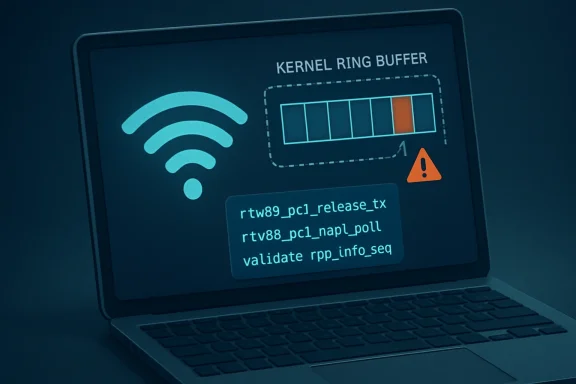
CVE-2026-43213 is a Linux kernel flaw disclosed by kernel.org and listed by Microsoft’s Security Update Guide on May 6, 2026, affecting the Realtek rtw89 PCI Wi-Fi driver when malformed TX release report sequence numbers trigger an out-of-bounds access and kernel crash. The bug is not the sort of remote-code-execution spectacular that makes patch teams sprint across the building. It is something more familiar to Linux laptop owners and fleet admins: a small driver assumption, sitting close to hardware, with enough privilege to take the machine down. That makes it worth treating less like a curiosity and more like a reminder that “just a Wi-Fi driver” is still kernel attack surface.
The fix behind CVE-2026-43213 is almost comically modest: validate
The Realtek
That matters because the failure happens in kernel context, not in a disposable user-space helper. The crash trace attached to the CVE shows the path through
This is unlikely to be the most dangerous Linux vulnerability of 2026. But it is exactly the kind of bug that keeps recurring because modern operating systems are full of tiny, high-speed trust relationships between silicon, firmware, drivers, and scheduler paths.
Kernel drivers often live in this awkward space. They need to be fast enough to handle interrupts and data paths without turning every packet into a legal proceeding. They also need to be paranoid enough to survive bad firmware, flaky hardware, power-management weirdness, and potentially hostile inputs. CVE-2026-43213 lands on the wrong side of that trade-off.
A TX release report is not glamorous. It is part of the bookkeeping that lets the driver know what transmitted work has completed and which buffers or descriptors can be released. If the reported sequence number points where the driver expects, the machine continues. If it points outside the structure the driver prepared, the kernel is suddenly reading where it should not.
The resolution is therefore simple but important: validate the sequence number before using it. That is the entire security story in miniature. The vulnerable behavior assumed the device’s report fit the driver’s ring state; the fixed behavior checks that assumption before touching the array.
For WindowsForum readers who spend more time in Device Manager than
That absence of a score is not a reason to ignore it. It is a reason not to overstate it. There is no public evidence in the supplied record that CVE-2026-43213 enables privilege escalation, code execution, credential theft, or wireless worm magic. The described result is a kernel oops caused by an out-of-bounds access ending in a NULL dereference.
For many environments, that still qualifies as a security problem. A local crash is downtime. A reproducible crash path in a kernel driver can become a denial-of-service primitive. In edge devices, kiosks, developer laptops, lab rigs, and workstations that depend on Wi-Fi, a “mere” kernel crash can be operationally meaningful.
The harder question is triggerability. The CVE text says hardware rarely reports the abnormal sequence number, which implies at least some observations came from real systems rather than a purely theoretical audit. But it does not establish whether an attacker can force the condition over the air, whether it requires specific Realtek firmware behavior, whether it depends on PCIe device state, or whether it is mainly a robustness patch assigned a CVE under the kernel project’s modern disclosure model.
That distinction is where administrators should be careful. Treat the fix as worth taking. Do not treat the CVE as proof that every nearby access point can panic your laptop.
