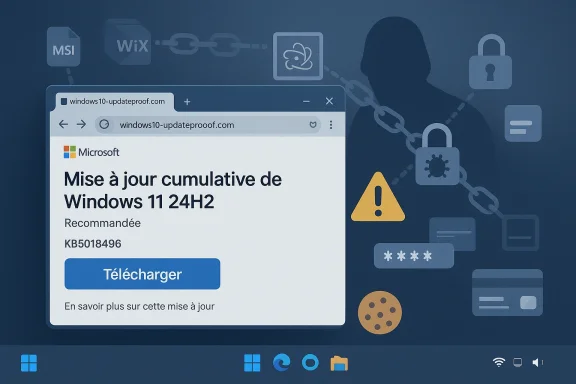
A convincing fake Windows 11 24H2 update is making the rounds, and the danger is not a broken patch or a botched reboot. It is a malicious installer disguised as a Microsoft download page, built to steal passwords, browser sessions, payment data, and other sensitive information from unwary users. Malwarebytes says the campaign uses a typosquatted domain, polished branding, and a fake KB number to look legitimate at first glance, while quietly delivering infostealer malware instead ows updates occupy a strange place in the user psyche. They are supposed to be boring, routine, and safe, which is exactly why attackers keep weaponizing them. A fake update prompt does not need to invent urgency from scratch; it only needs to hijack a workflow people already trust. That makes this kind of campaign especially effective against home users, and especially dangerous in environments where people are used to clicking through update prompts without much scrutiny .
The latest scam, aces, centers on a website hosted at a lookalike domain, microsoft-update[.]support, that imitates an official Microsoft support page and presents a believable Windows 11 24H2 cumulative update lure. The page is written in French, includes a prominent download button, and uses a plausible KB-style reference to create the impression of normal servicing. In other words, it borrows the visual grammar of Microsoft maintenance rather than the obvious branding cues users have been trained to spot .
That matters because Microsoft’s real upnt. Official guidance directs users to Windows Update in Settings, and Microsoft also points people to its own support pages and Update Catalog when a standalone package is actually required. There is no legitimate reason for a random website to present itself as a Microsoft patch portal and then ask users to fetch an “update” through a big blue button. The whole trick depends on making the user forget that source matters more than presentation .
There is also a timing angle. Windows 11 24H2 is a recognizabn name, which makes it especially useful for attackers. A current release label sounds believable to casual visitors, and a fake update for a version people have actually heard of feels more plausible than a generic “security patch” scam. That is one reason why the campaign feels modern rather than clumsy: it is using current Windows language as a social-engineering asset .
What makes the campaign more serious is that the malware chain is not crude. Malwarebytes says the package was built with WiX Toolset 4.0.0.5512, a legitimate open-source installer framework, and that the file metadata was spoofed to read as if Microsoft authored it. That combination is a reminder that legitimate tools can be repurposed for illegitimate ends, and that a file can look entirely ordinary while still being part of a theft operation .
A fake update succeeds by reducing the amount of thinking the user has to do. People are conditioned to see updates as maintenance, not as a decision point, so the attacker merely has to create a convincing maintenance environment. The more the page resembles a normal Windows workflow, the less likely the user is to pause and verify the domain or the KB reference .
The other reason these scams work is that they exploit a real problem: users have been taught for years to fear “outdated” software. That fear makew cumulative update feel protective rather than suspicious. In that sense, attackers are not inventing a new instinct; they are hijacking a healthy one and turning it against the victim .
The installer does not simply drop a single executable and run. Instead, it sets up an Electron-based application in the AppData folder, launches it through a script that uses Windows’ own cscript.exe, and then starts a renamed Python interpreter. That Python layer loads a set of additional modules that the malware uses for credential theft and data collection. The chain is deliberately indirect, and that indirection is what makes it harder to spot in a quick glance .
The campaign is also persistent. Malwarebytes says it creates a Run key called SecurityHealth in the user’s registry, pointing to WindowsUpdate.exe, and adds a shortcut named Spotify.lnk in Startup to quietly relaunch the malware on reboot. That is not just a nuisance; persistence turns a one-time mistake into an ongoing compromise. Once the malware survives restarts, it has more time to harvest data and more chances to evade cleanup .
