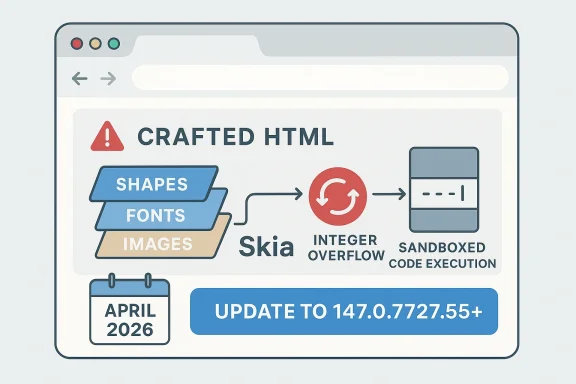
Google’s disclosure of CVE-2026-5870 is the latest reminder that browser security failures still cluster around the same dangerous pattern: a memory-safety bug in a shared graphics stack, reachable from a web page, with code execution possible inside Chrome’s sandbox. Microsoft’s Security Update Guide says the issue affects Google Chrome prior to 147.0.7727.55 and describes it as an integer overflow in Skia that can be triggered by a crafted HTML page. The timing matters because the record was published on April 8, 2026, and the fix lands in a release line that enterprises are already tracking for a broader April patch cycle.
Skia is one of those browser components that most users never notice, which is exactly why flaws in it are so important. It is Chromium’s 2D graphics engine, used for rendering text, shapes, images, and composited page content, and it sits in a part of the browser that handles highly complex, attacker-controlled input at scale. When a flaw in Skia is reachable through HTML, the attack surface is not niche at all; it is the ordinary web itself. That makes graphics bugs especially attractive to exploit developers, because they often offer a path from simple page delivery to memory corruption.
This is not the first time Skia has appeared in Chromium’s security notes. Google’s March 2026 stable update for Chrome 146 included a high-severity integer overflow in Skia as one of the security fixes, and a separate March update listed a heap buffer overflow in Skia as well. In other words, Skia has already been a repeated pressure point in the browser’s attack surface this year, suggesting that image and layout parsing paths continue to be a high-value target.
The new CVE fits that broader pattern. Google says the flaw allowed remote code execution inside a sandbox through a crafted HTML page, which is the classic Chromium security model: attackers may not get immediate full system compromise, but sandboxed code execution is often enough to start a multi-bug chain. Once an attacker can execute code in a renderer or similar constrained process, the next step is usually privilege escalation, sandbox escape, or credential theft through a chained exploit.
Microsoft’s appearance in the story is not incidental. For Chromium-derived issues, Microsoft often mirrors the upstream security condition in the Microsoft Security Update Guide so Edge administrators can see when Chromium fixes have been inherited downstream. Microsoft’s own Edge update documentation also makes clear that Edge’s stable, beta, dev, and canary channels are maintained through an update-policy framework, which is why enterprise admins watch Chromium CVEs even when they technically “belong” to Google Chrome.
The practical effect is simple: a Chrome bug becomes an Edge consideration, and an Edge consideration becomes a patch management problem. That has been the steady rhythm of Chromium security for years, but April 2026 stands out because so many browser issues are landing close together, all fixed in the same Chrome 147.0.7727.55 baseline. For defenders, that compresses the window for triage and increases the cost of delay.
The user-facing description is blunt: a remote attacker can execute arbitrary code inside a sandbox via a crafted HTML page. That is a serious statement even without a CVSS score from NVD yet, because it tells defenders two things at once. First, the exploit is reachable remotely through web content, and second, the browser’s own isolation boundary is not the end of the story. In modern Chromium exploitation, “inside a sandbox” is often the opening act, not the finale.
In graphics code, the risk is magnified by the variety of content the browser must accept. Fonts, paths, bitmap dimensions, transform matrices, color tables, clipping regions, and compositing metadata all involve values that can be parsed from web content or derived from it. That makes Skia a natural place for subtle arithmetic bugs to hide, especially when optimization, cross-platform support, and performance constraints all push code toward compact, high-speed implementations.
