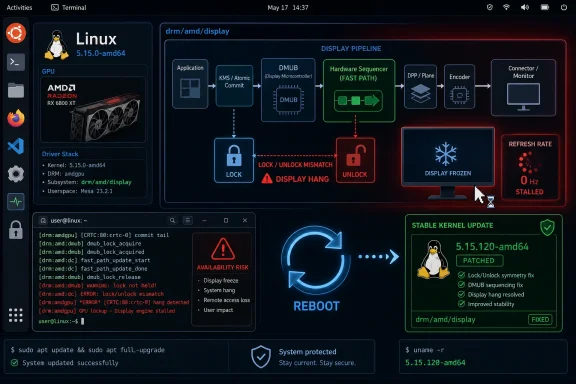
CVE-2026-43305 is a newly published Linux kernel vulnerability, disclosed through kernel.org and surfaced in Microsoft’s Security Update Guide on May 8, 2026, that fixes an AMD display-driver bug capable of hanging affected systems during a fast display update path. That plain sentence is the whole story for scanners, but not for administrators. The more interesting story is why a lock/unlock mismatch in AMD’s Linux graphics stack becomes a security-tracked vulnerability at all, and why WindowsForum readers should care even when the affected code is not Windows. Modern endpoint risk increasingly lives in the firmware-adjacent, driver-heavy territory where operating systems, GPUs, panels, power features, and vendor update pipelines all blur together.
The description of CVE-2026-43305 is almost aggressively unglamorous: the AMD display driver takes a hardware lock in one condition and fails to release it under the same condition. The affected area is
That mismatch matters because locks are promises. In kernel code, a lock says: I am about to touch shared state, and nobody else should proceed until I am done. If the unlock never comes, the rest of the system can wait forever, which is how a few lines of driver logic become a screen freeze, a dead session, or a hard reboot.
The CVE record does not yet carry an NVD CVSS score, and that absence is important. There is no public indication here of remote code execution, privilege escalation, credential theft, or a wormable attack chain. What is described is an availability problem: a hang triggered by a particular display fast path on AMD hardware configurations without FAMS support.
That does not make it irrelevant. Security teams have spent the last decade being trained to prioritize confidentiality and integrity first, but availability remains the part of security users actually experience. A laptop that hangs during display-state changes is not a theoretical defect to the person presenting from it, maintaining it remotely, or relying on it as a kiosk, workstation, build machine, or Linux desktop in a mixed fleet.
That odd framing is part of the modern vulnerability ecosystem. Microsoft’s security surfaces, including MSRC pages and Defender-facing vulnerability intelligence, often aggregate issues beyond classic Windows Patch Tuesday items because enterprises do not run Windows alone anymore. They run Windows clients, Linux servers, WSL workloads, Azure images, containers, developer laptops, GPU-enabled workstations, and hybrid estates where asset inventories are more important than operating-system tribalism.
For WindowsForum readers, the relevance is not that Windows 11 suddenly inherited this exact bug. It did not, based on the available description. The relevance is that Windows administrators increasingly own Linux risk by proxy. They own Ubuntu workstations used by developers, Linux-based CI runners, GPU nodes for AI workloads, SteamOS-like gaming systems, dual-boot laptops, and corporate machines where Linux kernel advisories show up in the same dashboards as Microsoft CVEs.
The practical lesson is therefore less “patch Windows” and more “do not let the Microsoft label fool you into thinking this is a Microsoft component.” CVE-2026-43305 belongs to the Linux kernel’s AMD display stack. If your vulnerability management tool flags it, the remediation path runs through kernel updates from the relevant Linux distribution or vendor image, not through a Windows cumulative update.
DMUB refers to AMD’s Display Microcontroller Unit. In practice, it helps manage display-related operations that need careful coordination with the GPU’s display hardware. The kernel driver sends commands, hardware state changes, and the driver must sometimes ensure that a given update is protected by a lock so that other display activity does not collide with it.
The affected path is described as an HWSS fast path. HWSS, or Hardware Sequencer, is the part of the display stack responsible for choreographing display state transitions. A “fast path” is the optimization route: use a shorter, less expensive sequence when the driver determines that a change does not require the full heavyweight validation and programming sequence.
