CVE-2026-8005 is a newly published Chromium vulnerability in Chrome’s Cast component, fixed in Google Chrome 148.0.7778.96 and later and documented by Microsoft on May 7, 2026, because Microsoft Edge inherits the Chromium code that contained the flaw. The bug is not a remote-code-execution emergency, and Google rates it low severity, but its shape is more interesting than its score. It is a reminder that the modern browser is no longer just a web renderer; it is a LAN-aware, device-discovery platform with a long tail of trust assumptions. For Windows administrators, the practical answer is simple: patch Chrome and Edge, but do not mistake “low” for “irrelevant.”
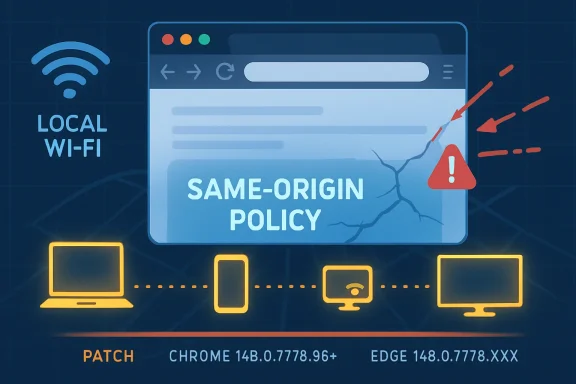
The vulnerability description is terse: insufficient validation of untrusted input in Cast allowed an attacker on the local network segment to bypass the same-origin policy through malicious network traffic. That sentence compresses three security boundaries into one line: input validation, local-network exposure, and the same-origin policy.
The same-origin policy is one of the core guardrails of the web. It is what keeps one site from casually reading another site’s data just because both pages happen to be open in the same browser. When a browser advisory says that policy can be bypassed, even in a constrained scenario, security teams should pause before dismissing it as housekeeping.
The limiting factor here is the attack position. This is not described as an internet-scale drive-by flaw, and the CVSS vector contributed by CISA’s ADP process marks the attack vector as adjacent rather than network-wide. In plain English, the attacker needs to be on the same local network segment, which pushes the bug away from mass exploitation and toward coffee-shop Wi-Fi, hostile guest networks, compromised office LANs, hotels, dorms, classrooms, labs, and shared workspaces.
That distinction matters, but it cuts both ways. Local-network requirements reduce exposure for well-segmented enterprise environments, yet they increase relevance in places where people still treat the LAN as a soft interior. Cast is precisely the sort of feature that assumes the local network is a place where discovery, convenience, and proximity can safely coexist.
That is the architectural point CVE-2026-8005 exposes. A browser feature that listens to, parses, or acts on local-network traffic must treat that traffic as hostile, even when it appears to come from a nearby device. The bug class, CWE-20 improper input validation, is not glamorous, but it is one of the oldest and most durable ways software gets into trouble.
The modern browser is full of these seams. It renders hostile web content, brokers permissions to cameras and microphones, talks to password managers, handles enterprise identity, mediates downloads, enforces site isolation, and increasingly participates in the local device ecosystem. Each seam creates a place where assumptions from one security model can leak into another.
Cast is especially interesting because it lives near a psychological blind spot. Users understand that a suspicious website may be dangerous. They are less likely to think of a malicious packet on the local network as a browser threat, and many administrators still reserve LAN-adjacent risk for printers, SMB, RDP, and unmanaged IoT gear.
The same-origin policy is not an optional hardening feature. It is part of the browser’s constitutional law. A bypass may have narrow preconditions, limited confidentiality impact, and no direct integrity or availability impact, but it still means code or traffic crossed a boundary the platform is supposed to enforce.
That is why browser bugs often look deceptively small in isolation. A renderer crash is just a crash until it becomes part of an exploit chain. An information disclosure is minor until it leaks the pointer, token, or page state needed for the next step. A same-origin-policy bypass is bounded until an attacker finds the web application that makes the boundary meaningful.
Nothing in the public description says CVE-2026-8005 is being exploited in the wild. Nothing suggests it is a crisis. But for defenders, the correct mental model is not “low severity, ignore”; it is “low severity, patch through normal browser channels, and check whether our local-network assumptions are still sane.”
