For millions of home users and dozens of industries that still run legacy printing fleets, January 15, 2026 will be remembered as the date Microsoft slammed the brakes on the distribution of legacy V3 and V4 printer drivers through Windows Update — a staged, multi‑year shift that puts older printers on borrowed time and forces IT teams and consumers to confront a simple truth: the Windows printing ecosystem is being modernized, and vendor‑specific drivers are no longer the default path forward.
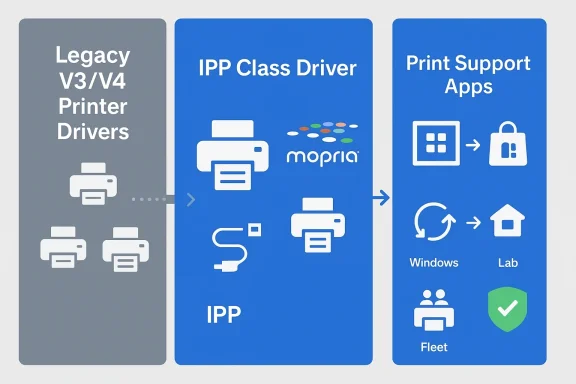
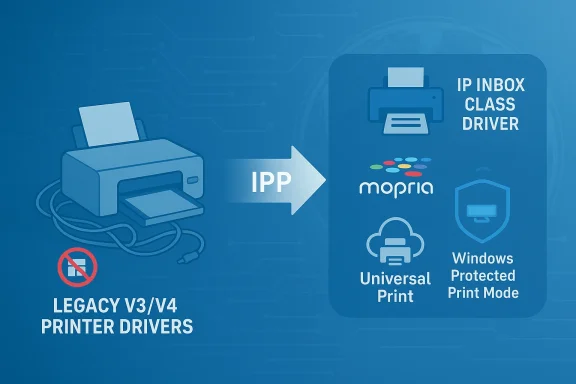
Microsoft began signaling this transition publicly in September 2023. The company’s long‑term plan centers on the modern print platform — an Internet Printing Protocol (IPP)-first architecture, the Microsoft IPP class driver, and complementary services such as Universal Print and Windows Protected Print Mode. Rather than continue to accept, certify and distribute thousands of vendor‑specific V3 and V4 drivers via Windows Update, Microsoft is redirecting the ecosystem toward standardized, inbox solutions and cloud services that reduce complexity and, importantly, the attack surface associated with third‑party print drivers.
This change is staged across clearly defined milestones. Microsoft’s plan moves from a deprecation announcement to a hard stop on new legacy drivers appearing on Windows Update (January 15, 2026 for Windows 11 and Windows Server 2025+), followed by changes in driver selection behavior (July 1, 2026) and a limitation on third‑party driver updates to security fixes only (July 1, 2027). The phased approach is explicit: existing drivers are not being forcibly deleted en masse today, but the operating rules for driver distribution and preference are changing in ways that will reshape how printers are installed and maintained on Windows devices.
Recommended actions:
High‑value actions for IT:
Actionable guidance:
Winners:
The era of treating printers as peripheral second‑class citizens in IT management is ending. Microsoft’s decision to stop distributing new V3/V4 drivers via Windows Update forces a clear, if uncomfortable, choice: modernize the printing estate now or accept growing operational and security risk later. For the cautious IT pro, the immediate imperative is to inventory, prioritize and engage — and to convert an inevitable change into a controlled migration rather than an emergency.
Source: Inbox.lv Total Shutdown: Printers Stop Working with Windows
 Background
Background
Microsoft began signaling this transition publicly in September 2023. The company’s long‑term plan centers on the modern print platform — an Internet Printing Protocol (IPP)-first architecture, the Microsoft IPP class driver, and complementary services such as Universal Print and Windows Protected Print Mode. Rather than continue to accept, certify and distribute thousands of vendor‑specific V3 and V4 drivers via Windows Update, Microsoft is redirecting the ecosystem toward standardized, inbox solutions and cloud services that reduce complexity and, importantly, the attack surface associated with third‑party print drivers.This change is staged across clearly defined milestones. Microsoft’s plan moves from a deprecation announcement to a hard stop on new legacy drivers appearing on Windows Update (January 15, 2026 for Windows 11 and Windows Server 2025+), followed by changes in driver selection behavior (July 1, 2026) and a limitation on third‑party driver updates to security fixes only (July 1, 2027). The phased approach is explicit: existing drivers are not being forcibly deleted en masse today, but the operating rules for driver distribution and preference are changing in ways that will reshape how printers are installed and maintained on Windows devices.