Realtek wireless hardware has long occupied a particular place in the Linux ecosystem. It is common, affordable, and frequently present in machines that were not bought with Linux compatibility as the first criterion. The user experience has improved dramatically compared with the old days of hunting for vendor tarballs, but the hardware remains a regular source of forum threads about suspend failures, missing firmware, DKMS confusion, and kernel-version mismatches.
That history shapes the risk. A kernel bug in an enterprise-only storage HBA is serious for the people who own that hardware, but invisible to everyone else. A bug in a laptop Wi-Fi driver can touch students, developers, dual-booters, Linux gaming handheld tinkerers, and remote workers who only discover the chipset name after something breaks.
The affected code path is also a reminder that Linux hardware support is not a single thing. The kernel may support the chipset, the distribution may ship the module, the firmware package may be present, power management may be tuned, and the system may still run into a driver edge case triggered by rare device behavior. “Supported” means the stack exists. It does not mean every corner case has been domesticated.
But Microsoft now lives in a world where Linux is part of its estate. Azure runs Linux at enormous scale. Microsoft ships and services Linux-adjacent components. Windows Subsystem for Linux has made Linux userlands a normal part of Windows developer machines, even if WSL itself does not turn a Windows Wi-Fi adapter into a Linux PCI driver path in the usual desktop configuration.
The practical reading is narrower: Microsoft tracks CVEs that matter to its products, services, customers, or vulnerability ecosystem. An MSRC page does not automatically mean your Windows 11 laptop is directly vulnerable through Windows. It means the vulnerability is in Microsoft’s security-tracking orbit.
That is healthy, if slightly confusing. The old mental model — Microsoft patches Windows, Linux vendors patch Linux, hardware vendors patch drivers — is increasingly obsolete. Cloud platforms, hybrid endpoints, developer environments, and appliance-like Linux systems have blurred the boundary. A Linux kernel CVE appearing in a Microsoft venue is not a category error; it is the modern supply chain showing through the wallpaper.
For a human admin, the missing score is an inconvenience. For automated vulnerability management, it can be a blind spot or a source of noisy uncertainty. A scanner that sees a CVE without a score may treat it too gently, too harshly, or inconsistently depending on local policy. A risk dashboard may know a CVE exists but not know how to rank it.
This is particularly awkward for Linux kernel CVEs because the affectedness story is rarely a single neat version range. The kernel has mainline, stable trees, long-term support branches, distribution backports, vendor kernels, cloud kernels, OEM kernels, and appliance kernels. The same fix may appear as one commit upstream, several backports in stable branches, and a differently numbered package in a distribution.
CVE-2026-43213 illustrates that mess. The public references point to multiple stable commits, while Ubuntu’s tracker shows evaluation still underway across many kernel flavors. That is not negligence; it is the kernel ecosystem functioning as designed. But it does mean security teams cannot simply wait for one global truth table to descend from NVD.
CVE-2026-43213 is a good example of the new normal. It is real. It has a concrete crash mode. It has a fix. It may affect hardware found in ordinary machines. It is also not, based on available information, an internet-wide emergency.
That middle category is where security programs often struggle. Patch teams are good at two modes: drop everything, or wait for the normal cycle. Driver CVEs like this demand a third mode: understand exposure, watch vendor status, and fold the fix into the next kernel update unless your environment has a specific reason to accelerate.
For consumers and enthusiasts, the advice is even simpler. If your distribution ships a kernel update that includes the fix, install it. If you are using an out-of-tree
The boringness is not a defect. Boring CVEs are the background radiation of a mature ecosystem. The danger is that we learn to ignore them all, including the ones that quietly describe how a privileged subsystem can be knocked over by data it should have distrusted.
On a Linux system, the relevant evidence is likely to live in
The CVE text includes a tainted kernel marker, which is common in real-world bug reports and worth reading carefully. Kernel taint flags can indicate proprietary modules, unsigned modules, out-of-tree code, warnings, or other state that upstream developers use to judge diagnostic cleanliness. They do not automatically invalidate the bug, but they can complicate support.
