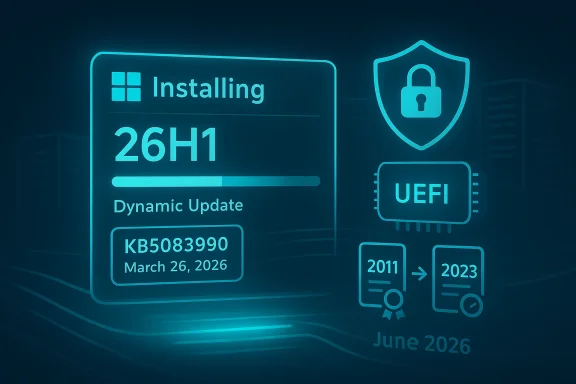
Microsoft’s March 26, 2026 Safe OS Dynamic Update for Windows 11 version 26H1, tracked as KB5081151, lands at a moment when a much bigger platform transition is coming into view: the June 2026 Secure Boot certificate expiration. In practical terms, this is not just another maintenance package. It is part of Microsoft’s broader effort to keep the pre-boot trust chain alive across consumer PCs, commercial fleets, virtualized environments, and managed devices before old 2011-era certificates age out. Microsoft’s support guidance makes clear that devices lacking the newer 2023 certificates will keep booting and continue receiving normal Windows updates, but they will gradually lose access to new early-boot protections and boot-level security updates. (support.microsoft.com)
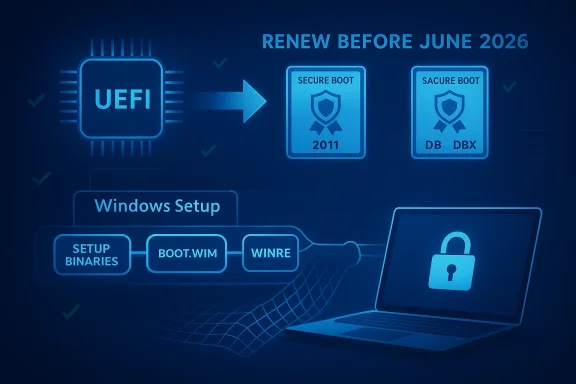
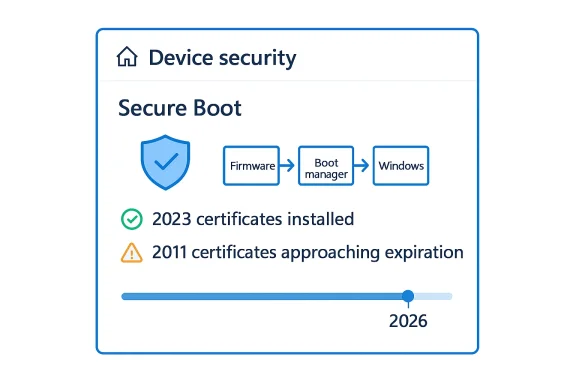
The significance of KB5081151 is easier to understand once you look at the architecture beneath it. Secure Boot is not a Windows feature in the narrow sense; it is a UEFI trust mechanism that validates boot components before the operating system takes control. Microsoft notes that Secure Boot first arrived with Windows 8 to counter pre-boot malware, including bootkits, by verifying firmware modules, boot loaders, and applications during startup. That original design is now entering its next major lifecycle event, because the Microsoft-issued certificates that support that trust chain are approaching expiration. (support.microsoft.com)
The certificates in question are the same broad family that shipped across the Windows and OEM ecosystem for more than a decade. Microsoft says the current KEK, PCA, and UEFI CA certificates were issued in 2011, and those certificates begin expiring in June 2026, with the last of them expiring by October 2026. Microsoft’s guidance is blunt: all Windows devices need to move to the newer 2023 certificates before the older ones lapse if they are to preserve the full Secure Boot update path. That is the core reason Microsoft has been seeding warnings into monthly cumulative updates and out-of-band servicing releases across Windows client and server. (support.microsoft.com)
The public messaging has also become more explicit. Microsoft’s support pages now spell out that devices without the updated certificates will continue to start normally and still install ordinary Windows updates. The catch is security depth: those machines will no longer receive future updates to the Windows Boot Manager, Secure Boot databases, revocation lists, or other mitigations for boot-level vulnerabilities. In other words, the device may remain operational while becoming progressively less resilient. That distinction matters for both home users and enterprise administrators, because the threat model is not immediate failure but reduced long-term trust. (support.microsoft.com)
Microsoft has been preparing the ecosystem for months. The same Secure Boot warning now appears in several cumulative updates across Windows Server and Windows 10/11 servicing lines, and the March 2026 Server 2022 update explicitly says quality updates now include additional “high confidence device targeting data” to increase coverage of devices eligible to automatically receive new Secure Boot certificates. That is the telltale sign of a phased rollout strategy rather than a one-shot migration. It suggests Microsoft wants the certificate transition handled like a broad security campaign, not a manual edge-case remediation. (support.microsoft.com)
The label 26H1 is also notable. Microsoft’s Windows release rhythm has become increasingly fluid, with servicing, enablement, and feature-delivery channels overlapping more than they did in the old major-version era. In that environment, a Safe OS dynamic update can do more than polish setup code; it can ensure that future installation and recovery paths understand the evolving certificate and boot trust state. If Microsoft’s goal is to keep devices recoverable and securable through the Secure Boot transition, then the pre-install and recovery environment is exactly where you would expect the company to harden behavior first. (support.microsoft.com)
