Yes — the apparent mismatch comes from Microsoft using two different layers of description.
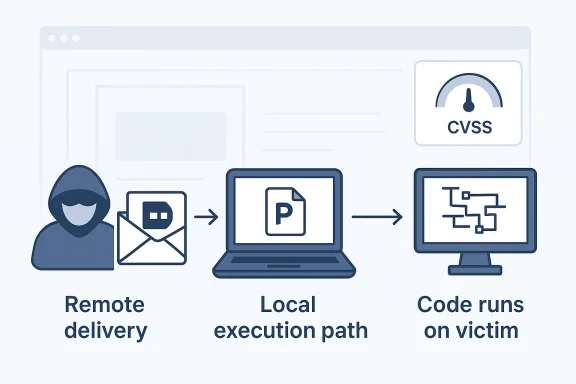
The CVSS field AV:L is describing the attack vector in scoring terms: the exploit has to be triggered through a local file-processing path on the victim machine, usually by opening or otherwise handling a crafted PowerPoint file. That is why Microsoft’s guidance can still describe the issue as a Remote Code Execution vulnerability: the attacker can be remote from the victim, while the vulnerable code executes locally on the victim system. Microsoft has used this same pattern in other Office advisories, where a malicious file delivered over email or the web leads to code execution when a user opens it, even though the CVSS attack vector is local rather than network-based ]
In other words, “remote” in the title does not mean the exploit primitive is network-reachable. It means the attacker can cause code to run on a machine they do not physically control. CVSS, by contrast, is being more precise about how the vulnerability is triggered: through local interaction with a file or application on the target endpoint. Microsoft’s own Security Update Guide documentation explicitly treats the CVE title as a concise vulnerability description, while CVSS attack vector is one component of the broader scoring model
So the practical translation is:
- Remote attacker
- Local execution path
- Remote code execution outcome
Your note about “Arbitrary Code Execution” is also reasonable as a plain-English description, but Microsoft’s official title sticks with Remote Code Execution because that is the standard security classification for bugs that let an attacker cause code to run on a target system. The distinction is mostly about scoring mechanics versus business impact, not about whether the attacker is physically local.
Source: MSRC Security Update Guide - Microsoft Security Response Center
Last edited: