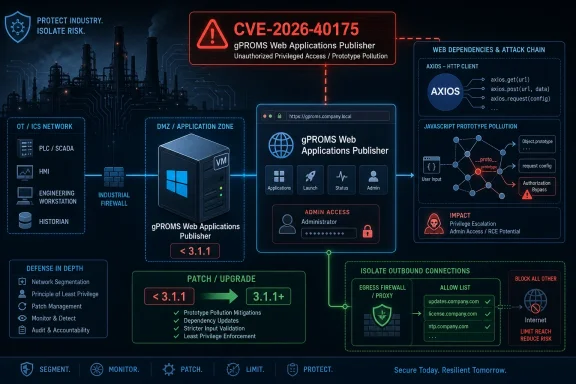
Siemens and CISA disclosed on May 12–14, 2026, that Siemens gPROMS Web Applications Publisher versions before 3.1.1 are affected by CVE-2026-40175, an Axios-linked vulnerability that can allow remote code execution under specific conditions. The advisory is narrow in product scope but broad in what it says about modern industrial software: the weak point is not always the controller, the protocol, or the plant-floor device. Sometimes it is the ordinary web stack wrapped around industrial intellectual property. For WindowsForum readers, the lesson is familiar but newly urgent: dependency risk has moved from developer workstations into the operational technology estate.
The affected product, Siemens gPROMS Web Applications Publisher, is not a PLC, an HMI panel, or a ruggedized switch. It is a web publishing layer for gPROMS applications, designed to make complex process-modeling insights accessible through web apps. That distinction matters, because it places the vulnerability at the intersection of industrial engineering, enterprise web operations, and the increasingly JavaScript-heavy software supply chain.
The Siemens advisory says all gWAP versions before V3.1.1 are affected, and the vendor’s remediation is straightforward: update to V3.1.1 or later. CISA’s republication puts the issue into the industrial control systems channel, noting deployment in critical manufacturing and worldwide exposure. That does not mean every instance is internet-facing, nor does it mean exploitation is trivial. It does mean the product sits in environments where compromise can have consequences beyond a single server.
The vulnerability is CVE-2026-40175, tied to Axios, the widely used HTTP client for browser and Node.js applications. Siemens describes the issue as a “gadget” attack chain that can allow prototype pollution in other third-party libraries to escalate into remote code execution or cloud compromise in some contexts. In Siemens’ gWAP implementation, the product-specific score is CVSS v3.1 8.0 and CVSS v4.0 8.9, with exploitation requiring privileged access to the application.
That last phrase is not a footnote. It is the difference between a drive-by internet worm and a post-authentication path to severe impact. But it should not lull defenders into dismissing the advisory, because industrial environments often rely on long-lived privileged accounts, shared administrative roles, remote access paths, and soft internal segmentation. A vulnerability that requires privilege can still be a serious problem when the surrounding identity model assumes the inside is mostly trusted.
That is why the Siemens advisory is careful about the chain. Axios is not described as a universal “press button, get shell” bug in every deployment. The Axios issue can become dangerous when another dependency or application path provides prototype pollution and Axios becomes the component that turns that condition into request manipulation, credential exposure, or code execution. In other words, the vulnerable component is part of the machinery of exploitation, not necessarily the first domino.
This is uncomfortable for traditional vulnerability management because it resists simple asset inventory logic. A scanner can say “Axios version vulnerable.” It cannot always say whether the application contains a reachable prototype pollution source, whether the dangerous Axios path is exercised, whether the runtime blocks part of the chain, or whether the server has cloud metadata access worth stealing. The result is a familiar split-screen: security tools scream, developers debate exploitability, and defenders still have to make a patching decision under uncertainty.
Siemens’ product-specific assessment cuts through some of that fog. For gWAP, the vendor says an attacker would need privileged application access, but the impact is high across confidentiality, integrity, and availability. That is a classic enterprise risk shape: not necessarily easy to exploit from the public internet, but dangerous after account compromise, insider misuse, weak role separation, or a pivot from another foothold.
For Axios itself, the advisory text points to high attack complexity and limited direct confidentiality and integrity impact in the generic case. For gWAP, Siemens assigns a higher product-specific score because the same weakness can produce severe consequences inside that application’s context. This is exactly how modern software risk behaves: the same npm package can be almost irrelevant in one project and a major incident path in another.
