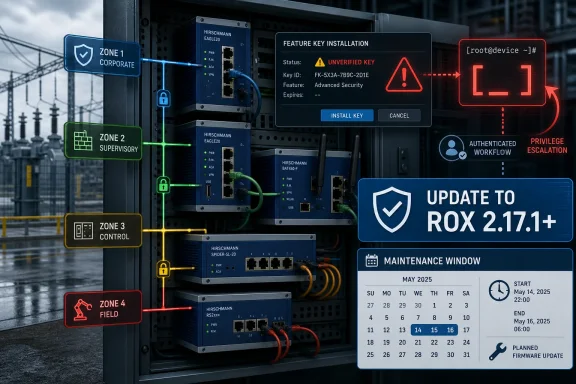
Siemens disclosed on May 12, 2026, that RUGGEDCOM ROX versions before 2.17.1 contain CVE-2025-40947, an authenticated remote command-injection flaw in the feature key installation process affecting MX5000, MX5000RE, RX1400, RX1500, RX1501, RX1510, RX1511, RX1512, RX1524, RX1536, and RX5000 devices worldwide. CISA republished the advisory on May 14, widening visibility for operators in critical manufacturing and other industrial environments. The bug is not a drive-by internet apocalypse, but it is exactly the kind of boring, privileged foothold that becomes dangerous inside flat or poorly segmented OT networks. Siemens’ fix is simple on paper — update to ROX 2.17.1 or later — while the operational reality is the harder story.
The vulnerable code path sits in the feature key installation process, which sounds like a licensing chore rather than a security boundary. That is why this advisory deserves more attention than its CVSS v3.1 score of 7.5 might suggest. Industrial systems are full of administrative workflows that are treated as trusted maintenance functions, and attackers love trusted maintenance functions because they often bridge the gap between a web UI, a management account, and the underlying operating system.
Siemens says affected devices fail to properly sanitize user-supplied input during that process. In plain English, a remote attacker who already has low-level authenticated access could inject operating-system commands and have them run as root. That last phrase is the important one: this is not merely a configuration bypass or a nuisance crash, but a path from authenticated management access to full control of the device’s host operating environment.
The advisory’s CVSS vector tells the same story in a dry dialect. Network access is enough, user interaction is not required, privileges are required, and confidentiality, integrity, and availability impacts are all rated high. Attack complexity is rated high, which moderates the score, but the destination is still root.
That is the awkwardness of OT risk scoring. A vulnerability can be meaningfully constrained and still be strategically serious. If a device is correctly isolated, tightly administered, and monitored, this is a patch-management item. If the same device sits in a management VLAN shared with jump boxes, engineering workstations, legacy tooling, and reused credentials, it becomes a post-authentication escalation route in infrastructure that usually does not tolerate surprises well.
Industrial networking gear has a different threat profile from laptops and servers. It may run for years in locations that are inconvenient to reach, under maintenance windows negotiated around production schedules, safety requirements, and regulatory controls. It may also act as connective tissue between zones that engineers assumed were separate enough, until an incident proves otherwise.
The affected list spans the ROX II family across MX and RX models, including MX5000, MX5000RE, RX1400, RX1500, RX1501, RX1510, RX1511, RX1512, RX1524, RX1536, and RX5000. Siemens marks all versions before 2.17.1 as affected. That is a clean boundary for asset owners, but also a blunt one: either the device is on 2.17.1 or later, or it belongs in the remediation queue.
For WindowsForum readers, the Windows angle is not that this is a Windows vulnerability. It is that Windows administrators increasingly own, touch, or defend the systems around these devices. The engineering workstation, the jump host, the patch repository, the VPN endpoint, the SIEM connector, and the credential store are often Windows-adjacent. A root compromise on an OT network device may begin outside Windows, but it can quickly become part of the same incident response map.
An attacker does not need to be the original administrator if they can obtain a valid account through phishing, password reuse, exposed remote access, a compromised engineering laptop, or a poorly protected vendor maintenance path. Once inside the operational environment, the attacker’s challenge becomes privilege expansion and persistence. A command-injection flaw in a device management function is tailor-made for that phase.
