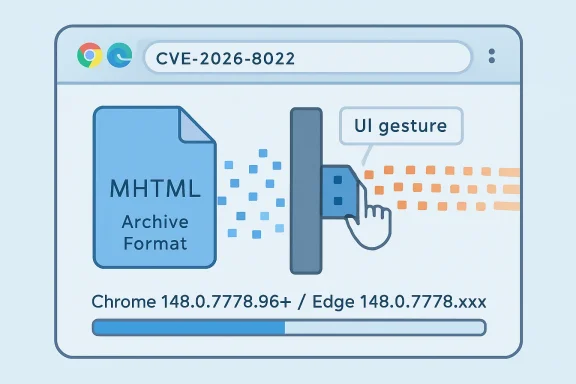
CVE-2026-8022 is a low-severity Chromium vulnerability disclosed May 6, 2026, affecting Google Chrome before 148.0.7778.96 and Microsoft Edge through its Chromium codebase, where a crafted MHTML page could leak cross-origin data after specific user interface gestures. That sentence sounds almost boring, which is precisely why the bug is worth paying attention to. The modern browser security story is no longer just about remote code execution and sandbox escapes; it is also about tiny seams in decades-old compatibility features. MHTML is one of those seams, and this CVE is a reminder that browser risk often hides in features most users never knowingly touch.
On paper, CVE-2026-8022 is not the kind of vulnerability that makes incident response teams cancel dinner. CISA’s ADP scoring puts it at 3.1 under CVSS 3.1, with network attack vector, high attack complexity, no privileges required, required user interaction, and low confidentiality impact. Chromium itself rates the issue as low severity.
That combination matters. The attacker must convince a user to perform specific UI gestures, and the stated impact is a leak of cross-origin data, not code execution, privilege escalation, or arbitrary file read. This is not a browser apocalypse.
But “low” is not “irrelevant.” Browser bugs that cross origin boundaries are interesting because the same-origin policy is one of the central load-bearing walls of the web. If a crafted page can coax the browser into revealing data that belongs to another origin, even in a narrow scenario, the browser has violated one of the assumptions developers, administrators, and users rely on every day.
The more important lesson is operational rather than dramatic. If Chrome before 148.0.7778.96 is vulnerable, and Edge inherits the fix through Chromium, then the relevant question for Windows administrators is not whether this single CVE deserves emergency treatment. It is whether their browser update machinery is fast enough, visible enough, and boring enough to make this class of issue disappear before anyone has to debate it.
The problem is that old web formats do not vanish simply because the front page of the internet moved on. They remain in browsers because users, enterprises, and application vendors still have documents, archives, and internal processes that depend on them. Every compatibility feature is a kind of treaty between the present and the past.
Security teams know this pattern well. Legacy functionality tends to accumulate edge cases because it was built for a friendlier or at least less adversarial environment. Later, it is wrapped in modern isolation rules, site boundaries, permission prompts, and renderer process models. Most of the time, that wrapping works. Occasionally, a weird interaction slips through.
CVE-2026-8022 lives in exactly that territory. The description says an inappropriate implementation in MHTML could allow a remote attacker to leak cross-origin data through a crafted MHTML page, provided the user performs specific UI gestures. That is not a simple drive-by exploit model. It is a manipulation model, and modern browser attacks increasingly blur the line between technical weakness and user-interface choreography.
That is why low-severity Chromium CVEs end up in Microsoft’s Security Update Guide. Microsoft did not assign this CVE; Chrome did. Microsoft’s role is downstream but not passive: Edge consumes Chromium, and when Chromium addresses a vulnerability, Edge must ingest that fix and tell enterprise customers whether action is required.
This is the uncomfortable truth of the Chromium era. Browser monoculture has benefits: faster patch propagation, shared engineering investment, and broad security research coverage. It also means a bug in shared code becomes a multi-vendor coordination event. The same underlying issue may appear in Chrome advisories, Edge release notes, vulnerability scanners, Linux distribution trackers, and enterprise dashboards.
That propagation is not noise. It is the supply chain doing what the supply chain does: turning one upstream bug into many downstream obligations. A Windows shop that standardizes on Edge is not insulated from Chromium vulnerabilities. It is participating in the Chromium ecosystem through Microsoft’s channel.
