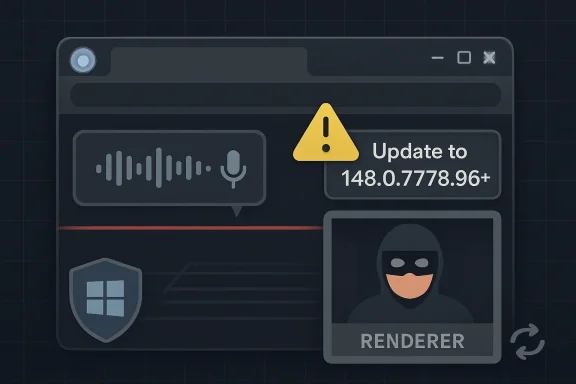
CVE-2026-7960 is a medium-severity Chromium vulnerability disclosed on May 6, 2026, affecting Google Chrome before version 148.0.7778.96, where a race condition in the browser’s Speech component could let a remote attacker with renderer compromise read sensitive process memory through crafted HTML. That phrasing sounds narrow, almost reassuring, but it lands in the most uncomfortable place in modern browser security: the space after the first bug has already succeeded. The vulnerability is not a standalone “visit a page and lose the machine” nightmare; it is a reminder that once the renderer is compromised, every imperfect boundary inside the browser becomes a second chance for the attacker. For Windows users and administrators, the practical lesson is blunt: Chromium patch cadence is now infrastructure hygiene, not consumer-app housekeeping.
The most important words in the description are not “Race in Speech.” They are “who had compromised the renderer process.” CVE-2026-7960 is not presented as the first domino in an attack chain; it is a bug that becomes useful after an attacker has already found a way into Chrome’s sandboxed rendering environment.
That distinction matters because browser vulnerability severity often collapses several very different risk profiles into a single label. A remote-code-execution flaw reachable from a webpage is not the same thing as an information disclosure flaw that requires a prior renderer compromise. Yet attackers do not experience vulnerabilities as isolated CVE entries. They experience them as components in a chain.
In that chain, a memory disclosure can be extremely valuable. Modern browsers are full of mitigations that rely on secrecy, compartmentalization, and process boundaries. If a bug exposes memory that was supposed to remain private, it can help defeat address-space randomization, leak tokens or data fragments, or turn an unreliable exploit into a dependable one.
That is why “Medium” should not be read as “ignore until next month.” It should be read as “this is not the loudest alarm in the release, but it belongs to the class of bugs attackers often pair with louder ones.” In a desktop browser, especially one deployed across a managed Windows fleet, that is enough to demand prompt patching.
But in browser security, “feature” is just another word for exposed code. The modern browser is not a document viewer; it is a permissions broker, media runtime, cryptographic client, app platform, device abstraction layer, and policy enforcement engine. Every subsystem that handles asynchronous events, device permissions, web-facing APIs, or cross-process messaging becomes part of the attack surface.
A race condition in that context is particularly unsurprising. Speech features are inherently event-driven. Audio capture, recognition callbacks, permission prompts, renderer-to-browser communication, and state transitions all need to happen in a carefully synchronized way. If two operations can observe or mutate shared state in the wrong order, the result can be a window where memory is read when it should not be, or where an object’s lifetime is misunderstood.
That is the essence of CWE-362, the weakness category assigned here: concurrent execution using a shared resource with improper synchronization. It is a dry taxonomy entry for a familiar engineering failure. The code assumes a sequence. Reality provides overlap.
The lesson is not that speech features are uniquely dangerous. It is that every new browser capability carries the same old burdens: lifecycle management, synchronization, privilege separation, and hostile input. The web platform keeps expanding, and attackers keep hunting the seams where that expansion outruns defensive design.
The better answer is that CVE-2026-7960 should be evaluated as part of the release cluster. Browser releases increasingly carry dozens, sometimes more than a hundred, security corrections across the stack. Some are critical, some high, some medium, and many are deliberately under-described until users have had time to update. The advisory model is intentionally incomplete at publication time because the alternative is handing attackers a roadmap before the population is patched.
Google’s practice of restricting bug details until a majority of users are updated is often frustrating for defenders. Security teams want root cause, affected code paths, proof-of-concept behavior, exploitability notes, and telemetry guidance. Instead, they often get a component name, a severity rating, and a version number.