CVSS v4.0 sharpens this distinction by giving Siemens’ product-specific impact an 8.9 score. That does not make the vulnerability magically easier to exploit. It does tell administrators that, if the prerequisite access and application conditions are present, the blast radius is serious enough to justify urgent attention. In operational technology-adjacent systems, that is usually the right way to think: likelihood is contextual, but impact is often expensive.
The advisory also tags the weakness as CWE-113, improper neutralization of CRLF sequences in HTTP headers, better known as HTTP request or response splitting. That classification points to the kind of low-level request manipulation that can make “just an HTTP client bug” into something more interesting. Header injection, request smuggling, SSRF-style behavior, and metadata service abuse all live in the same neighborhood of failure: software builds an outbound request, and an attacker influences pieces of it that were assumed to be inert.
For Windows admins and sysadmins, this should sound familiar. The enterprise spent the last decade discovering that “just a web app” often means Node.js services, transitive dependencies, build pipelines, package registries, reverse proxies, cloud connectors, identity providers, and a runtime environment that changes faster than the underlying business process. OT vendors have not escaped that gravity. They have merely brought it into plants, labs, and engineering environments where uptime windows are scarce and change control is strict.
Siemens gWAP sits in a particularly sensitive slice of that trend because it publishes modeling applications for business use. These are not generic marketing sites. They may expose process assumptions, optimization models, scenario analyses, and decision-support tools tied to production, design, or operational planning. Even if exploitation does not touch a controller, compromise of the web layer can still undermine confidentiality and decision integrity.
That is why the “critical manufacturing” label matters without needing alarmism. An attacker who compromises an engineering web application may not immediately stop a line. But they may steal process knowledge, alter outputs, impersonate trusted workflows, or use the host as a stepping stone into a more consequential network segment. In industrial security, the path from “information system” to “operational consequence” is often indirect, and attackers are patient enough to follow it.
Privileged access in business applications is frequently messier than diagrams suggest. Administrative rights may be granted for support tasks and never removed. Shared service accounts may exist for integrations. Contractors may retain access longer than intended. Password resets, VPN access, remote desktop paths, and identity federation all create chances for an attacker to arrive at the application already wearing the right badge.
The security industry has learned this lesson repeatedly in Microsoft-centric environments. Exchange vulnerabilities, SharePoint misconfigurations, VPN appliance flaws, and identity provider abuse all demonstrate that “requires authentication” is not synonymous with “low priority.” Once an attacker compromises credentials, any vulnerability gated by those credentials becomes part of the privilege escalation and lateral movement toolkit.
In a gWAP deployment, defenders should therefore treat the privilege requirement as a scoping factor, not a dismissal. It tells the SOC where to look: administrative users, unusual sessions, changes made through the application, outbound HTTP behavior, and any host-level activity that does not match normal gWAP operations. It does not remove the need to update.
This creates a visibility problem for enterprise and industrial defenders. A developer can run a package audit against a repository. A sysadmin responsible for a vendor-supplied industrial application may not have the source tree, the lockfile, or the container image manifest. The vendor advisory becomes the authoritative signal because the customer cannot independently determine whether the vulnerable code path is present or reachable.
That dynamic is a recurring weakness in third-party software risk. Customers are told to maintain asset inventories and software bills of materials, but many commercial products still provide only partial transparency. Even when an SBOM exists, it may list components without explaining exploitability. The result is a patching ecosystem built on trust, vendor timing, and advisory interpretation.
To Siemens’ credit, this advisory is clear on the key operational question: gWAP before 3.1.1 is affected, and 3.1.1 or later is the fix. That is more useful than a vague “under investigation” notice or an umbrella advisory that leaves product owners guessing. The remaining challenge is local execution: identifying where gWAP is deployed, who owns it, what integrations depend on it, and when it can be updated without disrupting business workflows.
Those recommendations may sound boilerplate because they are repeated so often. They are repeated because they remain painfully relevant. The easiest exploit chain is not always the one with the lowest CVSS complexity; it is the one that finds a forgotten web app on a flat network with stale credentials and outbound access to everything. Segmentation and exposure reduction turn many theoretical chains into dead ends.
There is also a subtle but important distinction between gWAP as a web application and classic control system equipment. The product may live closer to enterprise IT than to the plant floor, especially if it is used to publish modeling insights for business users. That can make ownership ambiguous. Is it maintained by engineering? IT? A process modeling team? A vendor support group? Ambiguous ownership is where patches go to age.