The advisory says the attacker needs remote authenticated access and can then execute arbitrary commands as root. That is a classic post-compromise amplifier. It may not be the first exploit in the chain, but it can turn an account with limited device-level privileges into practical control over the box.
This is why “not internet reachable” is necessary but insufficient. CISA’s familiar guidance — minimize exposure, isolate control-system networks, use firewalls, and prefer secure remote-access methods such as updated VPNs — is still correct. Yet the deeper point is that organizations should assume some authenticated access will eventually be abused. The defensive question is whether that access can reach the vulnerable management surface in the first place.
Unlike a browser update, a network-device firmware update can carry routing, redundancy, management, and availability concerns. A switch or router in a substation, plant floor, or transportation cabinet may have dependencies that are undocumented, tribal, or simply old. Firmware updates can be routine in well-run environments, but they are rarely trivial where uptime obligations dominate.
That does not mean organizations should postpone the fix into oblivion. It means they should treat the advisory as a reason to inventory first, test fast, and deploy in controlled waves. The version threshold is unambiguous: anything below 2.17.1 is in scope.
The worst response would be to file this under “requires authentication” and wait for the next scheduled annual maintenance cycle. The better response is to identify exposed management interfaces, review who can authenticate to them, restrict access immediately, and then plan the firmware move. Compensating controls are not a substitute for patching, but they buy down risk while operations teams do the careful work.
The republication also places the flaw in the context of critical manufacturing, worldwide deployment, and Germany-based Siemens as the vendor. Those labels are not decoration. They help security teams prioritize advisories across sprawling industrial inventories where no single administrator may know every fielded model by memory.
CISA repeats the standard industrial-control recommendations: minimize network exposure, avoid internet accessibility for control-system devices, place control networks behind firewalls, isolate them from business networks, and use secure remote-access methods when remote access is unavoidable. The phrasing is familiar because the pattern is familiar. Most ICS incidents are not magic; they are the result of reachable systems, weak segmentation, credential problems, and slow remediation colliding with vulnerable software.
The agency also reminds organizations to perform impact analysis and risk assessment before deploying defensive measures. That caveat is important. In OT, a hasty security fix that disrupts operations can itself become a safety or availability event. Mature security teams do not choose between patching and operational analysis; they make the analysis part of the patching process.
Modern industrial devices are software platforms with web interfaces, feature flags, cryptographic components, package dependencies, and remote administration. They may be ruggedized physically, but the software attack surface is increasingly recognizable to anyone who has audited enterprise infrastructure. The difference is that the devices are bolted into environments where disruption is expensive and change is slow.
The feature key angle is especially revealing. Licensing and entitlement workflows often receive less security scrutiny than login pages or exposed APIs, yet they parse externally supplied material and may run privileged system routines. If that parsing is sloppy, the licensing path becomes an execution path.
The lesson for vendors is not simply “sanitize input,” though that is the direct flaw here. The larger lesson is that any administrative workflow crossing from user-controlled data into privileged operating-system behavior must be treated as hostile by default. The fact that a feature is used by administrators does not make its input safe.
That shift cuts both ways. More researchers mean more vulnerabilities found and reported before criminals or state-backed actors can exploit them. It also means asset owners should expect a steady drumbeat of advisories against equipment that once felt obscure enough to be safe by default.
Industrial defenders sometimes resent that drumbeat because it creates work without creating new budget. But visibility is not the enemy. The enemy is an environment where vulnerabilities remain unknown until they are used in an incident.
The healthiest reading of this advisory is therefore not panic, but confirmation. The device family is important enough to attract serious research, the vendor has issued a fix, and public-sector channels are amplifying the remediation message. That is how coordinated disclosure is supposed to work. The remaining risk lives in the gap between disclosure and deployment.
The affected model list is specific enough for a targeted hunt. Security and operations teams should search configuration management databases, network discovery tools, procurement records, diagrams, backup configs, and field inventories for ROX MX5000, MX5000RE, RX1400, RX1500, RX1501, RX1510, RX1511, RX1512, RX1524, RX1536, and RX5000 devices. They should then verify firmware versions rather than assuming procurement age maps neatly to software state.
For Windows-heavy teams, this is where enterprise tooling can help but not finish the job. Vulnerability scanners, NAC systems, SIEM logs, privileged-access records, and remote-management platforms may reveal parts of the picture. OT teams may still need to confirm through vendor tools, console access, maintenance records, or site-level inspections.