So are we missing a CPE? Based on the public information provided, probably not in the narrow Chrome-desktop sense. The listed configuration covers the desktop platforms Google named for the stable-channel update: Windows, macOS, and Linux. The Chrome application CPE is the thing that carries the vulnerable version range; the OS CPEs describe the affected operating environments.
The more interesting omission is not necessarily a missing Chrome CPE, but the usual awkwardness around Chromium-derived products. Microsoft Edge is not the same product as Google Chrome, and it has its own update channel, release notes, and enterprise controls. Microsoft documents this CVE because Edge consumes Chromium, and its Security Update Guide says the latest Edge build is no longer vulnerable.
That does not automatically mean the NVD record should model every Chromium downstream browser as a vulnerable CPE. Vulnerability databases struggle with inherited open-source flaws because the affected code can exist in many products, but the fix, version number, release cadence, and exposure can differ by vendor. Over-modeling creates false positives; under-modeling hides downstream risk.
For a WindowsForum audience, the operational answer is cleaner than the taxonomy. If you manage Chrome, validate that Chrome is at 148.0.7778.96 or later. If you manage Edge, validate that Edge has moved to the 148.0.7778.xxx fixed line Microsoft identifies. If you manage other Chromium-based browsers, do not assume safety merely because the CVE page names Chrome.
Edge is a Microsoft product with Microsoft management hooks, Microsoft branding, Microsoft release notes, and Microsoft enterprise policy. But a large part of its security fate is tied to Chromium. When Chromium fixes a bug, Microsoft has to absorb, test, package, and ship that fix into Edge quickly enough that customers are not left with a lagging derivative.
This is not a criticism of Edge. The shared Chromium base has given the industry a faster, more coherent browser security pipeline than the old monoculture wars did in some respects. But it does mean administrators should stop treating browser patching as an app-by-app chore and start treating it as a dependency-management problem.
The CVE also shows why Microsoft’s Security Update Guide now regularly includes Chromium CVEs that may feel, at first glance, like Google’s news. Edge customers live in Microsoft’s patch ecosystem, not Google’s. If the vulnerable code is in the browser Microsoft ships to Windows users, then Microsoft has to surface the risk in the place Windows administrators actually watch.
The result is a two-track reality. Google’s advisory tells you where the vulnerability entered the public record and which Chrome builds fixed it. Microsoft’s entry tells you that Edge customers are part of the blast radius and that action is required through the Edge update path.
Enterprises have spent years moving identity and applications to the cloud while leaving local-network habits behind. Zero Trust became a slogan partly because the LAN stopped being a trustworthy perimeter. Yet browser features that discover and communicate with nearby devices still depend on local context in ways users rarely inspect.
That tension is where bugs like this matter. An attacker who must be adjacent is not omnipotent, but adjacency is not rare. Malware on one unmanaged device can become adjacent to everything else on the subnet. A malicious guest can be adjacent to employee laptops. A compromised printer, camera, TV, or casting dongle can become a strange little beachhead inside a supposedly ordinary office.
The attack described here is not a takeover of the network. It is a browser policy bypass via malicious traffic. Still, it belongs to the same family of problems: the local network is treated as a medium for convenience, while attackers treat it as a medium for influence.
For home users, the advice is not to panic about Cast. It is to keep browsers updated and avoid treating shared Wi-Fi as private space. For administrators, the advice is sharper: guest networks, client isolation, VLAN design, and browser policy should be considered part of browser risk management, not just network hygiene.
This CVE was fixed in Chrome 148.0.7778.96 for Linux and in the 148.0.7778.96/97 line for Windows and macOS. Microsoft’s Edge documentation points to the 148.0.7778.xxx build line for the Edge fix. The practical benchmark is not whether an update was offered; it is whether the vulnerable build has actually disappeared from managed devices.
That last mile is where browser security often fails. Chrome and Edge both update aggressively, but a browser that has downloaded an update may still need a restart. A kiosk, lab machine, shared workstation, or rarely rebooted VDI session can remain exposed longer than dashboards imply.
Administrators should also pay attention to Extended Stable channels. They are valuable for change control, but they are not a magic shield from security churn. Google’s own enterprise materials describe different cadences and trade-offs among Stable, Extended Stable, Beta, Dev, and Canary; the security question is whether the channel you chose is receiving the relevant fix and whether you can prove deployment.