This is a particularly important distinction for enterprises. Compliance teams often think in terms of uptime, patching, and endpoint protection status, but Secure Boot lives in a deeper layer: firmware trust, revocation control, and the ability to sign and distribute protections for the boot sequence itself. Once those certificates age out, an organization may still have a healthy-looking inventory that is nonetheless strategically stale. The machine is alive, but the chain of trust is no longer receiving the newest links. (support.microsoft.com)
The fleet challenge is especially tricky because Microsoft says most devices manufactured since 2012 support Secure Boot, but not all devices include the same exact certificate mix in firmware. Microsoft also states that not all devices include the Microsoft Corporation UEFI CA 2011, and on those systems, only the relevant new 2023 certificates need to be applied. That kind of nuance is exactly why blanket assumptions are dangerous. A transition of this scale demands inventory precision, not just policy declarations. (support.microsoft.com)
The consumer case is also shaped by repair and recovery behavior. Safe OS dynamic updates can influence how Windows behaves during resets, reinstalls, and setup flows. If the recovery environment is not aligned with the newer certificate requirements, users could encounter confusion when trying to rebuild a machine after a hardware failure or major issue. That makes KB5081151 potentially more important to ordinary users than the “dynamic update” label suggests. Recovery-time reliability is often where platform transitions become personal. (support.microsoft.com)
There is also a hardware-ecosystem angle. Secure Boot is jointly shaped by Microsoft, OEM firmware, and third-party bootloader ecosystems. If Microsoft can manage the rollover with minimal disruption, it reinforces the idea that Windows can sustain long-lived hardware platforms without sacrificing trust agility. If the rollout goes poorly, by contrast, it risks turning a technical maintenance cycle into an OEM support headache. That is why the company is leaning so hard on guidance, automation, and staged deployment. (support.microsoft.com)
Microsoft’s March 2026 server cumulative update also shows that Secure Boot certificate coverage is being increased by “high confidence device targeting data,” implying that Microsoft is using update telemetry to decide which devices are likely suitable for automatic certificate rollouts. That kind of targeting is a pragmatic response to a messy reality: not every endpoint is equally easy to update, and not every fleet has the same firmware posture. Dynamic updates help smooth those edges by improving the surrounding infrastructure first. (support.microsoft.com)
There is also a subtle competitive angle around firmware trust and platform continuity. The better Microsoft handles certificate rollover, the easier it becomes for OEMs and enterprises to trust future transitions, whether those involve boot policy, device attestation, or next-generation security baselines. That confidence matters because platform security is cumulative. The more the ecosystem trusts Microsoft to manage the boring, low-level stuff well, the easier it is for the company to ask customers to adopt new layers of security later. That compounding trust is strategic capital. (support.microsoft.com)
The most sensible expectation is that Microsoft will keep embedding Secure Boot notices into routine updates while extending the tooling and deployment guidance for IT administrators. That means the next several months are likely to look uneventful on the surface and increasingly important underneath. In Windows platform security, the most consequential changes are often the ones that happen before anyone notices them. That is especially true here. (support.microsoft.com)
Source: Microsoft Support KB5081151: Safe OS Dynamic Update for Windows 11, version 26H1: March 26, 2026 - Microsoft Support
 Background
Background