But user interaction requirements deserve careful reading. Phishing works because attackers are good at manufacturing context. A malicious page that says “click to view archived invoice,” “open saved report,” or “confirm preview” may not look like an exploit chain to the person at the keyboard. It looks like a task.
The history of web security is full of bugs that were technically constrained but practically useful in targeted scenarios. A vulnerability that leaks a small amount of cross-origin data may be enough to determine whether a user is logged into a service, infer state, expose a token-like value in a narrow context, or support a larger social-engineering sequence. The public description does not claim all of that for CVE-2026-8022, and we should not inflate it beyond the facts. Still, the category matters.
Cross-origin leaks are rarely satisfying in isolation. They become more interesting when combined with authentication assumptions, single sign-on, corporate SaaS apps, and browser-managed identity state. In other words, the risk is not that every user is one click away from compromise. The risk is that the browser is now where identity lives, and any origin-boundary leak touches that nervous system.
A low-severity browser CVE can still create high administrative friction. It appears in scanners, ticket queues, compliance reports, endpoint management dashboards, and executive rollups. If the organization has thousands of machines and several browser channels, the work is not in understanding the CVE. The work is in proving that every relevant endpoint moved past the vulnerable build.
That proof is harder than it sounds. Browser update status can differ across user profiles, virtual desktops, kiosk machines, golden images, server-hosted automation, and containerized workloads. Security teams often remember the browser on laptops but forget the headless Chromium instance embedded in a PDF conversion service or test harness. A low-severity issue is still a good excuse to audit where Chromium quietly exists.
The CPE configuration listed by NVD points toward Chrome on Windows, Linux, and macOS before 148.0.7778.96. Microsoft’s page calls out Edge with a fixed build line in the 148.0.7778.xxx family. The details are straightforward, but the operational footprint can be broad.
The cost is that Edge’s security cadence is now tied to Chromium’s. When Chrome ships a stable update, Edge administrators look for the corresponding Microsoft release, not because Microsoft independently created the flaw, but because Edge carries the affected code. This is not a scandal. It is how shared open-source infrastructure works.
Still, shared infrastructure changes patch psychology. A Windows team that once thought in terms of Patch Tuesday now has to think in terms of browser channels, rapid stable releases, extended stable releases, and out-of-band security updates. The browser does not wait politely for the second Tuesday of the month. It ships when the engine needs to ship.
CVE-2026-8022 arrived as part of a larger Chrome 148 desktop update, not as a lonely emergency flare. That is how most browser hardening reaches users: in a stream of fixes, many of them under-detailed until enough users are patched. Administrators who demand full exploit narratives before updating browsers are fighting the wrong war. Browser patching works because it is fast, frequent, and routine.
That does not mean administrators should panic and block every MHTML file tomorrow morning. It does mean they should know whether MHTML is used intentionally in their environment. If nobody can answer that question, the organization is not making a risk decision; it is inheriting one.
File handling policy is one of the most underappreciated parts of browser security. A browser is not just a renderer of websites. It is a document viewer, download broker, archive parser, preview surface, and sometimes the default handler for formats users barely recognize. Attackers like that ambiguity.
In the case of CVE-2026-8022, patching is the primary fix. But the secondary lesson is inventory: know which legacy web formats your users open, where they come from, and which applications are registered to handle them. The fact that a vulnerability is low severity does not make that exercise less useful. It makes it less likely that anyone will do it until the next, worse bug arrives.
Modern browsers enforce that separation through a layered set of mechanisms: same-origin policy, site isolation, frame restrictions, content security policies, cookie attributes, fetch rules, and increasingly strict handling of mixed or embedded content. The stack is impressive. It is also complicated.
Complexity is where inappropriate implementations live. A feature may do the right thing in ordinary browsing but mishandle an archived format, a preview path, an unusual navigation flow, or a UI-mediated action. That is why “specific UI gestures” matters. The vulnerability appears to sit at the intersection of data isolation and user-interface state.
The security industry tends to reserve attention for bugs that grant code execution, but data leaks are often the quieter failures that erode trust. The browser can be perfectly memory-safe in a given moment and still make the wrong information visible to the wrong origin. As more enterprise applications move into the browser, confidentiality bugs become more consequential even when their CVSS numbers stay modest.