The short version is that an integer overflow is not merely a math mistake. In a browser graphics pipeline, it can become a trust boundary failure between untrusted web content and privileged rendering logic. That is why the Chrome team labeled the issue High even before NVD assigned its own score.
The cadence matters because Chrome’s early stable releases often preview the eventual stable baseline. That creates a narrow but important gap where a small percentage of users may already have the fix while the bulk of the fleet remains on the prior version. For large organizations, that gap can become a false sense of progress if patch verification is based on “some devices updated” rather than “all managed devices updated.”
This is particularly important for managed Windows environments, where update deferral, maintenance windows, and policy-driven staging can leave endpoints behind the public release for days or weeks. In a crowded April patch window, that delay can be enough for opportunistic exploitation or for attackers to preposition against lagging fleets. The safer assumption is that browsers are part of the critical patch set, not a discretionary update category.
It is also a reminder that Chrome patching is not isolated from the rest of the Chromium ecosystem. When Google fixes a bug in Chrome, downstream channels like Edge are often watching the same code path and preparing their own release notes or update validation. That is why the CVE is already visible in Microsoft’s guidance even though the originating fix is Google’s.
Chrome’s recent history underscores the point. A heap buffer overflow in Skia was already part of the March 2026 stable update cycle, and earlier Skia-related issues also appeared in Google’s release notes. When the same subsystem shows up repeatedly, it often signals not one isolated bug but a class of boundary-checking problems that remain difficult to eliminate completely.
The broader implication is that browser vendors cannot treat graphics code as a “low-risk” subsystem. It is actually a frequent source of exploit primitives because so much of the web depends on rendering. For defenders, the lesson is that seemingly mundane rendering updates deserve the same urgency as JavaScript engine flaws or memory corruption in the media stack.
That is why the phrase crafted HTML page should not be minimized. It means the attacker does not need a malicious file format, a plugin, or a privileged local component. In many cases, a single link, ad slot, or compromised webpage can be enough to trigger the vulnerable path.
That is an important distinction for Windows environments. Many organizations standardize on Edge while still relying on Chromium compatibility for internal apps, and some also allow Chrome for specific workflows. A vulnerability like CVE-2026-5870 therefore affects both the browser users see and the patch source of truth admins consult.
The Microsoft Edge update-policy documentation reinforces that browser deployment is managed through policy, channel selection, and staged rollout. Those controls are useful for stability, but they also mean that a fleet may stay behind the upstream fix if administrators do not deliberately accelerate it. In other words, patch policy can become patch latency.
For smaller organizations, the risk is different but no less real. They may not have complex test rings, but they also may not have central visibility into browser versions. In that case, the main challenge is simply knowing which endpoints are still below 147.0.7727.55 and making browser updates part of routine incident hygiene.
That makes CVE-2026-5870 a probable component in a chain rather than necessarily the final payload. By itself, it may enable code execution in a constrained process. Chained with a separate renderer escape, logic flaw, or OS-level privilege issue, it could become part of a full compromise path. That is why even “sandboxed” browser RCEs are treated with urgency by serious defenders.
Another subtle point is that browser sandboxes evolve. The stronger the sandbox, the harder it may be to turn one bug into a full device compromise. But stronger sandboxing does not erase the value of the initial foothold; it simply forces attackers to chain more bugs. That is good for defenders, but it does not reduce the need to patch quickly.
The safest interpretation is that CVE-2026-5870 should be treated as a high-priority browser memory-corruption issue with real exploit potential, even if public details remain sparse. The lack of a finalized NVD score does not make the issue less relevant; it only means defenders should rely on the vendor guidance that already exists.
The same pattern appears repeatedly in Microsoft’s update notes for Edge. Microsoft often states that its release incorporates the latest Chromium security updates, which is the company’s way of telling admins that the upstream issue has been folded into the downstream package. For organizations that manage both Chrome and Edge, this means version tracking must happen per browser, not just per vulnerability ID.
This is also why security teams should resist the temptation to treat browser CVEs as duplicates. The vulnerability may be shared, but the deployment realities are not. Extension inventories, group policies, update rings, and platform-specific packaging can all create different exposure windows between Chrome and Edge.
The broader competitive implication is that browser security has become part of platform trust. Google’s release cadence influences Microsoft’s security guidance, and Microsoft’s visibility gives the issue enterprise weight. That is the Chromium ecosystem in 2026: one codebase, multiple products, one shared security burden.
Administrators should verify the browser version on managed endpoints and look for anything below 147.0.7727.55 in Chrome. For Edge environments, the relevant check is whether the installed release has incorporated the same Chromium fix, which Microsoft’s Security Update Guide is intended to clarify. This is the kind of update where version verification is more important than relying on auto-update optimism.
For home users, the advice is simpler: update Chrome immediately and restart if prompted. The browser cannot protect you from a vulnerability that is still sitting in the installed version, and waiting for a convenient moment is exactly how exploitation windows stay open.
It is also worth watching whether more details emerge about the exploitability of the Skia path. Many Chromium bugs begin as isolated memory-safety findings and later reveal themselves as part of a larger exploitation toolkit. If that happens here, the urgency will only increase, because code execution in a sandbox is already enough to motivate coordinated defense.
Source: NVD / Chromium Security Update Guide - Microsoft Security Response Center
 Background
Background
Skia is one of those browser components that most users never notice, which is exactly why flaws in it are so important. It is Chromium’s 2D graphics engine, used for rendering text, shapes, images, and composited page content, and it sits in a part of the browser that handles highly complex, attacker-controlled input at scale. When a flaw in Skia is reachable through HTML, the attack surface is not niche at all; it is the ordinary web itself. That makes graphics bugs especially attractive to exploit developers, because they often offer a path from simple page delivery to memory corruption.This is not the first time Skia has appeared in Chromium’s security notes. Google’s March 2026 stable update for Chrome 146 included a high-severity integer overflow in Skia as one of the security fixes, and a separate March update listed a heap buffer overflow in Skia as well. In other words, Skia has already been a repeated pressure point in the browser’s attack surface this year, suggesting that image and layout parsing paths continue to be a high-value target.
The new CVE fits that broader pattern. Google says the flaw allowed remote code execution inside a sandbox through a crafted HTML page, which is the classic Chromium security model: attackers may not get immediate full system compromise, but sandboxed code execution is often enough to start a multi-bug chain. Once an attacker can execute code in a renderer or similar constrained process, the next step is usually privilege escalation, sandbox escape, or credential theft through a chained exploit.
Microsoft’s appearance in the story is not incidental. For Chromium-derived issues, Microsoft often mirrors the upstream security condition in the Microsoft Security Update Guide so Edge administrators can see when Chromium fixes have been inherited downstream. Microsoft’s own Edge update documentation also makes clear that Edge’s stable, beta, dev, and canary channels are maintained through an update-policy framework, which is why enterprise admins watch Chromium CVEs even when they technically “belong” to Google Chrome.
The practical effect is simple: a Chrome bug becomes an Edge consideration, and an Edge consideration becomes a patch management problem. That has been the steady rhythm of Chromium security for years, but April 2026 stands out because so many browser issues are landing close together, all fixed in the same Chrome 147.0.7727.55 baseline. For defenders, that compresses the window for triage and increases the cost of delay.
What CVE-2026-5870 Actually Is
At its core, CVE-2026-5870 is an integer overflow in Skia. In security terms, that usually means arithmetic inside a length, offset, or allocation calculation wraps around to an unexpected value, causing the browser to reserve too little memory, index the wrong region, or mis-handle a buffer boundary. In a graphics engine, that kind of bug can quickly turn into corruption because rendering code constantly transforms attacker-influenced sizes, coordinates, and data structures.The user-facing description is blunt: a remote attacker can execute arbitrary code inside a sandbox via a crafted HTML page. That is a serious statement even without a CVSS score from NVD yet, because it tells defenders two things at once. First, the exploit is reachable remotely through web content, and second, the browser’s own isolation boundary is not the end of the story. In modern Chromium exploitation, “inside a sandbox” is often the opening act, not the finale.
Why integer overflows matter
Integer overflows can look boring on a code review, but they are one of the most reliable ways to create memory corruption. A size calculation that wraps can make a large object appear small, or can make a copy operation believe it is safe when it is not. Once the browser trusts the wrong size, the attacker may gain read/write primitives that were never meant to exist.In graphics code, the risk is magnified by the variety of content the browser must accept. Fonts, paths, bitmap dimensions, transform matrices, color tables, clipping regions, and compositing metadata all involve values that can be parsed from web content or derived from it. That makes Skia a natural place for subtle arithmetic bugs to hide, especially when optimization, cross-platform support, and performance constraints all push code toward compact, high-speed implementations.
The short version is that an integer overflow is not merely a math mistake. In a browser graphics pipeline, it can become a trust boundary failure between untrusted web content and privileged rendering logic. That is why the Chrome team labeled the issue High even before NVD assigned its own score.
How the Bug Fits Chrome’s April 2026 Security Cycle
Chrome 147’s arrival in stable channel updates has been unfolding in stages. Google issued an early stable update on April 1, 2026, then the full stable channel update that included the security fixes landed in the release stream shortly afterward. The version cited in the CVE, 147.0.7727.55, is the anchor point administrators should use when checking whether a device has moved beyond the vulnerable build.The cadence matters because Chrome’s early stable releases often preview the eventual stable baseline. That creates a narrow but important gap where a small percentage of users may already have the fix while the bulk of the fleet remains on the prior version. For large organizations, that gap can become a false sense of progress if patch verification is based on “some devices updated” rather than “all managed devices updated.”
The significance of 147.0.7727.55
The exact build number is more than an implementation detail. For browser security, version gates are the practical line between “vulnerable” and “remediated,” especially when upstream vendors publish the fix before downstream products confirm ingestion. The Chrome version cited by the CVE therefore becomes the minimum safe build, and anything below it should be treated as exposed until proven otherwise.This is particularly important for managed Windows environments, where update deferral, maintenance windows, and policy-driven staging can leave endpoints behind the public release for days or weeks. In a crowded April patch window, that delay can be enough for opportunistic exploitation or for attackers to preposition against lagging fleets. The safer assumption is that browsers are part of the critical patch set, not a discretionary update category.
It is also a reminder that Chrome patching is not isolated from the rest of the Chromium ecosystem. When Google fixes a bug in Chrome, downstream channels like Edge are often watching the same code path and preparing their own release notes or update validation. That is why the CVE is already visible in Microsoft’s guidance even though the originating fix is Google’s.
Why Skia Keeps Reappearing
Skia is a foundational library, and foundational libraries are where attackers get the most leverage. They are used everywhere, they are heavily optimized, and they must accept complicated inputs from hostile environments without slowing the browser down. That combination makes them particularly susceptible to arithmetic mistakes, especially when dimensions and offsets are derived from content that was never supposed to be trusted.Chrome’s recent history underscores the point. A heap buffer overflow in Skia was already part of the March 2026 stable update cycle, and earlier Skia-related issues also appeared in Google’s release notes. When the same subsystem shows up repeatedly, it often signals not one isolated bug but a class of boundary-checking problems that remain difficult to eliminate completely.
A recurring attack surface
Graphics engines are attractive because they sit between content parsing and visual output, which means they process lots of attacker-controlled data under time pressure. They also have to balance correctness against performance, and that tension can introduce subtle bugs in signed and unsigned arithmetic, allocation calculations, and clipping logic. Integer overflow problems are especially treacherous here because they may not crash immediately; they may only corrupt state under specific input shapes.The broader implication is that browser vendors cannot treat graphics code as a “low-risk” subsystem. It is actually a frequent source of exploit primitives because so much of the web depends on rendering. For defenders, the lesson is that seemingly mundane rendering updates deserve the same urgency as JavaScript engine flaws or memory corruption in the media stack.
That is why the phrase crafted HTML page should not be minimized. It means the attacker does not need a malicious file format, a plugin, or a privileged local component. In many cases, a single link, ad slot, or compromised webpage can be enough to trigger the vulnerable path.
