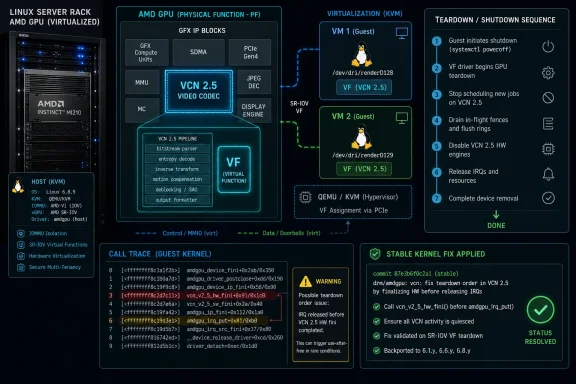
CVE-2026-43298, published to the NVD on May 8, 2026, documents a Linux kernel amdgpu driver flaw in which AMDGPU’s VCN 2.5 virtual-function teardown path tried to release a poison interrupt that the VF never enabled. That sounds almost comically narrow, but it is exactly the kind of kernel plumbing bug that matters in virtualized GPU environments. The visible symptom is not a glamorous remote exploit; it is a warning and call trace during driver deinitialization, the sort of thing that turns maintenance windows into forensic exercises. The lesson is that modern GPU virtualization is now deep enough in the infrastructure stack that even a one-line conditional can become a security record.
The Linux kernel’s CVE stream has made peace with an uncomfortable truth: not every vulnerability looks like an exploit demo. CVE-2026-43298 is a case study in that shift. The defect sits in the Direct Rendering Manager’s AMDGPU driver, specifically around VCN, AMD’s video codec engine, and the handling of a virtual function during device shutdown.
The bug description is blunt. On VCNv2.5, a VF does not enable the VCN poison interrupt, yet the cleanup path attempted to release it anyway. The result was a warning in
That distinction matters. This is not a browser sandbox escape, a wormable SMB defect, or a GPU memory disclosure with immediate cloud-hosting implications. It is a kernel driver state-management flaw that appears when the driver unwinds a virtualized AMD GPU function and discovers that the bookkeeping does not match the hardware reality.
But kernel security is not only about remote code execution. A kernel warning in a teardown path can still matter because teardown paths are where systems are most brittle: module unloads, device resets, VM shutdowns, host maintenance, passthrough handoffs, and error recovery. The closer a bug sits to those paths, the more it intersects with the daily work of administrators who need machines to survive routine operations.
The CVE’s “poison IRQ” language sounds dramatic, but in this context it is driver machinery. RAS, or reliability, availability, and serviceability, features often deal with poison events: hardware-detected faults, corrupted data paths, or error-signaling mechanisms that need software attention. An interrupt associated with that machinery is useful only if the particular hardware path enabled it in the first place.
The failure here is the mismatch. The VF path did not enable that VCN poison interrupt on VCNv2.5, but the shutdown code acted as if it had. When the driver later tried to put, or release, an interrupt reference that was never acquired, the kernel complained.
That makes the patch conceptually simple: skip releasing the VCN poison IRQ on VF. The fix is less a redesign than a correction of the driver’s mental model. The VF is not a smaller physical function; it is a different operating mode with different initialization and cleanup obligations.
This is also why the CVE is more useful to administrators than its sparse scoring data suggests. There is no NVD CVSS score attached yet, and no NVD enrichment beyond the received kernel record. Still, the condition described is concrete enough to scope: AMDGPU, VCNv2.5, VF behavior, deinitialization, and a call trace in the IRQ release path.
That era is ending. GPUs are no longer peripheral accelerators in the old sense; they are compute, display, media, AI, and encoding engines rolled into one high-state device. The driver has to understand power management, firmware queues, memory eviction, interrupt routing, reset domains, video codecs, RAS reporting, and virtualization boundaries.
CVE-2026-43298 lands in that world. VCN is the video codec block, not the shader core that most users associate with graphics performance. Yet the bug appears in a path that can affect virtual-function deinitialization. That tells us the attack surface and failure surface of a modern GPU driver are distributed across the entire device, not only the obvious rendering pipeline.
