly. Which Linux systems have Intel Wi-Fi hardware? Which are using iwlwifi? Which are running kernel builds that include the fix? Which are laptops that sleep for weeks and miss update windows?
If those questions are hard, CVE-2026-43172 has already done you a favor. It has exposed an asset-management gap with a relatively contained vulnerability rather than a high-severity actively exploited one.
CVE-2026-43172 will probably be remembered, if at all, as one of thousands of small Linux kernel CVEs that arrived with sparse prose and a modest patch. But that is precisely why it matters. The future of client and server security will be shaped less by the vulnerabilities that dominate headlines than by whether operating systems keep tightening these quiet trust boundaries before attackers find ways to make impossible states happen on demand.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
 A Tiny Wi-Fi Parser Bug Says Something Big About Kernel Trust
A Tiny Wi-Fi Parser Bug Says Something Big About Kernel Trust
On paper, CVE-2026-43172 is almost aggressively unglamorous. The Linux kernel’s Intel Wi-Fi driver, iwlwifi, parses a firmware-provided shared-memory configuration for the 22000 series, and the vulnerable path assumed the firmware would never claim three LMACs when the hardware does not have three. If that impossible value appeared, the driver could index beyond the bounds of the array holding LMAC configuration.That is not the sort of vulnerability that lends itself to a splashy demo. There is no public exploit chain in the advisory text, no remote worm scenario, no breathless claim that coffee-shop Wi-Fi is suddenly hostile to every laptop in the room. The record is still awaiting NVD enrichment, meaning there is no official NVD CVSS score or completed vector analysis as of the May 6 publication.
But dismissing it as “just another bounds check” misses the point. The most interesting thing about CVE-2026-43172 is not its likely severity; it is the boundary it exposes. A kernel driver asked firmware for a description of the device’s internal layout, accepted a value that hardware reality says should not exist, and used it in a way that could overrun an array.
That is the modern driver problem in miniature. The operating system is not merely talking to hardware anymore. It is negotiating with firmware blobs, device microcontrollers, tables, notifications, and platform-specific declarations that arrive from below the operating system’s traditional trust line.
The Firmware Did Not Need to Be Realistic to Be Dangerous
The upstream fix is blunt: if firmware reports more LMACs than the driver’s internal configuration can represent, reject it. The patch also changes the handling style, replacing warning-oriented behavior with a firmware check that treats the condition as bad input rather than an unexpected-but-debuggable surprise. That distinction matters more than the small diff suggests.A warning says, in effect, “this should not happen.” A check says, “this is input, and input lies.” Security engineering lives in the space between those two sentences.
LMAC, or lower MAC, is one of those hardware/firmware terms most users never see unless their Wi-Fi card has started filling
dmesg with errors. In Intel’s wireless stack, the firmware and driver coordinate over device capabilities, memory regions, FIFOs, and other configuration details. The driver has to interpret those structures correctly before the network interface is useful.The vulnerable scenario is almost absurd: firmware reports three LMACs even though the relevant hardware does not have three. Yet many real vulnerabilities begin with precisely that kind of impossible state. Not because the impossible state is expected in normal hardware, but because robust code must survive values that normal hardware would never produce.
That is why this CVE belongs in the security database rather than only in a driver changelog. The security boundary is not “can retail Intel hardware spontaneously invent a third LMAC?” The boundary is whether privileged kernel code safely handles malformed data from the device firmware path.
Microsoft’s Presence Is a Signal, Not a Claim of Ownership
The user-facing curiosity here is Microsoft’s Security Update Guide listing CVE-2026-43172. That can feel counterintuitive: this is a Linux kernel vulnerability in an Intel Wi-Fi driver, with references pointing to kernel.org stable commits. Why is it in Microsoft’s orbit at all?The answer is that Microsoft’s platform surface is no longer reducible to Windows NT plus Win32. Microsoft ships, supports, documents, and secures a broad estate that includes Linux components, cloud hosts, container infrastructure, Azure images, WSL-adjacent workflows, and products that depend on upstream open-source software. A Linux kernel CVE can therefore become relevant to Microsoft customers without being a Windows kernel bug.