The good news is that CVE-2026-8005 is exactly the kind of flaw that routine browser patching should absorb without drama. The bad news is that “without drama” depends on having routine browser patching that actually works.
Organizations with aggressive network segmentation and limited casting use may reasonably place this update into their normal browser patch cycle. Organizations with heavy use of wireless presentation systems, flat guest networks, or mixed-trust classrooms should care more. The vulnerability’s prerequisites are not exotic in those environments.
There is also a policy angle. Some enterprises disable or restrict Cast because they do not want unmanaged screen-sharing paths, local discovery chatter, or accidental data exposure. CVE-2026-8005 gives those teams another example for the file: browser convenience features are still attack surface.
That does not mean every organization should rip out Cast. It means Cast should be governed like other browser capabilities. If a feature can discover local devices, accept local network input, or bridge web content to physical displays, it belongs in the same conversation as WebUSB, WebBluetooth, local-network access prompts, and enterprise extension control.
Security teams sometimes lose credibility by treating every CVE as an emergency. The better argument here is proportionate: this is not a drop-everything bug, but it is a useful forcing function. If you cannot quickly answer which Chrome and Edge versions are deployed, or whether Cast is allowed on sensitive subnets, the vulnerability has already taught you something.
The browser perimeter is expanding sideways. It is not just the boundary between a user and the web; it is the boundary between web content, local devices, enterprise identity, cloud sync, extensions, media pipelines, and operating-system services. Every integration makes the browser more useful and more difficult to reason about.
Cast is part of that sideways expansion. It turns the browser into a participant in the local environment. That is useful in a living room, classroom, conference room, and boardroom, but it also means the browser must parse and trust signals from places security teams historically handled outside the browser threat model.
The same-origin policy angle makes the issue more than a device-discovery footnote. SOP is a web boundary, while Cast is a local-network feature. A bug that lets malicious local traffic affect web-origin isolation sits exactly at the seam between those worlds.
This is why the industry’s browser-security conversation cannot be only about JavaScript engines and renderer sandboxes. Those still matter enormously, but the browser’s non-web interfaces are where more of the weirdness now lives. Local network features, device APIs, media paths, AI assistants, password vaults, sync engines, and enterprise connectors all deserve the same suspicion once reserved for hostile HTML.
Chromium is not a single product in the way an old boxed application was a single product. It is an open-source project, a browser engine, a base for Chrome, a base for Edge, and a dependency for a wider ecosystem of browsers and embedded web surfaces. A flaw in Chromium can be a Chrome CVE, an Edge security note, a Linux distribution package issue, an Electron concern, or a non-event depending on what code is present and reachable.
CPEs were not designed to elegantly express all of that nuance. They are useful for scanners and inventories, but they flatten relationships that security engineers then have to unflatten. A record can be technically valid and still operationally incomplete for a given environment.
That is why mature vulnerability management increasingly requires enrichment from multiple places. NVD provides a common identifier and configuration data. Vendor advisories provide fixed versions and product-specific guidance. Endpoint inventory tells you whether the product is actually present. Network architecture tells you whether the preconditions are plausible. Business context tells you how fast you need to move.
For CVE-2026-8005, the CPE question should not stop at “is Chrome listed?” It should lead to “where do we run Chromium-derived browsers, how are they updated, and which of them expose Cast or similar local-network features?”
For unmanaged users, that means visiting the browser’s About page and restarting when prompted. For managed Windows environments, it means checking administrative consoles, update rings, GPO or cloud policy, and endpoint management reporting. The action is simple, but the evidence matters.
The larger challenge is discovering every place Chromium exists. Chrome and Edge are obvious. Brave, Vivaldi, Opera, Chromium packages, embedded browser controls, Electron applications, and vendor-bundled runtimes may be less obvious. Not all of them are necessarily affected by this particular Cast flaw, but they are part of the same maintenance universe.
Security teams should resist the temptation to declare victory because Windows Update is green. Edge has its own update mechanism, Chrome has its own update mechanism, and third-party Chromium products may follow still other paths. A patched operating system can host an unpatched browser for days, weeks, or longer if the update channel is blocked or restarts never happen.