CISA’s involvement helps by placing the issue in a channel that OT security teams monitor. But it should also pull in enterprise application owners and Windows administrators who may be running the underlying servers, identity integration, reverse proxy, backup jobs, endpoint protection, or database dependencies. The practical response is cross-functional, even if the advisory category says ICS.
The first task is inventory. Organizations should identify whether Siemens gPROMS Web Applications Publisher is deployed, which versions are running, and whether any instance is below V3.1.1. That sounds simple until a product is installed for a pilot, hosted on an engineering VM, reverse-proxied for a business unit, or maintained by a small team outside central IT. Industrial and engineering software often has a longer shadow than the CMDB admits.
The second task is access review. Because Siemens says exploitation requires privileged application access, defenders should verify who has those privileges and whether they still need them. This is a good moment to remove stale admins, rotate shared credentials, enforce MFA where supported, and check whether privileged sessions are logged well enough to reconstruct activity after the fact. Patching closes the known hole; access hygiene reduces the chance that the next hole begins with an already-compromised admin.
The third task is monitoring. If gWAP runs on Windows infrastructure, endpoint telemetry, process creation logs, PowerShell activity, outbound network connections, and web server logs become part of the detection surface. A successful exploitation path that leads to code execution should leave traces somewhere, even if the application-level trigger is subtle. The goal is not to write a perfect signature for CVE-2026-40175; it is to know what normal looks like for the host and notice when the application behaves like a foothold.
Cloud metadata services are only one example of a privileged internal endpoint. Enterprise applications may also have access to internal APIs, license servers, databases, model repositories, file shares, update servers, monitoring endpoints, or identity services. A server-side request that can be bent toward internal resources can reveal information or trigger actions that an external user could not reach directly.
This is where network egress controls become more than a checkbox. Many organizations segment inbound traffic but allow servers to initiate outbound connections broadly. That model assumes the server is trustworthy. Web application exploitation turns that assumption upside down: once the server is attacker-influenced, its outbound permissions become the attacker’s reach.
For gWAP owners, the defensive question is not simply “is this exposed to the internet?” It is also “what can this server reach if the application is abused?” If the answer is “most of the engineering network,” the patch should move faster. If the answer is “only the services it strictly needs,” the organization has already bought down part of the risk.
The challenge is not that administrators do not understand patching. It is that industrial software often supports workflows that are difficult to interrupt. A gPROMS web application may be used for modeling, optimization, reporting, or decision support tied to production or engineering schedules. The people who rely on it may not describe it as “critical infrastructure,” but they will notice when it is unavailable.
That is why the right response is urgent but disciplined. Test the update where possible. Confirm application behavior after upgrade. Preserve backups and configuration exports. Review release notes and vendor guidance. Schedule downtime with the teams that actually use the published apps, not merely the server owners who maintain the VM.
There is a danger in both extremes. Treating every ICS advisory as an emergency can burn credibility and destabilize environments. Treating every privileged-access vulnerability as deferrable can leave a high-impact path open for months. This one belongs in the middle lane: not panic, but not backlog purgatory.
For defenders, this makes vendor advisory review a recurring operational discipline rather than an occasional compliance task. Siemens ProductCERT, CISA ICS advisories, national CERT feeds, and vulnerability databases all become inputs. But intake is only half the job. The harder part is mapping advisories to actual deployments and assigning ownership before an attacker does that mapping for you.
The dependency dimension also means vendors will increasingly ship fixes for flaws they did not write. That can frustrate customers who wonder why a process-modeling web product is suddenly affected by a JavaScript HTTP client issue. But that is software now. The application you buy is also the dependency tree the vendor chose, the build process it uses, and the update cadence it can sustain.
This is where procurement and architecture meet security. Buyers should ask not only what features an industrial web application provides, but how the vendor tracks third-party dependencies, how quickly it issues patched versions, whether it provides SBOM data, and how customers are notified. The gWAP update is a response to one CVE; the larger question is how quickly the next one will move from disclosure to deployable fix.
Siemens gWAP’s Axios-linked flaw is a reminder that industrial security no longer lives only in ladder logic, fieldbus protocols, and locked cabinets; it also lives in npm packages, web runtimes, and application privileges. The fix is a version upgrade, but the lesson is architectural: as industrial software becomes more web-native, defenders must treat ordinary web dependency hygiene as part of operational resilience. The next advisory may name a different library or vendor, but the pattern will be the same — and the organizations that have already connected IT, OT, and application governance will move fastest when it arrives.