Fast paths are where performance engineering meets risk. They exist because users expect display changes to be smooth: refresh-rate shifts, panel self-refresh transitions, replay behavior, power-saving states, docking changes, and screen updates should not feel like a driver is rebuilding the world each time. But optimization paths also multiply assumptions, and CVE-2026-43305 is exactly the kind of bug that appears when two assumptions drift apart.
This is a classic asymmetry bug. It is not glamorous, but it is dangerous in low-level code because the correctness of a lock depends on pairing. The kernel does not care that the lock was acquired for a good reason if the release logic later forgets that reason existed.
The published fix is equally unromantic: store a flag indicating whether the lock should be used, then reuse that same flag when deciding whether to unlock. That is the kind of patch that looks obvious after the fact. It is also the kind of patch that prevents a driver from making the same decision twice and getting two different answers.
The bug is reported to show up when the fast path is used for an ASIC without FAMS support. That caveat matters because it narrows the affected population, but it does not eliminate concern. Display drivers are full of hardware-generation branches, feature gates, and panel-specific behavior, so administrators should not assume safety merely because only some AMD configurations are implicated.
That is a win for battery life and thermals. It is also a complexity tax. Laptop panels, embedded DisplayPort links, GPU display engines, firmware, and operating-system drivers all have to agree on exactly when the display pipeline can sleep, replay, refresh itself, or accept a new state transition.
In consumer terms, this is why modern graphics bugs so often appear as “my screen froze when waking,” “the laptop hangs when changing refresh rate,” “external monitor reconnects cause a black screen,” or “the system locks up when the panel powers down.” Those reports sound vague because the user sees only the last symptom. Underneath, the driver may be navigating a dense matrix of hardware-generation behavior and power-management features.
CVE-2026-43305 fits that pattern. It is not a buffer overflow with a cinematic exploit chain. It is a coordination failure in the kind of feature-rich display path that laptop users depend on every day and rarely think about until it fails.
The risk is especially annoying because GPU/display hangs are difficult to triage cleanly. Logs may be incomplete. Users may describe symptoms inconsistently. The same machine may run for days before reproducing the issue. The trigger may depend on display topology, kernel version, panel type, power state, and whether a particular fast path is taken.
Security teams also have to deal with scanner behavior. A CVE without an NVD score can still appear in vulnerability dashboards, compliance reports, and executive summaries. When that happens, the lack of a score does not reduce workload; it often increases it, because someone must decide whether the finding is real, applicable, exploitable, urgent, or merely noisy.
For CVE-2026-43305, the answer should be measured. It is not a panic item from the public record. It is, however, a legitimate kernel stability flaw in a widely used GPU driver family, and it deserves normal kernel hygiene rather than indefinite deferral.
This is where mature vulnerability management separates itself from dashboard theater. A CVSS score is useful, but it is not a substitute for applicability. The right question is not “is this a 7.8 or a 5.5?” The right question is “do we run affected Linux kernels on AMD display hardware in contexts where a hang creates meaningful operational risk?”
For a headless Linux server with no AMD GPU display stack in use, this CVE is likely irrelevant. For a developer laptop fleet using AMD APUs and external monitors, it may be more relevant than its eventual score suggests. For GPU-enabled desktops in labs, media workflows, Linux gaming rigs, or kiosks, the availability angle becomes more concrete.
The absence of scoring should also remind administrators that CVE publication is not the same as exploit publication. The public description explains the bug class and the fix, but it does not describe an attacker-controlled remote trigger. Treat it as a kernel maintenance issue unless additional evidence emerges.
That means remediation depends on the distro. Ubuntu, Debian, Fedora, Arch, openSUSE, Red Hat derivatives, enterprise kernels, and vendor appliance images all have their own packaging cadence. The same CVE may be fixed in one distribution’s kernel stream while still pending in another, and the visible kernel version number alone may not tell the whole story because enterprise vendors routinely backport fixes without rebasing to the latest upstream kernel.
This is why “what kernel version fixes it?” can be the wrong question. The better question is whether your vendor’s kernel package includes the relevant
For unmanaged Linux desktops, the advice is simpler: install current kernel updates and reboot into the fixed kernel. Driver bugs do not usually disappear until the running kernel changes, and a patched package sitting on disk will not help a machine still booted into an older image.
The obvious example is dual-boot and developer hardware. A company may standardize on Windows laptops while allowing Linux partitions for engineering, embedded development, security research, or GPU experimentation. If those machines use AMD integrated graphics, the Linux side may be exposed even though the Windows side is not.
WSL complicates the mental model, but probably not in the way some users fear. Windows Subsystem for Linux does not generally mean the guest distribution is running its own full Linux kernel display driver stack against the physical AMD display hardware. WSL risk should be evaluated based on Microsoft’s WSL kernel and the actual subsystem architecture, not by assuming every Linux kernel CVE maps directly to every WSL distro installed from the Store.
The broader lesson is asset inventory. If your vulnerability platform flags a Linux kernel CVE on a Windows-managed endpoint, do not swat it away automatically. Determine whether the device actually boots Linux, runs a Linux VM with GPU passthrough, hosts containers on Linux, or merely has a userland distribution that does not exercise the vulnerable kernel driver path.
CVE-2026-43305 is not the scary version of that story. It is a hang caused by a mismatched lock decision. Yet it lives in the same general risk neighborhood as more serious GPU-driver flaws because the graphics stack is large, stateful, and hardware-specific.
For Linux users, AMD’s open driver stack is both a strength and a source of visible churn. Bugs and fixes are discussed in public, patches move through upstream and stable trees, and the trail is inspectable. That transparency is healthy. It also means administrators see defects that might remain opaque in a purely proprietary driver ecosystem.
For Windows users, the comparable lesson is to treat GPU updates as part of platform maintenance rather than gaming decoration. Display drivers are not optional frills anymore. They are security-relevant components tied to browser acceleration, video decode, conferencing, AI workloads, desktop composition, and remote-work stability.
Security portals are becoming aggregators. They ingest CVEs, enrich records, expose API data, connect to endpoint telemetry, and feed compliance dashboards. The convenience is real, but the price is context collapse. A kernel.org issue, an Office remote-code-execution flaw, a third-party library bug, and a firmware advisory can all appear in the same visual language.
That is efficient for reporting and dangerous for decision-making. The source of a CVE determines who fixes it, how it is deployed, what systems are affected, and whether compensating controls make sense. CVE-2026-43305 should be routed to Linux platform owners, endpoint engineering teams managing Linux hardware, and administrators responsible for AMD-based Linux images.
The Microsoft angle is therefore less about culpability and more about visibility. If a Windows-oriented tool brings this to your attention, treat that as a useful signal. Just do not let the signal obscure the actual component.
That is what the fix does, according to the CVE description. It stores whether the lock should be used and then uses that stored value for the unlock decision. This is not merely tidier code; it reduces the chance that future feature additions will update one branch and forget the other.
Kernel display code is especially vulnerable to this kind of drift because features accrete. A new panel feature, a new ASIC generation, a new replay mode, a new fast path, or a new hardware lock requirement may be added for legitimate reasons. Each addition can widen the gap between originally symmetrical paths.
The lesson for developers is familiar but worth repeating: in low-level systems code, state transitions should be paired by construction wherever possible. If the lock condition and unlock condition are independently re-evaluated, the code is inviting time, refactoring, and feature flags to break the contract.
That makes exposure hardware- and configuration-dependent. A Linux server using an Intel iGPU or NVIDIA GPU is not the obvious target population. A headless AMD server not using the affected display path may also be outside practical exposure. A laptop with an AMD APU and an internal eDP panel is a more plausible candidate.
There is also a difference between installed code and reachable code. Many kernels include drivers for hardware that is not present. Vulnerability scanners sometimes flag by package version rather than by runtime hardware path, which can overstate risk. Conversely, a user with an affected AMD laptop may not see the finding at all if their scanner lacks kernel-driver granularity.