That is why browser version reporting should be a first-class endpoint signal. It is no longer enough to know the OS build. The browser is an application platform, and its patch state is often more urgent than the monthly operating-system rollup.
Those boundaries should shape the response. This is a patch-now-through-normal-process issue, not a shut-down-the-network issue. Organizations with exposed shared wireless environments may choose to accelerate, but most should treat it as part of the already necessary Chrome 148 and Edge 148 update cycle.
It is also worth remembering that Chrome 148 fixed a much larger set of vulnerabilities. CVE-2026-8005 is one entry in a broader release, and defenders rarely get to patch one browser CVE à la carte. The right question is whether the browser has moved to the fixed train, not whether one medium-scored CVE has been individually neutralized.
For Windows administrators, Edge deserves equal attention. Microsoft’s listing exists because the Chromium flaw matters to Edge. If Edge is the default browser in your estate, Chrome’s version number alone does not answer your exposure question.
Client isolation on guest Wi-Fi is not just about stopping file shares from being browsed. It can reduce the opportunity for local attackers to influence browser-adjacent services. Separating unmanaged IoT and presentation devices from employee workstations is not just neat network design; it changes who can be adjacent to whom.
This matters in small environments too. Home routers, mesh networks, smart TVs, casting dongles, printers, cameras, and work laptops often coexist on one cheerful subnet. Remote work collapsed enterprise and consumer networks into the same physical space, and the browser sits right in the middle.
The Cast feature itself is not villainous. It is a useful technology that reflects what users expect from modern devices. But every convenience that relies on local discovery should be treated as a negotiated risk, not an invisible default.
Enterprises that do not need Cast can restrict it. Enterprises that do need it can isolate the networks where it operates. The worst option is leaving it enabled everywhere simply because nobody remembered the browser had become a local-network participant.
That means inventory queries should look for older 147.x and early 148.x browser versions. Dashboards should separate Chrome from Edge rather than lumping them together as “browser updated.” Restart compliance should be checked, because browser updates that have staged but not activated are a familiar source of false confidence.
The CPE record is useful, but it should not become the whole story. It models Chrome on the major desktop operating systems, while Microsoft’s advisory maps the Chromium fix into Edge. A scanner that keys only on one product name may miss the other, and a human who reads only the score may miss the local-network implication.
Here is the compact version Windows shops should carry into their next patch review:
Source: NVD / Chromium Security Update Guide - Microsoft Security Response Center
 A Low-Severity Bug Lands in a High-Trust Corner of the Browser
A Low-Severity Bug Lands in a High-Trust Corner of the Browser
The vulnerability description is terse: insufficient validation of untrusted input in Cast allowed an attacker on the local network segment to bypass the same-origin policy through malicious network traffic. That sentence compresses three security boundaries into one line: input validation, local-network exposure, and the same-origin policy.The same-origin policy is one of the core guardrails of the web. It is what keeps one site from casually reading another site’s data just because both pages happen to be open in the same browser. When a browser advisory says that policy can be bypassed, even in a constrained scenario, security teams should pause before dismissing it as housekeeping.
The limiting factor here is the attack position. This is not described as an internet-scale drive-by flaw, and the CVSS vector contributed by CISA’s ADP process marks the attack vector as adjacent rather than network-wide. In plain English, the attacker needs to be on the same local network segment, which pushes the bug away from mass exploitation and toward coffee-shop Wi-Fi, hostile guest networks, compromised office LANs, hotels, dorms, classrooms, labs, and shared workspaces.
That distinction matters, but it cuts both ways. Local-network requirements reduce exposure for well-segmented enterprise environments, yet they increase relevance in places where people still treat the LAN as a soft interior. Cast is precisely the sort of feature that assumes the local network is a place where discovery, convenience, and proximity can safely coexist.
Cast Turns the Browser Into a Neighbor on the LAN
Cast is easy to underestimate because users experience it as a button. Click, pick a device, throw a tab or video to a screen, and move on. Underneath that convenience is a set of discovery and communication paths that make the browser aware of devices around it, not just websites in front of it.That is the architectural point CVE-2026-8005 exposes. A browser feature that listens to, parses, or acts on local-network traffic must treat that traffic as hostile, even when it appears to come from a nearby device. The bug class, CWE-20 improper input validation, is not glamorous, but it is one of the oldest and most durable ways software gets into trouble.