That distinction matters because security feeds have trained administrators to equate “Microsoft advisory” with “Patch Tuesday Windows update.” CVE-2026-43172 is not that. The primary remediation path is the Linux kernel stable update stream, not a cumulative update for Windows 11.
Still, its appearance in Microsoft’s vulnerability guide is useful. It reminds administrators that the advisory layer has become cross-platform, while remediation remains platform-specific. You may learn about the issue from Microsoft, but you fix it through your Linux distribution, kernel vendor, appliance vendor, cloud image maintainer, or embedded platform supplier.
For WindowsForum readers running Hyper-V hosts, WSL development boxes, Azure Linux workloads, home-lab Proxmox nodes, or dual-boot laptops, that distinction is not academic. The security workflow increasingly starts in one vendor’s database and ends in another vendor’s package manager.
The Bug Is Small Because the Patch Is Small
The patch changes only a handful of lines indrivers/net/wireless/intel/iwlwifi/fw/smem.c. It adds the relevant debug/check infrastructure, compares the firmware-reported LMAC count against the size of the driver’s actual fwrt->smem_cfg.lmac array, and returns early if the firmware advertises an impossible number. It also hardens another shared-memory notification size check in the same parsing function.That kind of fix is easy to underrate. In security operations, big patches feel serious and small patches feel routine. In kernel development, the opposite is often true: the best security patches are frequently small because the dangerous assumption is concentrated in one unchecked edge case.
The original logic apparently compared against a related firmware memory configuration array, while the unsafe access described in the CVE concerns the runtime shared-memory configuration array. The corrected test uses the array that is actually at risk. That is a classic kernel bug shape: a check exists, but it checks the wrong thing closely enough that the code looks defended at first glance.
This is also why automated vulnerability summaries often flatten the story. “Out-of-bounds access in iwlwifi” is true, but incomplete. The interesting failure is that the parser trusted a topology value from firmware because the hardware topology was assumed to constrain it.
The fix teaches a more durable rule: when parsing a structure, validate against the destination you are about to write or read, not against a nearby structure that happens to be conceptually related. Kernel code does not get partial credit for intent.
Intel Wi-Fi Is Everywhere, Which Makes Even Narrow Bugs Operationally Annoying
The iwlwifi driver supports a wide range of Intel wireless chips and is the mainline Linux driver for many current Intel Wi-Fi devices. It appears in consumer laptops, business notebooks, mini PCs, developer workstations, embedded systems, and Linux distributions that target modern Intel client hardware. Even when a CVE is narrow, the driver’s reach makes the patch operationally relevant.That does not mean every Intel Wi-Fi system is equally exposed. The CVE description specifically names the 22000 series SMEM parsing path, and the vulnerable condition depends on firmware reporting an invalid LMAC count. Administrators should resist the temptation to generalize the issue into “Intel Wi-Fi is unsafe” or “all Linux Wi-Fi is vulnerable.”
But broad deployment changes the patching calculus. A low-drama kernel bug in a common driver can still appear across fleets because the driver ships by default, loads automatically, and sits in the kernel. Nobody had to install a risky third-party agent for the code to exist.
The operational problem is also asymmetric. Most end users will never know whether their laptop’s wireless card falls into the affected family or whether their distribution has already absorbed the stable fix. They will simply install kernel updates when offered, reboot, and move on. Enterprises, on the other hand, need to know which kernel trains carry the patch, which images still boot older kernels, and whether any Linux endpoints are pinned to long-term kernels with delayed backports.
This is where kernel CVEs differ from application CVEs. You cannot usually remediate them by replacing one package and restarting one process. You patch the kernel, regenerate boot artifacts if needed, reboot into the corrected kernel, and verify that the old vulnerable kernel is not still the default entry in the bootloader.
