Microsoft has quietly begun a platform-level refresh of the cryptographic anchors that protect Windows’ pre‑boot environment, delivering new Secure Boot certificates through Windows Update and coordinated OEM firmware work to head off a calendar‑driven failure when Microsoft’s original UEFI certificates—first issued around 2011—begin to expire in mid‑2026. ([support.microsoft.microsoft.com/en-us/topic/secure-boot-certificate-updates-guidance-for-it-professionals-and-organizations-e2b43f9f-b424-42df-bc6a-8476db65ab2f)
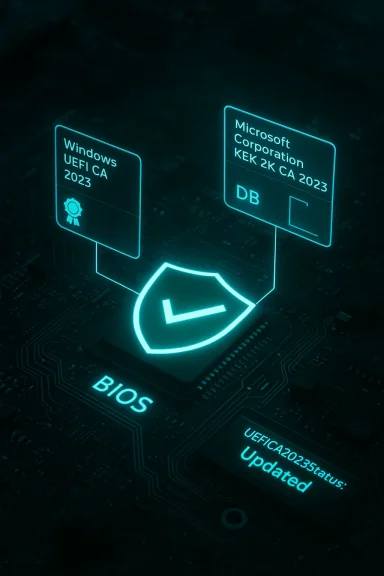
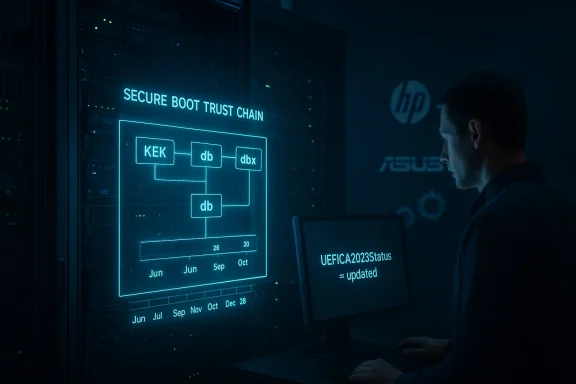
UEFI Secure Boot is the firmware‑level mechanism that ensures only trusted, digitally signed code runs before the operating system starts. Its trust model depends on a small set of certificate authorities (CAs) and keys stored in firmware variables: the Platform Key (PK), Key Exchange Keys (KEK), and the signature databases (DB and DBX). Over the last decade Microsoft has supplied a family of UEFI signing certificates used by Windows and many ecosystem partners to sign bootloaders, option ROMs, and other pre‑OS components.
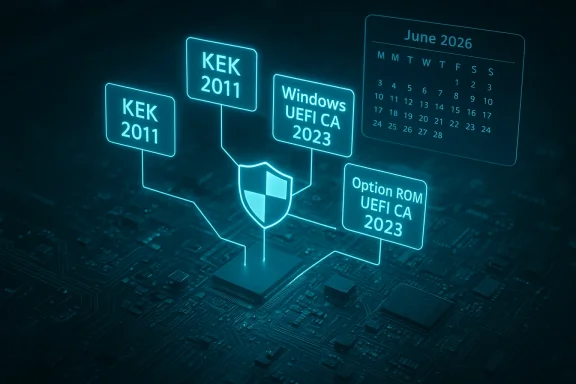
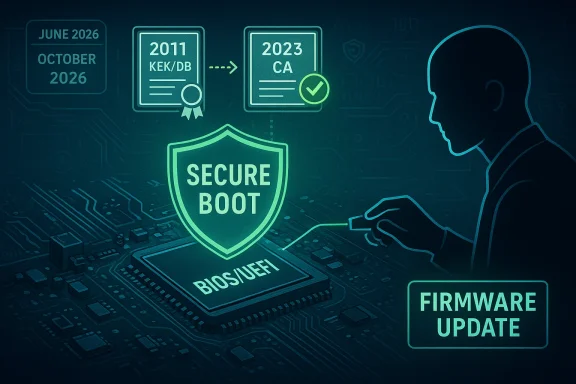
Those Microsoft‑provided certificates were originally issued around 2011 and were always expected to have finite lifetimes. As those 2011‑era keys approach the end of their ing in June 2026 and with related expirations through October 2026—Microsoft and OEM partners have coordinated a phased replacement: a new “2023” family of UEFI/CA certificates will be seeded to firmware and to Windows so that the Secure Boot chain of trust continues uninterrupted.