The best response is not to debate the CVE abstractly. Identify AMD Linux endpoints, confirm kernel advisory status, deploy vendor updates, and reboot. If the systems are high-availability workstations or kiosks, test the kernel update against the display configurations users actually run.
Display-driver hangs matter most where display state changes matter. That means laptops waking and sleeping, workstations changing monitors, docking stations renegotiating links, high-refresh panels shifting modes, and power-saving features activating during idle or presentation use. The affected code is part of the machinery that makes a graphical Linux session tolerable on modern AMD hardware.
That should interest WindowsForum’s enthusiast audience as well. AMD laptops and handhelds have made Linux graphics support more mainstream, especially among users experimenting with gaming distributions, development environments, and lightweight desktop setups. Stability bugs in the display stack directly affect whether those systems feel polished or fragile.
For IT, the rise of Linux desktops in engineering organizations makes these bugs more than hobbyist material. A developer workstation that hard-hangs twice a week is not just annoying; it is lost time, support load, and a reason users lose confidence in managed platform standards.
The translation should say that the issue is a Linux kernel AMD display-driver hang fixed upstream and in stable commits, with applicability limited to systems using the affected AMD display path. It should say that there is no current public indication, from the supplied record, of remote code execution or privilege escalation. It should say that remediation is through Linux kernel updates from the relevant distribution, followed by a reboot.
That level of specificity helps desktop engineering teams act without turning every CVE into a fire drill. It also helps security teams avoid the false precision of severity scores. A no-score CVE can still be operationally important, and a scored CVE can still be irrelevant to your environment.
The central question for administrators is not whether the CVE sounds scary. It is whether the vulnerable code runs on machines where a hang would matter.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center
 A Small AMD Display Bug Became a CVE Because Availability Is Still Security
A Small AMD Display Bug Became a CVE Because Availability Is Still Security
The description of CVE-2026-43305 is almost aggressively unglamorous: the AMD display driver takes a hardware lock in one condition and fails to release it under the same condition. The affected area is drm/amd/display, specifically a DMUB hardware lock used in a Hardware Sequencer fast path. In ordinary language, the kernel can enter a path where it believes it must coordinate display hardware access through AMD’s display microcontroller, then later decides—incorrectly—that no matching unlock is required.That mismatch matters because locks are promises. In kernel code, a lock says: I am about to touch shared state, and nobody else should proceed until I am done. If the unlock never comes, the rest of the system can wait forever, which is how a few lines of driver logic become a screen freeze, a dead session, or a hard reboot.
The CVE record does not yet carry an NVD CVSS score, and that absence is important. There is no public indication here of remote code execution, privilege escalation, credential theft, or a wormable attack chain. What is described is an availability problem: a hang triggered by a particular display fast path on AMD hardware configurations without FAMS support.
That does not make it irrelevant. Security teams have spent the last decade being trained to prioritize confidentiality and integrity first, but availability remains the part of security users actually experience. A laptop that hangs during display-state changes is not a theoretical defect to the person presenting from it, maintaining it remotely, or relying on it as a kiosk, workstation, build machine, or Linux desktop in a mixed fleet.
The Vulnerability Is in Linux, but the Signal Belongs to Every Fleet
The user-visible source link points to Microsoft’s Security Update Guide, which can look strange at first glance. Microsoft is not the maintainer of the Linux kernel’s AMD display driver, and this is not a Windows graphics vulnerability. The CVE source is kernel.org, with upstream stable references to Linux commits that correct the bug.That odd framing is part of the modern vulnerability ecosystem. Microsoft’s security surfaces, including MSRC pages and Defender-facing vulnerability intelligence, often aggregate issues beyond classic Windows Patch Tuesday items because enterprises do not run Windows alone anymore. They run Windows clients, Linux servers, WSL workloads, Azure images, containers, developer laptops, GPU-enabled workstations, and hybrid estates where asset inventories are more important than operating-system tribalism.