Fleet administrators should resist the temptation to diagnose by chipset name alone. Many Realtek devices use different drivers, and
Mainline and stable commit references are useful for maintainers and advanced users, but production systems live on packages. A vendor may backport the fix into a kernel whose version number still looks “old” compared with upstream. Conversely, a self-built kernel may carry a high version number but lack a specific stable patch if it was built before the fix landed.
This is why simple version comparisons mislead. The question is not only “Am I running Linux 6.x?” It is “Does my exact kernel build include the sequence-number validation in the
There is also a practical wrinkle for laptop users who installed
But mixed estates are everywhere now. A Windows laptop may dual-boot Linux. A developer workstation may run Linux on bare metal for CUDA, containers, or kernel work. A small office may have Linux-based routers, NAS boxes, thin clients, or embedded devices with Realtek wireless modules. A cloud team may consume Linux images without thinking of itself as a “Linux shop.”
That is why the right response is inventory, not panic. Find where Linux kernels and Realtek
WSL deserves a special note because it often causes category confusion. WSL lets Linux user-space workloads run on Windows, but it does not normally expose the laptop’s PCIe Wi-Fi device to the Linux guest as though it were a bare-metal
The deeper Microsoft connection is cloud and supply chain visibility. Security teams increasingly track vulnerabilities across operating systems from a single console. Seeing a Linux kernel CVE in a Microsoft-managed security feed is not weird anymore. It is evidence that the old platform silos no longer match how infrastructure is built.
For a developer laptop, the practical consequence may be an annoying crash and a lost work session. For a kiosk, point-of-sale device, or field system using Wi-Fi as its primary network, the same crash may be an outage. For a server with no Realtek Wi-Fi hardware and no loaded
That is the uncomfortable truth about driver vulnerabilities. They make nonsense of purely abstract risk scoring. Hardware presence, module loading, firmware behavior, and workload context matter as much as the CVE description.
Security vendors will eventually package this into clean colors and numbers. Administrators should not wait for the colors to think. The initial triage is simple: identify Linux systems, identify Realtek
The broader lesson is that hardware-originated data deserves the same suspicion as network-originated data. Modern systems tend to draw a mental line between “external input” and “internal device state,” but that line is porous. Devices have firmware. Firmware has bugs. Buses can misbehave. Power transitions can produce strange states. Attackers, in some contexts, can influence conditions that drivers once treated as merely mechanical.
This is especially true in networking drivers, where hardware and software constantly exchange descriptors, sequence numbers, ring indices, completion reports, and status bits. Every one of those fields is small. Every one is boring. Every one can become a crash site if the driver forgets that unlikely is not the same as impossible.
The best kernel fixes often look anticlimactic because they encode humility. Check the index. Validate the length. Reject the impossible state. Return early. Those are not glamorous engineering moves, but they are how mature systems survive contact with reality.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
 A Small Bounds Check Carries a Large Lesson
A Small Bounds Check Carries a Large Lesson
The fix behind CVE-2026-43213 is almost comically modest: validate rpp_info.seq before using it. That is the kind of sentence that makes seasoned kernel readers nod and everyone else wonder why such a thing was not already guaranteed. But kernel security is often the art of discovering which guarantees were only habits.The Realtek
rtw89 driver handles modern Realtek Wi-Fi chipsets, including PCIe 802.11ax hardware commonly found in laptops and small-form-factor systems. In this case, the vulnerable path sits in the PCI side of the driver, where the kernel processes a TX release report from the device. If the hardware reports an abnormal sequence number, the driver can index beyond the expected wd_ring->pages array and run into a NULL pointer dereference.That matters because the failure happens in kernel context, not in a disposable user-space helper. The crash trace attached to the CVE shows the path through
rtw89_pci_release_tx, rtw89_pci_napi_poll, and the networking softirq machinery. In plain English: the system is handling Wi-Fi-related interrupt/network work, trusts a sequence value too far, and falls over.This is unlikely to be the most dangerous Linux vulnerability of 2026. But it is exactly the kind of bug that keeps recurring because modern operating systems are full of tiny, high-speed trust relationships between silicon, firmware, drivers, and scheduler paths.