The Absence of a CVSS Score Is Not the Absence of Risk
NVD has not yet provided a CVSS score for CVE-2026-43172, and that gap should not surprise anyone. Kernel.org CVEs often land first with terse descriptions and upstream commit references, while enrichment, scoring, weakness mapping, and downstream advisories trail behind. Security teams increasingly have to make decisions in that interim period.The absence of a score should not be read as reassurance. It means the bureaucratic machinery has not finished classifying the issue. It does not mean the flaw is exploitable, non-exploitable, critical, or irrelevant.
At the same time, mature teams should not inflate every unscored kernel CVE into an emergency. The description here points to a malformed firmware-reported configuration value, not to a documented remote attacker path. Without additional evidence, the conservative reading is that this is a robustness and memory-safety fix in a privileged driver path, deserving timely patching but not panic.
The hard part is communicating that middle position. Security culture is bad at moderation. Vulnerability feeds produce either red sirens or background noise, while most real engineering risk lives somewhere in between.
CVE-2026-43172 belongs in that middle zone. It is a kernel memory-safety bug, so it deserves respect. It has no NVD score and no public exploitation claim in the available advisory text, so it does not deserve theatrical incident-response language.
Firmware Is Now Part of the Attack Surface Administrators Pretend They Do Not Manage
For years, administrators have treated firmware as something that occasionally needs an update when a laptop vendor publishes a BIOS package or when a server vendor rolls a platform bundle. The kernel world has made that attitude harder to sustain. Wi-Fi firmware, GPU firmware, Bluetooth firmware, storage controller firmware, management engine components, and platform tables all participate in how the OS understands the machine.The iwlwifi stack is a particularly visible example because Intel Wi-Fi on Linux depends on firmware files distributed separately from the driver. The driver loads firmware through the kernel’s firmware loader infrastructure, and distributions usually package those firmware blobs through
linux-firmware or equivalent packages. That creates a two-part maintenance story: kernel code and firmware content.CVE-2026-43172 is fixed in kernel driver code, not by asking users to manually copy a new firmware blob into
/lib/firmware. But the vulnerable condition exists because driver code is interpreting firmware-provided information. That is why the bug is a reminder, not just a patch note.A modern OS has to assume that low-level components can send malformed, stale, unexpected, or maliciously influenced data. Even if the normal commercial hardware never does so, the parser still has to be written as though it might. That is not paranoia; it is the baseline for memory-safe systems in a world full of opaque device firmware.
This is also where the industry’s trust model remains awkward. Firmware is privileged enough to shape the machine but opaque enough that most administrators cannot meaningfully inspect it. The kernel is therefore left to enforce sanity at the boundary, one bounds check at a time.
The Linux Stable Process Is Doing the Quiet Work Users Rarely See
The CVE references multiple stable kernel commits, and one public stable mailing-list posting shows the fix moving through a 6.19 stable review series in late February 2026. That timeline is important: the code fix existed upstream before the CVE record was published on May 6. The vulnerability label arrived after the engineering work.This is normal for Linux kernel security in 2026. A patch may be written and backported as a correctness fix, a robustness fix, or a driver fix, and only later acquire a CVE identifier. The CVE system is not always the starting gun; sometimes it is the filing cabinet catching up.
That can frustrate enterprise vulnerability management tools. Scanners speak CVE, while kernel maintainers speak commits, subsystem trees, stable series, and distribution kernel builds. Mapping one world to the other is often the real work.
Administrators who only ask “is CVE-2026-43172 present?” may get a less useful answer than those who ask “which kernel build am I booted into, and does my vendor’s changelog include the iwlwifi SMEM parsing fix?” The former depends on scanner coverage. The latter aligns with how the fix actually ships.
The boring operational truth is that Linux security remains heavily distribution-mediated. Ubuntu, Debian, Fedora, Arch, SUSE, Red Hat, Oracle, Canonical, appliance vendors, cloud providers, and OEM image maintainers may all backport the same fix under different kernel version strings. Upstream commit IDs are the common language, but deployed systems rarely run upstream vanilla kernels.