The key is to avoid turning this into a purely paperwork-driven exercise. A spreadsheet that says “RUGGEDCOM switch, patched” is not evidence. A verified version number, a change ticket, a backup, and a rollback plan are evidence.
Restricting management access is the fastest compensating measure. Administrative interfaces should be reachable only from dedicated management stations, jump hosts, or tightly controlled network segments. Accounts should be reviewed, dormant credentials removed, and shared passwords eliminated where possible.
Logs matter too, though embedded-device logging can be uneven. Teams should look for unexpected feature key installation activity, failed or unusual administrative actions, suspicious command execution artifacts where available, and management logins from unfamiliar hosts. The advisory does not describe known exploitation, but waiting for public exploitation before reviewing logs would be backward.
Remote access deserves special scrutiny. VPNs are often the sanctioned answer for OT maintenance, but CISA’s reminder that VPNs must themselves be updated is not a throwaway line. A VPN only narrows the door; it does not guarantee that whoever walks through it should be trusted with every device behind it.
If an attacker gains root on a network device, they may be able to alter traffic visibility, weaken segmentation, tamper with routing, pivot toward engineering stations, or create persistence that survives ordinary endpoint remediation. Even if the device is not directly involved in Windows authentication, it may sit on the path between Windows systems and industrial assets. Network infrastructure is not just another endpoint; it is the terrain.
This is also why enterprise security teams should stop treating OT advisories as someone else’s queue. The first affected object may be a Siemens device, but the response may involve Active Directory groups, privileged-access management, certificate stores, firewall rules, remote desktop gateways, Windows jump servers, backup validation, and SIEM detection engineering.
The forum audience knows this pattern from ransomware cases in ordinary IT. The first bug is rarely the whole incident. What matters is how many doors it opens after the attacker gets in.
Risk ranking should start with reachability and role. Devices with management interfaces reachable from broad enterprise networks, shared remote-access environments, or third-party maintenance paths should move first. Devices that sit at segmentation boundaries or carry traffic for critical operations deserve special attention because their compromise can alter what defenders see and what operators can trust.
Organizations should also consider account exposure. If ROX administrative credentials are shared, stale, stored in scripts, or known to multiple vendors, the authenticated requirement becomes much less reassuring. A vulnerability requiring credentials is only as constrained as the credential ecosystem around it.
Finally, patch planning should include configuration backups and recovery rehearsals. Updating firmware without a clean rollback and verified configuration state is how routine maintenance becomes an outage. Security urgency is real, but industrial networks punish improvisation.
Source: CISA Siemens Ruggedcom Rox | CISA
 A License-Key Workflow Became a Root Shell Boundary
A License-Key Workflow Became a Root Shell Boundary
The vulnerable code path sits in the feature key installation process, which sounds like a licensing chore rather than a security boundary. That is why this advisory deserves more attention than its CVSS v3.1 score of 7.5 might suggest. Industrial systems are full of administrative workflows that are treated as trusted maintenance functions, and attackers love trusted maintenance functions because they often bridge the gap between a web UI, a management account, and the underlying operating system.Siemens says affected devices fail to properly sanitize user-supplied input during that process. In plain English, a remote attacker who already has low-level authenticated access could inject operating-system commands and have them run as root. That last phrase is the important one: this is not merely a configuration bypass or a nuisance crash, but a path from authenticated management access to full control of the device’s host operating environment.
The advisory’s CVSS vector tells the same story in a dry dialect. Network access is enough, user interaction is not required, privileges are required, and confidentiality, integrity, and availability impacts are all rated high. Attack complexity is rated high, which moderates the score, but the destination is still root.
That is the awkwardness of OT risk scoring. A vulnerability can be meaningfully constrained and still be strategically serious. If a device is correctly isolated, tightly administered, and monitored, this is a patch-management item. If the same device sits in a management VLAN shared with jump boxes, engineering workstations, legacy tooling, and reused credentials, it becomes a post-authentication escalation route in infrastructure that usually does not tolerate surprises well.
RUGGEDCOM’s Job Is to Sit Where Failure Is Expensive
RUGGEDCOM Ethernet switches and routers are not consumer gadgets, and they are not typical office closet gear. Siemens describes the product family as designed for electrically harsh and climatically demanding environments such as utility substations and traffic-control cabinets. That detail matters because the consequences of compromise are shaped less by brand name than by placement.Industrial networking gear has a different threat profile from laptops and servers. It may run for years in locations that are inconvenient to reach, under maintenance windows negotiated around production schedules, safety requirements, and regulatory controls. It may also act as connective tissue between zones that engineers assumed were separate enough, until an incident proves otherwise.
The affected list spans the ROX II family across MX and RX models, including MX5000, MX5000RE, RX1400, RX1500, RX1501, RX1510, RX1511, RX1512, RX1524, RX1536, and RX5000. Siemens marks all versions before 2.17.1 as affected. That is a clean boundary for asset owners, but also a blunt one: either the device is on 2.17.1 or later, or it belongs in the remediation queue.
For WindowsForum readers, the Windows angle is not that this is a Windows vulnerability. It is that Windows administrators increasingly own, touch, or defend the systems around these devices. The engineering workstation, the jump host, the patch repository, the VPN endpoint, the SIEM connector, and the credential store are often Windows-adjacent. A root compromise on an OT network device may begin outside Windows, but it can quickly become part of the same incident response map.
“Authenticated” Is a Constraint, Not a Comfort Blanket
Vendors and defenders are right to distinguish authenticated from unauthenticated vulnerabilities. A bug that requires credentials is generally harder to exploit at scale than one exposed to the open internet. But in industrial environments, authentication often means something narrower than outsiders imagine.An attacker does not need to be the original administrator if they can obtain a valid account through phishing, password reuse, exposed remote access, a compromised engineering laptop, or a poorly protected vendor maintenance path. Once inside the operational environment, the attacker’s challenge becomes privilege expansion and persistence. A command-injection flaw in a device management function is tailor-made for that phase.
The advisory says the attacker needs remote authenticated access and can then execute arbitrary commands as root. That is a classic post-compromise amplifier. It may not be the first exploit in the chain, but it can turn an account with limited device-level privileges into practical control over the box.
This is why “not internet reachable” is necessary but insufficient. CISA’s familiar guidance — minimize exposure, isolate control-system networks, use firewalls, and prefer secure remote-access methods such as updated VPNs — is still correct. Yet the deeper point is that organizations should assume some authenticated access will eventually be abused. The defensive question is whether that access can reach the vulnerable management surface in the first place.
The Patch Is Small; the Change Window Is Not
Siemens has released fixed versions and recommends updating affected products to version 2.17.1 or later. That is the clean vendor answer, and it should be the end state. In practice, OT patching is a negotiation between cybersecurity urgency and operational certainty.Unlike a browser update, a network-device firmware update can carry routing, redundancy, management, and availability concerns. A switch or router in a substation, plant floor, or transportation cabinet may have dependencies that are undocumented, tribal, or simply old. Firmware updates can be routine in well-run environments, but they are rarely trivial where uptime obligations dominate.
That does not mean organizations should postpone the fix into oblivion. It means they should treat the advisory as a reason to inventory first, test fast, and deploy in controlled waves. The version threshold is unambiguous: anything below 2.17.1 is in scope.
The worst response would be to file this under “requires authentication” and wait for the next scheduled annual maintenance cycle. The better response is to identify exposed management interfaces, review who can authenticate to them, restrict access immediately, and then plan the firmware move. Compensating controls are not a substitute for patching, but they buy down risk while operations teams do the careful work.
CISA’s Republication Turns a Vendor Advisory Into an Operator Checklist
CISA’s May 14 republication is described as a verbatim conversion of Siemens ProductCERT advisory SSA-078743 from CSAF. That is bureaucratic language, but it performs a useful function. It puts the advisory into the feed watched by U.S. defenders, asset owners, managed security providers, and auditors who may not track every vendor portal directly.The republication also places the flaw in the context of critical manufacturing, worldwide deployment, and Germany-based Siemens as the vendor. Those labels are not decoration. They help security teams prioritize advisories across sprawling industrial inventories where no single administrator may know every fielded model by memory.