Why Microsoft did this — the technical and security case
The Windows print stack has been a perennial challenge for OS reliability and security teams. A few technical realities underpin Microsoft’s move:- Legacy driver models (V3 and V4) are vendor‑specific and often include installers, port monitors, kernel mode components and other modules that increase system complexity. Each extra module is an opportunity for misconfiguration or exploitation.
- High‑profile spooler vulnerabilities — most notably the family of issues collectively known as PrintNightmare — demonstrated how print driver installation and spooler behavior could be weaponized for remote code execution and local privilege escalation. That episode catalyzed a reexamination of how printing integrates with core OS services.
- Managing, certifying and distributing thousands of bespoke drivers via Windows Update consumes engineering and QA resources and introduces variability in behavior across hardware, architectures, and updates.
- Modern standards such as IPP, eSCL and Mopria compliance enable vendor‑agnostic features for printing and scanning over both network and USB connections, removing many historical reasons to rely on third‑party packages.
What changed on January 15, 2026 — the practical impact
The most commonly cited change is blunt: Microsoft stopped publishing new legacy V3/V4 third‑party printer drivers to Windows Update for Windows 11 and Windows Server 2025+. That means:- New legacy driver submissions to Windows Update are blocked by default and will require manual justification and special approval.
- Existing legacy drivers already published to Windows Update remain available for installation and in many cases will continue to function.
- Over the next 12–18 months Microsoft will change the driver ranking order to prefer the Microsoft IPP inbox class driver. In practical terms, Windows will default to class/inbox drivers rather than opting for a vendor package in many add‑printer flows.
- Eventually, starting in mid‑2027, third‑party driver updates via Windows Update will be limited primarily to security fixes — feature and non‑security fixes will be largely excluded.
Separating fact from alarmism: will my old printer stop working immediately?
Short answer: Not automatically. Long answer: it depends.- If your printer already uses an installed V3/V4 driver that was previously delivered via Windows Update, that driver typically remains present and functional — the device will not instantly stop printing just because Microsoft stopped publishing new driver packages.
- The pain points arise when a user tries to add a printer (new install), when device drivers are removed as part of a system refresh, or when a Windows Update changes driver ranking to prefer IPP class drivers. In those cases the OS may attempt to use the modern inbox driver instead of installing the legacy vendor package — which can be good (simpler, standard feature set) or bad (loss of vendor‑specific features like advanced finishing, secure release or scanner functionality).
- Reports claiming a “total shutdown” of printers are often overstated. Many journalists and social posts conflate the discontinuation of driver distribution with immediate device inoperability. That said, for specific older models — especially those reliant on deeply integrated vendor software — the transition will be disruptive and some devices will require vendor updates, workarounds, or replacement.
What this means for different audiences
Home users and small offices
If you own a consumer printer bought in the last 5–8 years, chances are it already supports IPP/eSCL or has a modern driver that will continue working. If you have a decade‑old multifunction device that required a vendor package, expect potential friction when reinstalling it or upgrading your PC.Recommended actions:
- Before upgrading or applying big OS changes, create a simple inventory: note the make and model, driver type and whether the manufacturer still lists downloads for that model.
- Try to install the printer using Windows’ built‑in “Add a printer” flow; if Windows selects the IPP inbox driver, test core functions (print, scan, fax) to see if the modern stack meets your needs.
- If a vendor installer is necessary, download the latest package from the manufacturer’s site and install it manually. The driver package may still be installable even though it won’t be distributed via Windows Update.
- Be skeptical about advice to "downgrade" to Windows 10 as a permanent fix. Windows 10 reached end of support on October 14, 2025; while existing installations may run, they no longer receive security updates unless you purchase Extended Security Updates (ESU). Using an out‑of‑support OS as a long‑term workaround is a risky trade‑off in security.