The WindowsForum Angle Is the Mixed Estate
A decade ago, a Linux Wi-Fi driver CVE might have seemed marginal to a Windows-focused publication. In 2026, that boundary is thinner. Windows enthusiasts run Linux in VMs, containers, WSL workflows, and dual-boot setups. Sysadmins manage Windows endpoints beside Linux servers and developer laptops. Azure customers consume Linux images as naturally as Windows Server images.The practical question is not whether CVE-2026-43172 threatens Windows 11 Wi-Fi networking. Based on the available information, it does not describe a Windows WLAN driver vulnerability. The practical question is whether your environment includes Linux systems using Intel wireless hardware and kernels that predate the relevant fix.
For home-lab users, that might mean a NUC-style box, a Framework laptop, a ThinkPad running Fedora, or a test machine that spends months on a pinned kernel because “it works.” For enterprises, it might mean developer workstations, Linux-based field devices, mobile engineering kits, or internal appliances built on standard distributions.
The mistake would be to filter the issue out simply because it appeared through a Microsoft page but names Linux. Cross-platform vulnerability visibility is useful only if teams have cross-platform ownership. Otherwise, the advisory becomes another orphaned alert.
Microsoft’s security guide increasingly functions like a broad radar screen. Radar is not a mechanic. It tells you something exists; it does not install the kernel, reboot the host, or confirm that the fixed image is running.
This Is a Patch-Now Bug, Not a Drop-Everything Bug
The right response to CVE-2026-43172 is disciplined routine. Update affected Linux systems through the normal kernel channel, verify that the patched kernel is actually booted, and do not treat the lack of an NVD score as a reason to defer indefinitely. That is enough for most environments.There is little justification, from the public description alone, for emergency weekend maintenance across all Linux endpoints. The flaw requires a particular driver path and a malformed firmware-reported condition, and there is no public advisory text indicating active exploitation. Security teams should avoid converting uncertainty into drama.
But there is also little justification for ignoring it. It is an out-of-bounds access in kernel driver code. It has upstream stable fixes. It touches a common wireless driver. Those facts are sufficient to put it into the next available maintenance window.
The more interesting remediation question is whether your organization can even answer the inventory question quickly. Which Linux systems have Intel Wi-Fi hardware? Which are using iwlwifi? Which are running kernel builds that include the fix? Which are laptops that sleep for weeks and miss update windows?
If those questions are hard, CVE-2026-43172 has already done you a favor. It has exposed an asset-management gap with a relatively contained vulnerability rather than a high-severity actively exploited one.
The Real Test Is Whether Your Kernel Hygiene Survives Small CVEs
Near the close, the concrete lessons are more useful than the drama. CVE-2026-43172 is unlikely to become a household name, but it is a good test case for whether Linux patch management is mature enough to handle the steady drip of driver-layer memory-safety fixes.- Organizations should treat CVE-2026-43172 as a Linux kernel driver issue affecting Intel iwlwifi 22000-series shared-memory parsing, not as a native Windows WLAN vulnerability.
- Administrators should prioritize kernel updates from their distribution or vendor rather than attempting ad hoc driver surgery.
- Systems are not remediated merely because an update package is installed; they must reboot into a kernel build that includes the fix.
- The missing NVD score on May 6, 2026, should be understood as incomplete enrichment, not proof that the issue is harmless.
- Linux laptops, dual-boot machines, developer workstations, and home-lab systems deserve the same vulnerability tracking discipline as servers.
- The most durable lesson is that firmware-provided values must be treated as untrusted input, even when hardware reality says the bad value should never occur.
CVE-2026-43172 will probably be remembered, if at all, as one of thousands of small Linux kernel CVEs that arrived with sparse prose and a modest patch. But that is precisely why it matters. The future of client and server security will be shaped less by the vulnerabilities that dominate headlines than by whether operating systems keep tightening these quiet trust boundaries before attackers find ways to make impossible states happen on demand.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center