The Kernel Trusted the Device a Little Too Much
The wording in the CVE is unusually revealing: “Hardware rarely reports abnormal sequence number.” That phrase does a lot of work. It says the driver was built around normal behavior, and normal behavior was mostly good enough — until it was not.Kernel drivers often live in this awkward space. They need to be fast enough to handle interrupts and data paths without turning every packet into a legal proceeding. They also need to be paranoid enough to survive bad firmware, flaky hardware, power-management weirdness, and potentially hostile inputs. CVE-2026-43213 lands on the wrong side of that trade-off.
A TX release report is not glamorous. It is part of the bookkeeping that lets the driver know what transmitted work has completed and which buffers or descriptors can be released. If the reported sequence number points where the driver expects, the machine continues. If it points outside the structure the driver prepared, the kernel is suddenly reading where it should not.
The resolution is therefore simple but important: validate the sequence number before using it. That is the entire security story in miniature. The vulnerable behavior assumed the device’s report fit the driver’s ring state; the fixed behavior checks that assumption before touching the array.
For WindowsForum readers who spend more time in Device Manager than
dmesg, the analogy is straightforward. A network adapter driver is not merely a conduit for packets. It is privileged code parsing a stream of device-provided status messages. When that parser gets trust wrong, the blast radius is the operating system itself.This Is a Denial-of-Service Bug Until Proven Otherwise
The public record, as of May 7, 2026, points to a crash-class flaw rather than an exploit-chain centerpiece. The observable failure is a NULL pointer dereference in kernel mode. NVD has marked the record as awaiting enrichment, with no CVSS score from NIST yet, and Ubuntu currently classifies the issue as Medium while still evaluating a long list of kernel packages.That absence of a score is not a reason to ignore it. It is a reason not to overstate it. There is no public evidence in the supplied record that CVE-2026-43213 enables privilege escalation, code execution, credential theft, or wireless worm magic. The described result is a kernel oops caused by an out-of-bounds access ending in a NULL dereference.
For many environments, that still qualifies as a security problem. A local crash is downtime. A reproducible crash path in a kernel driver can become a denial-of-service primitive. In edge devices, kiosks, developer laptops, lab rigs, and workstations that depend on Wi-Fi, a “mere” kernel crash can be operationally meaningful.
The harder question is triggerability. The CVE text says hardware rarely reports the abnormal sequence number, which implies at least some observations came from real systems rather than a purely theoretical audit. But it does not establish whether an attacker can force the condition over the air, whether it requires specific Realtek firmware behavior, whether it depends on PCIe device state, or whether it is mainly a robustness patch assigned a CVE under the kernel project’s modern disclosure model.
That distinction is where administrators should be careful. Treat the fix as worth taking. Do not treat the CVE as proof that every nearby access point can panic your laptop.
Realtek Wi-Fi Has Become Normal Linux Infrastructure
Thertw89 driver is no longer an obscure out-of-tree adventure for people willing to clone a repository at midnight. It entered the mainstream kernel line for Realtek’s newer Wi-Fi generations and supports a family of PCIe adapters that show up in ordinary laptops. That is precisely why a small driver bug gets a CVE with wide distribution interest.Realtek wireless hardware has long occupied a particular place in the Linux ecosystem. It is common, affordable, and frequently present in machines that were not bought with Linux compatibility as the first criterion. The user experience has improved dramatically compared with the old days of hunting for vendor tarballs, but the hardware remains a regular source of forum threads about suspend failures, missing firmware, DKMS confusion, and kernel-version mismatches.
That history shapes the risk. A kernel bug in an enterprise-only storage HBA is serious for the people who own that hardware, but invisible to everyone else. A bug in a laptop Wi-Fi driver can touch students, developers, dual-booters, Linux gaming handheld tinkerers, and remote workers who only discover the chipset name after something breaks.