The modern browser is full of these seams. It renders hostile web content, brokers permissions to cameras and microphones, talks to password managers, handles enterprise identity, mediates downloads, enforces site isolation, and increasingly participates in the local device ecosystem. Each seam creates a place where assumptions from one security model can leak into another.
Cast is especially interesting because it lives near a psychological blind spot. Users understand that a suspicious website may be dangerous. They are less likely to think of a malicious packet on the local network as a browser threat, and many administrators still reserve LAN-adjacent risk for printers, SMB, RDP, and unmanaged IoT gear.
Same-Origin Policy Bypasses Deserve More Respect Than Their Scores
A CVSS 3.1 score of 4.3 lands in medium territory under the CISA-ADP assessment, while Chromium’s own security severity is low. Both can be true. Scoring systems are designed to compare vulnerabilities across products, not to narrate how a bug fits into a specific organization’s threat model.The same-origin policy is not an optional hardening feature. It is part of the browser’s constitutional law. A bypass may have narrow preconditions, limited confidentiality impact, and no direct integrity or availability impact, but it still means code or traffic crossed a boundary the platform is supposed to enforce.
That is why browser bugs often look deceptively small in isolation. A renderer crash is just a crash until it becomes part of an exploit chain. An information disclosure is minor until it leaks the pointer, token, or page state needed for the next step. A same-origin-policy bypass is bounded until an attacker finds the web application that makes the boundary meaningful.
Nothing in the public description says CVE-2026-8005 is being exploited in the wild. Nothing suggests it is a crisis. But for defenders, the correct mental model is not “low severity, ignore”; it is “low severity, patch through normal browser channels, and check whether our local-network assumptions are still sane.”
The CPE Entry Looks Odd Because the Platform Story Is Odd
The NVD configuration shown for CVE-2026-8005 lists Google Chrome versions before 148.0.7778.96 and ties that application entry to Windows, Linux, and macOS operating-system CPEs. That can look strange if you expect a vulnerable-software record to name only Chrome. In this case, the structure appears to be expressing that vulnerable Chrome builds on those desktop operating systems are in scope.So are we missing a CPE? Based on the public information provided, probably not in the narrow Chrome-desktop sense. The listed configuration covers the desktop platforms Google named for the stable-channel update: Windows, macOS, and Linux. The Chrome application CPE is the thing that carries the vulnerable version range; the OS CPEs describe the affected operating environments.
The more interesting omission is not necessarily a missing Chrome CPE, but the usual awkwardness around Chromium-derived products. Microsoft Edge is not the same product as Google Chrome, and it has its own update channel, release notes, and enterprise controls. Microsoft documents this CVE because Edge consumes Chromium, and its Security Update Guide says the latest Edge build is no longer vulnerable.
That does not automatically mean the NVD record should model every Chromium downstream browser as a vulnerable CPE. Vulnerability databases struggle with inherited open-source flaws because the affected code can exist in many products, but the fix, version number, release cadence, and exposure can differ by vendor. Over-modeling creates false positives; under-modeling hides downstream risk.
For a WindowsForum audience, the operational answer is cleaner than the taxonomy. If you manage Chrome, validate that Chrome is at 148.0.7778.96 or later. If you manage Edge, validate that Edge has moved to the 148.0.7778.xxx fixed line Microsoft identifies. If you manage other Chromium-based browsers, do not assume safety merely because the CVE page names Chrome.
Microsoft’s Edge Note Is a Supply-Chain Disclosure in Miniature
Microsoft’s treatment of the CVE is formulaic, but the formula is revealing. The company says the CVE was assigned by Chrome, that Edge ingests Chromium, and that the latest Edge version is no longer vulnerable. That is a concise description of browser supply-chain reality in 2026.Edge is a Microsoft product with Microsoft management hooks, Microsoft branding, Microsoft release notes, and Microsoft enterprise policy. But a large part of its security fate is tied to Chromium. When Chromium fixes a bug, Microsoft has to absorb, test, package, and ship that fix into Edge quickly enough that customers are not left with a lagging derivative.