The significance of KB5081151 is easier to understand once you look at the architecture beneath it. Secure Boot is not a Windows feature in the narrow sense; it is a UEFI trust mechanism that validates boot components before the operating system takes control. Microsoft notes that Secure Boot first arrived with Windows 8 to counter pre-boot malware, including bootkits, by verifying firmware modules, boot loaders, and applications during startup. That original design is now entering its next major lifecycle event, because the Microsoft-issued certificates that support that trust chain are approaching expiration. (support.microsoft.com)The certificates in question are the same broad family that shipped across the Windows and OEM ecosystem for more than a decade. Microsoft says the current KEK, PCA, and UEFI CA certificates were issued in 2011, and those certificates begin expiring in June 2026, with the last of them expiring by October 2026. Microsoft’s guidance is blunt: all Windows devices need to move to the newer 2023 certificates before the older ones lapse if they are to preserve the full Secure Boot update path. That is the core reason Microsoft has been seeding warnings into monthly cumulative updates and out-of-band servicing releases across Windows client and server. (support.microsoft.com)
The public messaging has also become more explicit. Microsoft’s support pages now spell out that devices without the updated certificates will continue to start normally and still install ordinary Windows updates. The catch is security depth: those machines will no longer receive future updates to the Windows Boot Manager, Secure Boot databases, revocation lists, or other mitigations for boot-level vulnerabilities. In other words, the device may remain operational while becoming progressively less resilient. That distinction matters for both home users and enterprise administrators, because the threat model is not immediate failure but reduced long-term trust. (support.microsoft.com)
Microsoft has been preparing the ecosystem for months. The same Secure Boot warning now appears in several cumulative updates across Windows Server and Windows 10/11 servicing lines, and the March 2026 Server 2022 update explicitly says quality updates now include additional “high confidence device targeting data” to increase coverage of devices eligible to automatically receive new Secure Boot certificates. That is the telltale sign of a phased rollout strategy rather than a one-shot migration. It suggests Microsoft wants the certificate transition handled like a broad security campaign, not a manual edge-case remediation. (support.microsoft.com)
What KB5081151 Represents
KB5081151 is listed as a Safe OS Dynamic Update for Windows 11 version 26H1, dated March 26, 2026, and the title itself signals where Microsoft intends it to operate: in the recovery and setup layers rather than the everyday desktop runtime. Safe OS updates are the sort of packages that matter when Windows is being installed, repaired, reset, or serviced in a lower-level environment. That makes them especially relevant in a year when the boot trust chain itself is the story. Even without public page details beyond the title provided by Microsoft Support, the context strongly suggests this update is part of the platform preparation work surrounding the Secure Boot certificate transition. That is an inference, but it is a well-supported one given the timing and Microsoft’s repeated warnings on nearby support pages. (support.microsoft.com)The label 26H1 is also notable. Microsoft’s Windows release rhythm has become increasingly fluid, with servicing, enablement, and feature-delivery channels overlapping more than they did in the old major-version era. In that environment, a Safe OS dynamic update can do more than polish setup code; it can ensure that future installation and recovery paths understand the evolving certificate and boot trust state. If Microsoft’s goal is to keep devices recoverable and securable through the Secure Boot transition, then the pre-install and recovery environment is exactly where you would expect the company to harden behavior first. (support.microsoft.com)
Why the timing matters
The timing is not accidental. Microsoft has been stating for months that the June 2026 window is the point at which the oldest Secure Boot certificates begin expiring, and that systems need to be migrated to the 2023 certificate set in advance. A March 26 dynamic update gives Microsoft room to prepare the servicing stack, recovery media logic, and low-level deployment behavior before the expiration clock gets uncomfortably close. In a security transition like this, lead time is the product. (support.microsoft.com)- It arrives before the June 2026 expiration threshold.
- It fits the pattern of Microsoft seeding Secure Boot warnings into routine updates.
- It likely supports setup, recovery, or installation workflows that need to cope with newer trust material.
- It helps reduce the risk of a last-minute scramble across managed fleets.