For WindowsForum readers, the relevance is not that Windows 11 suddenly inherited this exact bug. It did not, based on the available description. The relevance is that Windows administrators increasingly own Linux risk by proxy. They own Ubuntu workstations used by developers, Linux-based CI runners, GPU nodes for AI workloads, SteamOS-like gaming systems, dual-boot laptops, and corporate machines where Linux kernel advisories show up in the same dashboards as Microsoft CVEs.
The practical lesson is therefore less “patch Windows” and more “do not let the Microsoft label fool you into thinking this is a Microsoft component.” CVE-2026-43305 belongs to the Linux kernel’s AMD display stack. If your vulnerability management tool flags it, the remediation path runs through kernel updates from the relevant Linux distribution or vendor image, not through a Windows cumulative update.
DMUB Is Where Display Plumbing Stops Looking Like Display Plumbing
The phrase DMUB HW lock is not written for normal humans, but it points to a real architectural trend. AMD’s modern display stack does not consist merely of a kernel driver talking directly to a dumb framebuffer. It involves display engines, link-management logic, panel power features, microcontroller firmware, and increasingly complex sequencing around when hardware state can change.DMUB refers to AMD’s Display Microcontroller Unit. In practice, it helps manage display-related operations that need careful coordination with the GPU’s display hardware. The kernel driver sends commands, hardware state changes, and the driver must sometimes ensure that a given update is protected by a lock so that other display activity does not collide with it.
The affected path is described as an HWSS fast path. HWSS, or Hardware Sequencer, is the part of the display stack responsible for choreographing display state transitions. A “fast path” is the optimization route: use a shorter, less expensive sequence when the driver determines that a change does not require the full heavyweight validation and programming sequence.
Fast paths are where performance engineering meets risk. They exist because users expect display changes to be smooth: refresh-rate shifts, panel self-refresh transitions, replay behavior, power-saving states, docking changes, and screen updates should not feel like a driver is rebuilding the world each time. But optimization paths also multiply assumptions, and CVE-2026-43305 is exactly the kind of bug that appears when two assumptions drift apart.
The Lock Path and the Unlock Path Disagreed
The kernel.org description gives a compact explanation of the fault: the evaluation for whether the driver needed to use the DMUB hardware lock was not the same as the evaluation for whether it needed to unlock. That means the driver could take a lock using one condition and later skip the unlock because a narrower condition said it was not required.This is a classic asymmetry bug. It is not glamorous, but it is dangerous in low-level code because the correctness of a lock depends on pairing. The kernel does not care that the lock was acquired for a good reason if the release logic later forgets that reason existed.
The published fix is equally unromantic: store a flag indicating whether the lock should be used, then reuse that same flag when deciding whether to unlock. That is the kind of patch that looks obvious after the fact. It is also the kind of patch that prevents a driver from making the same decision twice and getting two different answers.
The bug is reported to show up when the fast path is used for an ASIC without FAMS support. That caveat matters because it narrows the affected population, but it does not eliminate concern. Display drivers are full of hardware-generation branches, feature gates, and panel-specific behavior, so administrators should not assume safety merely because only some AMD configurations are implicated.
FAMS, PSR, Replay, and the Curse of Power-Saving Complexity
The CVE text calls out ASICs without FAMS support. The broader patch discussion around this driver area also points toward display features such as Panel Self Refresh and Replay as part of the lock-management universe. These technologies exist to save power and improve responsiveness by allowing parts of the display pipeline to avoid unnecessary work when screen contents are stable or when updates can be handled more efficiently.That is a win for battery life and thermals. It is also a complexity tax. Laptop panels, embedded DisplayPort links, GPU display engines, firmware, and operating-system drivers all have to agree on exactly when the display pipeline can sleep, replay, refresh itself, or accept a new state transition.
In consumer terms, this is why modern graphics bugs so often appear as “my screen froze when waking,” “the laptop hangs when changing refresh rate,” “external monitor reconnects cause a black screen,” or “the system locks up when the panel powers down.” Those reports sound vague because the user sees only the last symptom. Underneath, the driver may be navigating a dense matrix of hardware-generation behavior and power-management features.
CVE-2026-43305 fits that pattern. It is not a buffer overflow with a cinematic exploit chain. It is a coordination failure in the kind of feature-rich display path that laptop users depend on every day and rarely think about until it fails.