For WindowsForum readers, the Windows angle is not that this is a Windows kernel vulnerability. It is not. The Windows angle is that many Windows workloads now live as guests on Linux hosts, and many enthusiast Windows environments are built around Linux hypervisors. A Linux amdgpu flaw can therefore be a Windows reliability problem when the Windows system is the guest that depends on a GPU being cleanly handed off, reset, or detached.
That is the practical reality of mixed-platform computing. The host kernel owns the device. The guest operating system experiences the consequences.
It would be easy to dismiss this as a noisy warning. After all, the record does not describe privilege escalation, arbitrary write, or information disclosure. The NVD entry has no severity score yet. The fix appears to be a small guard around an IRQ release call.
That dismissal would be too casual. Kernel warnings during teardown are operationally significant because teardown is often chained to other actions. A VM stops, a device resets, a module unloads, a host migrates workload, a service restarts, and suddenly a warning that seemed harmless becomes the first clue in a longer stability problem.
The trace also shows the bug appearing under KVM, which is exactly where virtual GPU edge cases tend to surface. Virtualization forces drivers through code paths that bare-metal desktop users may never touch. A Radeon card sitting in a gaming PC may never encounter this condition, while the same hardware family in a lab, VDI node, passthrough workstation, or cloud-adjacent setup might.
This is the trap in reading CVE records too literally. The CVE describes the resolved bug, not the entire operational context. The absence of a dramatic exploit narrative does not mean the issue is irrelevant; it means the risk has to be evaluated through deployment architecture.
For administrators, the right reading is more nuanced. Microsoft has strong reasons to track Linux kernel vulnerabilities, especially where Azure hosts, Linux guests, GPU-backed workloads, confidential computing boundaries, or container platforms may intersect. A Linux kernel bug in a GPU driver can be relevant to Microsoft’s world even when it is not a bug in Windows.
That is increasingly normal. The old patch taxonomy — Windows issues on Patch Tuesday, Linux issues somewhere else, firmware issues from the OEM — does not map cleanly onto modern fleets. A single workload may depend on Windows Server, Ubuntu guests, AMD firmware, a hypervisor, a container runtime, and Azure or on-prem orchestration.
CVE-2026-43298 therefore sits in a category that security teams should recognize: cross-ecosystem infrastructure hygiene. It is not a reason for Windows desktop users to panic. It is a reason for teams running AMD GPU virtualization under Linux to check kernel advisories, stable backports, vendor kernels, and host update schedules.
The discipline is to separate catalog visibility from product impact. MSRC visibility tells you Microsoft is aware of the CVE in its security universe. It does not, by itself, define exploitability, affected Windows versions, or patch urgency for a Windows endpoint.
A future score may rate the issue low if the impact is limited to warnings during deinitialization. It may remain unscored for some time. It may be classified under a broad weakness category that tells administrators very little about whether their systems are actually exposed. None of those outcomes changes the practical scoping questions.
The meaningful questions are concrete. Are you running Linux hosts with AMDGPU? Are you using virtual functions, SR-IOV-like GPU partitioning, or passthrough workflows? Are affected kernels or vendor driver packages in use? Have you seen call traces around
This is where CVSS can mislead by omission. A low-scored bug in an irrelevant component is noise. An unscored bug in a driver path your infrastructure exercises every night is not noise.
That does not mean every kernel CVE deserves emergency treatment. It means the score is only one input, and for infrastructure drivers it is often a late-arriving one. The earlier signal comes from matching the described code path to the systems you actually operate.
The fix itself is narrow. It does not claim to redesign AMDGPU virtualization, rework RAS handling, or change VCN initialization. It simply avoids releasing an interrupt that the VF never enabled.
That kind of patch is both reassuring and frustrating. Reassuring, because small conditional fixes are easier to audit and less likely to introduce sweeping regressions. Frustrating, because the operational symptom may be buried inside larger kernel update cycles, especially for distributions that backport fixes without changing the visible major kernel version.
Ubuntu users, for example, may see a
The included trace mentions Ubuntu 22.04.1 with a 6.8 generic kernel, KVM, and AMDGPU modules marked as externally built. That should not be read as a definitive affected-version matrix. It is evidence of the environment in which the warning was observed, not a complete map of all affected distributions or hardware configurations.