There is a telling mismatch in the fake update’s story. Malwarebytes says the site advertises KB5034765 as if it were tied to Windows 11 24H2, but Microsoft’s own support history shows that KB5034765 was released for Windows 11 version 22H2 and 23H2. That kind of misplacement is small enough for a rushed user to miss, but it is also the sort of detail that exposes the scam to anyone who checks the context .
The larger pattern here is trust engineering. Attackers are no longer relying on crude .exe files with obvious names and cartoonish phishing pages. They are building plausible software delivery experiences that resemble vendor support, normal packaging, and ordinary update behavior. Tharategy because it shifts the fight from malware detection alone to user judgment, process control, and source verification .
That matters because security software is often best at catching the obvious stuff first. When the attackers wrap malicious behavior inside ordinary tools like Electron, Python, and Windows scripting, they are intentionally moving into the gray area between “looks normal” and “is malicious.” That gray area is where a lot of compromises happen, especially when the first-stage lure is polished enough to pass the smell test .
This approach is clever because each stage can look benign on its own. A script is not automatically suspicious. Electron is a common application framework. Python is a standard language for automation and orchestration. WiX Toolset is a normal installer framework. Put together, however, the sequence creates a malicious workflow that is far harder to recognize than a one-file dropper ever would be .
The use of cscript.exe is also important. It uses a Windows-native component, which helps the chain blend into ordinary system activity. That is a classic tradeoff in malware design: the more native the tooling, the less obvious the abuse. The downside for defenders is that they have to look at behavior and sequence, not just at isolated files or process names .
This is a textbook example of why endpoint detection increasingly has to reason about what a sequence is trying to do. An MSI alone may not tell the whole story. A script alone may not tell the whole story. But a script that launches Electron, which then starts a renamed Python interpreter, which then loads theft-related modules, tells a very different story indeed .
This is a much broader threat than a simple password theft. Browser sessions and cookies can be enough to access accounts without needing the password again, depending on the service and the session state. That means a victim can be compromised even if they never typed their password into a phishing site. The attacker is stealing the active trust relationship between the browser and the service, not just the credential itself .
Discord is a notable target in the report because Electron-based apps can be especially attractive to attackers. Malwarebytes says the smaller file in the chain targets Discord by modifying iogin tokens, payment details, and two-factor authentication changes when the app is opened. That is a reminder that app ecosystems built on shared web-like technology can also share a common attack surface .
Payment data raises the stakes again. Stored card details, autofill records, and cached billing artifacts can be abused quickly once they are in criminal hands. In a real-world fraud chain, a stolen browser profile can become the staty theft, card-not-present fraud, or further credential stuffing campaigns. That is why these infections tend to ripple outward long after the initial download .
Persistence is one of the key reasons these campaigns are so damaging. A malware sample that runs once and vanishes is bad enough. A sample that survives reboot, reopens on startup, and keeps harvesting data turns into an operational problem that can last far longer. That also gives the attacker time to retrieve credentials before the victim ever realizes what happened .
The report also notes that early samples showed zero detections in common scanning services. That is not the same as being safe, but it does show how much advantage a new campaign can get before signatures, heuristics, or user reports catch up. Freshness remains one of the attacker’s most useful assets .
The use of legitimate tools is a second layer of evasion make malware legal, of course, but it does make the installer feel standard. Electron and Python are everyday technologies, not exotic red flags. And cscript.exe is a built-in Windows component. Together, they create an environment where nothing looks obviously wrong until you assemble the whole chain .
The fake campaign leans on the idea that an update can come from anywhere if it looks official enough. That is false. The domain is the trust anchor, not the logo. A plausible product name does not validate a website, and a polished download button does not prove legitimacy. If anything, this campaign is a reminder that visual polish is not the same thing as provenance .
This also matters for enterprise environments. IT teams often distribute updates through managed channels, patch systems, or internal repositories. A random internet download that claims to be a Microsoft cumulative update should stand out immediately. If it does not, the organization has a bigger process problem than a single phishing page .