How Secure Boot Certificate Expiration Changes the Game
The easiest mistake to make is to assume this is a binary “works/doesn’t work” issue. Microsoft’s own language makes clear that it is subtler than that. Systems that miss the 2023 certificate update can continue booting and can still receive standard Windows updates. What they lose is the ability to receive new security protections for the early boot process, which is where attackers have historically tried to hide because it sits below much of the normal OS defense stack. That means the device’s security posture erodes over time rather than collapsing overnight. (support.microsoft.com)This is a particularly important distinction for enterprises. Compliance teams often think in terms of uptime, patching, and endpoint protection status, but Secure Boot lives in a deeper layer: firmware trust, revocation control, and the ability to sign and distribute protections for the boot sequence itself. Once those certificates age out, an organization may still have a healthy-looking inventory that is nonetheless strategically stale. The machine is alive, but the chain of trust is no longer receiving the newest links. (support.microsoft.com)
What expires, exactly
Microsoft’s guidance breaks the transition into familiar certificate roles. The KEK certificate signs updates to the DB and DBX, the PCA certificate signs the Windows boot loader, and the UEFI CA certificate signs third-party boot loaders and EFI applications. Microsoft also notes that, in some cases, the renewal splits option-ROM signing from boot-loader signing into separate 2023 certificates for finer trust control. That design choice matters: it gives administrators more granular authority over what they trust in firmware, which is especially relevant for heterogeneous fleets. (support.microsoft.com)- Microsoft Corporation KEK CA 2011 expires in June 2026.
- Microsoft Windows Production PCA 2011 expires in October 2026.
- Microsoft Corporation UEFI CA 2011 expires in June 2026.
- The replacement certificates are the 2023 versions now being rolled out.
Enterprise Impact
For IT departments, the Secure Boot transition is as much a fleet-management problem as it is a cryptography problem. Microsoft’s guidance is explicitly written for organizations that manage their own device updates, and it emphasizes preparation, monitoring, deployment, and remediation. That means the operational work spans far beyond Windows Update. Admins need to understand firmware states, deployment channels, and whether particular endpoints even expose the old certificates in firmware. (support.microsoft.com)The fleet challenge is especially tricky because Microsoft says most devices manufactured since 2012 support Secure Boot, but not all devices include the same exact certificate mix in firmware. Microsoft also states that not all devices include the Microsoft Corporation UEFI CA 2011, and on those systems, only the relevant new 2023 certificates need to be applied. That kind of nuance is exactly why blanket assumptions are dangerous. A transition of this scale demands inventory precision, not just policy declarations. (support.microsoft.com)
Deployment is not one-size-fits-all
Microsoft’s enterprise guidance outlines a deployment playbook that includes verifying Secure Boot status across the fleet, determining how updates are deployed, monitoring event logs, and using automated deployment assists where possible. The vendor is also adding new PowerShell scripts to help with verification and preparation. That suggests Microsoft expects the task to be operationalized, not treated as a one-time patch. In practice, this is the sort of update effort that benefits from ring-based rollout, canary devices, and careful rollback planning. (support.microsoft.com)- Verify whether Secure Boot is enabled and what certificate state the device actually has.
- Segment deployment by hardware model and firmware family.
- Monitor early failures through event logs and remediation tooling.
- Use automation wherever possible, but validate firmware behavior first.
- Treat virtualization, VDI, and cloud-managed devices as separate workstreams.