Managed browser updates should be observable. Administrators need to know which devices are on stable, extended stable, beta, or dev channels; which policies defer updates; which users have disabled or delayed restarts; and which endpoints have not checked in. If the answer to a browser CVE is “it should auto-update,” the next question is “show me.”
The browser restart remains a stubborn weak point. Chrome and Edge can download updates quietly, but users often need to restart the browser before the new build is active. In an era where browser sessions last for days or weeks and tabs are treated like memory extensions, update completion is not guaranteed by download alone.
This is where good endpoint management earns its keep. The best organizations do not treat browser patching as a monthly scramble. They treat it as a continuous hygiene system with deadlines, telemetry, user nudges, and escalation for stragglers. CVE-2026-8022 does not demand a crisis posture, but it does reward that maturity.
None of these views is wrong. They are optimized for different audiences. The problem is that administrators have to translate among them while scanners and dashboards often flatten the nuance.
CVE-2026-8022 is described by NIST with CWE-352, Cross-Site Request Forgery, and by CISA-ADP with CWE-1021, improper restriction of rendered UI layers or frames. That mismatch is not unusual in early enrichment and does not necessarily mean contradiction; weakness classification can be approximate when public technical details are sparse. But it does show how vulnerability records can look more definitive than they really are.
The Chromium issue tracker entry is permission-restricted, which is also normal. Vendors often withhold detailed bug information until a majority of users have received the fix. That frustrates defenders who want technical detail, but it also reduces the chance that public write-ups become exploit recipes before the patch has propagated.
So the responsible reading is restrained. We know the affected component, the fixed Chrome version, the general exploitation condition, the confidentiality impact, the Edge dependency, and the low severity classification. We do not know the full exploit mechanics from the public record, and pretending otherwise would be bad journalism and worse security practice.
The right response to CVE-2026-8022 is not to convene an emergency bridge. It is to check whether your ordinary browser update process already solved it. If it did, this CVE is a useful validation event. If it did not, the low score is a gift: you found a process gap before a more serious Chromium bug forced the issue.
This is particularly true for mixed-browser environments. Many organizations officially support Edge but tolerate Chrome. Others deploy Chrome for developer or SaaS compatibility while keeping Edge as the managed default. Some have both because mergers, departments, or historical policy drift made browser standardization politically harder than technical deployment.
In those environments, a Chromium CVE becomes a governance test. Do you know which Chromium-based browsers are installed? Do you know which update services control them? Do you know whether third-party software bundles old Chromium components? If the answer is no, the vulnerability score is not the main risk. The inventory gap is.
The public timeline is also straightforward. Chrome received the CVE on May 6, 2026. CISA-ADP added scoring and weakness data later that day. NVD performed initial analysis on May 7, adding CPE configuration and reference metadata. Microsoft’s Security Update Guide entry for Edge was released May 7.
That sequence is a small but useful example of how modern disclosure actually works. The vendor ships or announces the fix, the vulnerability databases enrich the record, downstream vendors document impact, scanners pick it up, and administrators eventually see a ticket. By the time the ticket reaches a help desk queue, the best remediation should already be underway.
There is a temptation to view this as bureaucratic duplication. In reality, it is the plumbing of coordinated defense. The challenge is that the plumbing is noisy, and security teams need enough context to distinguish a low-severity hygiene item from a crisis. CVE-2026-8022 belongs firmly in the former category, but it should not be ignored.
Security has largely settled that argument in pragmatic terms. A shared engine concentrates risk, but it also concentrates repair capacity. Chromium vulnerabilities are found constantly because Chromium is scrutinized constantly. The machine is noisy because it is alive.
The more useful debate is not whether Edge should use Chromium. That decision was made years ago. The useful debate is whether organizations have adapted their operational model to the consequences of that decision. If Edge consumes Chromium, then Edge patching must move at Chromium speed.
CVE-2026-8022 is a minor entry in that larger ledger. It does not prove Chromium is uniquely unsafe, nor does it prove MHTML is catastrophically broken. It proves something more mundane and more important: old formats, modern UI flows, and web isolation rules are still colliding inside the software we use all day.
CVE-2026-8022 will likely disappear into the long scroll of Chromium fixes, remembered only by vulnerability managers who had to clear it from dashboards. That is fine. The best outcome for a bug like this is boredom: patched browsers, clean telemetry, no exploit drama, and one more reminder that the browser is now critical infrastructure wearing the costume of an everyday app.