This is not a criticism of Edge. The shared Chromium base has given the industry a faster, more coherent browser security pipeline than the old monoculture wars did in some respects. But it does mean administrators should stop treating browser patching as an app-by-app chore and start treating it as a dependency-management problem.
The CVE also shows why Microsoft’s Security Update Guide now regularly includes Chromium CVEs that may feel, at first glance, like Google’s news. Edge customers live in Microsoft’s patch ecosystem, not Google’s. If the vulnerable code is in the browser Microsoft ships to Windows users, then Microsoft has to surface the risk in the place Windows administrators actually watch.
The result is a two-track reality. Google’s advisory tells you where the vulnerability entered the public record and which Chrome builds fixed it. Microsoft’s entry tells you that Edge customers are part of the blast radius and that action is required through the Edge update path.
The Local Network Is No Longer a Comfort Zone
The most important phrase in this CVE is “local network segment.” It sounds reassuring until you remember what local networks look like outside a diagram. A local segment can be a conference Wi-Fi network with hundreds of strangers, a hotel floor, a campus lab, a branch office with flat VLANs, or a home office full of unmanaged devices.Enterprises have spent years moving identity and applications to the cloud while leaving local-network habits behind. Zero Trust became a slogan partly because the LAN stopped being a trustworthy perimeter. Yet browser features that discover and communicate with nearby devices still depend on local context in ways users rarely inspect.
That tension is where bugs like this matter. An attacker who must be adjacent is not omnipotent, but adjacency is not rare. Malware on one unmanaged device can become adjacent to everything else on the subnet. A malicious guest can be adjacent to employee laptops. A compromised printer, camera, TV, or casting dongle can become a strange little beachhead inside a supposedly ordinary office.
The attack described here is not a takeover of the network. It is a browser policy bypass via malicious traffic. Still, it belongs to the same family of problems: the local network is treated as a medium for convenience, while attackers treat it as a medium for influence.
For home users, the advice is not to panic about Cast. It is to keep browsers updated and avoid treating shared Wi-Fi as private space. For administrators, the advice is sharper: guest networks, client isolation, VLAN design, and browser policy should be considered part of browser risk management, not just network hygiene.
Browser Patch Management Has Become Endpoint Patch Management
The old consumer advice still works: open the browser’s About page, let it check for updates, and restart. But enterprise environments need more than a ritual. They need telemetry that confirms browser build numbers across fleets, policies that prevent users from indefinitely deferring restarts, and a clear ownership model for Chrome, Edge, and any sanctioned Chromium derivative.This CVE was fixed in Chrome 148.0.7778.96 for Linux and in the 148.0.7778.96/97 line for Windows and macOS. Microsoft’s Edge documentation points to the 148.0.7778.xxx build line for the Edge fix. The practical benchmark is not whether an update was offered; it is whether the vulnerable build has actually disappeared from managed devices.
That last mile is where browser security often fails. Chrome and Edge both update aggressively, but a browser that has downloaded an update may still need a restart. A kiosk, lab machine, shared workstation, or rarely rebooted VDI session can remain exposed longer than dashboards imply.
Administrators should also pay attention to Extended Stable channels. They are valuable for change control, but they are not a magic shield from security churn. Google’s own enterprise materials describe different cadences and trade-offs among Stable, Extended Stable, Beta, Dev, and Canary; the security question is whether the channel you chose is receiving the relevant fix and whether you can prove deployment.
The good news is that CVE-2026-8005 is exactly the kind of flaw that routine browser patching should absorb without drama. The bad news is that “without drama” depends on having routine browser patching that actually works.
Low Severity Does Not Mean Low Priority Everywhere
Severity labels are global approximations. Risk is local. A low-severity Cast bug matters differently to a single desktop in a locked-down office than to a fleet of laptops constantly moving across client sites, classrooms, hotels, and coworking spaces.Organizations with aggressive network segmentation and limited casting use may reasonably place this update into their normal browser patch cycle. Organizations with heavy use of wireless presentation systems, flat guest networks, or mixed-trust classrooms should care more. The vulnerability’s prerequisites are not exotic in those environments.
There is also a policy angle. Some enterprises disable or restrict Cast because they do not want unmanaged screen-sharing paths, local discovery chatter, or accidental data exposure. CVE-2026-8005 gives those teams another example for the file: browser convenience features are still attack surface.