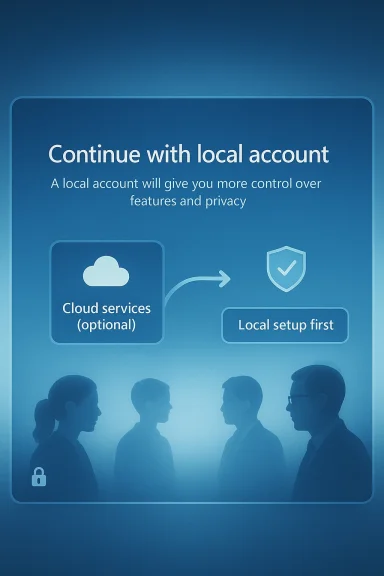
Consumer and Small-Business Impact
For home users, the story is less about certificate inventory and more about whether the machine quietly gets the new trust material through normal servicing. Microsoft says most Windows devices will receive the updated certificates automatically, and many OEMs will provide firmware updates when needed. That is reassuring, but it is not a reason to be passive. Systems that fall behind may not show obvious symptoms until a later stage, which is exactly how silent platform debt becomes visible at the worst possible time. (support.microsoft.com)The consumer case is also shaped by repair and recovery behavior. Safe OS dynamic updates can influence how Windows behaves during resets, reinstalls, and setup flows. If the recovery environment is not aligned with the newer certificate requirements, users could encounter confusion when trying to rebuild a machine after a hardware failure or major issue. That makes KB5081151 potentially more important to ordinary users than the “dynamic update” label suggests. Recovery-time reliability is often where platform transitions become personal. (support.microsoft.com)
What ordinary users should understand
The most important practical point is that this is not a panic item. Microsoft says affected systems will continue to boot and keep getting standard updates even if they miss the certificate transition window, but they will lose future boot-level security protections. That means the right instinct is preparation, not alarm. Users should expect these changes to arrive through Windows Update and OEM firmware channels rather than through any dramatic one-time event. (support.microsoft.com)Why Microsoft Is Doing This Now
The obvious answer is expiration, but the deeper answer is strategic continuity. Microsoft is trying to avoid a repeat of the security fragility that can appear when embedded trust roots age out without replacement. By refreshing Secure Boot certificates before the old set expires, Microsoft preserves the chain needed to sign future boot protections and revocations. That lets Windows continue evolving its early-boot defenses without leaving older machines behind all at once. (support.microsoft.com)There is also a hardware-ecosystem angle. Secure Boot is jointly shaped by Microsoft, OEM firmware, and third-party bootloader ecosystems. If Microsoft can manage the rollover with minimal disruption, it reinforces the idea that Windows can sustain long-lived hardware platforms without sacrificing trust agility. If the rollout goes poorly, by contrast, it risks turning a technical maintenance cycle into an OEM support headache. That is why the company is leaning so hard on guidance, automation, and staged deployment. (support.microsoft.com)
The trust-chain lesson
Secure Boot has always been about protecting the earliest moment of execution. That also means it is unforgiving when the infrastructure behind it ages out. The 2026 expiration is a reminder that security systems are not static artifacts; they are living supply chains of trust. If one generation of certificates is left to expire without migration, the entire update path becomes constrained. (support.microsoft.com)- Certificates are not just administrative paperwork; they are the basis of future security updates.
- Boot-time trust is harder to retrofit than OS-level protection.
- A phased migration reduces fleet-wide shock.
- Missing the window does not break Windows immediately, but it weakens future defenses.
The Role of Dynamic Updates and Safe OS Servicing
Dynamic updates are one of those Microsoft mechanisms that many users never notice, yet they are critical when the company needs to improve installation, setup, or recovery logic without waiting for a full release cycle. In the Secure Boot transition context, that makes them ideal for getting the “safe” environment ready before certificate changes become more consequential. If Windows has to repair itself, reinstall, or provision a new image, the servicing layer needs to understand the new trust assumptions. (support.microsoft.com)Microsoft’s March 2026 server cumulative update also shows that Secure Boot certificate coverage is being increased by “high confidence device targeting data,” implying that Microsoft is using update telemetry to decide which devices are likely suitable for automatic certificate rollouts. That kind of targeting is a pragmatic response to a messy reality: not every endpoint is equally easy to update, and not every fleet has the same firmware posture. Dynamic updates help smooth those edges by improving the surrounding infrastructure first. (support.microsoft.com)
Why this matters for imaging and recovery
The biggest understated risk in certificate transitions is not the everyday desktop but the re-image path. Organizations frequently discover platform problems only when a machine is wiped, repaired, or restored. A Safe OS dynamic update can reduce that risk by ensuring newer setup logic and recovery components are in place before the transition becomes unavoidable. In other words, it is a preventative move aimed at the moments when Windows is most vulnerable to inconsistency. (support.microsoft.com)Competitive and Ecosystem Implications
The Secure Boot rollover is not just a Microsoft story; it is an ecosystem story. Windows competes partly on its ability to support diverse OEM hardware, manage security at scale, and keep enterprise deployments stable over long device lifecycles. If Microsoft handles the 2026 certificate migration smoothly, it strengthens the argument that Windows remains the most operationally mature platform for mixed hardware fleets. If it stumbles, rivals will point to the complexity as evidence that the Windows ecosystem still carries too much legacy burden. (support.microsoft.com)There is also a subtle competitive angle around firmware trust and platform continuity. The better Microsoft handles certificate rollover, the easier it becomes for OEMs and enterprises to trust future transitions, whether those involve boot policy, device attestation, or next-generation security baselines. That confidence matters because platform security is cumulative. The more the ecosystem trusts Microsoft to manage the boring, low-level stuff well, the easier it is for the company to ask customers to adopt new layers of security later. That compounding trust is strategic capital. (support.microsoft.com)
Effects on third-party boot ecosystems
Third-party bootloaders and EFI applications are particularly sensitive to Secure Boot database changes. Microsoft’s updated certificate structure intentionally separates some trust roles so administrators can make narrower choices about what to trust, especially around option ROMs versus boot loaders. That may seem like an obscure detail, but it can matter greatly for specialty hardware, enterprise security tools, and alternative OS configurations. The certificate renewal is therefore not only about preservation; it is also about governance. (support.microsoft.com)- More granular trust control could reduce unnecessary exposure.