For enterprises, the implications are broader and more expensive. A compromised endpoint can reveal corporate browser sessions, email access, SaaS tokens, and potentially VPN-related artifacts. The immediate loss may not be a file server breach; it may be a quiet foothold that enables lateral movement or business-email compromise later. That makes the threat especially relevant to organizations that assume browser data is “just personal browsing” .
The French-language presentation also suggests a targeted initial audience, though campaigns like this can be ter. Attackers frequently start with one language or region, then adapt based on success. That means the issue is not limited to a single audience or geography; it is a repeatable pattern with a flexible front end .
Defenders should expect more of the same with different version numbers, different file names, and possibly different languages. The basic idea is too effective to abandon quickly. If anything, this incident is a preview of how update-themed phishing will evolve: less noisy, more professional, and increasingly built around ordinary tools that users are trained to trust.
This campaign is a reminder that modern malware often looks less like a hack and more like a service. It arrives with branding, metadata, and workflow design that tries to feel ordinary. The safest response is to remember that in security, ordinary-looking is not the same as trustworthy, and a download that feels like maintenance can still be theft in disguise
Source: extremetech.com Fake Windows 11 24H2 Update Poses as Legit Download to Steal Data
The latest scam, aces, centers on a website hosted at a lookalike domain, microsoft-update[.]support, that imitates an official Microsoft support page and presents a believable Windows 11 24H2 cumulative update lure. The page is written in French, includes a prominent download button, and uses a plausible KB-style reference to create the impression of normal servicing. In other words, it borrows the visual grammar of Microsoft maintenance rather than the obvious branding cues users have been trained to spot .
That matters because Microsoft’s real upnt. Official guidance directs users to Windows Update in Settings, and Microsoft also points people to its own support pages and Update Catalog when a standalone package is actually required. There is no legitimate reason for a random website to present itself as a Microsoft patch portal and then ask users to fetch an “update” through a big blue button. The whole trick depends on making the user forget that source matters more than presentation .
There is also a timing angle. Windows 11 24H2 is a recognizabn name, which makes it especially useful for attackers. A current release label sounds believable to casual visitors, and a fake update for a version people have actually heard of feels more plausible than a generic “security patch” scam. That is one reason why the campaign feels modern rather than clumsy: it is using current Windows language as a social-engineering asset .
What makes the campaign more serious is that the malware chain is not crude. Malwarebytes says the package was built with WiX Toolset 4.0.0.5512, a legitimate open-source installer framework, and that the file metadata was spoofed to read as if Microsoft authored it. That combination is a reminder that legitimate tools can be repurposed for illegitimate ends, and that a file can look entirely ordinary while still being part of a theft operation .
 Why fake updates work so well
Why fake updates work so well
A fake update succeeds by reducing the amount of thinking the user has to do. People are conditioned to see updates as maintenance, not as a decision point, so the attacker merely has to create a convincing maintenance environment. The more the page resembles a normal Windows workflow, the less likely the user is to pause and verify the domain or the KB reference .The other reason these scams work is that they exploit a real problem: users have been taught for years to fear “outdated” software. That fear makew cumulative update feel protective rather than suspicious. In that sense, attackers are not inventing a new instinct; they are hijacking a healthy one and turning it against the victim .
- The fake page borrows trust from Microsoft’s branding language.
- The lure uses a recognizable Windows 11 24H2 label.
- The installer hides behind legitimate packagind is designed to steal, not merely break.
- The campaign targets the gap between routine behavior and verification.
Overview
At the center of the campaign is an MSI installer named WindowsUpdate 1.0.0.msi. Malwarebytes reports that it is an 83 MB package with spoofed properties that list Microsoft as the author and present the file as ordinary installation content. That size is important: it is large enough to look serious and plausible, but not so large that users will question why a “patch” has to be downloaded outside the normal Windows Update path .The installer does not simply drop a single executable and run. Instead, it sets up an Electron-based application in the AppData folder, launches it through a script that uses Windows’ own cscript.exe, and then starts a renamed Python interpreter. That Python layer loads a set of additional modules that the malware uses for credential theft and data collection. The chain is deliberately indirect, and that indirection is what makes it harder to spot in a quick glance .