This article explains what changed, who is affected, how the rollout works, the practical risks of not transitioning, and step‑by‑step guidance for both home users and IT teams to avoid startup or long‑term security problems.
However, notable risks remain:
But the minority matters. Unmanaged Windows 10 machines that haven’t enrolled in ESU, specialized industrial equipment, air‑gapped servers, and custom‑shimbed Linux deployments present real operational risk. For those, the safe strategy is proactive inventory, testing, and remediation now—don’t wait for the expiry date to become an emergency.
Keep these simple rules in mind:
Conclusion: this is not a security panic moment, but it is a clear maintenance deadline. Take action now and you will likely never notice the change except for the reassurance that your platform’s root of trust remains intact.
Source: Bangkok Post Microsoft issues new security patch before expiry
 Background
Background
UEFI Secure Boot is the firmware‑level mechanism that ensures only trusted, digitally signed code runs before the operating system starts. Its trust model depends on a small set of certificate authorities (CAs) and keys stored in firmware variables: the Platform Key (PK), Key Exchange Keys (KEK), and the signature databases (DB and DBX). Over the last decade Microsoft has supplied a family of UEFI signing certificates used by Windows and many ecosystem partners to sign bootloaders, option ROMs, and other pre‑OS components.Those Microsoft‑provided certificates were originally issued around 2011 and were always expected to have finite lifetimes. As those 2011‑era keys approach the end of their ing in June 2026 and with related expirations through October 2026—Microsoft and OEM partners have coordinated a phased replacement: a new “2023” family of UEFI/CA certificates will be seeded to firmware and to Windows so that the Secure Boot chain of trust continues uninterrupted.
This article explains what changed, who is affected, how the rollout works, the practical risks of not transitioning, and step‑by‑step guidance for both home users and IT teams to avoid startup or long‑term security problems.
What Microsoft changed — the technical summary
- Microsoft published guidance and began distributing replacement Secure Boot certificates (the 2023 CA family) through Windows servicing and coordinated OEM firmware updates so devices don’t lose the ability to receive boot‑level protections after the 2011 certs expire.
- The replacement set includes distinct certificates to separate concerns: a KEK replacement (Microsoft Corporation KEK 2K CA 2023) to authorize DB/DBX updates; a Windows UEFI CA 2023 to sign Windows boot loader components; and one or two UEFI CA variants for third‑party boot loaders and option ROMs (including a Microsoft Option ROM UEFI CA 2023 where required). This separation allows finer control over what firmware trusts after the transition.
- Microsoft’s documentation and partner guidance make clear that already‑signed binaries remain valid even after the old CA expires; the risk is with future updates. Devices that do not receive the new CA certificates will continue to boot with existing signed components, but they will new DB/DBX updates or newly signed boot components once the 2011 certs lapse. Over time, that creates a degraded security state.
Who is affected
Windows 11 devices
Most Windows 11 machines are being prioritized for the certificate refresh and will receive the new certificates automatically via Windows Update in a phased rollout. Microsoft’s messaging explicitly urges Windows 11 users to keep devices updated so the new certificates are delivered before the 2011 roots begin to expire.Windows 10 devices
Devices running Windows 10 are only covered if they continue to receive servicing. Systems that have not been upgraded to a supported Windows release and are therefore outside Microsoft’s monthly servicing plane will not automatically receive the certificate refresh. Microsoft has recommended that organizations still on older Windows releases consider enrolling in the Extended Security Updates (ESU) program to keep receiving critical platform deliveries, including this certificate refresh where applicable.Older firmware, unmanaged and air‑gapped devices
A material minority of systems may require firmware or BIOS/UEFI updates from OEMs to fully accept and persist the new certificates. This includes:- Devices with outdated OEM firmware that cannot accept additional KEK/DB entries,
- Enterprise or industrial devices that are air‑gapped or otherwise managed offline,
- Custom‑signed Linux distributions and environments that rely on their own shim/signing flows and therefore may need new shims signed against the 2023 CAs.
Why the change matters — risks and realistic consequences
At first glance: devices will still boot. That’s true, but it understates the security consequences.- Loss of future boot‑level updates: When a device still contains only the expiring 2011 certificates and those certificates reach their expiry, Microsoft (and OEMs) will no longer be able to sign and deliver new DB, DBX, or boot component updates that the firmware would accept. That means new mitigations for pre‑boot vulnerabilities or new revocations of compromised boot signatures cannot be applied to those machines. Over time, this reduces the effectiveness of Secure Boot as a protective layer.