Source: CISA Siemens gWAP | CISA
 Siemens’ gWAP Flaw Turns a Web Dependency Into an Industrial Risk Story
Siemens’ gWAP Flaw Turns a Web Dependency Into an Industrial Risk Story
The affected product, Siemens gPROMS Web Applications Publisher, is not a PLC, an HMI panel, or a ruggedized switch. It is a web publishing layer for gPROMS applications, designed to make complex process-modeling insights accessible through web apps. That distinction matters, because it places the vulnerability at the intersection of industrial engineering, enterprise web operations, and the increasingly JavaScript-heavy software supply chain.The Siemens advisory says all gWAP versions before V3.1.1 are affected, and the vendor’s remediation is straightforward: update to V3.1.1 or later. CISA’s republication puts the issue into the industrial control systems channel, noting deployment in critical manufacturing and worldwide exposure. That does not mean every instance is internet-facing, nor does it mean exploitation is trivial. It does mean the product sits in environments where compromise can have consequences beyond a single server.
The vulnerability is CVE-2026-40175, tied to Axios, the widely used HTTP client for browser and Node.js applications. Siemens describes the issue as a “gadget” attack chain that can allow prototype pollution in other third-party libraries to escalate into remote code execution or cloud compromise in some contexts. In Siemens’ gWAP implementation, the product-specific score is CVSS v3.1 8.0 and CVSS v4.0 8.9, with exploitation requiring privileged access to the application.
That last phrase is not a footnote. It is the difference between a drive-by internet worm and a post-authentication path to severe impact. But it should not lull defenders into dismissing the advisory, because industrial environments often rely on long-lived privileged accounts, shared administrative roles, remote access paths, and soft internal segmentation. A vulnerability that requires privilege can still be a serious problem when the surrounding identity model assumes the inside is mostly trusted.
The Most Important Word in the Advisory Is “Gadget”
Prototype pollution has a way of sounding like an academic JavaScript oddity until it becomes an incident report. In JavaScript, objects inherit behavior through prototypes; if an attacker can modify those prototypes, they may be able to change how unrelated code behaves later. By itself, that may cause instability or data tampering. Paired with a useful gadget — a piece of legitimate code that unintentionally reads the polluted property in a dangerous way — it can become a route to much more serious outcomes.That is why the Siemens advisory is careful about the chain. Axios is not described as a universal “press button, get shell” bug in every deployment. The Axios issue can become dangerous when another dependency or application path provides prototype pollution and Axios becomes the component that turns that condition into request manipulation, credential exposure, or code execution. In other words, the vulnerable component is part of the machinery of exploitation, not necessarily the first domino.
This is uncomfortable for traditional vulnerability management because it resists simple asset inventory logic. A scanner can say “Axios version vulnerable.” It cannot always say whether the application contains a reachable prototype pollution source, whether the dangerous Axios path is exercised, whether the runtime blocks part of the chain, or whether the server has cloud metadata access worth stealing. The result is a familiar split-screen: security tools scream, developers debate exploitability, and defenders still have to make a patching decision under uncertainty.
Siemens’ product-specific assessment cuts through some of that fog. For gWAP, the vendor says an attacker would need privileged application access, but the impact is high across confidentiality, integrity, and availability. That is a classic enterprise risk shape: not necessarily easy to exploit from the public internet, but dangerous after account compromise, insider misuse, weak role separation, or a pivot from another foothold.
The CVSS Numbers Tell Two Different Stories, and Both Matter
The underlying Axios CVE is listed with a lower CVSS v3.1 base score in Siemens’ advisory than the gWAP-specific impact score. That discrepancy may look odd at first, but it reflects an important reality in dependency vulnerabilities. A library’s theoretical severity is not always the same as the severity of a product that embeds it in a particular architecture, privilege model, and deployment pattern.For Axios itself, the advisory text points to high attack complexity and limited direct confidentiality and integrity impact in the generic case. For gWAP, Siemens assigns a higher product-specific score because the same weakness can produce severe consequences inside that application’s context. This is exactly how modern software risk behaves: the same npm package can be almost irrelevant in one project and a major incident path in another.