A Hang Is Not a Breach, but It Can Still Be Operationally Expensive
A kernel hang is sometimes dismissed as “just a denial of service,” as if denial of service were a minor inconvenience. In enterprise operations, that framing is too casual. A hung workstation can interrupt a remote session, corrupt unsaved work, break a build, stall a point-of-sale terminal, knock a monitoring screen offline, or force a physical intervention for a device that was supposed to be managed remotely.The risk is especially annoying because GPU/display hangs are difficult to triage cleanly. Logs may be incomplete. Users may describe symptoms inconsistently. The same machine may run for days before reproducing the issue. The trigger may depend on display topology, kernel version, panel type, power state, and whether a particular fast path is taken.
Security teams also have to deal with scanner behavior. A CVE without an NVD score can still appear in vulnerability dashboards, compliance reports, and executive summaries. When that happens, the lack of a score does not reduce workload; it often increases it, because someone must decide whether the finding is real, applicable, exploitable, urgent, or merely noisy.
For CVE-2026-43305, the answer should be measured. It is not a panic item from the public record. It is, however, a legitimate kernel stability flaw in a widely used GPU driver family, and it deserves normal kernel hygiene rather than indefinite deferral.
The Missing CVSS Score Is a Warning Against Score-Driven Triage
NVD had not yet provided CVSS scoring in the supplied record. That means organizations relying solely on numeric severity may mishandle the issue in either direction. Some tools may treat it as unknown and push it into a gray zone; others may infer severity from the presence of a CVE and create unnecessary alarm.This is where mature vulnerability management separates itself from dashboard theater. A CVSS score is useful, but it is not a substitute for applicability. The right question is not “is this a 7.8 or a 5.5?” The right question is “do we run affected Linux kernels on AMD display hardware in contexts where a hang creates meaningful operational risk?”
For a headless Linux server with no AMD GPU display stack in use, this CVE is likely irrelevant. For a developer laptop fleet using AMD APUs and external monitors, it may be more relevant than its eventual score suggests. For GPU-enabled desktops in labs, media workflows, Linux gaming rigs, or kiosks, the availability angle becomes more concrete.
The absence of scoring should also remind administrators that CVE publication is not the same as exploit publication. The public description explains the bug class and the fix, but it does not describe an attacker-controlled remote trigger. Treat it as a kernel maintenance issue unless additional evidence emerges.
Stable Kernel Backports Are the Real Patch Channel
The CVE record references two stable kernel commits. That is a strong sign that the fix has moved through the normal Linux stable machinery rather than remaining an isolated upstream-only change. For administrators, the crucial point is that most users will not apply those commits directly; they will consume them through distribution kernel packages.That means remediation depends on the distro. Ubuntu, Debian, Fedora, Arch, openSUSE, Red Hat derivatives, enterprise kernels, and vendor appliance images all have their own packaging cadence. The same CVE may be fixed in one distribution’s kernel stream while still pending in another, and the visible kernel version number alone may not tell the whole story because enterprise vendors routinely backport fixes without rebasing to the latest upstream kernel.
This is why “what kernel version fixes it?” can be the wrong question. The better question is whether your vendor’s kernel package includes the relevant
drm/amd/display fix. In a corporate environment, that answer should come from the distribution’s security advisory, package changelog, or vendor support channel.For unmanaged Linux desktops, the advice is simpler: install current kernel updates and reboot into the fixed kernel. Driver bugs do not usually disappear until the running kernel changes, and a patched package sitting on disk will not help a machine still booted into an older image.
Windows Admins Should Read This as a WSL and Fleet Inventory Problem
There is no sign that CVE-2026-43305 affects Windows’ own AMD display driver stack. Windows uses a different driver model, different vendor driver packages, and a different display architecture. But Windows administrators can still encounter this CVE through the systems around Windows.The obvious example is dual-boot and developer hardware. A company may standardize on Windows laptops while allowing Linux partitions for engineering, embedded development, security research, or GPU experimentation. If those machines use AMD integrated graphics, the Linux side may be exposed even though the Windows side is not.
WSL complicates the mental model, but probably not in the way some users fear. Windows Subsystem for Linux does not generally mean the guest distribution is running its own full Linux kernel display driver stack against the physical AMD display hardware. WSL risk should be evaluated based on Microsoft’s WSL kernel and the actual subsystem architecture, not by assuming every Linux kernel CVE maps directly to every WSL distro installed from the Store.
The broader lesson is asset inventory. If your vulnerability platform flags a Linux kernel CVE on a Windows-managed endpoint, do not swat it away automatically. Determine whether the device actually boots Linux, runs a Linux VM with GPU passthrough, hosts containers on Linux, or merely has a userland distribution that does not exercise the vulnerable kernel driver path.
GPU Drivers Have Become an Enterprise Attack Surface Even When the Bug Is Boring
The industry tends to notice GPU security only when the words “AI,” “cloud,” or “memory leak” are attached. That misses the quieter truth: graphics drivers have become one of the most complicated and privileged codebases on the endpoint. They parse untrusted inputs, manage memory, interact with firmware, coordinate power states, and run in or near the kernel.CVE-2026-43305 is not the scary version of that story. It is a hang caused by a mismatched lock decision. Yet it lives in the same general risk neighborhood as more serious GPU-driver flaws because the graphics stack is large, stateful, and hardware-specific.
For Linux users, AMD’s open driver stack is both a strength and a source of visible churn. Bugs and fixes are discussed in public, patches move through upstream and stable trees, and the trail is inspectable. That transparency is healthy. It also means administrators see defects that might remain opaque in a purely proprietary driver ecosystem.
For Windows users, the comparable lesson is to treat GPU updates as part of platform maintenance rather than gaming decoration. Display drivers are not optional frills anymore. They are security-relevant components tied to browser acceleration, video decode, conferencing, AI workloads, desktop composition, and remote-work stability.
Microsoft’s Presence in the Record Shows How Vulnerability Feeds Have Changed
The MSRC link in the supplied material is easy to misread. It can make a Linux kernel CVE look like a Microsoft vulnerability at a glance, especially in downstream tools that flatten every source into a single row. That flattening is one of the quiet hazards of modern vulnerability management.Security portals are becoming aggregators. They ingest CVEs, enrich records, expose API data, connect to endpoint telemetry, and feed compliance dashboards. The convenience is real, but the price is context collapse. A kernel.org issue, an Office remote-code-execution flaw, a third-party library bug, and a firmware advisory can all appear in the same visual language.
That is efficient for reporting and dangerous for decision-making. The source of a CVE determines who fixes it, how it is deployed, what systems are affected, and whether compensating controls make sense. CVE-2026-43305 should be routed to Linux platform owners, endpoint engineering teams managing Linux hardware, and administrators responsible for AMD-based Linux images.
The Microsoft angle is therefore less about culpability and more about visibility. If a Windows-oriented tool brings this to your attention, treat that as a useful signal. Just do not let the signal obscure the actual component.
The Patch Is Simple Because the Failure Was Architectural
A one-flag fix can sound trivial, but it addresses a design smell: duplicated decision logic. If the code asks “do I need the lock?” in one place and later asks “do I need to unlock?” in another, the two answers must never diverge. The safest way to guarantee that is to compute the decision once and carry it forward.That is what the fix does, according to the CVE description. It stores whether the lock should be used and then uses that stored value for the unlock decision. This is not merely tidier code; it reduces the chance that future feature additions will update one branch and forget the other.
Kernel display code is especially vulnerable to this kind of drift because features accrete. A new panel feature, a new ASIC generation, a new replay mode, a new fast path, or a new hardware lock requirement may be added for legitimate reasons. Each addition can widen the gap between originally symmetrical paths.
The lesson for developers is familiar but worth repeating: in low-level systems code, state transitions should be paired by construction wherever possible. If the lock condition and unlock condition are independently re-evaluated, the code is inviting time, refactoring, and feature flags to break the contract.