The key pattern is device lifecycle fragility. Passing a GPU to a VM is not just about getting the guest driver to install. It is about binding, unbinding, resetting, unloading, reloading, and surviving the transition between host ownership and guest ownership. Every one of those transitions is a place where driver state must line up with hardware state.
CVE-2026-43298 is not a universal explanation for AMDGPU unload failures. It is too specific for that. But it is exactly the kind of upstream fix that enthusiasts should notice when troubleshooting recent kernel behavior: a VF-only teardown condition, a VCN block, an IRQ release warning, and a call trace during deinitialization.
If you are running a Linux host with a Windows guest and AMD GPU passthrough, the pragmatic response is not to chase the CVE number in isolation. It is to compare your kernel changelog against the stable fix, test shutdown and restart paths, and preserve logs around module unloads and VM teardown.
That is especially true for systems using vendor-supplied AMDGPU stacks or DKMS-style modules. The trace’s tainted-module status is a reminder that many real-world GPU setups are not pristine upstream kernels. They are layered combinations of distro kernels, backported DRM code, vendor modules, and local configuration.
A teardown warning can break confidence even when it does not break the machine. Administrators need to know whether an error message is harmless, whether it indicates resource leakage, whether it blocks future device initialization, or whether it points to a deeper mismatch in the virtualization stack. CVE-2026-43298 appears to be about avoiding an invalid release rather than plugging a known exploit path, but that still improves determinism.
Security teams should also resist the temptation to ignore all GPU driver CVEs as “graphics stuff.” The GPU is a privileged DMA-capable device with firmware, memory managers, command processors, media engines, and interrupt paths. On virtualized hosts, its driver is part of the boundary between workloads and hardware.
That does not make this CVE catastrophic. It makes it structurally important. The health of the GPU driver is part of the health of the host, and the host is what enforces the promises made to every VM above it.
This is the kind of issue that should flow into patch planning rather than incident response. If your environment does not use AMDGPU virtual functions or VCNv2.5 paths, it is likely not urgent. If it does, it belongs in the next kernel qualification cycle with explicit teardown testing.
That has produced predictable fatigue. Security teams see a new kernel CVE with no score, no exploit, and a terse driver-specific description. Administrators see a component they may not use. Vendors see another item to ingest, map, and backport.
The answer is not to pretend every kernel CVE is equally dangerous. It is to build enough asset intelligence to know when a small record maps to a large operational dependency. A container host without AMD GPUs can treat this differently from a KVM host exporting AMD virtual functions to production guests.
The same is true for home labs. If you run Windows 11 in a VM with GPU passthrough on a Linux host, you are now operating the kind of stack that used to belong only to enterprise virtualization teams. That is exciting, but it also means upstream kernel churn can affect your “desktop” in ways that look like datacenter maintenance problems.
CVE records are names, not narratives. The narrative has to be supplied by the environment.
It is also why bugs like this happen. A code path that is correct for one function type may be wrong for another. An interrupt that exists for a physical function may not be enabled for a virtual function. A cleanup sequence that appears symmetrical on paper may not be symmetrical in the real hardware state machine.
The interesting engineering lesson is that cleanup code is harder than it looks. Developers often focus on initialization because that is where features come alive. But deinitialization has to reverse only the actions that actually happened, not the actions that might have happened in a nearby configuration.
That is exactly what this fix encodes. Do not release the VCN poison IRQ on a VF that did not enable it. In kernel terms, that is almost mundane. In operations terms, it is the difference between a clean shutdown path and a scary trace in the logs.
For Windows users inside VMs, the answer changes. If your Windows installation depends on a Linux host that owns the physical AMD GPU, the Linux host’s kernel and driver stack are part of your Windows experience. A shutdown, reset, or detach problem below the guest can look like a Windows graphics issue even when Windows is merely the passenger.
That is a recurring theme in modern troubleshooting. The visible operating system is not always the controlling operating system. The host kernel, firmware, hypervisor, and device driver can all determine whether the guest sees a stable GPU.