CISA repeats the standard industrial-control recommendations: minimize network exposure, avoid internet accessibility for control-system devices, place control networks behind firewalls, isolate them from business networks, and use secure remote-access methods when remote access is unavoidable. The phrasing is familiar because the pattern is familiar. Most ICS incidents are not magic; they are the result of reachable systems, weak segmentation, credential problems, and slow remediation colliding with vulnerable software.
The agency also reminds organizations to perform impact analysis and risk assessment before deploying defensive measures. That caveat is important. In OT, a hasty security fix that disrupts operations can itself become a safety or availability event. Mature security teams do not choose between patching and operational analysis; they make the analysis part of the patching process.
Siemens Has a Pattern Here, and So Does Everyone Else
This is not the first RUGGEDCOM ROX advisory involving command execution risk, and it will not be the last industrial-networking advisory of its kind. Siemens has previously issued ROX updates for command-injection and multiple third-party vulnerabilities, and 2.17.1 also appears in other recent ROX advisories. That does not make Siemens uniquely negligent; it makes ROX part of the same software supply-chain and embedded-platform reality affecting every major industrial vendor.Modern industrial devices are software platforms with web interfaces, feature flags, cryptographic components, package dependencies, and remote administration. They may be ruggedized physically, but the software attack surface is increasingly recognizable to anyone who has audited enterprise infrastructure. The difference is that the devices are bolted into environments where disruption is expensive and change is slow.
The feature key angle is especially revealing. Licensing and entitlement workflows often receive less security scrutiny than login pages or exposed APIs, yet they parse externally supplied material and may run privileged system routines. If that parsing is sloppy, the licensing path becomes an execution path.
The lesson for vendors is not simply “sanitize input,” though that is the direct flaw here. The larger lesson is that any administrative workflow crossing from user-controlled data into privileged operating-system behavior must be treated as hostile by default. The fact that a feature is used by administrators does not make its input safe.
Palo Alto’s OT Lab Finding Shows How the Research Market Has Shifted
Siemens credits Emmanuel Zhou, Rick Wyble, Mehemt Balta, and Adam Robbie of Palo Alto Networks’ OT Threat Research Lab with reporting the vulnerability. That attribution is a small but telling sign of where industrial cybersecurity now sits. OT research is no longer the province of a few niche specialists and government labs; it is part of the mainstream security research economy.That shift cuts both ways. More researchers mean more vulnerabilities found and reported before criminals or state-backed actors can exploit them. It also means asset owners should expect a steady drumbeat of advisories against equipment that once felt obscure enough to be safe by default.
Industrial defenders sometimes resent that drumbeat because it creates work without creating new budget. But visibility is not the enemy. The enemy is an environment where vulnerabilities remain unknown until they are used in an incident.
The healthiest reading of this advisory is therefore not panic, but confirmation. The device family is important enough to attract serious research, the vendor has issued a fix, and public-sector channels are amplifying the remediation message. That is how coordinated disclosure is supposed to work. The remaining risk lives in the gap between disclosure and deployment.
Asset Inventory Is the Control That Decides Whether This Is Hard
Every ICS advisory eventually reduces to a basic question: do you know where the affected devices are? If the answer is no, the vulnerability severity almost does not matter. Unknown infrastructure cannot be patched, segmented, monitored, or exempted with confidence.The affected model list is specific enough for a targeted hunt. Security and operations teams should search configuration management databases, network discovery tools, procurement records, diagrams, backup configs, and field inventories for ROX MX5000, MX5000RE, RX1400, RX1500, RX1501, RX1510, RX1511, RX1512, RX1524, RX1536, and RX5000 devices. They should then verify firmware versions rather than assuming procurement age maps neatly to software state.
For Windows-heavy teams, this is where enterprise tooling can help but not finish the job. Vulnerability scanners, NAC systems, SIEM logs, privileged-access records, and remote-management platforms may reveal parts of the picture. OT teams may still need to confirm through vendor tools, console access, maintenance records, or site-level inspections.
The key is to avoid turning this into a purely paperwork-driven exercise. A spreadsheet that says “RUGGEDCOM switch, patched” is not evidence. A verified version number, a change ticket, a backup, and a rollback plan are evidence.