IT admins and enterprise teams
Enterprises with mixed fleets must treat this as a change control and asset‑management problem, not just a helpdesk surge. The move gives IT an opportunity to modernize print infrastructure — but it also raises short‑term operational risk.High‑value actions for IT:
- Inventory your estate now. Use native tools and scripts to capture models, installed driver packages and timestamps. Useful commands:
- pnputil /enum-drivers
- Get‑PrinterDriver (PowerShell PrintManagement module)
- Get‑Printer
- pnputil /enum-drivers /files /format CSV /output-file DriverInventory.csv
- Categorize devices:
- Mopria/IPP/eSCL compatible — candidates for modern print migration.
- Vendor‑specific features required (secure print, badge auth, finishing) — require vendor engagement.
- End‑of‑life models — plan replacement windows and budget accordingly.
- Pilot Windows Protected Print Mode and Universal Print in controlled segments. Protected Print Mode forces modern print usage and reduces driver complexity; Universal Print can remove the need for local drivers entirely in many scenarios.
- Maintain a fallback plan: a legacy print server running an older OS (air‑gapped and tightly controlled) can be used to preserve vendor features for a narrow set of machines while you migrate the rest of the estate. However, such servers must be isolated, patched where possible and monitored.
- Engage vendors early. Ask for IPP/eSCL firmware updates, Print Support Apps for the Microsoft Store model, or signed installer packages that can be deployed via Intune or SCCM.
SMBs, healthcare, manufacturing and regulated industries
These environments often have specialized printers (labelers, PACS attachments, multi‑function devices with advanced scanning workflows). The combination of device age and regulatory compliance means that disruption is risk‑intolerant.Actionable guidance:
- Map printers to business processes — which printers are critical for revenue, compliance, or patient safety.
- Prioritize hardware refreshes for critical devices where vendor support is unavailable or where modern standards can’t replicate required features.
- If replacement is not immediate, establish hardened print servers and network segmentation to reduce exposure from legacy drivers.
Migration paths and remediation options
Below are realistic options ranked from least to most disruptive.- Check for a vendor update or signed installer (low disruption)
- Many OEMs will still host drivers and installers directly on their sites. Use manufacturer installers to restore functionality where Windows Update no longer provides packages.
- Use the modern print stack (IPP/eSCL/Mopria) (low to medium)
- If your device is Mopria‑certified, the modern stack will often provide printing (and sometimes scanning) without vendor drivers. Enabling Windows Protected Print Mode forces devices to use the modern platform.
- Universal Print (cloud) (medium)
- For organizations with Microsoft 365 entitlements, Universal Print can remove the need for endpoint drivers entirely. Universal Print Anywhere (pull print) also solves secure release and mobility issues for distributed workplaces.
- Local print server or virtualization (medium to high)
- Maintain a hardened, dedicated print server with vendor drivers for machines that require them. Consider isolating the print server network access and tight change control.
- Replace unsupported hardware (high cost, long term benefit)
- Procure Mopria‑certified or Universal Print‑ready devices as part of refresh cycles. Prioritize devices that support IPP over USB and network IPP to minimize driver dependence.
- Extended Security Updates (ESU) for Windows 10 (short‑term stopgap)
- If stakeholders advise “go back to Windows 10” as a fix, remember Windows 10 mainstream support ended October 14, 2025. ESU can extend security patches through an additional window, but it costs money, may require enrollment rules (Microsoft account linking) and is explicitly not a long‑term strategy.
Detailed, practical steps for administrators
Step 1 — Inventory (one‑time audit)
- Run pnputil to list driver packages:
- Open an elevated Command Prompt and run: pnputil /enum-drivers /files /format CSV /output-file C:\Temp\DriverInventory.csv
- Use PowerShell to list installed printers and drivers:
- Open an elevated PowerShell:
- Import-Module PrintManagement
- Get-Printer | Select Name, DriverName, PortName | Export-Csv C:\Temp\Printers.csv -NoTypeInformation
- Get-PrinterDriver | Select Name, Manufacturer, Version | Export-Csv C:\Temp\PrinterDrivers.csv -NoTypeInformation
- Correlate model numbers with vendor support pages and Mopria certification lists.