That does not mean every organization should rip out Cast. It means Cast should be governed like other browser capabilities. If a feature can discover local devices, accept local network input, or bridge web content to physical displays, it belongs in the same conversation as WebUSB, WebBluetooth, local-network access prompts, and enterprise extension control.
Security teams sometimes lose credibility by treating every CVE as an emergency. The better argument here is proportionate: this is not a drop-everything bug, but it is a useful forcing function. If you cannot quickly answer which Chrome and Edge versions are deployed, or whether Cast is allowed on sensitive subnets, the vulnerability has already taught you something.
The Real Story Is the Browser’s Expanding Perimeter
CVE-2026-8005 is not likely to be remembered as one of 2026’s landmark browser vulnerabilities. Chrome 148 fixed many security issues, including more severe flaws, and the Cast bug sits far below the headline-grabbing memory-safety class that usually drives emergency patching. Yet it is a better symbol of where browser security is headed.The browser perimeter is expanding sideways. It is not just the boundary between a user and the web; it is the boundary between web content, local devices, enterprise identity, cloud sync, extensions, media pipelines, and operating-system services. Every integration makes the browser more useful and more difficult to reason about.
Cast is part of that sideways expansion. It turns the browser into a participant in the local environment. That is useful in a living room, classroom, conference room, and boardroom, but it also means the browser must parse and trust signals from places security teams historically handled outside the browser threat model.
The same-origin policy angle makes the issue more than a device-discovery footnote. SOP is a web boundary, while Cast is a local-network feature. A bug that lets malicious local traffic affect web-origin isolation sits exactly at the seam between those worlds.
This is why the industry’s browser-security conversation cannot be only about JavaScript engines and renderer sandboxes. Those still matter enormously, but the browser’s non-web interfaces are where more of the weirdness now lives. Local network features, device APIs, media paths, AI assistants, password vaults, sync engines, and enterprise connectors all deserve the same suspicion once reserved for hostile HTML.
Security Databases Still Struggle With Chromium Reality
The user-facing CVE record asks, in effect, whether a CPE is missing. That small prompt says a lot about the state of vulnerability metadata. Software supply chains have become more compositional than the databases built to describe them.Chromium is not a single product in the way an old boxed application was a single product. It is an open-source project, a browser engine, a base for Chrome, a base for Edge, and a dependency for a wider ecosystem of browsers and embedded web surfaces. A flaw in Chromium can be a Chrome CVE, an Edge security note, a Linux distribution package issue, an Electron concern, or a non-event depending on what code is present and reachable.
CPEs were not designed to elegantly express all of that nuance. They are useful for scanners and inventories, but they flatten relationships that security engineers then have to unflatten. A record can be technically valid and still operationally incomplete for a given environment.
That is why mature vulnerability management increasingly requires enrichment from multiple places. NVD provides a common identifier and configuration data. Vendor advisories provide fixed versions and product-specific guidance. Endpoint inventory tells you whether the product is actually present. Network architecture tells you whether the preconditions are plausible. Business context tells you how fast you need to move.
For CVE-2026-8005, the CPE question should not stop at “is Chrome listed?” It should lead to “where do we run Chromium-derived browsers, how are they updated, and which of them expose Cast or similar local-network features?”
The Patch Is Easy; The Inventory Question Is Not
The immediate remediation path is straightforward. Chrome users should update to 148.0.7778.96 or later, with the relevant 148.0.7778.96/97 builds applying to Windows and macOS in Google’s stable-channel release. Edge users should update to Microsoft’s fixed 148.0.7778.xxx line.For unmanaged users, that means visiting the browser’s About page and restarting when prompted. For managed Windows environments, it means checking administrative consoles, update rings, GPO or cloud policy, and endpoint management reporting. The action is simple, but the evidence matters.
The larger challenge is discovering every place Chromium exists. Chrome and Edge are obvious. Brave, Vivaldi, Opera, Chromium packages, embedded browser controls, Electron applications, and vendor-bundled runtimes may be less obvious. Not all of them are necessarily affected by this particular Cast flaw, but they are part of the same maintenance universe.