- Third-party boot ecosystem vendors will need to validate compatibility.
- OEM firmware update quality becomes more important, not less.
- Enterprise mixed-OS environments may need closer testing.
Strengths and Opportunities
The strongest part of Microsoft’s approach is that it is happening early enough to be manageable, and the company is framing the issue in operational rather than alarmist terms. It is also pushing updates across multiple servicing channels, which increases the odds that ordinary devices and managed fleets both get the message in time. Just as important, the new certificate structure offers more granular trust control, which is a rare example of a security migration that can actually improve governance while preserving continuity. That is a meaningful upside for long-term platform stability. (support.microsoft.com)- Early warning gives enterprises planning time.
- Automatic rollout reduces the burden on average users.
- Separation of boot-loader and option-ROM trust can improve precision.
- Broad support coverage increases the chance of ecosystem-wide consistency.
- Dynamic updates can harden recovery and setup paths.
- Microsoft’s guidance is detailed enough to support real fleet operations.
- The migration can strengthen confidence in Windows firmware security over time.
Risks and Concerns
The biggest risk is uneven rollout. Microsoft itself acknowledges that some devices may not receive updates automatically, that certain firmware configurations vary, and that organizations managing their own endpoints need to test and verify carefully. The second risk is complacency: because affected devices will keep booting and keep receiving standard Windows updates, many users may underestimate the security debt they are accumulating. That is the sort of problem that usually surfaces after the deadline, not before it. (support.microsoft.com)- Some devices may fall through the automatic-update cracks.
- OEM firmware quality will shape real-world success.
- Enterprises may not have accurate Secure Boot inventory data.
- Users may confuse “still works” with “fully protected.”
- Recovery and re-image scenarios can expose hidden compatibility issues.
- Third-party boot software could encounter trust mismatches.
- Late remediation may be more expensive than early planning.
Looking Ahead
What happens next depends on whether Microsoft can keep the certificate migration quiet. If the company’s staged rollout continues to spread the 2023 certificates across the installed base, then June 2026 becomes a managed milestone rather than a disruption point. If not, the industry may face a wave of support issues, especially from organizations that assumed Secure Boot was one of those invisible features that would take care of itself indefinitely. The evidence so far suggests Microsoft is trying very hard to avoid that outcome. (support.microsoft.com)The most sensible expectation is that Microsoft will keep embedding Secure Boot notices into routine updates while extending the tooling and deployment guidance for IT administrators. That means the next several months are likely to look uneventful on the surface and increasingly important underneath. In Windows platform security, the most consequential changes are often the ones that happen before anyone notices them. That is especially true here. (support.microsoft.com)
Watch these items closely
- Whether KB5081151 is followed by more setup and recovery-oriented servicing changes.
- How Microsoft expands automated Secure Boot certificate targeting.
- Whether OEM firmware updates arrive consistently across major device lines.
- How enterprises report success or friction in certificate deployment.
- Whether Microsoft adds further warnings to upcoming cumulative updates.
Source: Microsoft Support KB5081151: Safe OS Dynamic Update for Windows 11, version 26H1: March 26, 2026 - Microsoft Support
Last edited: