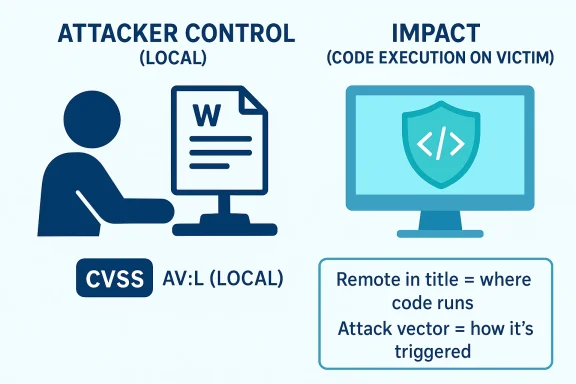
Microsoft’s use of “Remote Code Execution” in a CVE title does not always mean the exploit is launched over the network from a distant attacker. In Microsoft’s terminology, the label describes the impact of the bug: if exploited successfully, it can let an attacker run code on the target system. The CVSS attack vector is a separate field, and Microsoft has explicitly said that a local attack vector is equivalent to “log on to affected system.”
That is the key distinction here. A vulnerability can be categorized as remote code execution because the end result is arbitrary code running on the victim’s machine, while still requiring a local prerequisite such as opening a crafted file, running a local process, or otherwise interacting with Word on the affected machine. Microsoft has repeatedly used that pattern in past advisories: the exploit path may be local or require user interaction, yet the outcome is still RCE because code executes in the victim’s security context.
So for CVE-2026-23657, the title is describing the security consequence of exploitation, not necessarily the attack route. If the Security Update Guide lists AV:L, that tells you the attacker must already be local to the system, have the victim execute something locally, or otherwise satisfy a local prerequisite. The “remote” in the title is about where the code execution occurs relative to the attacker’s control, not about the CVSS attack vector.
In practical terms, think of it this way:
- CVSS AV:L = the attacker must exploit the flaw from a local foothold or through a local action on the target machine.
- Remote Code Execution = the bug can still lead to arbitrary code running on the victim system, even though the triggering condition is local.
- Microsoft uses both labels together when the exploit path is local but the impact is full code execution.
Source: MSRC Security Update Guide - Microsoft Security Response Center