The affected code path is also a reminder that Linux hardware support is not a single thing. The kernel may support the chipset, the distribution may ship the module, the firmware package may be present, power management may be tuned, and the system may still run into a driver edge case triggered by rare device behavior. “Supported” means the stack exists. It does not mean every corner case has been domesticated.
Microsoft’s Listing Is a Signal, Not a Windows Panic
The presence of CVE-2026-43213 in Microsoft’s Security Update Guide will inevitably raise eyebrows. The vulnerability is in the Linux kernel, not in the Windows networking stack. For the ordinary Windows desktop user, this does not mean Windows Update is about to patch Realtek Wi-Fi through the Linux kernel.But Microsoft now lives in a world where Linux is part of its estate. Azure runs Linux at enormous scale. Microsoft ships and services Linux-adjacent components. Windows Subsystem for Linux has made Linux userlands a normal part of Windows developer machines, even if WSL itself does not turn a Windows Wi-Fi adapter into a Linux PCI driver path in the usual desktop configuration.
The practical reading is narrower: Microsoft tracks CVEs that matter to its products, services, customers, or vulnerability ecosystem. An MSRC page does not automatically mean your Windows 11 laptop is directly vulnerable through Windows. It means the vulnerability is in Microsoft’s security-tracking orbit.
That is healthy, if slightly confusing. The old mental model — Microsoft patches Windows, Linux vendors patch Linux, hardware vendors patch drivers — is increasingly obsolete. Cloud platforms, hybrid endpoints, developer environments, and appliance-like Linux systems have blurred the boundary. A Linux kernel CVE appearing in a Microsoft venue is not a category error; it is the modern supply chain showing through the wallpaper.
The NVD Gap Is Now Part of the Story
The CVE record is currently “awaiting enrichment” at NVD. That phrase has become familiar to anyone tracking vulnerabilities at scale, and not in a comforting way. It means the basic identifier and description exist, but the downstream metadata many tools rely on — CVSS scoring, affected product mappings, weakness categorization, and richer analysis — may lag behind.For a human admin, the missing score is an inconvenience. For automated vulnerability management, it can be a blind spot or a source of noisy uncertainty. A scanner that sees a CVE without a score may treat it too gently, too harshly, or inconsistently depending on local policy. A risk dashboard may know a CVE exists but not know how to rank it.
This is particularly awkward for Linux kernel CVEs because the affectedness story is rarely a single neat version range. The kernel has mainline, stable trees, long-term support branches, distribution backports, vendor kernels, cloud kernels, OEM kernels, and appliance kernels. The same fix may appear as one commit upstream, several backports in stable branches, and a differently numbered package in a distribution.
CVE-2026-43213 illustrates that mess. The public references point to multiple stable commits, while Ubuntu’s tracker shows evaluation still underway across many kernel flavors. That is not negligence; it is the kernel ecosystem functioning as designed. But it does mean security teams cannot simply wait for one global truth table to descend from NVD.
Kernel CVEs Are Becoming More Numerous and More Boring
The Linux kernel project’s role as a CVE Numbering Authority has changed the texture of kernel vulnerability tracking. More fixes that might once have been read only as stable-tree robustness patches now receive CVE identifiers. That produces a healthier disclosure trail, but it also floods dashboards with issues that vary wildly in exploitability and operational urgency.CVE-2026-43213 is a good example of the new normal. It is real. It has a concrete crash mode. It has a fix. It may affect hardware found in ordinary machines. It is also not, based on available information, an internet-wide emergency.
That middle category is where security programs often struggle. Patch teams are good at two modes: drop everything, or wait for the normal cycle. Driver CVEs like this demand a third mode: understand exposure, watch vendor status, and fold the fix into the next kernel update unless your environment has a specific reason to accelerate.