That opacity is not negligence. It is a trade-off. Publicly documenting the exact race window in a web-exposed browser component on day one would improve defender understanding, but it would also shorten attacker development time. The modern browser patch note is therefore less like a postmortem and more like an evacuation notice: here is the building, here is the exit, details later.
For home users, that means “restart Chrome” is still the only meaningful advice. For IT teams, it means version compliance matters more than interpretive debate. If endpoints are below the fixed build, they are carrying known exposure.
Chrome’s multi-process architecture is designed around the assumption that renderers are risky. They parse untrusted web content, execute JavaScript, process complex formats, and interact with a massive API surface. The sandbox exists because the renderer is expected to be the place where bad things first happen.
If an attacker already has arbitrary code execution in a renderer, the next challenge is escaping constraints or extracting value despite them. Sometimes that means a sandbox escape. Sometimes it means stealing data accessible to the renderer. Sometimes it means using information disclosure to make a subsequent exploit more reliable. CVE-2026-7960 sits in that post-compromise utility zone.
The CVSS vector assigned by CISA’s ADP enrichment captures this tension. Network attack vector, high attack complexity, no privileges required, user interaction required, unchanged scope, high confidentiality impact, no integrity impact, no availability impact. That produces a medium score, but the “high confidentiality” component is the part defenders should notice.
A crafted HTML page is still the delivery mechanism. User interaction is still required, but that can be as mundane as visiting a malicious page or being redirected through a compromised site, depending on the exploit chain around it. The fact that the attacker must first compromise the renderer does not make the bug irrelevant; it tells us where it fits.
Defenses such as address-space layout randomization are designed to make memory locations unpredictable. Object lifetime protections, heap hardening, site isolation, pointer integrity checks, and sandbox boundaries all increase the cost of building reliable exploit chains. A memory disclosure can reduce that cost.
In a browser context, “potentially sensitive information from process memory” can mean many things, and the public description does not give us enough to make precise claims about what CVE-2026-7960 leaks. It may be a narrow read. It may be difficult to exploit consistently. It may only expose data under certain timing conditions. That uncertainty is exactly why patching is preferable to speculation.
Race conditions also tend to be capricious. They can be hard to trigger in a lab and still practical for a motivated attacker with enough attempts, device fingerprinting, and environmental tuning. The web is a convenient delivery system for repeated attempts because the attacker controls timing, page behavior, script orchestration, and user flow.
The uncomfortable truth is that exploit reliability is a product feature for attackers. Anything that leaks process memory can become part of that product, even if the original CVE never becomes famous.
The user-supplied MSRC entry for CVE-2026-7960 is a good example of how Chromium vulnerabilities now propagate through the Windows security conversation. Microsoft is not necessarily the originator of the bug or the patch, but Edge’s shared engine means the vulnerability becomes relevant to Microsoft’s update ecosystem. In practical fleet terms, “we do not run Google Chrome” is not the same thing as “we are not exposed to Chromium bugs.”
This is one of the underappreciated consequences of Chromium’s dominance. Standardization has benefits: faster fixes, shared hardening, a broad research base, and fewer independent engines for attackers and defenders to model. But it also means a single engine-level class of bug can ripple across Chrome, Edge, Brave, Opera, Vivaldi, Electron-based applications, and embedded browser components on different schedules.
Enterprise administrators therefore need two inventories. The first is the obvious browser inventory: Chrome, Edge, channel, version, update policy, restart status. The second is the embedded Chromium inventory: applications that ship their own runtime, lag behind upstream, or bundle web-rendering components without surfacing the version clearly. CVE-2026-7960 is a Chrome-branded CVE, but the operational lesson is broader than Chrome.
Edge’s update behavior is generally efficient on consumer and unmanaged systems, but enterprise environments can slow it down through policy, maintenance windows, frozen virtual desktop images, application compatibility testing, or simple restart inertia. The patch is not installed in any meaningful sense until the running browser process is on the fixed build.
Administrators should not overread that moment. CPE data is useful for scanners, compliance dashboards, and vulnerability correlation, but it often lags the operational truth of software deployment. If Chrome or a Chromium-based browser is below the fixed version, it is the version that matters first. The CPE is the database’s way of describing the world; the installed binary is the world.