What Microsoft’s Inclusion Means for Edge
Microsoft surfacing the CVE in its Security Update Guide is a strong signal for enterprise administrators. It means the Chromium-originated issue is relevant not just to Chrome users but to Microsoft Edge deployments that consume the upstream Chromium codebase. In practice, that turns a Google browser advisory into a downstream patch-tracking event across Windows fleets.That is an important distinction for Windows environments. Many organizations standardize on Edge while still relying on Chromium compatibility for internal apps, and some also allow Chrome for specific workflows. A vulnerability like CVE-2026-5870 therefore affects both the browser users see and the patch source of truth admins consult.
Enterprise patching reality
Enterprises rarely patch browsers instantly, even when the risk is clear. They need to test extensions, validate line-of-business sites, and ensure security tooling still behaves correctly after a browser update. That is understandable, but it also means the vulnerable interval is often longer than anyone would prefer, especially when the browser bug is remotely reachable through ordinary HTML.The Microsoft Edge update-policy documentation reinforces that browser deployment is managed through policy, channel selection, and staged rollout. Those controls are useful for stability, but they also mean that a fleet may stay behind the upstream fix if administrators do not deliberately accelerate it. In other words, patch policy can become patch latency.
For smaller organizations, the risk is different but no less real. They may not have complex test rings, but they also may not have central visibility into browser versions. In that case, the main challenge is simply knowing which endpoints are still below 147.0.7727.55 and making browser updates part of routine incident hygiene.
The Real Exploitation Story
The publicly described impact says remote code execution is possible inside the sandbox, and that wording matters. A sandboxed renderer compromise is not the same as full device takeover, but it is still a meaningful foothold because browser exploit chains often progress in stages. An attacker who gets code execution in one process may then look for a second bug to escape the sandbox or elevate privileges.That makes CVE-2026-5870 a probable component in a chain rather than necessarily the final payload. By itself, it may enable code execution in a constrained process. Chained with a separate renderer escape, logic flaw, or OS-level privilege issue, it could become part of a full compromise path. That is why even “sandboxed” browser RCEs are treated with urgency by serious defenders.
Why sandboxed RCE still matters
The sandbox is designed to limit blast radius, not to make exploitation harmless. If a sandboxed browser process can be directed to run attacker code, that code may still interact with the page, steal session data present in-process, or stage follow-on actions. In enterprise settings, that can be enough to compromise a user session, exfiltrate tokens, or prepare a second-stage attack.Another subtle point is that browser sandboxes evolve. The stronger the sandbox, the harder it may be to turn one bug into a full device compromise. But stronger sandboxing does not erase the value of the initial foothold; it simply forces attackers to chain more bugs. That is good for defenders, but it does not reduce the need to patch quickly.
The safest interpretation is that CVE-2026-5870 should be treated as a high-priority browser memory-corruption issue with real exploit potential, even if public details remain sparse. The lack of a finalized NVD score does not make the issue less relevant; it only means defenders should rely on the vendor guidance that already exists.
Chrome, Edge, and the Chromium Supply Chain
One reason Chromium vulnerabilities create so much noise is that they propagate through the browser ecosystem. Chrome is the first stop, but not the only stop. Microsoft Edge, and any other Chromium-based browser, has to ingest the fix and then ship its own validated build. That makes the upstream CVE only half the story; the downstream patch adoption date matters just as much.The same pattern appears repeatedly in Microsoft’s update notes for Edge. Microsoft often states that its release incorporates the latest Chromium security updates, which is the company’s way of telling admins that the upstream issue has been folded into the downstream package. For organizations that manage both Chrome and Edge, this means version tracking must happen per browser, not just per vulnerability ID.
What this means in practice
If a company uses Chrome, the fix target is obvious: get to 147.0.7727.55 or later. If it uses Edge, the practical question is whether the installed Edge build has already absorbed the Chromium fix, which may not match the Chrome version number exactly. That downstream translation layer is why Microsoft publishes its own guidance rather than telling customers to read Chrome’s blog and infer the rest.This is also why security teams should resist the temptation to treat browser CVEs as duplicates. The vulnerability may be shared, but the deployment realities are not. Extension inventories, group policies, update rings, and platform-specific packaging can all create different exposure windows between Chrome and Edge.