CVSS v4.0 sharpens this distinction by giving Siemens’ product-specific impact an 8.9 score. That does not make the vulnerability magically easier to exploit. It does tell administrators that, if the prerequisite access and application conditions are present, the blast radius is serious enough to justify urgent attention. In operational technology-adjacent systems, that is usually the right way to think: likelihood is contextual, but impact is often expensive.
The advisory also tags the weakness as CWE-113, improper neutralization of CRLF sequences in HTTP headers, better known as HTTP request or response splitting. That classification points to the kind of low-level request manipulation that can make “just an HTTP client bug” into something more interesting. Header injection, request smuggling, SSRF-style behavior, and metadata service abuse all live in the same neighborhood of failure: software builds an outbound request, and an attacker influences pieces of it that were assumed to be inert.
Industrial Software Now Inherits the Web’s Dependency Debt
The gWAP advisory is not notable because Siemens used Axios. It is notable because almost everyone does something like this now. Industrial software that once shipped as thick clients, monolithic engineering tools, or isolated runtime packages increasingly arrives as web portals, dashboards, APIs, and browser-accessible applications. That evolution brings convenience, but it also imports the dependency graph of modern web development.For Windows admins and sysadmins, this should sound familiar. The enterprise spent the last decade discovering that “just a web app” often means Node.js services, transitive dependencies, build pipelines, package registries, reverse proxies, cloud connectors, identity providers, and a runtime environment that changes faster than the underlying business process. OT vendors have not escaped that gravity. They have merely brought it into plants, labs, and engineering environments where uptime windows are scarce and change control is strict.
Siemens gWAP sits in a particularly sensitive slice of that trend because it publishes modeling applications for business use. These are not generic marketing sites. They may expose process assumptions, optimization models, scenario analyses, and decision-support tools tied to production, design, or operational planning. Even if exploitation does not touch a controller, compromise of the web layer can still undermine confidentiality and decision integrity.
That is why the “critical manufacturing” label matters without needing alarmism. An attacker who compromises an engineering web application may not immediately stop a line. But they may steal process knowledge, alter outputs, impersonate trusted workflows, or use the host as a stepping stone into a more consequential network segment. In industrial security, the path from “information system” to “operational consequence” is often indirect, and attackers are patient enough to follow it.
Privileged Access Is a Barrier, Not a Defense Strategy
The advisory’s requirement for privileged application access will be the sentence many organizations use to push this patch down the queue. That instinct is understandable. If an unauthenticated internet exploit is a fire alarm, a privileged-access exploit sounds more like a locked filing cabinet. The problem is that many real intrusions begin by turning ordinary credentials into privileged ones.Privileged access in business applications is frequently messier than diagrams suggest. Administrative rights may be granted for support tasks and never removed. Shared service accounts may exist for integrations. Contractors may retain access longer than intended. Password resets, VPN access, remote desktop paths, and identity federation all create chances for an attacker to arrive at the application already wearing the right badge.
The security industry has learned this lesson repeatedly in Microsoft-centric environments. Exchange vulnerabilities, SharePoint misconfigurations, VPN appliance flaws, and identity provider abuse all demonstrate that “requires authentication” is not synonymous with “low priority.” Once an attacker compromises credentials, any vulnerability gated by those credentials becomes part of the privilege escalation and lateral movement toolkit.
In a gWAP deployment, defenders should therefore treat the privilege requirement as a scoping factor, not a dismissal. It tells the SOC where to look: administrative users, unusual sessions, changes made through the application, outbound HTTP behavior, and any host-level activity that does not match normal gWAP operations. It does not remove the need to update.
The Axios Angle Is Bigger Than One Siemens Product
Axios has become one of the default HTTP clients in the JavaScript ecosystem because it is convenient, familiar, and portable across browser and Node.js contexts. That popularity is precisely why an Axios vulnerability creates noisy downstream effects. The same package can appear directly in an application, indirectly through a framework, bundled into a vendor product, or frozen inside a packaged appliance that customers cannot easily inspect.This creates a visibility problem for enterprise and industrial defenders. A developer can run a package audit against a repository. A sysadmin responsible for a vendor-supplied industrial application may not have the source tree, the lockfile, or the container image manifest. The vendor advisory becomes the authoritative signal because the customer cannot independently determine whether the vulnerable code path is present or reachable.