- Compatibility and ecosystem friction: Future versions of signed boot components, hypervisors, or anti‑cheat drivers that are signed with new certificates may not be trusted by systems that never received the 2023 CA family. That can cause application or driver failures, blocked updates, or issues with secure scenarios like BitLocker recovery flows that rely on Secure Boot integrity.
- Operational headaches for IT: For enterprises wiecialized equipment, the problem isn’t instant failure. It’s the accumulation of edge cases—air‑gapped servers, imaging workflows, custom‑signed shims and bootloaders, and firmware‑locked devices—that make remediation costly under time pressure. The recommended mitigation is planning and staged validation now rather than emergency remediation later.
- False sense of safety: Because machines will continue to start after the expiry, some administrators or home users may ignore the issue. That “it still boots” logic is dangerous: the device’s ability to accept future protections is what is at stake. Microsoft labels this a migration to avoid a degraded security state, and the industry reporting echoes that call.
How the rollout is designed to work
Microsoft and OEM partners designed a multi‑track, phased approach rather than a blunt, one‑time swap:- Seed new certificates to new hardware: OEMs began shipping devices with the 2023 certificates included in firmware long before the expiry window, so newer machines already trust both 2011 and 2023 families where appropriate.
- Deliver through Windows servicing: For existing devices, Microsoft is delivering the new KEK/DB entries via Windows Update as part of cumulative/security rollups. The OS‑side update writes the new certificates into firmware where allowed, or prepares the system to accept the keys if an OEM firmware update is also required. This staged delivery reduces the blast radius and lets Microsoft gate pnd compatibility signals. (support.microsoft.com
- Coordinate OEM firmware updates: For machines where the firmware cannot accept an automatic addition of keys or where OEM policy requires vendor involvement, OEMs will ship BIOS/UEFI updates to enroll the new cetors should monitor OEM advisories for those models that need manual firmware updates.
- Partner guidance for Linux and shims: Distributions and customers that manage their own shims (for example, some RHEL/CentOS/Ubuntu deployments) need to rebuild and re‑sign shims against the new certificates or deploy updated shims provided by distribution vendors to ensure continued compatibility. Red Hat and others have posted guidance aligned with Microsoft’s timetable.
Practical steps for users and administrators
Below are concrete, actionable steps to make sure your systems complete the migration safely.For home users with Windows 11 (recommended)
- Keep Windows Update enabled and allow the February/March 2026 cumulative updates (or the next available rollups) to install. Windows Update delivers the new certificates to the majority of systems automatically.
- If you use custom boot configurations, dual‑boot with Linux, or manually enroll keys in firmware, check your firmware Secure Boot configuration after updates and follow vendor guidance before making further changes. Some custom shims may need ment.
- If you are a gamer, don’t panic—but do keep your system updated. Major anti‑cheat vendors have acknowledged the update and OEMs and Microsoft are coordinating to avoid breaking game integrity checks. Still, machines with out‑of‑date firmware may need vendor updates.
For IT teams and enterprises
- Inventory: Identify devices with Secure Boot enabled and record firmware versions andze servers and endpoints that are air‑gapped or have long lifecycles.
- Pilot: Test the Windows‑delivered certificate update on a small representative set of hardware models and any custning workflows. Validate boot, BitLocker, and recovery scenarios.
- Firmware patch plan: For models that cannot accept the update via Windows alone, prepare to deploy OEM BIOS/UEFI updates that enroll the new CA family. Coordinate maintenance windows and test recovery processes.
- ESU and legacy support: If you run older Windows releases, evaluate Extended Security Updates (ESU) enrollment to maintain access to platform deliveries while you migrate or decommission legacy devices. This is especially important for machines that cannot receive firmware updates or are out of the normal servicing channel.
- Communication: Inform stakeholders—desktop support, security, imaging teams, and vendor contacts—about the timelines. Don’t wait until June 2026 to start action; most organizations will need weeks or months to validate and roll out firmware updates across diverse hardware famio verify whether your machine already has the new certificates
- Windows PowerShell: Query the UEFI Secure Boot variables (DB, KEK) to inspect enrolled certificates. Microsoft and community documentation include sample PowerShell commands to list subject names and thumbprints of enrolled CAs. If you see the new “2023” CA entries listed, the device has already enrolled the replacement certificates.