This is especially true for Chromium vulnerabilities because packaging differs across platforms. Chrome on Windows is not deployed like Chromium snaps on Ubuntu. Edge has its own release notes and update mechanisms. Linux distributions may ship Chromium differently, or in some cases replace transitional packages with snaps or downstream-managed builds. Vulnerability management systems have to flatten all of that into machine-readable product strings, and the flattening is never perfect.
The better question for defenders is not whether the NVD CPE is pristine on day one. It is whether their scanners can identify installed browser versions accurately, whether they distinguish running and installed versions, and whether they detect applications that bundle Chromium without registering as Chrome. CPE precision helps, but it does not replace endpoint reality.
In that sense, the prompt’s “Are we missing a CPE here?” is almost accidentally profound. Yes, vulnerability databases are often missing a CPE somewhere. More importantly, most organizations are missing at least one browser-like runtime somewhere.
That is where security teams often lose time. A machine can report that an update is available or staged, while users continue running the vulnerable process for days. Browser windows become workspaces. Tabs become task lists. Users resist restarts not because they are reckless, but because the browser has become the shell for their workday.
Enterprises have tools to force the issue, but they are politically expensive. Aggressive restart enforcement annoys users, interrupts meetings, breaks fragile web apps, and creates help-desk tickets. Lenient enforcement leaves known vulnerabilities alive across the fleet. There is no perfect policy, only a risk decision.
CVE-2026-7960 is not the kind of bug that necessarily justifies panic banners and immediate browser termination in every environment. But the broader Chrome 148 security release may justify a shorter restart grace period than ordinary feature updates. Organizations that already classify browser security updates as high-priority should treat this release accordingly, especially on endpoints used by privileged staff, developers, finance teams, executives, and administrators.
The most mature posture is boring: automatic updates enabled, update deadlines configured, restart prompts enforced with a reasonable countdown, and visibility into stragglers. Browser security is no longer won by heroic incident response. It is won by making the patched state the default state.
This is a recurring problem with component-named browser CVEs. A flaw in “Speech” does not necessarily mean the user must knowingly grant microphone access, speak into a device, or use dictation. It may involve API state, object lifecycle, permission prompts, synthesis paths, recognition setup, or internal plumbing that is reachable before a user thinks of the feature as active. Without bug details, strong claims about mitigations are guesswork.
That does not mean policy controls are useless. Organizations with strict browser baselines should continue limiting unnecessary permissions, blocking risky site capabilities by default, and using allowlists for sensitive APIs. Reducing exposed feature surface is sound defense-in-depth.
But defense-in-depth is not patch management. If the vulnerable version is present, policy controls can at best lower the chance that a specific exploit path works. They cannot give the assurance that the fixed code provides.
Speech is a perfect example because it sits at the intersection of accessibility, productivity, and ambient computing. Voice input helps users who cannot type comfortably. Speech synthesis improves usability. Web apps increasingly expect rich media and device access. None of this is frivolous.
But every step toward a more capable browser also increases the number of state machines inside it. The browser must ask who is allowed to access what, when, under which user gesture, in which frame, from which origin, for how long, and across which process boundary. Race conditions thrive where state machines meet concurrency.
The security model is therefore under constant pressure. It is not enough for a feature to be safe when used normally. It must be safe when initialized twice, canceled midstream, torn down during navigation, triggered from nested frames, interrupted by permission changes, and abused by scripts written specifically to find the one interleaving the programmer did not expect.
That is why browser security will never be “solved” by one sandbox or one memory-safe rewrite or one policy toggle. It is an ongoing negotiation between capability and containment. CVE-2026-7960 is one more negotiation failure, patched before the details become broadly useful.
Patch diffing is not magic, but it is a real discipline. Once a fixed build is available, researchers and attackers can compare changes, look for security-relevant modifications, and infer vulnerability mechanics. Restricted bug trackers slow the process, but they do not stop it. Time favors the side doing the reverse engineering if the defender has not updated.
This is why browser updates have a different tempo from traditional monthly patch cycles. Operating system patching still often moves in scheduled waves because compatibility risk can be high. Browsers, by contrast, are permanently exposed to untrusted content and update on a much faster cadence. Treating Chrome and Edge like ordinary desktop apps is a category error.
The irony is that many organizations now have excellent tooling for operating system patches but weaker discipline around browsers. They can tell you the Windows cumulative update status of every machine, yet struggle to prove which Chrome process version is currently running under every user profile. Attackers do not care which dashboard is more mature.
For CVE-2026-7960, the exposure window begins closing at 148.0.7778.96 and later. The organizations that shrink that window quickly will likely never think about this CVE again. The organizations that let old browser processes linger are volunteering for the long tail.
That routine is the point. Browser CVEs have become too frequent and too interconnected for one-off drama. A mature response is not a war room for every medium-severity bug; it is a system that absorbs these releases quickly without needing a crisis narrative.
Source: NVD / Chromium Security Update Guide - Microsoft Security Response Center
 A Medium Bug With a Post-Compromise Shape
A Medium Bug With a Post-Compromise Shape
The most important words in the description are not “Race in Speech.” They are “who had compromised the renderer process.” CVE-2026-7960 is not presented as the first domino in an attack chain; it is a bug that becomes useful after an attacker has already found a way into Chrome’s sandboxed rendering environment.That distinction matters because browser vulnerability severity often collapses several very different risk profiles into a single label. A remote-code-execution flaw reachable from a webpage is not the same thing as an information disclosure flaw that requires a prior renderer compromise. Yet attackers do not experience vulnerabilities as isolated CVE entries. They experience them as components in a chain.
In that chain, a memory disclosure can be extremely valuable. Modern browsers are full of mitigations that rely on secrecy, compartmentalization, and process boundaries. If a bug exposes memory that was supposed to remain private, it can help defeat address-space randomization, leak tokens or data fragments, or turn an unreliable exploit into a dependable one.
That is why “Medium” should not be read as “ignore until next month.” It should be read as “this is not the loudest alarm in the release, but it belongs to the class of bugs attackers often pair with louder ones.” In a desktop browser, especially one deployed across a managed Windows fleet, that is enough to demand prompt patching.
The Speech Stack Is Another Browser Attack Surface
The Speech component is not the first subsystem most administrators think about when they triage browser risk. JavaScript engines, GPU code, WebRTC, Blink, PDF handling, and media codecs usually get the attention because they have a long public history of high-impact vulnerabilities. Speech feels like a feature: dictation, voice recognition, synthesis, accessibility, convenience.But in browser security, “feature” is just another word for exposed code. The modern browser is not a document viewer; it is a permissions broker, media runtime, cryptographic client, app platform, device abstraction layer, and policy enforcement engine. Every subsystem that handles asynchronous events, device permissions, web-facing APIs, or cross-process messaging becomes part of the attack surface.
A race condition in that context is particularly unsurprising. Speech features are inherently event-driven. Audio capture, recognition callbacks, permission prompts, renderer-to-browser communication, and state transitions all need to happen in a carefully synchronized way. If two operations can observe or mutate shared state in the wrong order, the result can be a window where memory is read when it should not be, or where an object’s lifetime is misunderstood.
That is the essence of CWE-362, the weakness category assigned here: concurrent execution using a shared resource with improper synchronization. It is a dry taxonomy entry for a familiar engineering failure. The code assumes a sequence. Reality provides overlap.
The lesson is not that speech features are uniquely dangerous. It is that every new browser capability carries the same old burdens: lifecycle management, synchronization, privilege separation, and hostile input. The web platform keeps expanding, and attackers keep hunting the seams where that expansion outruns defensive design.
Chrome 148 Is a Security Release Wearing a Version Number
Chrome 148.0.7778.96 is the fixing line for Linux, while Windows and macOS users are also seeing the 148.0.7778.96/97 branch in the stable rollout. The update arrived as part of a broad Chrome 148 stable-channel release that bundled a large number of security fixes, not as a tiny one-CVE hotfix. That matters operationally because administrators may be tempted to ask whether this one medium CVE justifies emergency action.The better answer is that CVE-2026-7960 should be evaluated as part of the release cluster. Browser releases increasingly carry dozens, sometimes more than a hundred, security corrections across the stack. Some are critical, some high, some medium, and many are deliberately under-described until users have had time to update. The advisory model is intentionally incomplete at publication time because the alternative is handing attackers a roadmap before the population is patched.
Google’s practice of restricting bug details until a majority of users are updated is often frustrating for defenders. Security teams want root cause, affected code paths, proof-of-concept behavior, exploitability notes, and telemetry guidance. Instead, they often get a component name, a severity rating, and a version number.