The campaign is also persistent. Malwarebytes says it creates a Run key called SecurityHealth in the user’s registry, pointing to WindowsUpdate.exe, and adds a shortcut named Spotify.lnk in Startup to quietly relaunch the malware on reboot. That is not just a nuisance; persistence turns a one-time mistake into an ongoing compromise. Once the malware survives restarts, it has more time to harvest data and more chances to evade cleanup .
There is a telling mismatch in the fake update’s story. Malwarebytes says the site advertises KB5034765 as if it were tied to Windows 11 24H2, but Microsoft’s own support history shows that KB5034765 was released for Windows 11 version 22H2 and 23H2. That kind of misplacement is small enough for a rushed user to miss, but it is also the sort of detail that exposes the scam to anyone who checks the context .
The larger pattern here is trust engineering. Attackers are no longer relying on crude .exe files with obvious names and cartoonish phishing pages. They are building plausible software delivery experiences that resemble vendor support, normal packaging, and ordinary update behavior. Tharategy because it shifts the fight from malware detection alone to user judgment, process control, and source verification .
A familiar but more polished attack style
Fake Adobe updates, fake browser updates, fake antivirus renewals, and fake Windows maintenance pages have circulated for years. What has changed is the quality of the disguise. The current campaign uses a legitimate installer framework, spoofed metadata, and layered payloads so the file looks routine to users and less suspicious to some tools as well .That matters because security software is often best at catching the obvious stuff first. When the attackers wrap malicious behavior inside ordinary tools like Electron, Python, and Windows scripting, they are intentionally moving into the gray area between “looks normal” and “is malicious.” That gray area is where a lot of compromises happen, especially when the first-stage lure is polished enough to pass the smell test .
- The installer uses a legitimate software packaging ecosystem.
- The fake support page looks professionally built.
- The file metadata is crafted to appear Microsoft-like.
- The execution chain is layered to slow analysis.
- The persistence mechanism is designed to survive reboot.
The Delivery Chain
Malwarebytes describes a multi-stage delivery chain rather than a single malicious payload. The MSI drops a Visual Basic script, which launches an Electron-based application, which then spawns a disguised Python process. That process installs multiple packages associated with data theft and system inspection. The whole design is built around staging, not immediacy, which is a hallmark of modern infostealer operations .This approach is clever because each stage can look benign on its own. A script is not automatically suspicious. Electron is a common application framework. Python is a standard language for automation and orchestration. WiX Toolset is a normal installer framework. Put together, however, the sequence creates a malicious workflow that is far harder to recognize than a one-file dropper ever would be .
Why the layering matters
Layering helps the attackers survive both human inspection and basic automated checks. A user who opens the installer properties may see “Microsoft” in the author field and a generic installation database description, which feels reassuring. A scanner might initially see a known packaging format and a script launcher rather than a ready-made infostealer binary. By the time the real payload behavior appears, the attacker has already bought time .The use of cscript.exe is also important. It uses a Windows-native component, which helps the chain blend into ordinary system activity. That is a classic tradeoff in malware design: the more native the tooling, the less obvious the abuse. The downside for defenders is that they have to look at behavior and sequence, not just at isolated files or process names .
This is a textbook example of why endpoint detection increasingly has to reason about what a sequence is trying to do. An MSI alone may not tell the whole story. A script alone may not tell the whole story. But a script that launches Electron, which then starts a renamed Python interpreter, which then loads theft-related modules, tells a very different story indeed .
Sequence of compromise
- User lands on a fake Microsoft-style support page.
- User downloads the MSI labeled WindowsUpdate 1.0.0.msi.
- The installer drops supporting files and scripts.
- A VBS launcher starts the app through cscript.exe.
- Electron and Python handle the theft workflow.
- Persistence is added through registry and Startup mechanisms.