Administrators should therefore document GPU topology with the same seriousness they document storage and networking topology. Which host owns the GPU? Which guests receive virtual or passed-through functions? Which kernel branch is in use? Which firmware packages and AMDGPU components are installed? Without that map, a CVE like this is either overblown or missed entirely.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
 A Small AMDGPU Fix Becomes a CVE Because the Kernel Is the Boundary
A Small AMDGPU Fix Becomes a CVE Because the Kernel Is the Boundary
The Linux kernel’s CVE stream has made peace with an uncomfortable truth: not every vulnerability looks like an exploit demo. CVE-2026-43298 is a case study in that shift. The defect sits in the Direct Rendering Manager’s AMDGPU driver, specifically around VCN, AMD’s video codec engine, and the handling of a virtual function during device shutdown.The bug description is blunt. On VCNv2.5, a VF does not enable the VCN poison interrupt, yet the cleanup path attempted to release it anyway. The result was a warning in
amdgpu_irq_put() and a call trace during deinitialization, shown in the report against an Ubuntu 22.04-derived 6.8 generic kernel running under Red Hat KVM/RHEL hardware virtualization.That distinction matters. This is not a browser sandbox escape, a wormable SMB defect, or a GPU memory disclosure with immediate cloud-hosting implications. It is a kernel driver state-management flaw that appears when the driver unwinds a virtualized AMD GPU function and discovers that the bookkeeping does not match the hardware reality.
But kernel security is not only about remote code execution. A kernel warning in a teardown path can still matter because teardown paths are where systems are most brittle: module unloads, device resets, VM shutdowns, host maintenance, passthrough handoffs, and error recovery. The closer a bug sits to those paths, the more it intersects with the daily work of administrators who need machines to survive routine operations.
The Interesting Word Is “VF,” Not “Poison”
The acronym that carries the real weight here is VF. In PCIe virtualization, a physical GPU can expose virtual functions so that guest systems or isolated workloads interact with a slice of the device rather than the entire physical function. That model is central to SR-IOV-style designs and to the broader enterprise ambition of making GPUs schedulable, shareable, and manageable infrastructure.The CVE’s “poison IRQ” language sounds dramatic, but in this context it is driver machinery. RAS, or reliability, availability, and serviceability, features often deal with poison events: hardware-detected faults, corrupted data paths, or error-signaling mechanisms that need software attention. An interrupt associated with that machinery is useful only if the particular hardware path enabled it in the first place.
The failure here is the mismatch. The VF path did not enable that VCN poison interrupt on VCNv2.5, but the shutdown code acted as if it had. When the driver later tried to put, or release, an interrupt reference that was never acquired, the kernel complained.
That makes the patch conceptually simple: skip releasing the VCN poison IRQ on VF. The fix is less a redesign than a correction of the driver’s mental model. The VF is not a smaller physical function; it is a different operating mode with different initialization and cleanup obligations.
This is also why the CVE is more useful to administrators than its sparse scoring data suggests. There is no NVD CVSS score attached yet, and no NVD enrichment beyond the received kernel record. Still, the condition described is concrete enough to scope: AMDGPU, VCNv2.5, VF behavior, deinitialization, and a call trace in the IRQ release path.
Virtualized GPUs Have Outgrown Their “Special Case” Era
For years, GPU passthrough and virtualized graphics lived in a liminal space. Enthusiasts used VFIO to pass Radeon cards into gaming VMs. Workstation users built elaborate Linux hosts with Windows guests. Cloud and VDI vendors treated GPU partitioning as premium infrastructure. In each case, GPU virtualization was powerful, but it often felt like something bolted onto an operating system stack that had been designed for simpler devices.That era is ending. GPUs are no longer peripheral accelerators in the old sense; they are compute, display, media, AI, and encoding engines rolled into one high-state device. The driver has to understand power management, firmware queues, memory eviction, interrupt routing, reset domains, video codecs, RAS reporting, and virtualization boundaries.
CVE-2026-43298 lands in that world. VCN is the video codec block, not the shader core that most users associate with graphics performance. Yet the bug appears in a path that can affect virtual-function deinitialization. That tells us the attack surface and failure surface of a modern GPU driver are distributed across the entire device, not only the obvious rendering pipeline.
For WindowsForum readers, the Windows angle is not that this is a Windows kernel vulnerability. It is not. The Windows angle is that many Windows workloads now live as guests on Linux hosts, and many enthusiast Windows environments are built around Linux hypervisors. A Linux amdgpu flaw can therefore be a Windows reliability problem when the Windows system is the guest that depends on a GPU being cleanly handed off, reset, or detached.
That is the practical reality of mixed-platform computing. The host kernel owns the device. The guest operating system experiences the consequences.
The Call Trace Is a Symptom, Not the Whole Disease
The trace included with the CVE record is familiar to anyone who has debugged kernel driver failures. It begins with DRM cleanup, hits a warning inamdgpu_irq_put(), and shows rmmod as the process context. The system is tainted by out-of-tree or externally built modules, which is common in GPU and vendor-driver testing environments.It would be easy to dismiss this as a noisy warning. After all, the record does not describe privilege escalation, arbitrary write, or information disclosure. The NVD entry has no severity score yet. The fix appears to be a small guard around an IRQ release call.
That dismissal would be too casual. Kernel warnings during teardown are operationally significant because teardown is often chained to other actions. A VM stops, a device resets, a module unloads, a host migrates workload, a service restarts, and suddenly a warning that seemed harmless becomes the first clue in a longer stability problem.
The trace also shows the bug appearing under KVM, which is exactly where virtual GPU edge cases tend to surface. Virtualization forces drivers through code paths that bare-metal desktop users may never touch. A Radeon card sitting in a gaming PC may never encounter this condition, while the same hardware family in a lab, VDI node, passthrough workstation, or cloud-adjacent setup might.
This is the trap in reading CVE records too literally. The CVE describes the resolved bug, not the entire operational context. The absence of a dramatic exploit narrative does not mean the issue is irrelevant; it means the risk has to be evaluated through deployment architecture.
Microsoft’s Presence Is a Routing Signal, Not a Windows Patch
The source link provided through Microsoft’s Security Update Guide can confuse the story. Microsoft catalogs many CVEs because its ecosystem now includes Windows, Azure, Linux distributions, containers, firmware, open-source components, and cloud-hosted dependencies. Seeing an MSRC page attached to a Linux kernel CVE does not automatically mean Microsoft shipped a Windows fix or that Windows clients are directly vulnerable.For administrators, the right reading is more nuanced. Microsoft has strong reasons to track Linux kernel vulnerabilities, especially where Azure hosts, Linux guests, GPU-backed workloads, confidential computing boundaries, or container platforms may intersect. A Linux kernel bug in a GPU driver can be relevant to Microsoft’s world even when it is not a bug in Windows.
That is increasingly normal. The old patch taxonomy — Windows issues on Patch Tuesday, Linux issues somewhere else, firmware issues from the OEM — does not map cleanly onto modern fleets. A single workload may depend on Windows Server, Ubuntu guests, AMD firmware, a hypervisor, a container runtime, and Azure or on-prem orchestration.
CVE-2026-43298 therefore sits in a category that security teams should recognize: cross-ecosystem infrastructure hygiene. It is not a reason for Windows desktop users to panic. It is a reason for teams running AMD GPU virtualization under Linux to check kernel advisories, stable backports, vendor kernels, and host update schedules.
The discipline is to separate catalog visibility from product impact. MSRC visibility tells you Microsoft is aware of the CVE in its security universe. It does not, by itself, define exploitability, affected Windows versions, or patch urgency for a Windows endpoint.
The Missing CVSS Score Is Part of the Story
At publication, NVD had not assigned a CVSS 4.0, 3.x, or 2.0 score for CVE-2026-43298. That is not unusual in the current vulnerability-management climate, and it should not paralyze triage. In fact, this CVE shows why a score-first workflow is often too crude for kernel bugs.A future score may rate the issue low if the impact is limited to warnings during deinitialization. It may remain unscored for some time. It may be classified under a broad weakness category that tells administrators very little about whether their systems are actually exposed. None of those outcomes changes the practical scoping questions.
The meaningful questions are concrete. Are you running Linux hosts with AMDGPU? Are you using virtual functions, SR-IOV-like GPU partitioning, or passthrough workflows? Are affected kernels or vendor driver packages in use? Have you seen call traces around
amdgpu_irq_put() or VCN teardown during module unload, VM shutdown, or host maintenance?This is where CVSS can mislead by omission. A low-scored bug in an irrelevant component is noise. An unscored bug in a driver path your infrastructure exercises every night is not noise.