That opacity is not negligence. It is a trade-off. Publicly documenting the exact race window in a web-exposed browser component on day one would improve defender understanding, but it would also shorten attacker development time. The modern browser patch note is therefore less like a postmortem and more like an evacuation notice: here is the building, here is the exit, details later.
For home users, that means “restart Chrome” is still the only meaningful advice. For IT teams, it means version compliance matters more than interpretive debate. If endpoints are below the fixed build, they are carrying known exposure.
The Renderer Requirement Is Not the Comfort It Seems
It is tempting to downgrade concern because CVE-2026-7960 requires a compromised renderer process. That temptation misunderstands how browser attacks are assembled. A renderer compromise is not an exotic precondition in the threat model; it is one of the principal goals of web exploitation.Chrome’s multi-process architecture is designed around the assumption that renderers are risky. They parse untrusted web content, execute JavaScript, process complex formats, and interact with a massive API surface. The sandbox exists because the renderer is expected to be the place where bad things first happen.
If an attacker already has arbitrary code execution in a renderer, the next challenge is escaping constraints or extracting value despite them. Sometimes that means a sandbox escape. Sometimes it means stealing data accessible to the renderer. Sometimes it means using information disclosure to make a subsequent exploit more reliable. CVE-2026-7960 sits in that post-compromise utility zone.
The CVSS vector assigned by CISA’s ADP enrichment captures this tension. Network attack vector, high attack complexity, no privileges required, user interaction required, unchanged scope, high confidentiality impact, no integrity impact, no availability impact. That produces a medium score, but the “high confidentiality” component is the part defenders should notice.
A crafted HTML page is still the delivery mechanism. User interaction is still required, but that can be as mundane as visiting a malicious page or being redirected through a compromised site, depending on the exploit chain around it. The fact that the attacker must first compromise the renderer does not make the bug irrelevant; it tells us where it fits.
Memory Disclosure Is the Grease Between Exploit Stages
Information disclosure vulnerabilities rarely get the same attention as code execution flaws. They lack the cinematic quality of a remote shell. They often do not crash systems, deploy ransomware, or announce themselves in logs. But browser exploit developers have long valued memory leaks because modern exploitation is a battle against uncertainty.Defenses such as address-space layout randomization are designed to make memory locations unpredictable. Object lifetime protections, heap hardening, site isolation, pointer integrity checks, and sandbox boundaries all increase the cost of building reliable exploit chains. A memory disclosure can reduce that cost.
In a browser context, “potentially sensitive information from process memory” can mean many things, and the public description does not give us enough to make precise claims about what CVE-2026-7960 leaks. It may be a narrow read. It may be difficult to exploit consistently. It may only expose data under certain timing conditions. That uncertainty is exactly why patching is preferable to speculation.
Race conditions also tend to be capricious. They can be hard to trigger in a lab and still practical for a motivated attacker with enough attempts, device fingerprinting, and environmental tuning. The web is a convenient delivery system for repeated attempts because the attacker controls timing, page behavior, script orchestration, and user flow.
The uncomfortable truth is that exploit reliability is a product feature for attackers. Anything that leaks process memory can become part of that product, even if the original CVE never becomes famous.
Microsoft Edge Inherits the Chromium Weather
For WindowsForum readers, the Google Chrome version number is only half the story. Microsoft Edge is Chromium-based, and Microsoft tracks Chromium security fixes through its own release and MSRC processes. A Chromium CVE can therefore matter even in organizations that have standardized on Edge and removed Chrome from the managed image.The user-supplied MSRC entry for CVE-2026-7960 is a good example of how Chromium vulnerabilities now propagate through the Windows security conversation. Microsoft is not necessarily the originator of the bug or the patch, but Edge’s shared engine means the vulnerability becomes relevant to Microsoft’s update ecosystem. In practical fleet terms, “we do not run Google Chrome” is not the same thing as “we are not exposed to Chromium bugs.”
This is one of the underappreciated consequences of Chromium’s dominance. Standardization has benefits: faster fixes, shared hardening, a broad research base, and fewer independent engines for attackers and defenders to model. But it also means a single engine-level class of bug can ripple across Chrome, Edge, Brave, Opera, Vivaldi, Electron-based applications, and embedded browser components on different schedules.