Source: NVD / Chromium Security Update Guide - Microsoft Security Response Center
 A Low-Severity Bug Still Tells a High-Value Story
A Low-Severity Bug Still Tells a High-Value Story
On paper, CVE-2026-8022 is not the kind of vulnerability that makes incident response teams cancel dinner. CISA’s ADP scoring puts it at 3.1 under CVSS 3.1, with network attack vector, high attack complexity, no privileges required, required user interaction, and low confidentiality impact. Chromium itself rates the issue as low severity.That combination matters. The attacker must convince a user to perform specific UI gestures, and the stated impact is a leak of cross-origin data, not code execution, privilege escalation, or arbitrary file read. This is not a browser apocalypse.
But “low” is not “irrelevant.” Browser bugs that cross origin boundaries are interesting because the same-origin policy is one of the central load-bearing walls of the web. If a crafted page can coax the browser into revealing data that belongs to another origin, even in a narrow scenario, the browser has violated one of the assumptions developers, administrators, and users rely on every day.
The more important lesson is operational rather than dramatic. If Chrome before 148.0.7778.96 is vulnerable, and Edge inherits the fix through Chromium, then the relevant question for Windows administrators is not whether this single CVE deserves emergency treatment. It is whether their browser update machinery is fast enough, visible enough, and boring enough to make this class of issue disappear before anyone has to debate it.
MHTML Is the Compatibility Ghost That Refuses to Leave
MHTML, or MIME HTML, is an archive format for saving a web page and its resources into a single file. In the consumer imagination, it belongs to an older web: saved pages, email clients, corporate intranets, help systems, and workflows that predate the expectation that everything is live, authenticated, and cloud-backed. That makes it easy to dismiss.The problem is that old web formats do not vanish simply because the front page of the internet moved on. They remain in browsers because users, enterprises, and application vendors still have documents, archives, and internal processes that depend on them. Every compatibility feature is a kind of treaty between the present and the past.
Security teams know this pattern well. Legacy functionality tends to accumulate edge cases because it was built for a friendlier or at least less adversarial environment. Later, it is wrapped in modern isolation rules, site boundaries, permission prompts, and renderer process models. Most of the time, that wrapping works. Occasionally, a weird interaction slips through.
CVE-2026-8022 lives in exactly that territory. The description says an inappropriate implementation in MHTML could allow a remote attacker to leak cross-origin data through a crafted MHTML page, provided the user performs specific UI gestures. That is not a simple drive-by exploit model. It is a manipulation model, and modern browser attacks increasingly blur the line between technical weakness and user-interface choreography.
The Browser Is Now a Security Boundary, Not an App
For Windows users, Chrome and Edge are often treated as applications that update frequently and somewhat annoyingly. For administrators, they are more accurately described as security boundaries with user interfaces attached. They broker authentication sessions, render untrusted code, mediate access to cloud apps, handle password managers, parse documents, enforce cross-origin rules, and sit in the middle of almost every business process.That is why low-severity Chromium CVEs end up in Microsoft’s Security Update Guide. Microsoft did not assign this CVE; Chrome did. Microsoft’s role is downstream but not passive: Edge consumes Chromium, and when Chromium addresses a vulnerability, Edge must ingest that fix and tell enterprise customers whether action is required.
This is the uncomfortable truth of the Chromium era. Browser monoculture has benefits: faster patch propagation, shared engineering investment, and broad security research coverage. It also means a bug in shared code becomes a multi-vendor coordination event. The same underlying issue may appear in Chrome advisories, Edge release notes, vulnerability scanners, Linux distribution trackers, and enterprise dashboards.
That propagation is not noise. It is the supply chain doing what the supply chain does: turning one upstream bug into many downstream obligations. A Windows shop that standardizes on Edge is not insulated from Chromium vulnerabilities. It is participating in the Chromium ecosystem through Microsoft’s channel.
The User Gesture Requirement Is a Speed Bump, Not a Seat Belt
The exploit description’s most comforting phrase is “specific UI gestures.” It suggests the user has to do something unusual, perhaps click, drag, open, focus, save, preview, or otherwise interact with a crafted MHTML page in a way that makes exploitation less reliable. That helps explain the high attack complexity and low severity score.But user interaction requirements deserve careful reading. Phishing works because attackers are good at manufacturing context. A malicious page that says “click to view archived invoice,” “open saved report,” or “confirm preview” may not look like an exploit chain to the person at the keyboard. It looks like a task.
The history of web security is full of bugs that were technically constrained but practically useful in targeted scenarios. A vulnerability that leaks a small amount of cross-origin data may be enough to determine whether a user is logged into a service, infer state, expose a token-like value in a narrow context, or support a larger social-engineering sequence. The public description does not claim all of that for CVE-2026-8022, and we should not inflate it beyond the facts. Still, the category matters.
Cross-origin leaks are rarely satisfying in isolation. They become more interesting when combined with authentication assumptions, single sign-on, corporate SaaS apps, and browser-managed identity state. In other words, the risk is not that every user is one click away from compromise. The risk is that the browser is now where identity lives, and any origin-boundary leak touches that nervous system.
CVSS Captures Severity, But Not Administrative Friction
The CVSS vector tells a tidy story: remote attack vector, high complexity, no privileges, required user interaction, unchanged scope, low confidentiality impact, no integrity or availability impact. It is a reasonable score for the facts available. For vulnerability management teams, however, CVSS is only the beginning of the conversation.A low-severity browser CVE can still create high administrative friction. It appears in scanners, ticket queues, compliance reports, endpoint management dashboards, and executive rollups. If the organization has thousands of machines and several browser channels, the work is not in understanding the CVE. The work is in proving that every relevant endpoint moved past the vulnerable build.
That proof is harder than it sounds. Browser update status can differ across user profiles, virtual desktops, kiosk machines, golden images, server-hosted automation, and containerized workloads. Security teams often remember the browser on laptops but forget the headless Chromium instance embedded in a PDF conversion service or test harness. A low-severity issue is still a good excuse to audit where Chromium quietly exists.
The CPE configuration listed by NVD points toward Chrome on Windows, Linux, and macOS before 148.0.7778.96. Microsoft’s page calls out Edge with a fixed build line in the 148.0.7778.xxx family. The details are straightforward, but the operational footprint can be broad.
Edge’s Chromium Dependency Is a Feature Until It Becomes a Calendar Problem
Microsoft’s Edge strategy has been a practical success because it stopped fighting the web platform at the engine level. By adopting Chromium, Microsoft gained compatibility, reduced developer friction, and focused Edge differentiation on management, security services, enterprise integration, and user-facing features. For Windows administrators, that generally made life easier.The cost is that Edge’s security cadence is now tied to Chromium’s. When Chrome ships a stable update, Edge administrators look for the corresponding Microsoft release, not because Microsoft independently created the flaw, but because Edge carries the affected code. This is not a scandal. It is how shared open-source infrastructure works.
Still, shared infrastructure changes patch psychology. A Windows team that once thought in terms of Patch Tuesday now has to think in terms of browser channels, rapid stable releases, extended stable releases, and out-of-band security updates. The browser does not wait politely for the second Tuesday of the month. It ships when the engine needs to ship.
CVE-2026-8022 arrived as part of a larger Chrome 148 desktop update, not as a lonely emergency flare. That is how most browser hardening reaches users: in a stream of fixes, many of them under-detailed until enough users are patched. Administrators who demand full exploit narratives before updating browsers are fighting the wrong war. Browser patching works because it is fast, frequent, and routine.
The MHTML Angle Should Make Enterprise IT Check Its Assumptions
MHTML is not a hot consumer feature, but enterprises are where neglected formats often live longest. Archived reports, exported web apps, case-management systems, documentation bundles, and email-adjacent workflows can all create a surprising amount of contact with old formats. The more regulated the environment, the more likely it is to have preserved some legacy workflow because it was once validated, audited, or simply never replaced.That does not mean administrators should panic and block every MHTML file tomorrow morning. It does mean they should know whether MHTML is used intentionally in their environment. If nobody can answer that question, the organization is not making a risk decision; it is inheriting one.
File handling policy is one of the most underappreciated parts of browser security. A browser is not just a renderer of websites. It is a document viewer, download broker, archive parser, preview surface, and sometimes the default handler for formats users barely recognize. Attackers like that ambiguity.
In the case of CVE-2026-8022, patching is the primary fix. But the secondary lesson is inventory: know which legacy web formats your users open, where they come from, and which applications are registered to handle them. The fact that a vulnerability is low severity does not make that exercise less useful. It makes it less likely that anyone will do it until the next, worse bug arrives.
The Cross-Origin Wall Keeps Getting Tested
The phrase “cross-origin data” can sound abstract, but it describes one of the web’s central promises. A page from one site should not be able to freely read sensitive data from another site. Your banking tab, your Microsoft 365 session, your admin console, and a random site you just opened should not be part of the same trust universe.Modern browsers enforce that separation through a layered set of mechanisms: same-origin policy, site isolation, frame restrictions, content security policies, cookie attributes, fetch rules, and increasingly strict handling of mixed or embedded content. The stack is impressive. It is also complicated.
Complexity is where inappropriate implementations live. A feature may do the right thing in ordinary browsing but mishandle an archived format, a preview path, an unusual navigation flow, or a UI-mediated action. That is why “specific UI gestures” matters. The vulnerability appears to sit at the intersection of data isolation and user-interface state.
The security industry tends to reserve attention for bugs that grant code execution, but data leaks are often the quieter failures that erode trust. The browser can be perfectly memory-safe in a given moment and still make the wrong information visible to the wrong origin. As more enterprise applications move into the browser, confidentiality bugs become more consequential even when their CVSS numbers stay modest.
Patch Velocity Is the Real Control
For most WindowsForum readers, the practical answer is simple: make sure Chrome is at 148.0.7778.96 or later, and make sure Edge has received Microsoft’s corresponding 148.0.7778.xxx security update. That is the user-level version of the story. The fleet-level version is more demanding.Managed browser updates should be observable. Administrators need to know which devices are on stable, extended stable, beta, or dev channels; which policies defer updates; which users have disabled or delayed restarts; and which endpoints have not checked in. If the answer to a browser CVE is “it should auto-update,” the next question is “show me.”
The browser restart remains a stubborn weak point. Chrome and Edge can download updates quietly, but users often need to restart the browser before the new build is active. In an era where browser sessions last for days or weeks and tabs are treated like memory extensions, update completion is not guaranteed by download alone.
This is where good endpoint management earns its keep. The best organizations do not treat browser patching as a monthly scramble. They treat it as a continuous hygiene system with deadlines, telemetry, user nudges, and escalation for stragglers. CVE-2026-8022 does not demand a crisis posture, but it does reward that maturity.
Vulnerability Feeds Are Becoming a Translation Problem
One of the oddities of modern vulnerability management is that the same issue appears differently depending on where you look. The Chrome advisory names the browser build. NVD enriches the record with CPEs, CWE mappings, and scoring data. CISA’s ADP contribution adds a CVSS vector and an additional weakness classification. Microsoft’s Security Update Guide explains why a Chrome-assigned CVE appears in Edge documentation.None of these views is wrong. They are optimized for different audiences. The problem is that administrators have to translate among them while scanners and dashboards often flatten the nuance.
CVE-2026-8022 is described by NIST with CWE-352, Cross-Site Request Forgery, and by CISA-ADP with CWE-1021, improper restriction of rendered UI layers or frames. That mismatch is not unusual in early enrichment and does not necessarily mean contradiction; weakness classification can be approximate when public technical details are sparse. But it does show how vulnerability records can look more definitive than they really are.
The Chromium issue tracker entry is permission-restricted, which is also normal. Vendors often withhold detailed bug information until a majority of users have received the fix. That frustrates defenders who want technical detail, but it also reduces the chance that public write-ups become exploit recipes before the patch has propagated.
So the responsible reading is restrained. We know the affected component, the fixed Chrome version, the general exploitation condition, the confidentiality impact, the Edge dependency, and the low severity classification. We do not know the full exploit mechanics from the public record, and pretending otherwise would be bad journalism and worse security practice.
Low-Severity Browser Bugs Are Where Process Beats Heroics
There is a certain kind of security culture that only wakes up for critical CVEs. That culture is understandable. Teams are overloaded, vulnerability backlogs are absurd, and not every low-severity item deserves the same attention as an actively exploited zero-day. But browsers are different because they sit so close to daily user behavior.The right response to CVE-2026-8022 is not to convene an emergency bridge. It is to check whether your ordinary browser update process already solved it. If it did, this CVE is a useful validation event. If it did not, the low score is a gift: you found a process gap before a more serious Chromium bug forced the issue.
This is particularly true for mixed-browser environments. Many organizations officially support Edge but tolerate Chrome. Others deploy Chrome for developer or SaaS compatibility while keeping Edge as the managed default. Some have both because mergers, departments, or historical policy drift made browser standardization politically harder than technical deployment.
In those environments, a Chromium CVE becomes a governance test. Do you know which Chromium-based browsers are installed? Do you know which update services control them? Do you know whether third-party software bundles old Chromium components? If the answer is no, the vulnerability score is not the main risk. The inventory gap is.
The Quiet Work After Chrome 148
The concrete fix line is easy to remember: Chrome before 148.0.7778.96 is affected. Windows and macOS stable builds in the Chrome 148 release train include 148.0.7778.96 and 148.0.7778.97, while Linux is listed at 148.0.7778.96. Microsoft’s Edge guidance points to the 148.0.7778.xxx build family for its corresponding security update.The public timeline is also straightforward. Chrome received the CVE on May 6, 2026. CISA-ADP added scoring and weakness data later that day. NVD performed initial analysis on May 7, adding CPE configuration and reference metadata. Microsoft’s Security Update Guide entry for Edge was released May 7.
That sequence is a small but useful example of how modern disclosure actually works. The vendor ships or announces the fix, the vulnerability databases enrich the record, downstream vendors document impact, scanners pick it up, and administrators eventually see a ticket. By the time the ticket reaches a help desk queue, the best remediation should already be underway.
There is a temptation to view this as bureaucratic duplication. In reality, it is the plumbing of coordinated defense. The challenge is that the plumbing is noisy, and security teams need enough context to distinguish a low-severity hygiene item from a crisis. CVE-2026-8022 belongs firmly in the former category, but it should not be ignored.
The Chrome-to-Edge Pipeline Leaves Little Room for Sentimentality
For Windows enthusiasts, Edge’s Chromium base can still provoke philosophical arguments. Some miss the days when browser engines represented sharper platform competition. Others prefer the current era because sites work, developer testing is simpler, and Microsoft can focus on enterprise integration rather than fighting rendering bugs one site at a time.Security has largely settled that argument in pragmatic terms. A shared engine concentrates risk, but it also concentrates repair capacity. Chromium vulnerabilities are found constantly because Chromium is scrutinized constantly. The machine is noisy because it is alive.
The more useful debate is not whether Edge should use Chromium. That decision was made years ago. The useful debate is whether organizations have adapted their operational model to the consequences of that decision. If Edge consumes Chromium, then Edge patching must move at Chromium speed.
CVE-2026-8022 is a minor entry in that larger ledger. It does not prove Chromium is uniquely unsafe, nor does it prove MHTML is catastrophically broken. It proves something more mundane and more important: old formats, modern UI flows, and web isolation rules are still colliding inside the software we use all day.
The Patch Is Small; the Lesson Is Fleet-Wide
CVE-2026-8022 should be handled as a routine browser security update, but routine does not mean casual. The value of this CVE is that it exposes the control points administrators should already have in place.- Chrome installations should be updated to 148.0.7778.96 or later, with attention to platform-specific stable builds where 148.0.7778.97 is present.
- Microsoft Edge should be updated to the corresponding 148.0.7778.xxx security build because Edge consumes the affected Chromium code.
- Browser update compliance should be verified through management telemetry rather than assumed from automatic update settings.
- Long-running browser sessions should be forced or nudged to restart when security updates are staged but not active.
- Organizations should review whether MHTML files are used intentionally and whether legacy web archive handling is covered by policy.
- Vulnerability teams should treat this as a useful test of Chromium inventory across desktops, servers, virtual environments, and embedded automation.
CVE-2026-8022 will likely disappear into the long scroll of Chromium fixes, remembered only by vulnerability managers who had to clear it from dashboards. That is fine. The best outcome for a bug like this is boredom: patched browsers, clean telemetry, no exploit drama, and one more reminder that the browser is now critical infrastructure wearing the costume of an everyday app.
Source: NVD / Chromium Security Update Guide - Microsoft Security Response Center