That dynamic is a recurring weakness in third-party software risk. Customers are told to maintain asset inventories and software bills of materials, but many commercial products still provide only partial transparency. Even when an SBOM exists, it may list components without explaining exploitability. The result is a patching ecosystem built on trust, vendor timing, and advisory interpretation.
To Siemens’ credit, this advisory is clear on the key operational question: gWAP before 3.1.1 is affected, and 3.1.1 or later is the fix. That is more useful than a vague “under investigation” notice or an umbrella advisory that leaves product owners guessing. The remaining challenge is local execution: identifying where gWAP is deployed, who owns it, what integrations depend on it, and when it can be updated without disrupting business workflows.
CISA’s Republication Is a Signal About Visibility, Not Panic
CISA’s ICS advisories often get misread as a declaration that a vulnerability is being actively exploited against factories. That is not what this republication says. CISA republished Siemens ProductCERT’s advisory to increase visibility, and the text carries the usual defensive guidance: minimize network exposure, keep control system assets away from direct internet access, isolate control networks from business networks, and use secure remote access methods where needed.Those recommendations may sound boilerplate because they are repeated so often. They are repeated because they remain painfully relevant. The easiest exploit chain is not always the one with the lowest CVSS complexity; it is the one that finds a forgotten web app on a flat network with stale credentials and outbound access to everything. Segmentation and exposure reduction turn many theoretical chains into dead ends.
There is also a subtle but important distinction between gWAP as a web application and classic control system equipment. The product may live closer to enterprise IT than to the plant floor, especially if it is used to publish modeling insights for business users. That can make ownership ambiguous. Is it maintained by engineering? IT? A process modeling team? A vendor support group? Ambiguous ownership is where patches go to age.
CISA’s involvement helps by placing the issue in a channel that OT security teams monitor. But it should also pull in enterprise application owners and Windows administrators who may be running the underlying servers, identity integration, reverse proxy, backup jobs, endpoint protection, or database dependencies. The practical response is cross-functional, even if the advisory category says ICS.
Windows Shops Should Read This as an Application Governance Problem
WindowsForum readers tend to think in terms of endpoints, servers, Active Directory, patch baselines, and the monthly rhythm of Microsoft updates. This Siemens advisory belongs in that world too. gWAP may be a Siemens product, but the operational response likely touches Windows Server administration, identity governance, network segmentation, backup validation, logging, and change control.The first task is inventory. Organizations should identify whether Siemens gPROMS Web Applications Publisher is deployed, which versions are running, and whether any instance is below V3.1.1. That sounds simple until a product is installed for a pilot, hosted on an engineering VM, reverse-proxied for a business unit, or maintained by a small team outside central IT. Industrial and engineering software often has a longer shadow than the CMDB admits.
The second task is access review. Because Siemens says exploitation requires privileged application access, defenders should verify who has those privileges and whether they still need them. This is a good moment to remove stale admins, rotate shared credentials, enforce MFA where supported, and check whether privileged sessions are logged well enough to reconstruct activity after the fact. Patching closes the known hole; access hygiene reduces the chance that the next hole begins with an already-compromised admin.
The third task is monitoring. If gWAP runs on Windows infrastructure, endpoint telemetry, process creation logs, PowerShell activity, outbound network connections, and web server logs become part of the detection surface. A successful exploitation path that leads to code execution should leave traces somewhere, even if the application-level trigger is subtle. The goal is not to write a perfect signature for CVE-2026-40175; it is to know what normal looks like for the host and notice when the application behaves like a foothold.
The Cloud Metadata Warning Should Not Be Ignored On-Prem
The Axios CVE description includes the possibility of AWS IMDSv2 bypass and full cloud compromise in some conditions. That phrase may tempt on-prem administrators to tune out. If gWAP is running in a local data center, why care about cloud metadata? Because the same class of request-manipulation issue often matters anywhere an application can reach internal services that users cannot.Cloud metadata services are only one example of a privileged internal endpoint. Enterprise applications may also have access to internal APIs, license servers, databases, model repositories, file shares, update servers, monitoring endpoints, or identity services. A server-side request that can be bent toward internal resources can reveal information or trigger actions that an external user could not reach directly.
This is where network egress controls become more than a checkbox. Many organizations segment inbound traffic but allow servers to initiate outbound connections broadly. That model assumes the server is trustworthy. Web application exploitation turns that assumption upside down: once the server is attacker-influenced, its outbound permissions become the attacker’s reach.