Enterprise administrators therefore need two inventories. The first is the obvious browser inventory: Chrome, Edge, channel, version, update policy, restart status. The second is the embedded Chromium inventory: applications that ship their own runtime, lag behind upstream, or bundle web-rendering components without surfacing the version clearly. CVE-2026-7960 is a Chrome-branded CVE, but the operational lesson is broader than Chrome.
Edge’s update behavior is generally efficient on consumer and unmanaged systems, but enterprise environments can slow it down through policy, maintenance windows, frozen virtual desktop images, application compatibility testing, or simple restart inertia. The patch is not installed in any meaningful sense until the running browser process is on the fixed build.
The CPE Oddity Is Less Important Than the Asset Reality
The NVD change history described in the prompt shows a CPE configuration for Google Chrome versions before 148.0.7778.96, with operating system context including Windows, Linux, and macOS. It also includes the familiar “Are we missing a CPE?” prompt that appears when the vulnerability database is still being enriched or may not perfectly describe affected platforms.Administrators should not overread that moment. CPE data is useful for scanners, compliance dashboards, and vulnerability correlation, but it often lags the operational truth of software deployment. If Chrome or a Chromium-based browser is below the fixed version, it is the version that matters first. The CPE is the database’s way of describing the world; the installed binary is the world.
This is especially true for Chromium vulnerabilities because packaging differs across platforms. Chrome on Windows is not deployed like Chromium snaps on Ubuntu. Edge has its own release notes and update mechanisms. Linux distributions may ship Chromium differently, or in some cases replace transitional packages with snaps or downstream-managed builds. Vulnerability management systems have to flatten all of that into machine-readable product strings, and the flattening is never perfect.
The better question for defenders is not whether the NVD CPE is pristine on day one. It is whether their scanners can identify installed browser versions accurately, whether they distinguish running and installed versions, and whether they detect applications that bundle Chromium without registering as Chrome. CPE precision helps, but it does not replace endpoint reality.
In that sense, the prompt’s “Are we missing a CPE here?” is almost accidentally profound. Yes, vulnerability databases are often missing a CPE somewhere. More importantly, most organizations are missing at least one browser-like runtime somewhere.
The Patch Is Simple; The Restart Is the Hard Part
Browser patching has become technically easy and operationally annoying. Chrome and Edge are designed to update frequently. The binaries arrive quietly, policies can steer the channel, and most users never think about installers. Yet the last mile remains stubborn: the browser must restart, sessions must close, and long-lived processes must die.That is where security teams often lose time. A machine can report that an update is available or staged, while users continue running the vulnerable process for days. Browser windows become workspaces. Tabs become task lists. Users resist restarts not because they are reckless, but because the browser has become the shell for their workday.
Enterprises have tools to force the issue, but they are politically expensive. Aggressive restart enforcement annoys users, interrupts meetings, breaks fragile web apps, and creates help-desk tickets. Lenient enforcement leaves known vulnerabilities alive across the fleet. There is no perfect policy, only a risk decision.
CVE-2026-7960 is not the kind of bug that necessarily justifies panic banners and immediate browser termination in every environment. But the broader Chrome 148 security release may justify a shorter restart grace period than ordinary feature updates. Organizations that already classify browser security updates as high-priority should treat this release accordingly, especially on endpoints used by privileged staff, developers, finance teams, executives, and administrators.
The most mature posture is boring: automatic updates enabled, update deadlines configured, restart prompts enforced with a reasonable countdown, and visibility into stragglers. Browser security is no longer won by heroic incident response. It is won by making the patched state the default state.
Speech Permissions Are Not a Sufficient Defense
Some readers will wonder whether disabling microphone permissions or restricting speech recognition mitigates this vulnerability. It might reduce exposure to some code paths, but the public description does not provide enough detail to treat permission configuration as a substitute for the patch. The vulnerable component is Speech, but the exact trigger conditions remain restricted.This is a recurring problem with component-named browser CVEs. A flaw in “Speech” does not necessarily mean the user must knowingly grant microphone access, speak into a device, or use dictation. It may involve API state, object lifecycle, permission prompts, synthesis paths, recognition setup, or internal plumbing that is reachable before a user thinks of the feature as active. Without bug details, strong claims about mitigations are guesswork.