For consumers and enthusiasts, the advice is even simpler. If your distribution ships a kernel update that includes the fix, install it. If you are using an out-of-tree
rtw89 build because your hardware once needed it, reconsider whether the in-kernel driver now supports your adapter. Carrying a separate driver tree can leave you outside the normal security and regression-testing path.The boringness is not a defect. Boring CVEs are the background radiation of a mature ecosystem. The danger is that we learn to ignore them all, including the ones that quietly describe how a privileged subsystem can be knocked over by data it should have distrusted.
The Crash Trace Tells Admins Where to Look
The stack trace in the CVE gives affected users a useful fingerprint. The crash involvesrtw89_pci_release_tx, rtw89_pci_napi_poll, net_rx_action, and softirq handling, with the thread name showing irq/129-rtw89_p. That does not mean every kernel crash with rtw89 in the log is CVE-2026-43213, but it narrows the hunt.On a Linux system, the relevant evidence is likely to live in
journalctl, dmesg, persistent kernel logs, or crash dumps if configured. Look for an oops or NULL pointer dereference around the Realtek rtw89_pci module. If the system reboots immediately, persistent journaling or a serial/netconsole-style setup may be necessary to capture the trace.The CVE text includes a tainted kernel marker, which is common in real-world bug reports and worth reading carefully. Kernel taint flags can indicate proprietary modules, unsigned modules, out-of-tree code, warnings, or other state that upstream developers use to judge diagnostic cleanliness. They do not automatically invalidate the bug, but they can complicate support.
Fleet administrators should resist the temptation to diagnose by chipset name alone. Many Realtek devices use different drivers, and
rtw89 itself spans multiple chip families and companion modules. Confirm the loaded module, the PCI ID, the kernel version, and the distribution package before declaring a system exposed or fixed.The Patch Path Runs Through Distributions, Not Heroics
The safest fix for most users is not to cherry-pick a kernel commit by hand. It is to take the kernel update from the distribution or vendor that owns your running kernel. That is especially true on Ubuntu, Fedora, Debian, Red Hat-derived systems, Arch-based systems, and appliance distributions that carry their own kernel configuration and backport policy.Mainline and stable commit references are useful for maintainers and advanced users, but production systems live on packages. A vendor may backport the fix into a kernel whose version number still looks “old” compared with upstream. Conversely, a self-built kernel may carry a high version number but lack a specific stable patch if it was built before the fix landed.
This is why simple version comparisons mislead. The question is not only “Am I running Linux 6.x?” It is “Does my exact kernel build include the sequence-number validation in the
rtw89 PCI TX release path?” Distribution changelogs, security notices, and package metadata answer that better than folklore.There is also a practical wrinkle for laptop users who installed
rtw89 from a third-party repository years ago. Those installations often made sense when a chipset was newer than the distribution kernel. In 2026, they may be technical debt. If the external module is still in use, it may not receive fixes on the same schedule as the distro kernel, and it may break whenever internal kernel APIs move.The Windows Angle Is Mostly About Mixed Estates
For WindowsForum’s core audience, the natural question is whether this matters on a Windows machine. If you are running Windows with the normal Realtek Windows driver, CVE-2026-43213 is not describing that driver. It is describing Linux kernel code. The same physical Wi-Fi chip can be driven by entirely different software stacks depending on the operating system.But mixed estates are everywhere now. A Windows laptop may dual-boot Linux. A developer workstation may run Linux on bare metal for CUDA, containers, or kernel work. A small office may have Linux-based routers, NAS boxes, thin clients, or embedded devices with Realtek wireless modules. A cloud team may consume Linux images without thinking of itself as a “Linux shop.”
That is why the right response is inventory, not panic. Find where Linux kernels and Realtek
rtw89 hardware overlap. If there is no overlap, this CVE is probably just background noise. If there is overlap, wait for or apply the relevant kernel update according to your normal change process.WSL deserves a special note because it often causes category confusion. WSL lets Linux user-space workloads run on Windows, but it does not normally expose the laptop’s PCIe Wi-Fi device to the Linux guest as though it were a bare-metal
rtw89_pci environment. Treat this as a bare-metal Linux or Linux-appliance concern unless your configuration is doing something unusually low-level with hardware passthrough.The deeper Microsoft connection is cloud and supply chain visibility. Security teams increasingly track vulnerabilities across operating systems from a single console. Seeing a Linux kernel CVE in a Microsoft-managed security feed is not weird anymore. It is evidence that the old platform silos no longer match how infrastructure is built.
Severity Is a Local Decision Until the Scoring Catches Up
Once NVD enrichment lands, CVE-2026-43213 will likely become easier to sort in dashboards. But the official score, when it appears, will still be a generic approximation. Your real severity depends on whether affected hardware exists in your environment, whether the system is exposed to untrusted wireless conditions, whether crashes create safety or availability issues, and how quickly kernel updates can be deployed.For a developer laptop, the practical consequence may be an annoying crash and a lost work session. For a kiosk, point-of-sale device, or field system using Wi-Fi as its primary network, the same crash may be an outage. For a server with no Realtek Wi-Fi hardware and no loaded
rtw89_pci module, the CVE may be irrelevant even if the source tree technically contains the vulnerable code.That is the uncomfortable truth about driver vulnerabilities. They make nonsense of purely abstract risk scoring. Hardware presence, module loading, firmware behavior, and workload context matter as much as the CVE description.
Security vendors will eventually package this into clean colors and numbers. Administrators should not wait for the colors to think. The initial triage is simple: identify Linux systems, identify Realtek
rtw89 PCI Wi-Fi, check kernel vendor status, and patch through the supported channel.The Real Fix Is Treating Device Reports as Hostile Inputs
CVE-2026-43213 is not a grand indictment of Realtek, Linux, or wireless drivers. It is a familiar software mistake in an unforgiving place. The device reported a value the driver did not sufficiently constrain, and privileged code used that value to index memory.The broader lesson is that hardware-originated data deserves the same suspicion as network-originated data. Modern systems tend to draw a mental line between “external input” and “internal device state,” but that line is porous. Devices have firmware. Firmware has bugs. Buses can misbehave. Power transitions can produce strange states. Attackers, in some contexts, can influence conditions that drivers once treated as merely mechanical.
This is especially true in networking drivers, where hardware and software constantly exchange descriptors, sequence numbers, ring indices, completion reports, and status bits. Every one of those fields is small. Every one is boring. Every one can become a crash site if the driver forgets that unlikely is not the same as impossible.
The best kernel fixes often look anticlimactic because they encode humility. Check the index. Validate the length. Reject the impossible state. Return early. Those are not glamorous engineering moves, but they are how mature systems survive contact with reality.
The Patch Note That Should Shape This Week’s Triage
CVE-2026-43213 should land in patch queues with a clear but measured priority: important for exposed Linux systems with Realtekrtw89 PCI Wi-Fi, less urgent for everyone else, and not currently supported by public evidence of a broader exploit class. The concrete action is to let distribution kernels absorb the upstream fix and avoid bespoke driver arrangements unless there is a strong reason to maintain them.- Systems using Windows with the normal Windows Realtek driver are not the target described by this Linux kernel CVE.
- Linux systems with Realtek
rtw89PCI Wi-Fi hardware should be tracked for vendor kernel updates that include the sequence-number validation fix. - The current public description points to a kernel crash through NULL pointer dereference, not confirmed remote code execution or privilege escalation.
- NVD had not yet enriched the record with a CVSS score as of May 7, 2026, so organizations should not rely on scoring alone for triage.
- Out-of-tree or manually built
rtw89drivers deserve special scrutiny because they may sit outside normal distribution patching. - Crash logs mentioning
rtw89_pci_release_txandrtw89_pci_napi_pollare strong clues for investigation, though not proof by themselves.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center