That does not mean every kernel CVE deserves emergency treatment. It means the score is only one input, and for infrastructure drivers it is often a late-arriving one. The earlier signal comes from matching the described code path to the systems you actually operate.
The Patch Says More Than the Record
The three stable kernel references attached to the CVE indicate that the fix has been carried into maintained kernel branches. That matters because most administrators will not apply a standalone commit from upstream; they will receive the change through a distribution kernel, a vendor kernel, or a hardware enablement stack.The fix itself is narrow. It does not claim to redesign AMDGPU virtualization, rework RAS handling, or change VCN initialization. It simply avoids releasing an interrupt that the VF never enabled.
That kind of patch is both reassuring and frustrating. Reassuring, because small conditional fixes are easier to audit and less likely to introduce sweeping regressions. Frustrating, because the operational symptom may be buried inside larger kernel update cycles, especially for distributions that backport fixes without changing the visible major kernel version.
Ubuntu users, for example, may see a
6.8.0-xx-generic kernel line and assume all systems with that number are alike. Enterprise distributions routinely backport individual fixes, so the real question is not only “what upstream kernel version am I on?” but “has my vendor’s build included the relevant stable patch?” That is tedious, but it is how Linux fleet management actually works.The included trace mentions Ubuntu 22.04.1 with a 6.8 generic kernel, KVM, and AMDGPU modules marked as externally built. That should not be read as a definitive affected-version matrix. It is evidence of the environment in which the warning was observed, not a complete map of all affected distributions or hardware configurations.
For Enthusiasts, This Is a VFIO Smell Test
WindowsForum has a long memory for GPU passthrough pain. Single-GPU passthrough, dual-GPU host setups, Looking Glass builds, and “why won’t my Radeon reset after the VM shuts down?” threads all live in the same neighborhood as this CVE, even if they are not the same bug.The key pattern is device lifecycle fragility. Passing a GPU to a VM is not just about getting the guest driver to install. It is about binding, unbinding, resetting, unloading, reloading, and surviving the transition between host ownership and guest ownership. Every one of those transitions is a place where driver state must line up with hardware state.
CVE-2026-43298 is not a universal explanation for AMDGPU unload failures. It is too specific for that. But it is exactly the kind of upstream fix that enthusiasts should notice when troubleshooting recent kernel behavior: a VF-only teardown condition, a VCN block, an IRQ release warning, and a call trace during deinitialization.
If you are running a Linux host with a Windows guest and AMD GPU passthrough, the pragmatic response is not to chase the CVE number in isolation. It is to compare your kernel changelog against the stable fix, test shutdown and restart paths, and preserve logs around module unloads and VM teardown.
That is especially true for systems using vendor-supplied AMDGPU stacks or DKMS-style modules. The trace’s tainted-module status is a reminder that many real-world GPU setups are not pristine upstream kernels. They are layered combinations of distro kernels, backported DRM code, vendor modules, and local configuration.
For Enterprises, The Risk Is Maintenance Reliability
In enterprise environments, the most immediate concern is not a desktop user seeing a warning indmesg. It is whether GPU-backed hosts can be maintained predictably. Virtual desktop infrastructure, media encoding farms, AI-adjacent workloads with display or video components, and lab clusters all depend on clean device lifecycle events.A teardown warning can break confidence even when it does not break the machine. Administrators need to know whether an error message is harmless, whether it indicates resource leakage, whether it blocks future device initialization, or whether it points to a deeper mismatch in the virtualization stack. CVE-2026-43298 appears to be about avoiding an invalid release rather than plugging a known exploit path, but that still improves determinism.
Security teams should also resist the temptation to ignore all GPU driver CVEs as “graphics stuff.” The GPU is a privileged DMA-capable device with firmware, memory managers, command processors, media engines, and interrupt paths. On virtualized hosts, its driver is part of the boundary between workloads and hardware.
That does not make this CVE catastrophic. It makes it structurally important. The health of the GPU driver is part of the health of the host, and the host is what enforces the promises made to every VM above it.
This is the kind of issue that should flow into patch planning rather than incident response. If your environment does not use AMDGPU virtual functions or VCNv2.5 paths, it is likely not urgent. If it does, it belongs in the next kernel qualification cycle with explicit teardown testing.