The Immediate Risk Is Management-Plane Exposure
Because exploitation requires authenticated remote access, the most urgent defensive question is who can reach the management plane. If the management interface is exposed broadly inside the corporate network, the organization is betting that every upstream credential and endpoint control will hold. That is not a bet most defenders should enjoy.Restricting management access is the fastest compensating measure. Administrative interfaces should be reachable only from dedicated management stations, jump hosts, or tightly controlled network segments. Accounts should be reviewed, dormant credentials removed, and shared passwords eliminated where possible.
Logs matter too, though embedded-device logging can be uneven. Teams should look for unexpected feature key installation activity, failed or unusual administrative actions, suspicious command execution artifacts where available, and management logins from unfamiliar hosts. The advisory does not describe known exploitation, but waiting for public exploitation before reviewing logs would be backward.
Remote access deserves special scrutiny. VPNs are often the sanctioned answer for OT maintenance, but CISA’s reminder that VPNs must themselves be updated is not a throwaway line. A VPN only narrows the door; it does not guarantee that whoever walks through it should be trusted with every device behind it.
Windows Admins Should Care Because the Blast Radius Crosses Domains
A Siemens ROX vulnerability can sound distant from the daily work of Windows administrators. It should not. The operational network increasingly depends on Windows systems for identity, monitoring, engineering, backup, documentation, remote access, and incident response. Compromise rarely respects the org chart.If an attacker gains root on a network device, they may be able to alter traffic visibility, weaken segmentation, tamper with routing, pivot toward engineering stations, or create persistence that survives ordinary endpoint remediation. Even if the device is not directly involved in Windows authentication, it may sit on the path between Windows systems and industrial assets. Network infrastructure is not just another endpoint; it is the terrain.
This is also why enterprise security teams should stop treating OT advisories as someone else’s queue. The first affected object may be a Siemens device, but the response may involve Active Directory groups, privileged-access management, certificate stores, firewall rules, remote desktop gateways, Windows jump servers, backup validation, and SIEM detection engineering.
The forum audience knows this pattern from ransomware cases in ordinary IT. The first bug is rarely the whole incident. What matters is how many doors it opens after the attacker gets in.
The Version Number Is Clearer Than the Operational Priority
There is no ambiguity in the fixed line: update affected RUGGEDCOM ROX devices to 2.17.1 or later. The ambiguity is priority. A device in a tightly segmented lab environment with restricted management access is not the same as a fielded router reachable from a vendor VPN used by multiple contractors.Risk ranking should start with reachability and role. Devices with management interfaces reachable from broad enterprise networks, shared remote-access environments, or third-party maintenance paths should move first. Devices that sit at segmentation boundaries or carry traffic for critical operations deserve special attention because their compromise can alter what defenders see and what operators can trust.
Organizations should also consider account exposure. If ROX administrative credentials are shared, stale, stored in scripts, or known to multiple vendors, the authenticated requirement becomes much less reassuring. A vulnerability requiring credentials is only as constrained as the credential ecosystem around it.
Finally, patch planning should include configuration backups and recovery rehearsals. Updating firmware without a clean rollback and verified configuration state is how routine maintenance becomes an outage. Security urgency is real, but industrial networks punish improvisation.
The Practical Reading for ROX Operators
The core message is not complicated, but it needs to be acted on with industrial discipline. Siemens has fixed the vulnerability, CISA has amplified the advisory, and the affected device list is precise enough to drive a targeted response.- Organizations should identify every RUGGEDCOM ROX MX5000, MX5000RE, RX1400, RX1500, RX1501, RX1510, RX1511, RX1512, RX1524, RX1536, and RX5000 device and verify whether it is running version 2.17.1 or later.
- Devices below ROX 2.17.1 should be scheduled for update, with priority given to systems whose management interfaces are reachable from broader enterprise, vendor, or remote-access networks.
- Management-plane access should be restricted immediately to trusted administrative hosts and accounts while patch windows are planned.
- Teams should review administrative logs and change records for unusual feature key installation activity or unexpected authenticated access.
- Remote-access paths into OT networks should be checked for current VPN software, strong authentication, and least-privilege network reachability.
- Asset owners should treat compensating controls as temporary risk reduction, not as a reason to leave vulnerable firmware in service indefinitely.
Source: CISA Siemens Ruggedcom Rox | CISA