Step 2 — Classify and prioritize
- Tag printers as critical, business‑important, or non‑essential.
- Identify dependencies like scanning workflows, secure release, or SDK integrations.
Step 3 — Pilot modern print and Protected Print Mode
- Select a non‑critical segment and enable Windows Protected Print Mode on a handful of devices.
- Validate that Mopria‑certified devices re-install using the modern stack and test scanning and finishing behavior.
- Monitor helpdesk tickets and user satisfaction.
Step 4 — Vendor engagement
- Open support cases with OEMs for models that fail under the modern stack.
- Request signed driver packages or Print Support Apps that can be managed centrally.
Step 5 — Migration and enforcement
- For wide deployments, use group policy or Intune to enable Protected Print Mode where appropriate.
- Roll out Universal Print for shared environments to remove driver distribution headaches entirely.
The vendor responsibility problem — and the market response
One recurring theme of this transition is vendor behavior. Hardware OEMs have varying incentives to update firmware, certify Mopria compliance or provide modern print support for models that are at or near end of sale. Two realistic outcomes are likely:- OEMs update popular models and provide Print Support Apps or signed installers that IT can deploy; this reduces friction and maintains features.
- OEMs stop supporting old models, leaving customers to choose between replacing hardware or accepting limited functionality under the modern stack.
Security tradeoffs and the policy tension
Microsoft’s move is primarily security‑driven; consolidating driver paths reduces injection points for malicious modules and simplifies auditing. But there are tradeoffs:- Short‑term availability risk for legacy printers. Customers may lose vendor‑specific functions or face reinstallation failures during OS upgrades.
- Procurement and refresh costs are real for cash‑constrained organizations that use printers intensively (hospital imaging centers, manufacturing lines, postal systems).
- Reliance on cloud services like Universal Print raises operational and privacy considerations (data custody, authentication requirements) that must be evaluated under each organization’s compliance model.
What should consumers say to support and retail staff?
If you call your printer manufacturer or a reseller, be prepared with three things:- The exact model and serial number of the device.
- The driver package currently installed (if present) and how it was obtained (Windows Update or manufacturer download).
- The Windows build and edition (e.g., Windows 11 24H2, Home/Pro/Enterprise).
Final analysis — who wins and who loses?
Microsoft’s goals — improved security, fewer unreliable third‑party modules, and a simpler support model — are technically sound. The modern print platform and Universal Print offer a clear long‑term path away from brittle, vendor‑specific ecosystems.Winners:
- Organizations that have already standardized on Mopria‑certified or Universal Print‑ready devices.
- IT teams that prioritize security and are ready to modernize print workflows (cloud print, secure release).
- End users who will eventually enjoy more consistent, installer‑free printing experiences.
- Owners of older, vendor‑driver‑dependent printers that are no longer maintained.
- Small businesses and public sector customers with tight refresh budgets and mission‑critical printers tied to legacy workflows.
- IT teams that lack the resources to inventory, test and migrate printing fleets quickly.
Quick checklist — what to do in the next 30 days
- Inventory printers and drivers across endpoints and servers.
- Identify critical devices and validate whether they function with the modern print stack.
- Pilot Windows Protected Print Mode in a small user group.
- Engage OEMs for signed drivers or Print Support Apps.
- Evaluate Universal Print for high‑density or mobile printing scenarios.
- Plan procurement that prioritizes Mopria certification and modern print capabilities.
- Avoid recommending Windows 10 as a long‑term fix; its mainstream support window closed in October 2025 and extended security options are temporary and potentially costly.
The era of treating printers as peripheral second‑class citizens in IT management is ending. Microsoft’s decision to stop distributing new V3/V4 drivers via Windows Update forces a clear, if uncomfortable, choice: modernize the printing estate now or accept growing operational and security risk later. For the cautious IT pro, the immediate imperative is to inventory, prioritize and engage — and to convert an inevitable change into a controlled migration rather than an emergency.
Source: Inbox.lv Total Shutdown: Printers Stop Working with Windows