The Data Theft Goals
The primary payload goal is not destruction but collection. Malwarebytes says the malware can extract browser-stored passwords, cookies, account sessions, Discord data, and payment-related information. That places the campaign squarely in infostealer territory, where the objective is to harvest reusable data that can be monetized, resold, or used for account takeover .This is a much broader threat than a simple password theft. Browser sessions and cookies can be enough to access accounts without needing the password again, depending on the service and the session state. That means a victim can be compromised even if they never typed their password into a phishing site. The attacker is stealing the active trust relationship between the browser and the service, not just the credential itself .
Why cookies and tokens are so valuable
Cookies, tokens, and session artifacts are valuable because they can bypass some of the friction that passwords are supposed to creauires a valid session token, they may not need to solve two-factor authentication in the traditional sense. The result is a faster path to email, cloud apps, gaming accounts, or other services that are linked to the infected browser profile .Discord is a notable target in the report because Electron-based apps can be especially attractive to attackers. Malwarebytes says the smaller file in the chain targets Discord by modifying iogin tokens, payment details, and two-factor authentication changes when the app is opened. That is a reminder that app ecosystems built on shared web-like technology can also share a common attack surface .
Payment data raises the stakes again. Stored card details, autofill records, and cached billing artifacts can be abused quickly once they are in criminal hands. In a real-world fraud chain, a stolen browser profile can become the staty theft, card-not-present fraud, or further credential stuffing campaigns. That is why these infections tend to ripple outward long after the initial download .
- Browser passwords are only one part of the prize.
- Session tokens may be more useful than passwords.
- Discord data can expose community and payment accounts.
- Payment artifacts can accelerate fraud.
- Stolen credentials often seed further attacks.
Pe
The fake updater does not disappear after a reboot. Malwarebytes says it creates a Run registry key named SecurityHealth, and it also drops a Spotify.lnk shortcut in Startup to quietly relaunch the malware. Those choices are intentional camouflage. A Run key named after a Windows security component is less likely to look suspicious than something obviously malicious, and a Spotify shortcut is the sort of ordinarynore at a glance .Persistence is one of the key reasons these campaigns are so damaging. A malware sample that runs once and vanishes is bad enough. A sample that survives reboot, reopens on startup, and keeps harvesting data turns into an operational problem that can last far longer. That also gives the attacker time to retrieve credentials before the victim ever realizes what happened .
Why evasion beats brute force
This campaign does not need a noisy exploit chain or a dramatic privilege escalation event. It only needs the user to believe the installer is legitimate long enough for the payload to establish a foothold. Once that happens, the malware can blend into ordinary startup activity, and the attacker can keep collecting data with relatively little noise .The report also notes that early samples showed zero detections in common scanning services. That is not the same as being safe, but it does show how much advantage a new campaign can get before signatures, heuristics, or user reports catch up. Freshness remains one of the attacker’s most useful assets .
The use of legitimate tools is a second layer of evasion make malware legal, of course, but it does make the installer feel standard. Electron and Python are everyday technologies, not exotic red flags. And cscript.exe is a built-in Windows component. Together, they create an environment where nothing looks obviously wrong until you assemble the whole chain .
- The Run key disguises itself as a security-related entry.
- The Startup shortcut borrows a familiar consumer name.
- Built-in Windows components help the chain blend in.
- Fresh samples can lag behind detection systems.
- Evasion is often about time, not just stealth.
Microsoft’s Real Update Path
Microsoft’s genuine Windows update flow is much simpler and less dramatic. Users are supposed to use Windows Update in Settings, where Windows checks for and installs updates directly. When Microsoft provides a standalone package or an update history page, it does so through official Microsoft properties and documentation. That distinction is crucial because a real update should not require a suspicious third-party site, especially one that looks like a support page but lives on a lookalike domain .The fake campaign leans on the idea that an update can come from anywhere if it looks official enough. That is false. The domain is the trust anchor, not the logo. A plausible product name does not validate a website, and a polished download button does not prove legitimacy. If anything, this campaign is a reminder that visual polish is not the same thing as provenance .