The Kernel CVE Firehose Rewards Asset Context
CVE-2026-43298 also illustrates the wider problem with the modern Linux kernel CVE stream. The kernel is enormous, and the number of CVEs assigned to resolved bugs has grown dramatically. Many entries now describe fixes that look, to outsiders, like ordinary robustness patches.That has produced predictable fatigue. Security teams see a new kernel CVE with no score, no exploit, and a terse driver-specific description. Administrators see a component they may not use. Vendors see another item to ingest, map, and backport.
The answer is not to pretend every kernel CVE is equally dangerous. It is to build enough asset intelligence to know when a small record maps to a large operational dependency. A container host without AMD GPUs can treat this differently from a KVM host exporting AMD virtual functions to production guests.
The same is true for home labs. If you run Windows 11 in a VM with GPU passthrough on a Linux host, you are now operating the kind of stack that used to belong only to enterprise virtualization teams. That is exciting, but it also means upstream kernel churn can affect your “desktop” in ways that look like datacenter maintenance problems.
CVE records are names, not narratives. The narrative has to be supplied by the environment.
AMDGPU’s Complexity Is the Price of Doing Everything
AMDGPU is not a simple display driver. It is a large kernel subsystem that supports a wide range of AMD GPU generations, memory managers, display features, compute paths, video engines, power management, virtualization modes, and reliability features. That breadth is why AMD hardware works across so many Linux scenarios, from gaming handhelds to workstations to cloud hosts.It is also why bugs like this happen. A code path that is correct for one function type may be wrong for another. An interrupt that exists for a physical function may not be enabled for a virtual function. A cleanup sequence that appears symmetrical on paper may not be symmetrical in the real hardware state machine.
The interesting engineering lesson is that cleanup code is harder than it looks. Developers often focus on initialization because that is where features come alive. But deinitialization has to reverse only the actions that actually happened, not the actions that might have happened in a nearby configuration.
That is exactly what this fix encodes. Do not release the VCN poison IRQ on a VF that did not enable it. In kernel terms, that is almost mundane. In operations terms, it is the difference between a clean shutdown path and a scary trace in the logs.
Windows Users Should Look One Layer Down
For a Windows user on bare metal, CVE-2026-43298 is mostly background noise. The bug is in the Linux kernel’s AMDGPU driver, and the record does not indicate a Windows client vulnerability. Updating Windows or Radeon Software on a standard Windows gaming PC is not the relevant mitigation path for this CVE.For Windows users inside VMs, the answer changes. If your Windows installation depends on a Linux host that owns the physical AMD GPU, the Linux host’s kernel and driver stack are part of your Windows experience. A shutdown, reset, or detach problem below the guest can look like a Windows graphics issue even when Windows is merely the passenger.
That is a recurring theme in modern troubleshooting. The visible operating system is not always the controlling operating system. The host kernel, firmware, hypervisor, and device driver can all determine whether the guest sees a stable GPU.
Administrators should therefore document GPU topology with the same seriousness they document storage and networking topology. Which host owns the GPU? Which guests receive virtual or passed-through functions? Which kernel branch is in use? Which firmware packages and AMDGPU components are installed? Without that map, a CVE like this is either overblown or missed entirely.
The Practical Read for CVE-2026-43298
This is not a panic-button vulnerability, but it is not meaningless paperwork either. It is a narrow kernel fix with a clear operational signature, relevant mainly to Linux systems using AMDGPU virtual-function paths around VCNv2.5 and driver deinitialization.- Systems that do not run AMDGPU, do not expose AMD GPU virtual functions, and do not use the affected VCN teardown path are unlikely to have meaningful exposure to this specific issue.
- Hosts running AMD GPU virtualization should verify whether their distribution or vendor kernel has incorporated the stable fix referenced by the CVE record.
- Administrators should look for call traces involving
amdgpu_irq_put()andvcn_v2_5_hw_fini()during module unload, VM shutdown, device reset, or host maintenance. - Windows guests using AMD GPU passthrough or virtualized GPU resources depend on the Linux host’s AMDGPU behavior, even though the CVE is not a Windows kernel bug.
- The lack of an NVD CVSS score should not delay environment-specific triage, because the deployment context determines whether the bug is irrelevant noise or a maintenance reliability concern.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center