- Firmware setup screens: On many OEM machines you can inspect Secure Boot key enrollment from the UEFI setup utility. The presentation varies by vendor but firmware menus commonly display enrolled key aliases.
- Vendor‑specific toogement: Use your endpoint management tools (SCCM/Intune/others) to query Secure Boot state and firmware versions at scale. Many organizations will aance check to flag non‑compliant hardware before June 2026.
Troubleshooting: if something goes wrong
- Boot facate update are rare, but possible on devices with firmware bugs or custom Secure Boot key state. If a machine won’t boot after an attempted update, use the OEM recovery menu and consult vendor instructions for restoring previous key statEK entries.
- If BitLocker or device encryption triggers a recovery prompt after a change in Secure Boot keys, recover keys using your normal BitLoc That’s why administrators must ensure BitLocker recovery information is backed up before mass rollouts.
- For air‑gapped or offline devices, plan for manual firmware update procedures and test those in maintenance windows. Don’t attempt blind mass firmware updates without pilot validation.
- If you encounter devices that absolutely cannot accept new keys and cannot be upgraded, catalog their risk and consider decommissioning or isolating them from sensitive networks. Leaving such devices running in a production network after the 2011 certs expire increases long‑term exposure.
Strengths of Microsoft’s approach — and where risks remain
Microsoft’s plan has clear strengths: the vendor began the migration early, published detailed guidance for partners and IT, and leveraged Windows Update for mass distribution while coordinating OEM firmware updates for edge cases. This layered approach signihance of a sudden, industry‑wide outage and gives enterprises time to plan.However, notable risks remain:
- Firmware diversity: The PC ecosystem remains extremely fragmented. OEM firmware implementations vary; some vendors may require manual updates or expose firmware limitations that prevent automatic enrollment. That minority of devices could become a persistent operational burden.
- Timing and communications: The expiry window (June–October 2026) is fixed. That constrains the time available to handle complex imaging workflows, air‑gapped devices, and specialized hardware, and it puts pressure on organizations that ft’s guidance is clear, but execution still rests with thousands of OEM and enterprise engineering teams. (support.microsoft.com)
- Third‑party ecosystems: Linux distributions, custom shims, and third‑party boot components must be re‑signed or reissued in many cases. While major vendors are coordinating, smaller projects and bespoke software may be overlooked. That increases the chance of compatibility surprises in niche environments.
- Non‑serviced Windows 10 fleets: Organizations that deferred migrations and aren’t on ESU risk falling outside the automatic delivery path and will need manual remediation—often expensive and slow.
Checklist: A short operational playbook
- Inventory all devices with Secure Boot enabled and identify firmware versions and OEM models.
- Pilot the Windows update that installs 2023 CA certificates on a representative device set. Validate BitLocker, dual‑boot, and anti‑cheat/driver scenarios.
- Identify models that need OEM BIOS/UEFI updates and schedule firmware deployments.
- For Linux and custom environments, coordinate with distro vendors for updated shims signed by the 2023 family.
- Back up BitLocker recovery keys and ensure recovery procedures are tested before broad rollout.
- Track updates and compliance using endpoint management tools; escalate models that remain unpatched as decommissioning candidates if necessary.
Final assessment and recommendation
This is one of those operational changes that looks small in a headline but matters because it touches the root of trust on billions of devices. Microsoft’s early, phased approach is the right one: it reduces the likelihood of a mass outage, provides vendor guidance, and gives organizations predictable paths to remediation. The most likely outcome is a smooth transition for the vast majority of users who keep Windows Update enabled and apply OEM firmware updates when offered.But the minority matters. Unmanaged Windows 10 machines that haven’t enrolled in ESU, specialized industrial equipment, air‑gapped servers, and custom‑shimbed Linux deployments present real operational risk. For those, the safe strategy is proactive inventory, testing, and remediation now—don’t wait for the expiry date to become an emergency.
Keep these simple rules in mind:
- If you are on Windows 11: make sure Windows Update is enabled and applied.
- If you run a mixed or enterprise fleet: inventory, pilot, and coordinate OEM firmware updates now.
- If you run unsupported Windows 10: enroll in ESU or plan migration; otherwise, you could lose critical boot‑level protections after the certificates expire.
Conclusion: this is not a security panic moment, but it is a clear maintenance deadline. Take action now and you will likely never notice the change except for the reassurance that your platform’s root of trust remains intact.
Source: Bangkok Post Microsoft issues new security patch before expiry