Security teams should resist the temptation to declare victory because Windows Update is green. Edge has its own update mechanism, Chrome has its own update mechanism, and third-party Chromium products may follow still other paths. A patched operating system can host an unpatched browser for days, weeks, or longer if the update channel is blocked or restarts never happen.
That is why browser version reporting should be a first-class endpoint signal. It is no longer enough to know the OS build. The browser is an application platform, and its patch state is often more urgent than the monthly operating-system rollup.
The Cast Bug’s Practical Boundaries Are Clear
There is no public indication in the provided records that CVE-2026-8005 is under active exploitation. The impact described is limited to confidentiality, with no direct integrity or availability impact in the CISA-ADP vector. The attack requires adjacent-network positioning and no user interaction, which is a meaningful but not catastrophic combination.Those boundaries should shape the response. This is a patch-now-through-normal-process issue, not a shut-down-the-network issue. Organizations with exposed shared wireless environments may choose to accelerate, but most should treat it as part of the already necessary Chrome 148 and Edge 148 update cycle.
It is also worth remembering that Chrome 148 fixed a much larger set of vulnerabilities. CVE-2026-8005 is one entry in a broader release, and defenders rarely get to patch one browser CVE à la carte. The right question is whether the browser has moved to the fixed train, not whether one medium-scored CVE has been individually neutralized.
For Windows administrators, Edge deserves equal attention. Microsoft’s listing exists because the Chromium flaw matters to Edge. If Edge is the default browser in your estate, Chrome’s version number alone does not answer your exposure question.
This CVE Belongs in the Network Segmentation Conversation
The most durable lesson from CVE-2026-8005 is not about Cast alone. It is about how browser attack surface and network architecture now meet. A browser flaw with an adjacent-network vector turns network segmentation from a background control into a direct exploit mitigator.Client isolation on guest Wi-Fi is not just about stopping file shares from being browsed. It can reduce the opportunity for local attackers to influence browser-adjacent services. Separating unmanaged IoT and presentation devices from employee workstations is not just neat network design; it changes who can be adjacent to whom.
This matters in small environments too. Home routers, mesh networks, smart TVs, casting dongles, printers, cameras, and work laptops often coexist on one cheerful subnet. Remote work collapsed enterprise and consumer networks into the same physical space, and the browser sits right in the middle.
The Cast feature itself is not villainous. It is a useful technology that reflects what users expect from modern devices. But every convenience that relies on local discovery should be treated as a negotiated risk, not an invisible default.
Enterprises that do not need Cast can restrict it. Enterprises that do need it can isolate the networks where it operates. The worst option is leaving it enabled everywhere simply because nobody remembered the browser had become a local-network participant.
The 148.0.7778 Line Is the Number Administrators Need to See
The operational heart of this advisory is not the CVE prose; it is the build number. Chrome before 148.0.7778.96 is the vulnerable range called out in the public record. Microsoft’s Edge entry points administrators to the 148.0.7778.xxx fixed build line.That means inventory queries should look for older 147.x and early 148.x browser versions. Dashboards should separate Chrome from Edge rather than lumping them together as “browser updated.” Restart compliance should be checked, because browser updates that have staged but not activated are a familiar source of false confidence.
The CPE record is useful, but it should not become the whole story. It models Chrome on the major desktop operating systems, while Microsoft’s advisory maps the Chromium fix into Edge. A scanner that keys only on one product name may miss the other, and a human who reads only the score may miss the local-network implication.
Here is the compact version Windows shops should carry into their next patch review:
- Chrome desktop builds earlier than 148.0.7778.96 should be treated as vulnerable for CVE-2026-8005.
- Microsoft Edge is in scope because it consumes Chromium, and Microsoft identifies the fixed Edge line as 148.0.7778.xxx.
- The attack requires local-network adjacency, so exposure depends heavily on Wi-Fi design, guest segmentation, shared networks, and unmanaged devices.
- The bug is not known publicly as an actively exploited zero-day, but it affects the same-origin policy, which is a core browser boundary.
- The NVD CPE data appears to cover Chrome on Windows, Linux, and macOS, while downstream Chromium-based products still require vendor-specific verification.
- Browser update success should be measured by active build numbers after restart, not by whether an update was merely offered.
Source: NVD / Chromium Security Update Guide - Microsoft Security Response Center