Practical Exposure Is Narrower Than the CVE Name Suggests
The phrase “Linux kernel vulnerability” can sound universal, but this one is not. The bug is in AMD display code. It requires a path where the relevant AMD display driver logic is present and exercised. The record specifically mentions the fast path and ASICs without FAMS support.That makes exposure hardware- and configuration-dependent. A Linux server using an Intel iGPU or NVIDIA GPU is not the obvious target population. A headless AMD server not using the affected display path may also be outside practical exposure. A laptop with an AMD APU and an internal eDP panel is a more plausible candidate.
There is also a difference between installed code and reachable code. Many kernels include drivers for hardware that is not present. Vulnerability scanners sometimes flag by package version rather than by runtime hardware path, which can overstate risk. Conversely, a user with an affected AMD laptop may not see the finding at all if their scanner lacks kernel-driver granularity.
The best response is not to debate the CVE abstractly. Identify AMD Linux endpoints, confirm kernel advisory status, deploy vendor updates, and reboot. If the systems are high-availability workstations or kiosks, test the kernel update against the display configurations users actually run.
The Fix Matters Most Where Linux Is a Desktop, Not a Server
Linux vulnerability coverage often assumes servers first. That instinct is understandable: Linux dominates infrastructure, and remote server risk drives many patching programs. CVE-2026-43305 flips the emphasis back toward the Linux desktop.Display-driver hangs matter most where display state changes matter. That means laptops waking and sleeping, workstations changing monitors, docking stations renegotiating links, high-refresh panels shifting modes, and power-saving features activating during idle or presentation use. The affected code is part of the machinery that makes a graphical Linux session tolerable on modern AMD hardware.
That should interest WindowsForum’s enthusiast audience as well. AMD laptops and handhelds have made Linux graphics support more mainstream, especially among users experimenting with gaming distributions, development environments, and lightweight desktop setups. Stability bugs in the display stack directly affect whether those systems feel polished or fragile.
For IT, the rise of Linux desktops in engineering organizations makes these bugs more than hobbyist material. A developer workstation that hard-hangs twice a week is not just annoying; it is lost time, support load, and a reason users lose confidence in managed platform standards.
The Scanner Row Needs Human Translation
If CVE-2026-43305 appears in a vulnerability report, the worst response is to paste the row into a ticket with no interpretation. The second-worst response is to close it because NVD has not scored it yet. This is a case where a short human translation saves everyone time.The translation should say that the issue is a Linux kernel AMD display-driver hang fixed upstream and in stable commits, with applicability limited to systems using the affected AMD display path. It should say that there is no current public indication, from the supplied record, of remote code execution or privilege escalation. It should say that remediation is through Linux kernel updates from the relevant distribution, followed by a reboot.
That level of specificity helps desktop engineering teams act without turning every CVE into a fire drill. It also helps security teams avoid the false precision of severity scores. A no-score CVE can still be operationally important, and a scored CVE can still be irrelevant to your environment.
The central question for administrators is not whether the CVE sounds scary. It is whether the vulnerable code runs on machines where a hang would matter.
The Concrete Read for AMD Linux Estates
CVE-2026-43305 is a reminder that graphics reliability and security maintenance now belong in the same operational conversation. The fix is small, the affected path is specific, and the available record does not justify panic. But the bug sits in a privileged kernel driver on hardware that many users actually touch all day.- Administrators should treat CVE-2026-43305 as a Linux kernel AMD display-driver availability issue, not as a Windows graphics vulnerability.
- The most relevant systems are Linux desktops, laptops, workstations, or specialized endpoints using AMD display hardware and affected kernel builds.
- The remediation path is to install the vendor-provided Linux kernel update that includes the upstream stable fix and then reboot into that kernel.
- NVD’s lack of a CVSS score should not be mistaken for proof that the bug is harmless or proof that it is urgent.
- Vulnerability teams should check hardware and runtime applicability before escalating scanner findings across mixed Windows and Linux fleets.
- Users seeing AMD Linux display hangs around panel power features, display updates, docking, or refresh behavior should prioritize kernel updates before chasing higher-level desktop environment causes.
Source: NVD / Linux Kernel Security Update Guide - Microsoft Security Response Center