The broader competitive implication is that browser security has become part of platform trust. Google’s release cadence influences Microsoft’s security guidance, and Microsoft’s visibility gives the issue enterprise weight. That is the Chromium ecosystem in 2026: one codebase, multiple products, one shared security burden.
How Administrators Should Think About Priority
The most important operational decision is not whether the issue is severe; Google has already answered that by labeling it High. The real question is how fast to move, and the answer should be: as fast as change control allows. A browser flaw that is remotely reachable through a crafted HTML page belongs near the top of any patch queue, particularly when it affects both consumer and enterprise browsers.Administrators should verify the browser version on managed endpoints and look for anything below 147.0.7727.55 in Chrome. For Edge environments, the relevant check is whether the installed release has incorporated the same Chromium fix, which Microsoft’s Security Update Guide is intended to clarify. This is the kind of update where version verification is more important than relying on auto-update optimism.
A practical response order
- Inventory which systems have Chrome or Edge installed.
- Check version numbers against the fixed Chrome baseline and downstream Edge guidance.
- Accelerate rollout in higher-risk groups such as executives, developers, and web-heavy users.
- Re-test critical internal sites and extension behavior after update.
- Document exceptions so no machine remains permanently behind.
For home users, the advice is simpler: update Chrome immediately and restart if prompted. The browser cannot protect you from a vulnerability that is still sitting in the installed version, and waiting for a convenient moment is exactly how exploitation windows stay open.
Strengths and Opportunities
The good news is that the ecosystem around this CVE is mature enough to respond quickly. Google has already shipped the fix, Microsoft has already surfaced the downstream relevance, and the affected build number is precise enough for clean remediation. That makes this a manageable security event, provided organizations treat it with real urgency.- Clear fixed version: the vulnerable boundary is explicit at 147.0.7727.55.
- Rapid vendor signaling: Google and Microsoft have both acknowledged the issue.
- Straightforward remediation: browser update and restart are the core steps.
- Strong policy tooling: enterprise administrators can enforce rollout through browser management policies.
- Low ambiguity about exposure: the attack path is remote and web-delivered.
- Good opportunity to validate patch hygiene: teams can use this CVE to audit browser inventory processes.
- Potential to tighten update SLAs: incidents like this justify faster browser update windows.
Risks and Concerns
The biggest concern is the familiar one: there is usually a gap between a vendor patch and real-world adoption. In that gap, a remotely reachable browser flaw can become a practical exploitation target, especially if proof-of-concept details or exploit chains emerge later.- Delayed endpoint updates can leave large fleets exposed.
- Sandboxed RCE may be chained with other bugs for deeper compromise.
- Edge and Chrome version drift can create confusing patch status.
- Users may postpone restarts, keeping vulnerable code loaded longer.
- Attackers can deliver HTML remotely, lowering the barrier to attack.
- Graphics subsystems are recurring targets, so adjacent bugs may follow.
- NVD scores may lag vendor urgency, causing false reassurance.
Looking Ahead
The next thing to watch is how quickly downstream Chromium browsers confirm the fix in their own release trains. Microsoft’s Security Update Guide is the key place for that confirmation, but the broader browser market will likely mirror the same rhythm because so many products now depend on the same upstream codebase. As with previous Chromium issues, the real story will be the pace of adoption, not just the disclosure itself.It is also worth watching whether more details emerge about the exploitability of the Skia path. Many Chromium bugs begin as isolated memory-safety findings and later reveal themselves as part of a larger exploitation toolkit. If that happens here, the urgency will only increase, because code execution in a sandbox is already enough to motivate coordinated defense.
- Edge release confirmation for the Chromium fix.
- Any exploit reporting that suggests active abuse.
- Additional Skia advisories in future Chrome updates.
- Enterprise patch adoption rates across managed fleets.
- Whether Chrome 147’s rollout accelerates after the CVE.
Source: NVD / Chromium Security Update Guide - Microsoft Security Response Center