What Microsoft users should remember
Windows 11 24H2 is a real and active version, which makes it useful for social engineering. But that does not mean every page mentioning 24H2 is trustworthy. The real question is where the file came from, how it is distributed, and whether the path aligns with Microsoft’s official update model. If those answers are vague, the safest assumption is that something is wrong .This also matters for enterprise environments. IT teams often distribute updates through managed channels, patch systems, or internal repositories. A random internet download that claims to be a Microsoft cumulative update should stand out immediately. If it does not, the organization has a bigger process problem than a single phishing page .
Enterprise vs Consumer Impact
For consumers, the risk is mostly about credential theft, browser session hijacking, and account takeover. A h a fake updater may lose saved passwords, cloud access, banking data, or gaming accounts. Because many consumer workflows rely heavily on browser convenience, a single infected profile can expose a broad slice of daily digital life .For enterprises, the implications are broader and more expensive. A compromised endpoint can reveal corporate browser sessions, email access, SaaS tokens, and potentially VPN-related artifacts. The immediate loss may not be a file server breach; it may be a quiet foothold that enables lateral movement or business-email compromise later. That makes the threat especially relevant to organizations that assume browser data is “just personal browsing” .
Different users, same blind spot
Both consumer and enterprise victims share the same blind spot: they kflows. Consumers trust the idea that a patch is meant to protect them. Enterprises trust internal habits and endpoint controls to catch the obvious cases. This campaign works because it turns that trust into an attack surface, and that is a problem no single product can solve by itself .The French-language presentation also suggests a targeted initial audience, though campaigns like this can be ter. Attackers frequently start with one language or region, then adapt based on success. That means the issue is not limited to a single audience or geography; it is a repeatable pattern with a flexible front end .
Strengths and Opportunities
There is one upside to a campaign like this: it exposes exactly where users and defenders still rely on habits instead of verification. The more this kind of attack circulates, the more incentive there is to harden browser hygiene, user training, and update distribution controls. It also gives Microsoft and security vendors a clear case study in how update-themed social engineering is evolving.- It highlights the value of source verification over visual trust.
- It reinforces the case for browser session hygiene and password rotation.
- It gives defenders concrete indicators to hunt for.
- It may improve awareness of typosquatted support domains.
- It shows why managed update channels matter in enterprises.
- It underscores the need to monitor persistence mechanisms.
- It encourages stronger skepticism around standalone “updates.”
Risks and Concerns
The biggest concern is that this style of attack is easy to repeat and hard to kill. Once criminals have a convincing update template, they can swap out versions, file names, and languages while keeping the same basic technique. The more polished the fake support page becomes, the more likely it is to fool users who are already accustomed to clicking update prompts without pausing.- Victims may not notice until after session theft has occurred.
- Browser cookies and tokens can bypass ordinary password changes.
- Persistence can make cleanup more complicated than expected.
- Fresh malware may evade detection at first.
- Organizations may underestimate browser-data exposure.
- Users may confuse polished design with legitimacy.
- Attackers can easily retarget the same playbook.
Looking Ahead
The most likely short-term outcome is that more users will become cautious about any Windows update that arrives outside the normal Windows Update path. That is a good thing, but it will not be enough on its own. The campaign is already designed to survive shallow checks, and attackers will continue refining the site, metadata, and payload chain as long as the lure works.Defenders should expect more of the same with different version numbers, different file names, and possibly different languages. The basic idea is too effective to abandon quickly. If anything, this incident is a preview of how update-themed phishing will evolve: less noisy, more professional, and increasingly built around ordinary tools that users are trained to trust.
- Watch for new typosquatted domains that mimic Microsoft support.
- Watch for copycat campaigns using other Windows version labels.
- Watch for changes in packaging frameworks and script loaders.
- Watch for persistence entries disguised as benign software.
- Watch for broader abuse of browser session theft.
This campaign is a reminder that modern malware often looks less like a hack and more like a service. It arrives with branding, metadata, and workflow design that tries to feel ordinary. The safest response is to remember that in security, ordinary-looking is not the same as trustworthy, and a download that feels like maintenance can still be theft in disguise
Source: extremetech.com Fake Windows 11 24H2 Update Poses as Legit Download to Steal Data