That does not mean policy controls are useless. Organizations with strict browser baselines should continue limiting unnecessary permissions, blocking risky site capabilities by default, and using allowlists for sensitive APIs. Reducing exposed feature surface is sound defense-in-depth.
But defense-in-depth is not patch management. If the vulnerable version is present, policy controls can at best lower the chance that a specific exploit path works. They cannot give the assurance that the fixed code provides.
The Web Platform Keeps Turning Convenience Into Risk
CVE-2026-7960 is a small window into a larger architectural bargain. Users want browsers to do everything. Developers want APIs that make web apps feel native. Platform vendors want the browser to be the universal runtime for productivity, AI, communication, gaming, collaboration, and device interaction. Security teams then inherit a codebase that must safely expose all of that to hostile pages.Speech is a perfect example because it sits at the intersection of accessibility, productivity, and ambient computing. Voice input helps users who cannot type comfortably. Speech synthesis improves usability. Web apps increasingly expect rich media and device access. None of this is frivolous.
But every step toward a more capable browser also increases the number of state machines inside it. The browser must ask who is allowed to access what, when, under which user gesture, in which frame, from which origin, for how long, and across which process boundary. Race conditions thrive where state machines meet concurrency.
The security model is therefore under constant pressure. It is not enough for a feature to be safe when used normally. It must be safe when initialized twice, canceled midstream, torn down during navigation, triggered from nested frames, interrupted by permission changes, and abused by scripts written specifically to find the one interleaving the programmer did not expect.
That is why browser security will never be “solved” by one sandbox or one memory-safe rewrite or one policy toggle. It is an ongoing negotiation between capability and containment. CVE-2026-7960 is one more negotiation failure, patched before the details become broadly useful.
The Real Risk Is Patch Latency, Not This One CVE
If there is a villain in this story, it is not the Speech component. It is latency. The longer a known browser vulnerability remains deployed after a stable patch exists, the more attractive it becomes to attackers who can diff patches, study restricted bugs as they become public, or incorporate the issue into exploit chains.Patch diffing is not magic, but it is a real discipline. Once a fixed build is available, researchers and attackers can compare changes, look for security-relevant modifications, and infer vulnerability mechanics. Restricted bug trackers slow the process, but they do not stop it. Time favors the side doing the reverse engineering if the defender has not updated.
This is why browser updates have a different tempo from traditional monthly patch cycles. Operating system patching still often moves in scheduled waves because compatibility risk can be high. Browsers, by contrast, are permanently exposed to untrusted content and update on a much faster cadence. Treating Chrome and Edge like ordinary desktop apps is a category error.
The irony is that many organizations now have excellent tooling for operating system patches but weaker discipline around browsers. They can tell you the Windows cumulative update status of every machine, yet struggle to prove which Chrome process version is currently running under every user profile. Attackers do not care which dashboard is more mature.
For CVE-2026-7960, the exposure window begins closing at 148.0.7778.96 and later. The organizations that shrink that window quickly will likely never think about this CVE again. The organizations that let old browser processes linger are volunteering for the long tail.
Chrome 148 Turns a Small Race Into a Fleet Test
The practical response to CVE-2026-7960 is refreshingly unglamorous. Update Chrome to the fixed branch, verify Edge and other Chromium-based browsers through their respective channels, force or strongly encourage restarts, and make sure vulnerability scanners are reading real versions rather than stale inventory records.That routine is the point. Browser CVEs have become too frequent and too interconnected for one-off drama. A mature response is not a war room for every medium-severity bug; it is a system that absorbs these releases quickly without needing a crisis narrative.
- Chrome installations older than 148.0.7778.96 should be treated as vulnerable for CVE-2026-7960 and the broader Chrome 148 security set.
- The bug is most concerning as a post-renderer-compromise information disclosure issue, meaning it may help an attacker extend or stabilize a larger exploit chain.
- Microsoft Edge administrators should track the corresponding Chromium security uptake rather than assuming a Google-branded CVE is irrelevant to Windows fleets.
- Browser restart compliance matters because a patched package does not protect a user who is still running the old process.
- CPE and scanner enrichment may lag, so endpoint version verification should drive action before database metadata looks perfect.
- Feature restrictions around speech and microphone access are useful hardening, but they should not be treated as a replacement for installing the fixed build.
Source: NVD / Chromium Security Update Guide - Microsoft Security Response Center