For gWAP owners, the defensive question is not simply “is this exposed to the internet?” It is also “what can this server reach if the application is abused?” If the answer is “most of the engineering network,” the patch should move faster. If the answer is “only the services it strictly needs,” the organization has already bought down part of the risk.
The Patch Is Simple; The Change Window May Not Be
Siemens’ remediation is clean: update gWAP to V3.1.1 or later. In an ordinary SaaS product, that sentence might be the end of the story. In industrial and engineering environments, it is the beginning of a process that includes compatibility checks, validation, downtime planning, rollback preparation, and coordination with teams that may be using published applications for active work.The challenge is not that administrators do not understand patching. It is that industrial software often supports workflows that are difficult to interrupt. A gPROMS web application may be used for modeling, optimization, reporting, or decision support tied to production or engineering schedules. The people who rely on it may not describe it as “critical infrastructure,” but they will notice when it is unavailable.
That is why the right response is urgent but disciplined. Test the update where possible. Confirm application behavior after upgrade. Preserve backups and configuration exports. Review release notes and vendor guidance. Schedule downtime with the teams that actually use the published apps, not merely the server owners who maintain the VM.
There is a danger in both extremes. Treating every ICS advisory as an emergency can burn credibility and destabilize environments. Treating every privileged-access vulnerability as deferrable can leave a high-impact path open for months. This one belongs in the middle lane: not panic, but not backlog purgatory.
The Wider Siemens Advisory Batch Shows the New Normal
The gWAP advisory landed among a broader set of Siemens security notices in May 2026, including issues in engineering software, Ruggedcom products, Teamcenter, SIMATIC-related components, and other industrial offerings. That context is important because it shows how security maintenance now spans the entire industrial software stack. The edge device, the engineering workstation, the web portal, and the third-party library all take turns being the weak link.For defenders, this makes vendor advisory review a recurring operational discipline rather than an occasional compliance task. Siemens ProductCERT, CISA ICS advisories, national CERT feeds, and vulnerability databases all become inputs. But intake is only half the job. The harder part is mapping advisories to actual deployments and assigning ownership before an attacker does that mapping for you.
The dependency dimension also means vendors will increasingly ship fixes for flaws they did not write. That can frustrate customers who wonder why a process-modeling web product is suddenly affected by a JavaScript HTTP client issue. But that is software now. The application you buy is also the dependency tree the vendor chose, the build process it uses, and the update cadence it can sustain.
This is where procurement and architecture meet security. Buyers should ask not only what features an industrial web application provides, but how the vendor tracks third-party dependencies, how quickly it issues patched versions, whether it provides SBOM data, and how customers are notified. The gWAP update is a response to one CVE; the larger question is how quickly the next one will move from disclosure to deployable fix.
The gWAP Advisory Rewards Teams That Know Their Own Sprawl
The practical message from this advisory is not complicated, but it is easy to lose in the jargon. Siemens has shipped a fixed gWAP version. The vulnerable versions are known. The exploit path requires privileged application access, but the impact can be severe. The rest is execution.- Organizations running Siemens gPROMS Web Applications Publisher should identify every deployed instance and verify whether it is older than V3.1.1.
- Administrators should update affected gWAP installations to V3.1.1 or later after normal testing, backup, and change-control steps.
- Security teams should review privileged gWAP accounts because Siemens’ product-specific exploit scenario depends on privileged application access.
- Network teams should confirm that gWAP instances are not internet-exposed and cannot freely reach unrelated internal or cloud metadata services.
- Monitoring teams should treat unusual gWAP server activity, unexpected outbound requests, and abnormal privileged user behavior as signals worth investigating.
- Procurement and platform owners should use this case to demand better visibility into third-party dependencies in industrial web applications.
Siemens gWAP’s Axios-linked flaw is a reminder that industrial security no longer lives only in ladder logic, fieldbus protocols, and locked cabinets; it also lives in npm packages, web runtimes, and application privileges. The fix is a version upgrade, but the lesson is architectural: as industrial software becomes more web-native, defenders must treat ordinary web dependency hygiene as part of operational resilience. The next advisory may name a different library or vendor, but the pattern will be the same — and the organizations that have already connected IT, OT, and application governance will move fastest when it arrives.
Source: CISA Siemens gWAP | CISA